Computer Networking > EXAM > CSIS 330 Final Exam Liberty, (Version 2, Latest 2019/2020), Re-take, 100% Correct. (All)
CSIS 330 Final Exam Liberty, (Version 2, Latest 2019/2020), Re-take, 100% Correct.
Document Content and Description Below
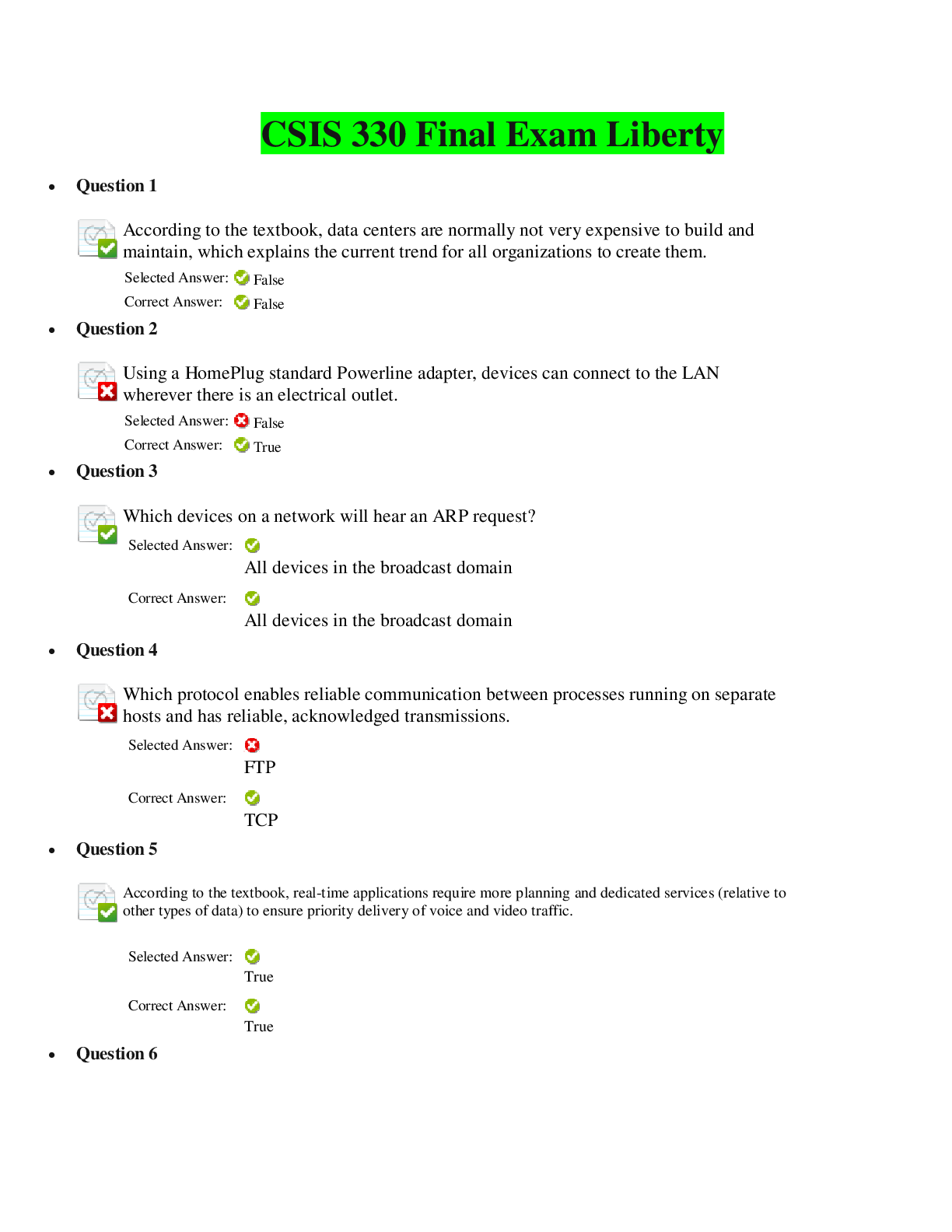
CSIS 330 Final Exam Liberty • Question 1 According to the textbook, data centers are normally not very expensive to build and maintain, which explains the current trend for all organizati... ons to create them. • Question 2 Using a HomePlug standard Powerline adapter, devices can connect to the LAN wherever there is an electrical outlet. • Question 3 Which devices on a network will hear an ARP request? • Question 4 Which protocol enables reliable communication between processes running on separate hosts and has reliable, acknowledged transmissions. • Question 5 According to the textbook, real-time applications require more planning and dedicated services (relative to other types of data) to ensure priority delivery of voice and video traffic. • Question 6 Which of the following connections runs over a telephone line with the line split into three channels? • Question 7 IEEE rates UTP cabling according to its performance, thereby placing cables into categories according to their ability to carry higher-bandwidth rates. Of the following categories, which one is the recommended type for data networking in new building installations? • Question 8 The need for a single, reserved circuit from end to end exists in a packet-switched network. • Question 9 What is true of Tier 3 ISPs? • Question 10 What is the decimal equivalent of the binary number 11111000? • Question 11 According to the textbook, which of the following is a way in which network infrastructures can vary? • Question 12 Which of the following is not one of the three primary collaboration questions that organizations must ask to achieve effective collaboration? • Question 13 Like IPv4, IPv6 uses both the prefix length and the dotted-decimal subnet mask notation for indicate the network portion of an IPv6 address. • Question 14 The ________________ provides communications between the hardware and software of the computer system as well as manages hardware resources. • Question 15 Which IPv4 block of addresses is reserved for multi-cast groups? • Question 16 What is a fault-tolerant network? • Question 17 According to the textbook, switch devices and wireless access points cannot be separate dedicated devices within a network implementation. • Question 18 What type of physical topology involves end systems connected to their respective neighbor, forming a circle? • Question 19 ___________________________ is the most common type of networking cable. It is commonly used to interconnect a host to a switch and a switch to a router. • Question 20 ______________ are pages that are easy to update and edit and give anyone a means to communicate their thoughts to a global audience without technical knowledge of web design. They are like an individual, personal journal. • Question 21 What are two types of network security concerns that must be addressed with respect to security? • Question 22 What is the result of the binary number 00000000 ANDed with 00101010? • Question 23 In the textbook, which of the following is not listed among the most common external threats to networks? • Question 24 The seven OSI model layers are more often referred to by number rather than by name. Which layer number is the session layer in the OSI model? • Question 25 UDP is a reliable protocol, whereas TCP does not provide reliability. • Question 26 Which type of traffic must receive the highest priority from QoS? • Question 27 To identify a target application in a data stream, the transport layer assigns each application an identifier known as a(n) ___________________. • Question 28 According to the textbook, a ______________________ network is one that limits the impact of a failure so that the fewest number of devices are affected by it. • Question 29 A scalable network can expand quickly to support new users and applications without impacting the performance of the service being delivered to existing users. • Question 30 ________________ is the name given to the clock signal that occurs evenly spaced time durations during which data signals are sent in synchronous transmissions. • Question 31 What is the IPv6 DHCP message that corresponds to the IPv4 DHCPACK message? • Question 32 Which of the following is not a characteristic of single-mode fiber? • Question 33 Which of the following is not a factor that needs to be considered when designing a small network? • Question 34 Just above the physical layer is the _________________ layer. • Question 35 What is the hexadecimal equivalent of the decimal number 68? • Question 36 Which field in an Ethernet frame is used for error detection? • Question 37 When a host sends messages using a one-to-many delivery option, it is known as a ____________________. • Question 38 Global configuration mode and interface configuration modes can only be reached from the User EXEC mode. • Question 39 What is the binary equivalent of the decimal number 128? • Question 40 Which protocol enables clients to retrieve email from a mail server and downloads email from the mail server to the desktop? • Question 41 What is the binary equivalent of the decimal number 119? • Question 42 How many hosts per network can you have with a subnet mask of 255.255.224.0? • Question 43 Which of the following is not a way of ensuring confidentiality in a network? • Question 44 The local routing table of a host typically contains a route to the loopback interface (127.0.0.1). This address is known as a ______________________. • Question 45 The further a device is from a wireless access point, the stronger the wireless signal it receives. • Question 46 The function of the _________ layer is to facilitate the transport of data from one network to another. • Question 47 Which of the following is a characteristic of Cat7 cable? • Question 48 ________________________ is technology that is integrated into everyday appliances, allowing them to interconnect with other devices, making them more automated. • Question 49 According to the textbook, throughput usually does not match the specified bandwidth in physical layer implementations. • Question 50 According to the textbook, when a banner is used on an IOS device, it should always welcome someone to the device as its first statement. • Question 51 You are given an IPv4 network address of 192.168.10.0/24 by your ISP. You need to subnet this network. You know that the subnet mask will be 255.255.255.252. What is the last usable host address of the first subnet (i.e. subnet[0])? • Question 52 The _____________ command is used to verify the internal IP configuration on a local host. • Question 53 Which Wi-Fi standard operates in the 2.4-GHz frequency band and offers speeds of up to 11 Mbps? • Question 54 Which of the following data communications standards apply to wireless media? I. IEEE 802.11 II. IEEE 802.15 III. IEEE 802.16 • Question 55 What command(s) is(are) used to take a device from privileged EXEC mode to the global configuration mode? • Question 56 You have been assigned an IP address for your network of 192.168.1.0 / 24. Each subnet needs to accommodate 12 hosts. What is the subnet mask? • Question 57 The term ________________ refers to a private connection of LANs and WANs that belongs to an organization and is designed to be accessible only by the organization’s members, employees, or others with authorization. • Question 58 A(n) ______ firewall consists of a firewall application that runs on a network operating system such as UNIX or Windows. • Question 59 What is the decimal equivalent of the hexadecimal number AA? • Question 60 A(n) _______________________ transmission exists when data signals are transmitted without an associated clock signal. • Question 61 _________________ is a protocol that governs the way that a web server and a web client interact. • Question 62 What is the decimal equivalent of the hexadecimal number EA? • Question 63 Controlled access is also known as ______. • Question 64 When data travels from a source node to a destination node, the user data is first segmented by the _________ layer, placed into packets by the _________ layer, and further encapsulated as frames by the _____________ layer. • Question 65 Which of the following firewall techniques blocks unsolicited packets unless permitted specifically? • Question 66 Shining a bright flashlight into one end of a fiber cable while observing the visible light at the other end of the fiber ensures the performance of the fiber. • Question 67 When a sender does not receive an acknowledgement from a TCP transmission within a certain period of time, what happens? • Question 68 Which IPv4 block of addresses is reserved for future use and is currently being used for research and experimentation purposes? • Question 69 _____________________________occurs in fiber-optic media when the media do not completely touch at the splice or connection. • Question 70 Which of the following organizations developed standard ISO 8877, which officially adopted the RJ connections such as RJ-11 and RJ-45? • Question 71 _______________________ communication relies on unidirectional data flow, where sending and receiving data are not performed at the same time. • Question 72 __________ enables the automatic assignment of addressing information such as IP address, subnet mask, default gateway, and other configuration information. • Question 73 What is the IPv6 DHCP message that corresponds to the IPv4 DHCPOFFER message? • Question 74 In Ethernet technology, IP addresses are used to identify the frame source and destination. • Question 75 When an incoming data frame is received by a switch and the destination MAC address is not found in the MAC address table, the switch forwards the frame out all ports, except for the port on which it was received. [Show More]
Last updated: 1 year ago
Preview 1 out of 15 pages
Reviews( 0 )
Recommended For You
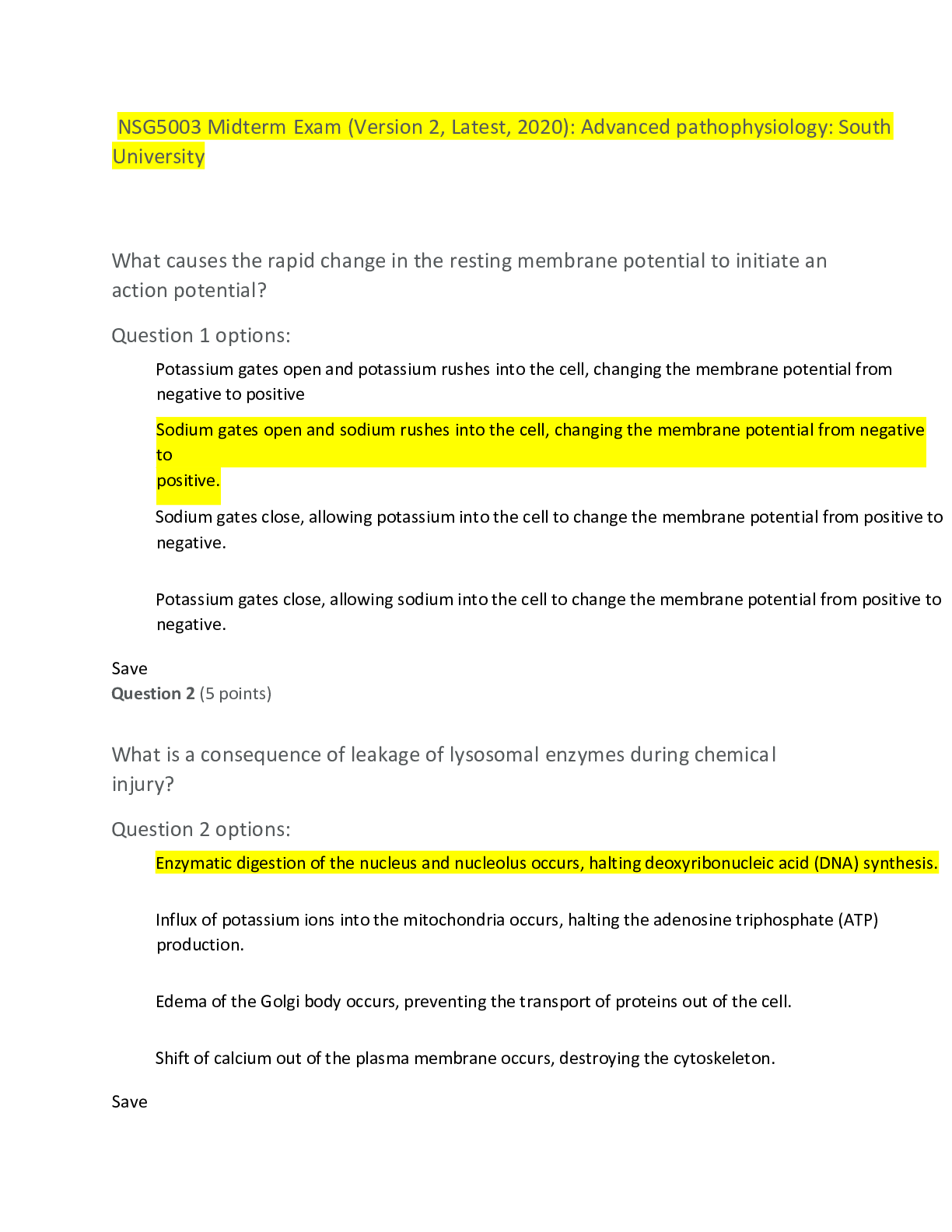
Health Care> EXAM > NSG5003 Midterm Exam (Version 2, Latest, 2020): Advanced pathophysiology : South University (100% Correct Q & A) (All)
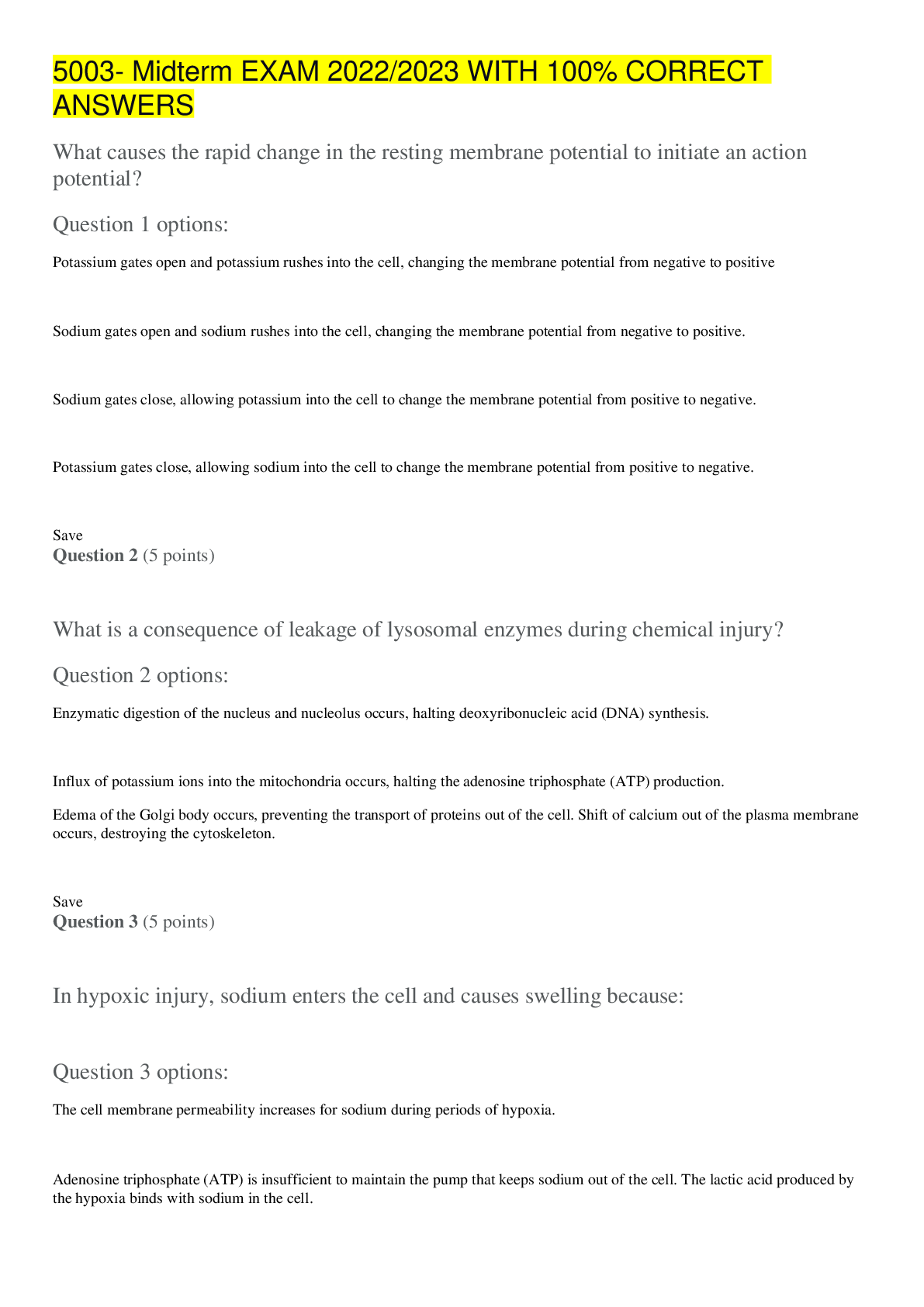
NSG5003 Midterm Exam (Version 2, Latest, 2020): Advanced pathophysiology : South University (100% Correct Q & A)
NSG5003 Midterm Exam (Version 2, Latest, 2020): Advanced pathophysiology : South University (100% Correct Q & A)NSG5003 Midterm Exam (Version 2, Latest, 2020): Advanced pathophysiology : South Univers...
By Otieno , Uploaded: Oct 16, 2022
$15
Health Care> EXAM > NSG5003 Midterm Exam (Version 2, Latest, 2020): Advanced pathophysiology : South University (100% Correct Q & A) (All)
.png)
NSG5003 Midterm Exam (Version 2, Latest, 2020): Advanced pathophysiology : South University (100% Correct Q & A)
NSG5003 Midterm Exam (Version 2, Latest, 2020): Advanced pathophysiology : South University (100% Correct Q & A)NSG5003 Midterm Exam (Version 2, Latest, 2020): Advanced pathophysiology : South Univers...
By DOCTOR BEN , Uploaded: Oct 17, 2022
$14
Health Care> EXAM > NSG5003 Midterm Exam (Version 2, Latest, 2020): Advanced pathophysiology : South University (100% Correct Q & A) (All)
.png)
NSG5003 Midterm Exam (Version 2, Latest, 2020): Advanced pathophysiology : South University (100% Correct Q & A)
NSG5003 Midterm Exam (Version 2, Latest, 2020): Advanced pathophysiology : South University (100% Correct Q & A)NSG5003 Midterm Exam (Version 2, Latest, 2020): Advanced pathophysiology : South Univers...
By IMMANUEL , Uploaded: Oct 17, 2022
$15
Health Care> EXAM > NSG5003 Midterm Exam (Version 2, Latest, 2020): Advanced pathophysiology : South University (100% Correct Q & A) (All)
.png)
NSG5003 Midterm Exam (Version 2, Latest, 2020): Advanced pathophysiology : South University (100% Correct Q & A)
NSG5003 Midterm Exam (Version 2, Latest, 2020): Advanced pathophysiology : South University (100% Correct Q & A)NSG5003 Midterm Exam (Version 2, Latest, 2020): Advanced pathophysiology : South Univers...
By Doctor Immanuel , Uploaded: Oct 17, 2022
$15
*NURSING> EXAM > NSG5003 Midterm Exam (Version 2, Latest, (All)
NSG5003 Midterm Exam (Version 2, Latest,
NSG5003 Midterm Exam (Version 2, Latest, 2020)
By MrMase , Uploaded: Jun 24, 2023
$10
*NURSING> EXAM > NSG5003 Midterm Exam (Version 2, Latest, 2023) (All)
NSG5003 Midterm Exam (Version 2, Latest, 2023)
NSG5003 Midterm Exam (Version 2, Latest, 2023)
By Clem11doc , Uploaded: Aug 19, 2023
$16
*NURSING> EXAM > NSG5003 Midterm Exam (Version 2, Latest, 2023) (All)
NSG5003 Midterm Exam (Version 2, Latest, 2023)
NSG5003 Midterm Exam (Version 2, Latest, 2023)
By mcJay , Uploaded: Aug 19, 2023
$11
*NURSING> EXAM > NSG5003 Midterm Exam (Version 2, Latest, 2023) (All)
NSG5003 Midterm Exam (Version 2, Latest, 2023)
NSG5003 Midterm Exam (Version 2, Latest, 2023) Document Description *:
By chamberlain , Uploaded: Aug 15, 2023
$16
*NURSING> EXAM > NSG5003 Midterm Exam (Version 2, Latest, 2023) (All)
NSG5003 Midterm Exam (Version 2, Latest, 2023)
NSG5003 Midterm Exam (Version 2, Latest, 2023)
By oxlade , Uploaded: Aug 19, 2023
$13
*NURSING> EXAM > NSG5003 Midterm Exam (Version 2, Latest, 2023) (All)
NSG5003 Midterm Exam (Version 2, Latest, 2023)
NSG5003 Midterm Exam (Version 2, Latest, 2023)
By Thirty3 , Uploaded: Aug 19, 2023
$14
Document information
Connected school, study & course
About the document
Uploaded On
Feb 08, 2020
Number of pages
15
Written in
Additional information
This document has been written for:
Uploaded
Feb 08, 2020
Downloads
1
Views
146