Information Technology > EXAM > Hinds Community College - IST 1124;IT final milestone_all answers 100% correct. (All)
Hinds Community College - IST 1124;IT final milestone_all answers 100% correct.
Document Content and Description Below
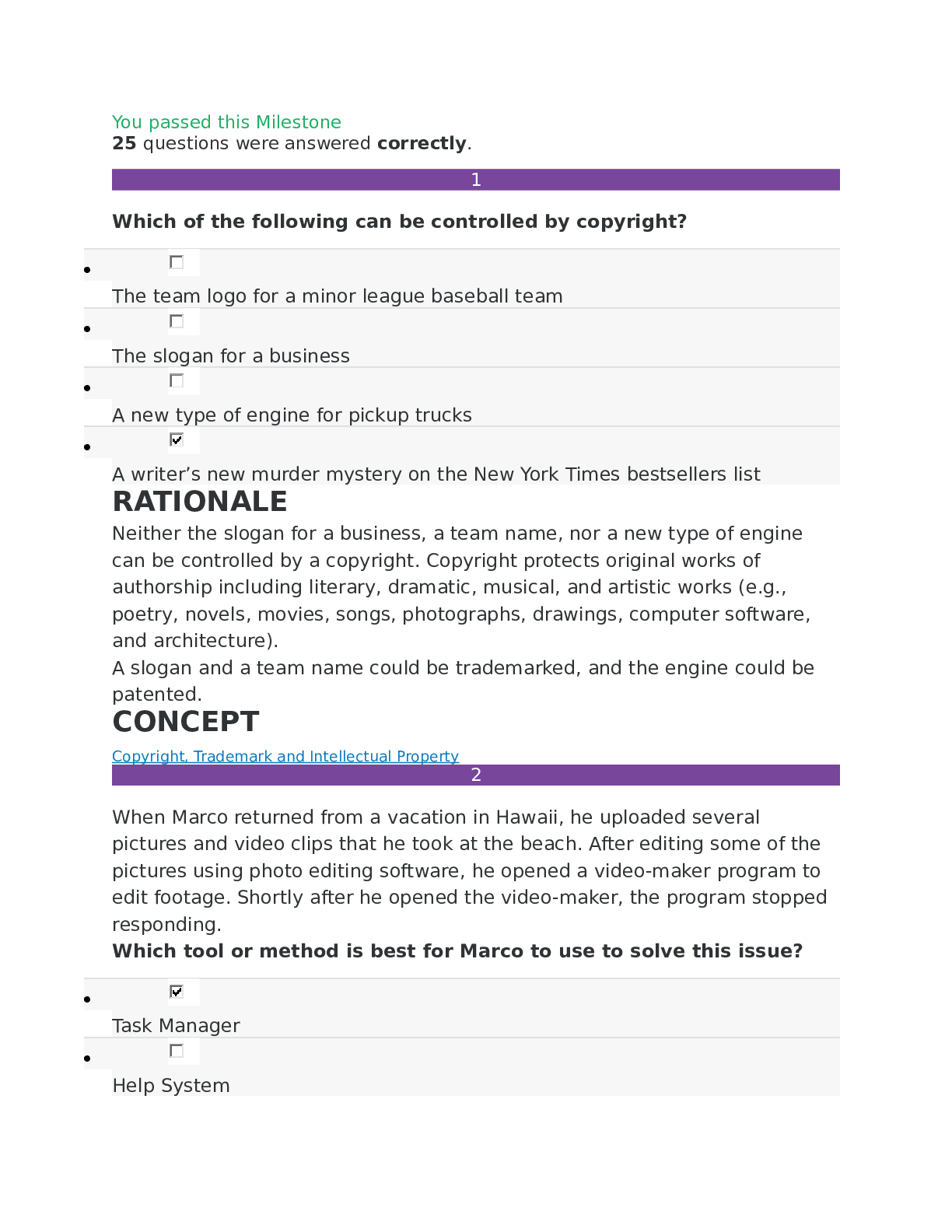
IT final milestone. You passed this Milestone 25 questions were answered correctly. 1 Which of the following can be controlled by copyright? • The team logo for a minor league baseball team ... • The slogan for a business • A new type of engine for pickup trucks • A writer’s new murder mystery on the New York Times bestsellers list 2 When Marco returned from a vacation in Hawaii, he uploaded several pictures and video clips that he took at the beach. After editing some of the pictures using photo editing software, he opened a video-maker program to edit footage. Shortly after he opened the video-maker, the program stopped responding. Which tool or method is best for Marco to use to solve this issue? • Task Manager • Help System • System Restore • Safe Mode 3 In which of the following scenarios can a trademark be applied? • Tiffany records a sequence of three musical notes that appear in every ad for a company. • Erik uploads a new reaction video to his YouTube channel. • Paige creates a gluten-free dessert recipe and posts it on her blog. • Randy designs a bracelet for his jewelry line. 4 Because a computer typically runs a variety of programs simultaneously, the role of the operating system is to ensure that all programs have access to the __________. • power supply • monitor • keyboard • CPU 5 Select the true statement about the CPU. • It permits the exchange of electrical signals between computer components. • It transfers data from the hard disk for processing. • It provides a central connection for computer components. • It executes commands sent by program software. 6 Which of the following is a best practice for maintaining a safe and healthy workstation? • Adjusting the back of the chair so that a person's lower back is supported and perpendicular to the floor • Adjusting the chair so that the user can stretch his or her legs straight out • Reaching to the left to access the keyboard • Placing the monitor screen seven inches from the face 7 ENIAC, which stands for Electronic Numerical Integrator and Computer, is an example of a __________ computer. • mini • mainframe • microprocessor • personal 8 Michiko works for a credit union. When a new employee is hired, the manager contacts Michiko to add a new user to the network and to set appropriate permissions for that user. What is Michiko's role in her organization? • Systems Administrator • Network Engineer • Programming Language Specialist • Database Administrator 9 Tyler works with a software development team at a large healthcare organization. His job is to identify the aspects of the software that must be tested, develop appropriate tests, run those tests, and evaluate the results. What is Tyler's role in the organization? • Quality Assurance • Software Project Manager • Software Developer • Analyst 10 Jeremiah searches his computer for movie files that he recently shot during his vacation in Belize. Select the set of file types that Jeremiah should look for. • .avi and .wmv • .mpg and .key • .mov and .ods • .wma and .mpg 11 __________ is a mobile application used primarily to share photos and videos with others. • LinkedIn • Instagram • QQ • Twitter 12 Kirby visited a sweepstakes website and agreed to download a new program. Later, when he tried to use a word processing program, his document files became corrupted. How can Kirby try to remove the offending program and prevent future attacks? • Kirby should use WPA network encryption. • Kirby should change the password on his computer. • Kirby should run an antivirus program. • Kirby should install a biometric reader. 13 __________, developed by OpenOffice, is an example of word processing software. • Writer • Numbers • Keynote • Impress 14 Which of the following is NOT an example of copyright infringement? • Chris posts a number of full-text articles onto his website without giving credit to the authors. • Melanie finds images that are in the public domain and submits them to a photography competition as her own work. • Eddie likes photos that were posted on a business's website, so he downloads them to his computer. • Katy uses Wi-Fi at Starbucks during her lunch break to check her email, and to turn in a book report. 15 Select the scenario that describes a bottom-up approach to data warehouse design. • Charley’s Wholesalers combines data from its produce, meat, and dry goods vendors into a single data warehouse, and distributes it among several data marts. • Hollywood Advertising combines data marts from its San Diego, Los Angeles, and San Francisco offices into a single data warehouse. • Dave’s Appliances, which has five locations in the city, combines data from each store to a single database, and distributes it to three new data marts. • Jaime’s Research Consulting Firm combines data from its clients into a central database, then shares the data with several individual contractors. 16 Chip stays up late every night surfing the Web, but tells himself that he hardly ever does this. Which computer addiction symptom is Chip experiencing? • Neglect • Lack of control • Uncomfortable feelings • Downplaying 17 Select the file size that is the LARGEST. • 5 MB • 4 TB • 3,000 GB • 1,000,000 KB 18 Information systems consist of five components: hardware, software, data, process, and __________. • data management • people • monitors • peripherals 19 Paul wants to present information about a new product at the upcoming national sales meeting. Which productivity software should Paul use? • Microsoft Excel • OpenOffice Impress • IBM DB2 • Google Docs 20 Mel is a research scientist at a health sciences center. His job requires him to analyze large amounts of data in short periods of time. Select the best computer for Mel. • A handheld tablet computer • A desktop computer with two screens • A portable laptop computer • A desktop computer with a fast processor 21 Malouka participates in a research project for a large consumer behavior research firm. Each time she purchases items in a grocery store, she scans the barcodes of her products into an app, which sends her purchase data to the firm for analysis. Malouka is working with an example of automation known as __________. • textfill/autocorrect • advertising and marketing • billing • importing/exporting data 22 More than 70% of YouTube users are located outside the United States. This statement describes the trend known as __________. • social media growth • autonomous technology • personalization • mobilization 23 Alex establishes information-security policies for his organization, and oversees the implementation of those policies. Alex is employed as a __________. • Computer Engineer • Database Administrator • Computer Operator • Computer Programmer 24 Which of the following statements about the relationship between hardware and software is FALSE? • Application software, which does something useful, is a main category of software. • Hardware will not function without software, and software will not run without the appropriate hardware. • Computer software drives computer hardware by providing the instructions that tell the hardware what to do. • Application software runs independently of any hardware. 25 John is using __________, a software development management tool that easily integrates into his business’s enterprise software/information system. • MS Resource • Visual Studio • Primavera • Visio [Show More]
Last updated: 1 year ago
Preview 1 out of 14 pages
Reviews( 0 )
Recommended For You
*NURSING> EXAM > Ati PN comprehensive predictor 180 Questions and Answers 100% Correct. Download to Score an Outstanding A (All)
Ati PN comprehensive predictor 180 Questions and Answers 100% Correct. Download to Score an Outstanding A
. A nurse is planning to obtain a 12-lead ECG for a client who has a history of cardiac dysrhythmias. Which of the following actions should the nurse plan to take? - tell the client to expect a mild...
By PHISHER , Uploaded: May 16, 2022
$15
Health Care> EXAM > TESTBANK-CONTEMPORARY NURSING ISSUES,TRENDS,AND MANAGEMENT CHERRY & JACOB 7th EDITION,CHAPTERS[1-28]QUESTIONS AND ANSWERS 100% CORRECT. (All)

TESTBANK-CONTEMPORARY NURSING ISSUES,TRENDS,AND MANAGEMENT CHERRY & JACOB 7th EDITION,CHAPTERS[1-28]QUESTIONS AND ANSWERS 100% CORRECT.
TESTBANK-CONTEMPORARY NURSING ISSUES,TRENDS,AND MANAGEMENT CHERRY & JACOB 7th EDITION,CHAPTERS[1-28]QUESTIONS AND ANSWERS 100% CORRECT.
By MARKALLAN , Uploaded: Jul 02, 2022
$7
*NURSING> EXAM > NSG 6001 WEEK 5 QUIZ, QUESTION AND ANSWERS 100% Correct. (All)

NSG 6001 WEEK 5 QUIZ, QUESTION AND ANSWERS 100% Correct.
A patient with shoulder pain is seen by an orthopedic specialist who notes erythema, warmth, and fluctuance of the shoulder joint. What is the next step in treatment for this patient?
By professor chue , Uploaded: Jun 20, 2022
$11.5
*NURSING> EXAM > 2022 CNA Exam questions and answers 100% correct. (All)
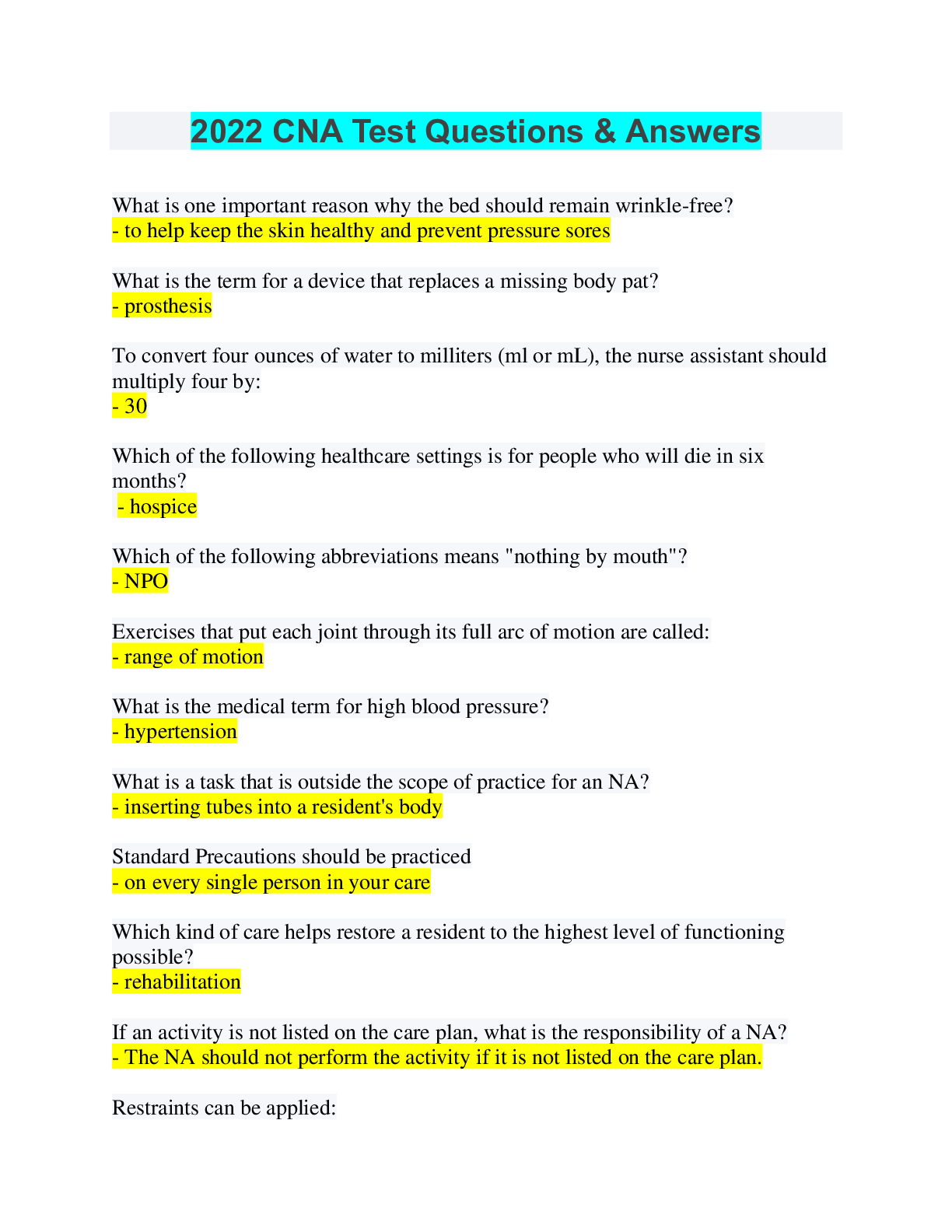
2022 CNA Exam questions and answers 100% correct.
2022 CNA Test Questions & Answers What is one important reason why the bed should remain wrinkle-free? What is the term for a device that replaces a missing body pat? To convert four ounces...
By CoursesExams , Uploaded: Apr 25, 2022
$15
*NURSING> EXAM > NCLEX Practice Questions Exam 1 WITH VERIFIED ANSWERS 100% correct. (All)
NCLEX Practice Questions Exam 1 WITH VERIFIED ANSWERS 100% correct.
NCLEX Practice Questions Exam 1
By [email protected] , Uploaded: Apr 20, 2022
$17
*NURSING> EXAM > Exit HESI Test Bank (98 Questions) 2022 / UPDATED Exit HESI Prep Distinction Level Assignment Has everything. All Answers 100% Correct. (All)
Exit HESI Test Bank (98 Questions) 2022 / UPDATED Exit HESI Prep Distinction Level Assignment Has everything. All Answers 100% Correct.
Exit HESI Test Bank (98 Questions) 2022 / UPDATED Exit HESI Prep Distinction Level Assignment Has everything. All Answers 100% Correct. 1. A nurse is providing information to a group of pregna...
By Tutorsammy , Uploaded: Mar 17, 2022
$19
*NURSING> EXAM > Palliative and Hospice Care CASE STUDY.,WELL EXPLAINED WITH VERIFIED ANSWERS 100% CORRECT. (All)
Palliative and Hospice Care CASE STUDY.,WELL EXPLAINED WITH VERIFIED ANSWERS 100% CORRECT.
Palliative and Hospice Care Imagine you are the Home Health Hospice Nurse providing care for Frank Jones a 70 year old client diagnosed with Stage 4 Metastatic Brain Cancer admitted to hospice care tw...
By merit95 , Uploaded: May 29, 2021
$15
*NURSING> EXAM > Palliative and Hospice Care CASE STUDY.,WELL EXPLAINED WITH VERIFIED ANSWERS 100% CORRECT. (All)
Palliative and Hospice Care CASE STUDY.,WELL EXPLAINED WITH VERIFIED ANSWERS 100% CORRECT.
Palliative and Hospice Care Imagine you are the Home Health Hospice Nurse providing care for Frank Jones a 70 year old client diagnosed with Stage 4 Metastatic Brain Cancer admitted to hospice care tw...
By [email protected] , Uploaded: May 29, 2021
$15
*NURSING> EXAM > Pharm_Scenario_02_.,WELL EXPLAINED WITH VERIFIED ANSWERS 100% CORRECT. (All)
Pharm_Scenario_02_.,WELL EXPLAINED WITH VERIFIED ANSWERS 100% CORRECT.
1. Document assessment data of Toua Xiong, including a focused history, physical examination (including vital signs), focused respiratory assessment, pain level assessment, and assessment of the oral...
By merit95 , Uploaded: May 13, 2021
$13
*NURSING> EXAM > Pharm_Scenario_02_.,WELL EXPLAINED WITH VERIFIED ANSWERS 100% CORRECT. (All)
Pharm_Scenario_02_.,WELL EXPLAINED WITH VERIFIED ANSWERS 100% CORRECT.
1. Document assessment data of Toua Xiong, including a focused history, physical examination (including vital signs), focused respiratory assessment, pain level assessment, and assessment of the oral...
By [email protected] , Uploaded: May 13, 2021
$15
Document information
Connected school, study & course
About the document
Uploaded On
Sep 26, 2020
Number of pages
14
Written in
Additional information
This document has been written for:
Uploaded
Sep 26, 2020
Downloads
0
Views
266