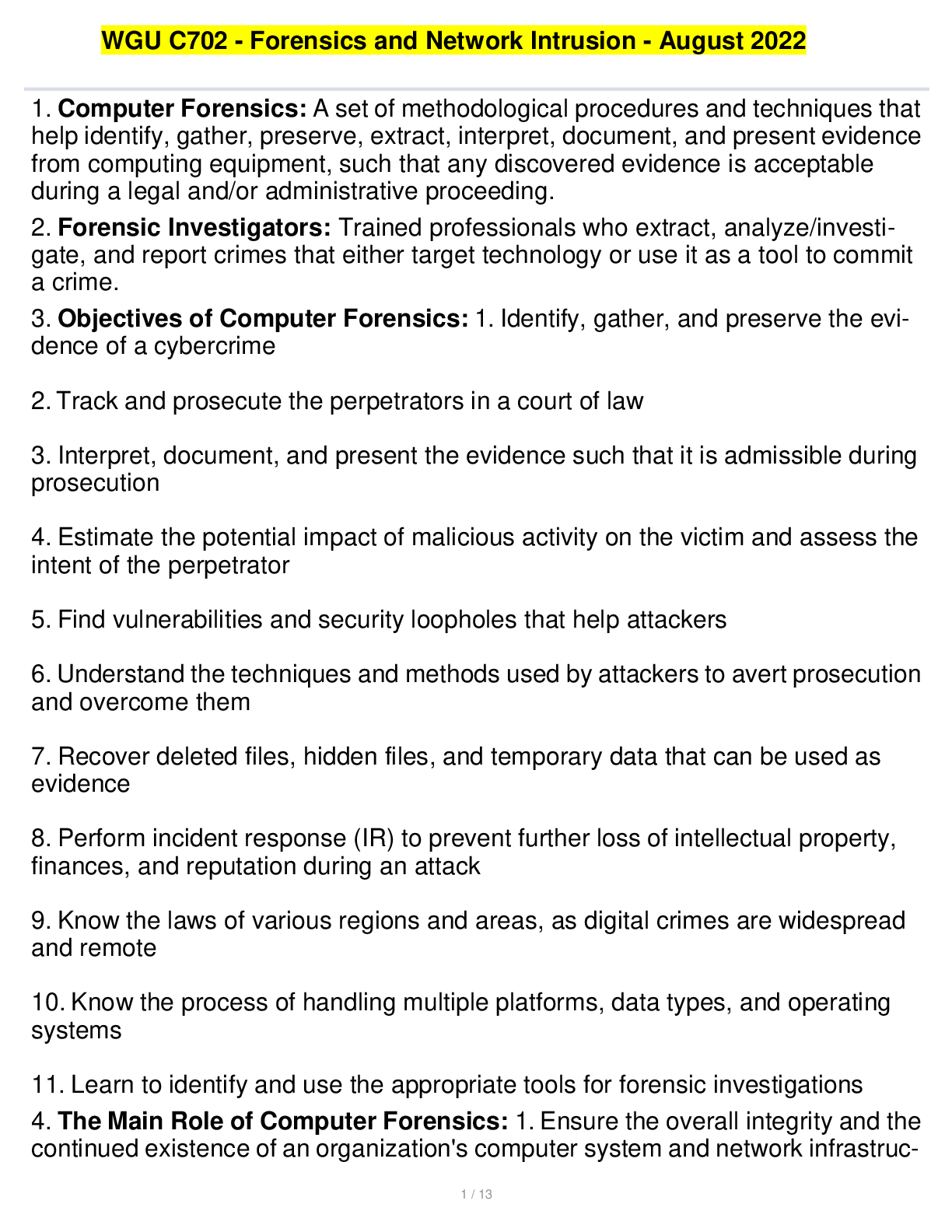
WGU C702 - Forensics and Network Intrusion - August 2022
Document Content and Description Below
1. Computer Forensics: A set of methodological procedures and techniques that help identify, gather, preserve, extract, interpret, document, and present evidence from computing equipment, such that an... y discovered evidence is acceptable during a legal and/or administrative proceeding. 2. Forensic Investigators: Trained professionals who extract, analyze/investi- gate, and report crimes that either target technology or use it as a tool to commit a crime. 3. Objectives of Computer Forensics: 1. Identify, gather, and preserve the evi- dence of a cybercrime 2. Track and prosecute the perpetrators in a court of law 3. Interpret, document, and present the evidence such that it is admissible during prosecution 4. Estimate the potential impact of malicious activity on the victim and assess the intent of the perpetrator 5. Find vulnerabilities and security loopholes that help attackers 6. Understand the techniques and methods used by attackers to avert prosecution and overcome them 7. Recover deleted files, hidden files, and temporary data that can be used as evidence 8. Perform incident response (IR) to prevent further loss of intellectual property, finances, and reputation during an attack 9. Know the laws of various regions and areas, as digital crimes are widespread and remote 10. Know the process of handling multiple platforms, data types, and operating systems 11. Learn to identify and use the appropriate tools for forensic investigations 4. The Main Role of Computer Forensics: 1. Ensure the overall integrity and the continued existence of an organization's computer system and network infrastruc- ture 2. Help the organization capture important information if their computer systems or networks are compromised. Forensic evidence also helps prosecute the perpe- trator of a cybercrime, if caught. 3. Extract, process, and interpret the actual evidence so that it proves the attacker's actions and their guilt or innocence in court 4. Efficiently track down perpetrators/terrorists from different parts of the world. Terrorists who use the Internet as a communication medium can be tracked down, and their plans can be discovered. IP addresses are vital to finding the geographical location of the terrorists. 5. Save the organization's money and valuable time. Many managers allocate a large portion of their IT budget for computer and network security. 6. Track complex cases such as email spamming and other nefarious activities, etc. 5. Why should computer forensics be used?: 1. Prepare for incidents in ad- vance to ensure the integrity and continuity of network infrastructure 2. Identify and gather evidence of cybercrimes in a forensically sound manner 3. Offer ample protection to data resources and ensure regulatory compliance 4. Protect the organization from similar incidents in the future 5. Help counteract online [Show More]
Last updated: 1 year ago
Preview 1 out of 13 pages
Instant download
Buy this document to get the full access instantly
Instant Download Access after purchase
Add to cartInstant download
Reviews( 0 )
Document information
Connected school, study & course
About the document
Uploaded On
Oct 14, 2022
Number of pages
13
Written in
Additional information
This document has been written for:
Uploaded
Oct 14, 2022
Downloads
0
Views
34

.png)
.png)



.png)
.png)

