Engineering > EXAM > PCI-DSS ISA Exam QUESTIONS AND ANSWERS 2022 (All)
PCI-DSS ISA Exam QUESTIONS AND ANSWERS 2022
Document Content and Description Below
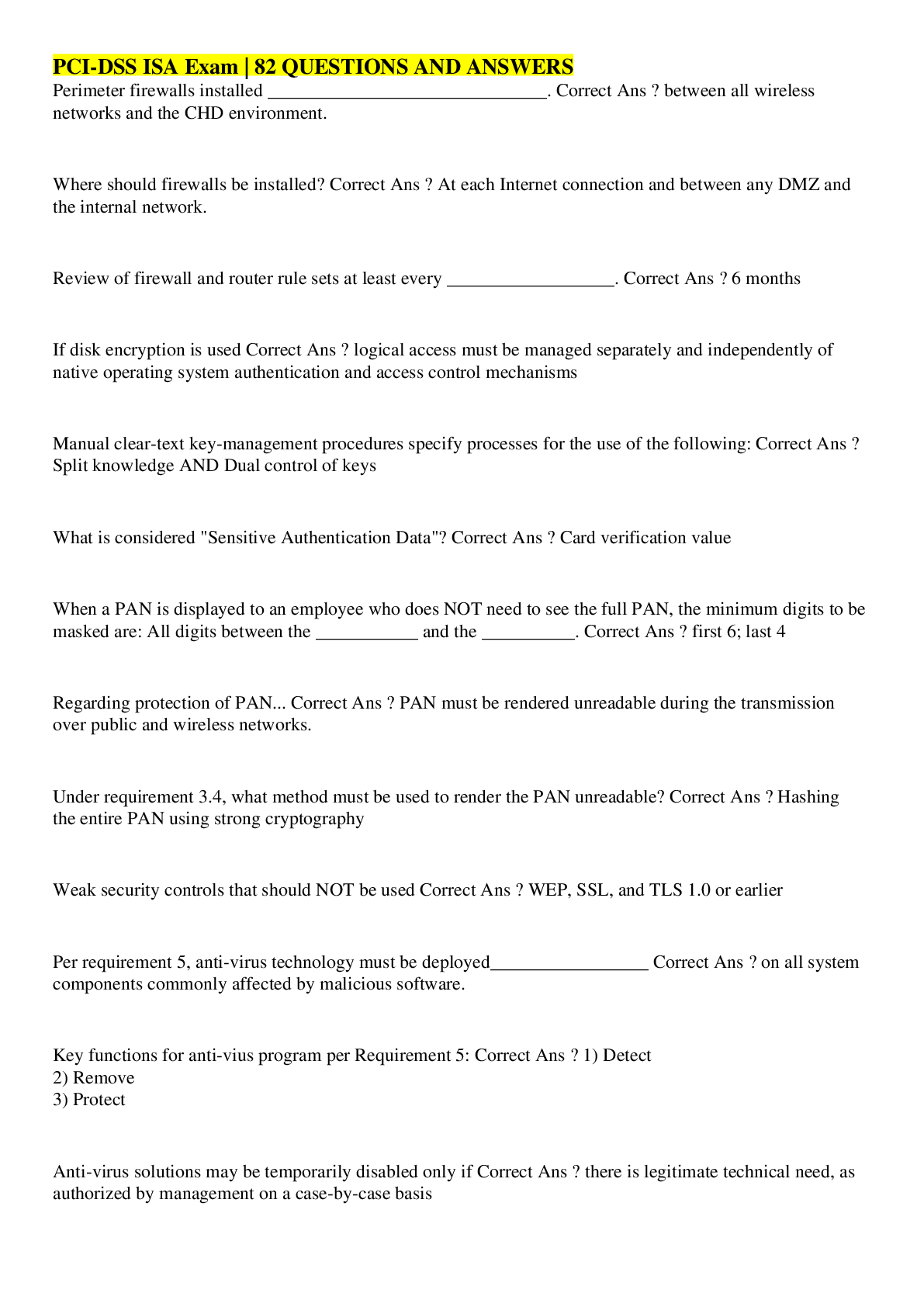
Perimeter firewalls installed ______________________________. between all wireless networks and the CHD environment. Where should firewalls be installed? At each Internet connection and betwe... en any DMZ and the internal network. Review of firewall and router rule sets at least every __________________. 6 months If disk encryption is used logical access must be managed separately and independently of native operating system authentication and access control mechanisms Manual clear-text key-management procedures specify processes for the use of the following: Split knowledge AND Dual control of keys What is considered "Sensitive Authentication Data"? Card verification value When a PAN is displayed to an employee who does NOT need to see the full PAN, the minimum digits to be masked are: All digits between the ___________ and the __________. first 6; last 4 Regarding protection of PAN... PAN must be rendered unreadable during the transmission over public and wireless networks. Under requirement 3.4, what method must be used to render the PAN unreadable? Hashing the entire PAN using strong cryptography Weak security controls that should NOT be used WEP, SSL, and TLS 1.0 or earlier Per requirement 5, anti-virus technology must be deployed_________________ on all system components commonly affected by malicious software. Key functions for anti-vius program per Requirement 5: 1) Detect 2) Remove 3) Protect Anti-virus solutions may be temporarily disabled only if there is legitimate technical need, as authorized by management on a case-by-case basis When to install "critical" applicable vendor-supplied security patches? ---> within _________ of release. 1 month When to install applicable vendor-supplied security patches? within an appropriate time frame (for example, within three months). When assessing requirement 6.5, testing to verify secure coding techniques are in place to address common coding vulnerabilities includes: Reviewing software development policies and procedures Requirements 7 restricted access controls by: Need-to-know and least privilege Inactive accounts over _____________days need to be removed or disabled. 90 days To verify user access termination policy, an ISA need to select a sample of user terminated in the past _______________ months, and review current user access lists—for both local and remote access—to verify that their IDs have been deactivated or removed from the access lists. 6 months How many logon attempts should be allowed until resulting temporarily account locked-out? 6 attempts Once user account is locked-out, it will remain locked for a minimum of ________________________ or until a system administrator resets the account. 30 minutes System/session idle time out must be set to_________ minutes or less. 15 minutes What are the methods to authenticate users? - "Something you know", such as a password or passphrase - "Something you have", such as a token device or smart card, or - "Something you are", such as a biometric. Where passwords or pass-phrases are used, they must be at least _______ characters long and contain both numeric and alphabetic characters. 7 Passwords must be changed at least once every__________________. 90 days Password history must also be in place to ensure that users' ________ previous passwords can't be re-used. 4 An example of a "one-way" cryptographic function used to render data unreadable is: SHA-2 Data from video cameras and/or access control mechanisms is reviewed, and that data is stored for at least ________________. 3 months The visitor logs must contain the relevant information and be retained for at least_________________. 3 months Verify that the storage location security is reviewed at least ____________________ to confirm that backup media storage is secure. annually [Show More]
Last updated: 1 year ago
Preview 1 out of 5 pages
Reviews( 1 )

by anthony f dennis · 1 year ago
Document information
Connected school, study & course
About the document
Uploaded On
Oct 13, 2022
Number of pages
5
Written in
Additional information
This document has been written for:
Uploaded
Oct 13, 2022
Downloads
1
Views
178


 Leadership ATI correctly answered to pass.png)