Computer Networking > QUESTIONS & ANSWERS > PNSCE - Firewall 10.0: WildFire Versus Malware Exam Questions with Correct Answers (All)
PNSCE - Firewall 10.0: WildFire Versus Malware Exam Questions with Correct Answers
Document Content and Description Below
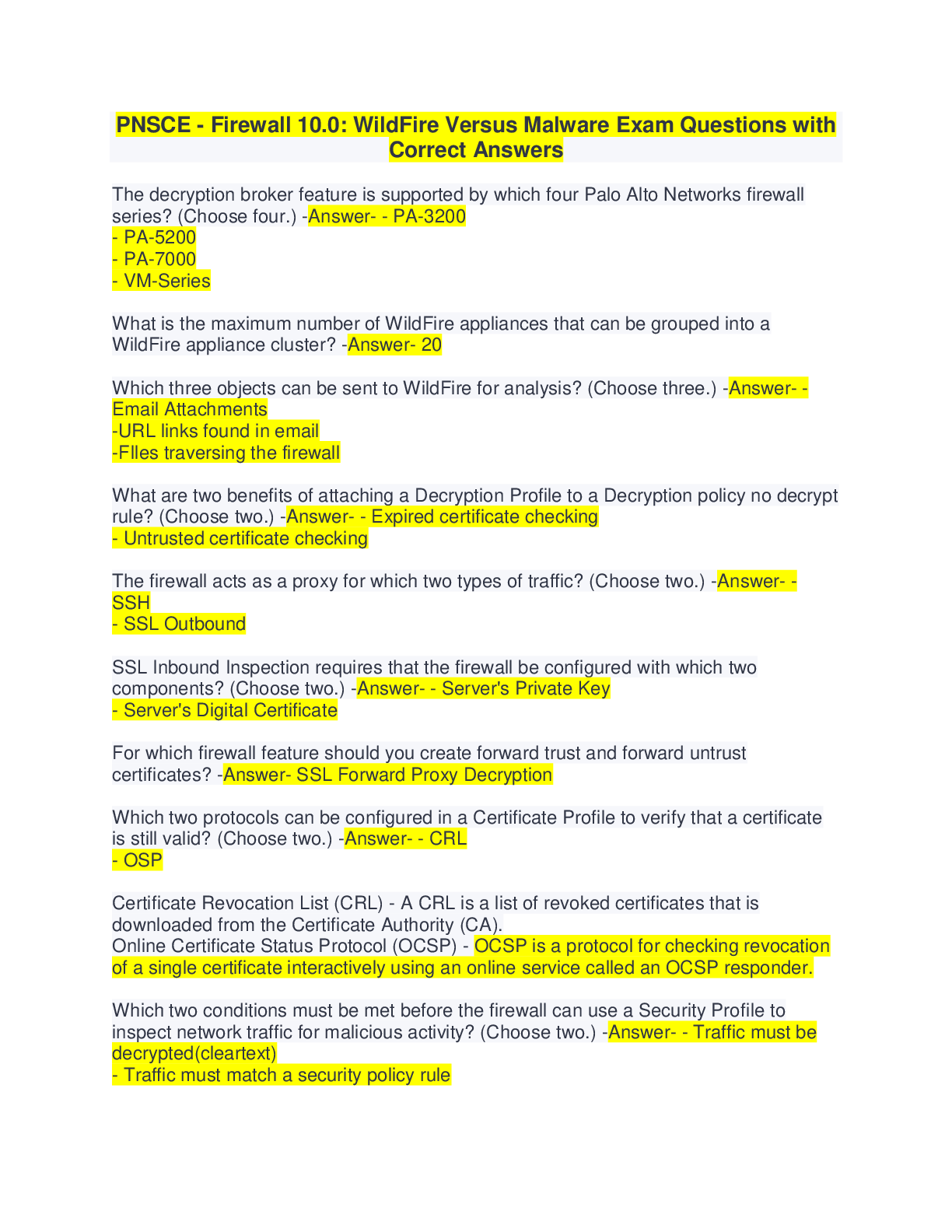
PNSCE - Firewall 10.0: WildFire Versus Malware Exam Questions with Correct Answers The decryption broker feature is supported by which four Palo Alto Networks firewall series? (Choose four.) -Answe... r- - PA-3200 - PA-5200 - PA-7000 - VM-Series What is the maximum number of WildFire appliances that can be grouped into a WildFire appliance cluster? -Answer- 20 Which three objects can be sent to WildFire for analysis? (Choose three.) -Answer- -Email Attachments -URL links found in email -FIles traversing the firewall What are two benefits of attaching a Decryption Profile to a Decryption policy no decrypt rule? (Choose two.) -Answer- - Expired certificate checking - Untrusted certificate checking The firewall acts as a proxy for which two types of traffic? (Choose two.) -Answer- - SSH - SSL Outbound SSL Inbound Inspection requires that the firewall be configured with which two components? (Choose two.) -Answer- - Server's Private Key - Server's Digital Certificate For which firewall feature should you create forward trust and forward untrust certificates? -Answer- SSL Forward Proxy Decryption Which two protocols can be configured in a Certificate Profile to verify that a certificate is still valid? (Choose two.) -Answer- - CRL - OSP Certificate Revocation List (CRL) - A CRL is a list of revoked certificates that is downloaded from the Certificate Authority (CA). Online Certificate Status Protocol (OCSP) - OCSP is a protocol for checking revocation of a single certificate interactively using an online service called an OCSP responder. Which two conditions must be met before the firewall can use a Security Profile to inspect network traffic for malicious activity? (Choose two.) -Answer- - Traffic must be decrypted(cleartext) - Traffic must match a security policy rule WildFire analysis is used to update which three Palo Alto Networks information sources? (Choose three.) -Answer- - Malicious Domains - Malicious IP Addresses - PAN-DB Categories Which two statements are true regarding how the firewall uses its master key? (Choose two.) -Answer- - Used to encrypt private keys - Used to encrypt local firewall account passwords Wildfire Global Threat Intelligence Cloud -Answer- Palo Alto Networks firewalls across the world automatically forward unknown files and URL links found in emails to the WildFire global threat intelligence cloud or to one of three WildFire regional clouds in Europe, Japan, and Singapore for analysis. Each WildFire cloud analyzes samples and generates malware signatures and verdicts independently of the other WildFire clouds. WildFire signatures and verdicts then are shared globally, which enables WildFire users worldwide to benefit from malware coverage regardless of the location where the malware was first detected. Wildfire Verdict -Answer- WildFire is a cloud-based, virtual sandbox used to evaluate unknown files and URL links found in emails. The evaluation occurs for: Android Linux macOS Windows XP Windows 7 Windows 10 After analysis is complete, files and links are labeled as: benign grayware malware phishing If a malware or a phishing URL is found, WildFire creates a new antivirus signature or adds the URL to the PAN-DB Phishing URL category and then makes these updates available within minutes for download by firewalls around the world. [Show More]
Last updated: 1 year ago
Preview 1 out of 19 pages
Instant download
Buy this document to get the full access instantly
Instant Download Access after purchase
Add to cartInstant download
Reviews( 0 )
Document information
Connected school, study & course
About the document
Uploaded On
Sep 05, 2022
Number of pages
19
Written in
Additional information
This document has been written for:
Uploaded
Sep 05, 2022
Downloads
0
Views
89