Top 50 AWS COMPLETE WITH ANSWERS
Document Content and Description Below
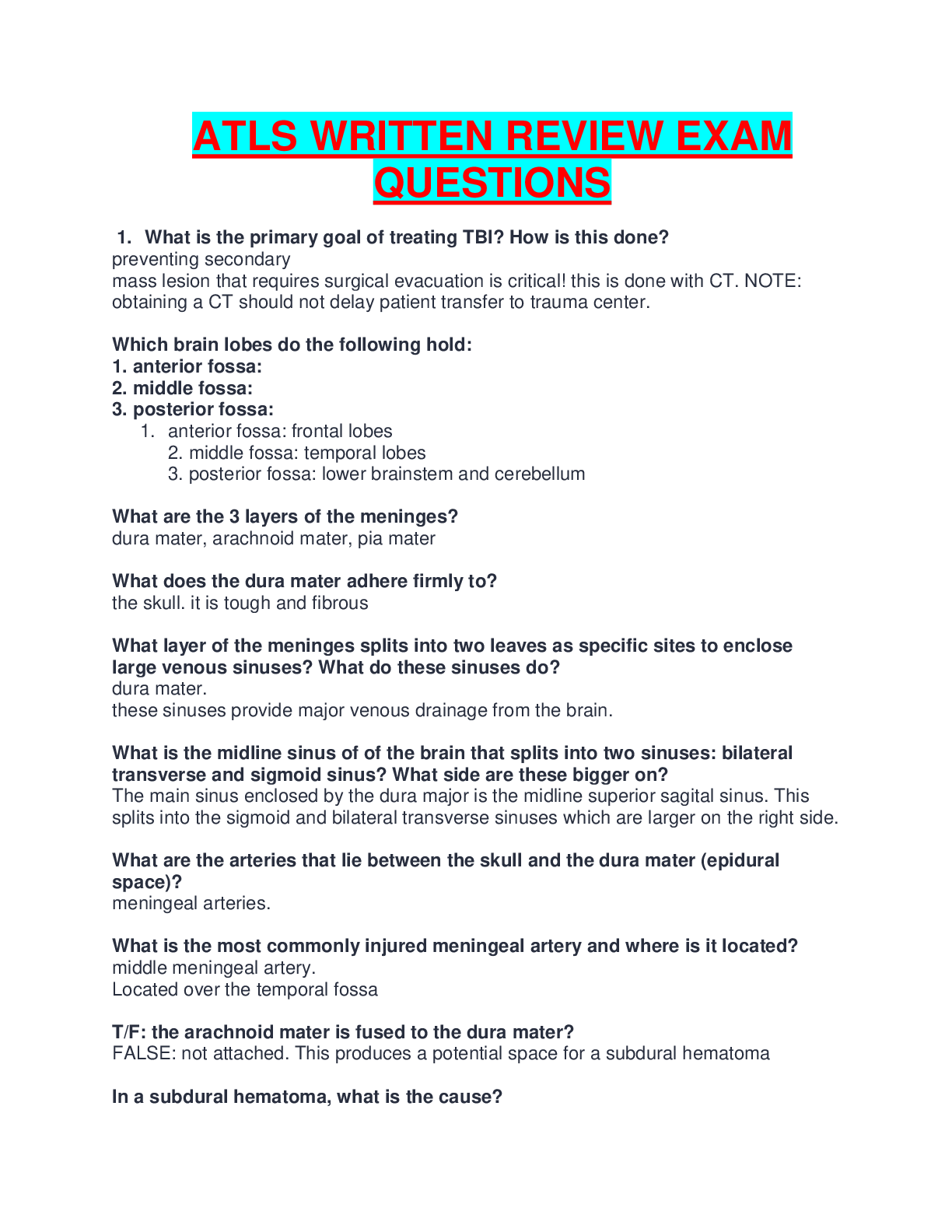
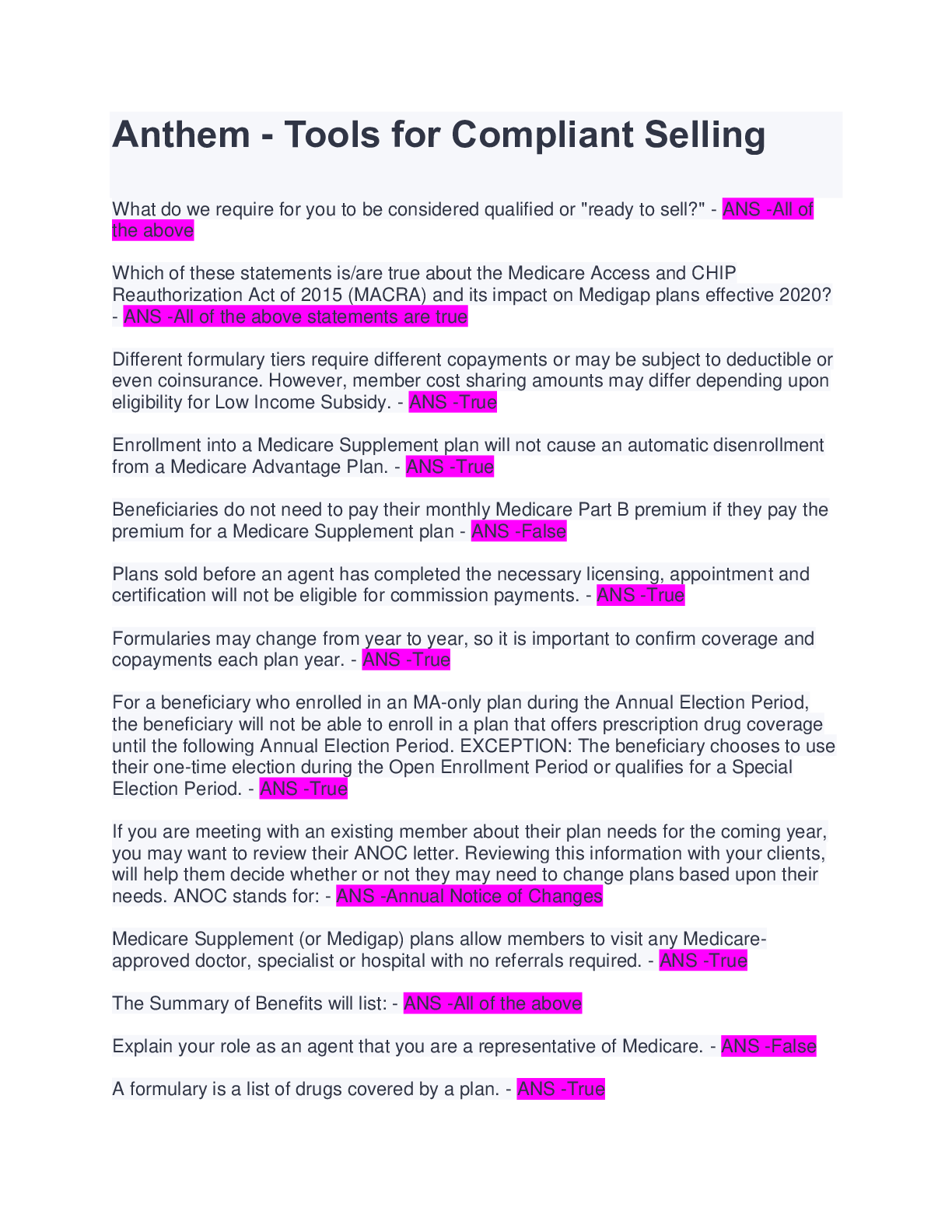
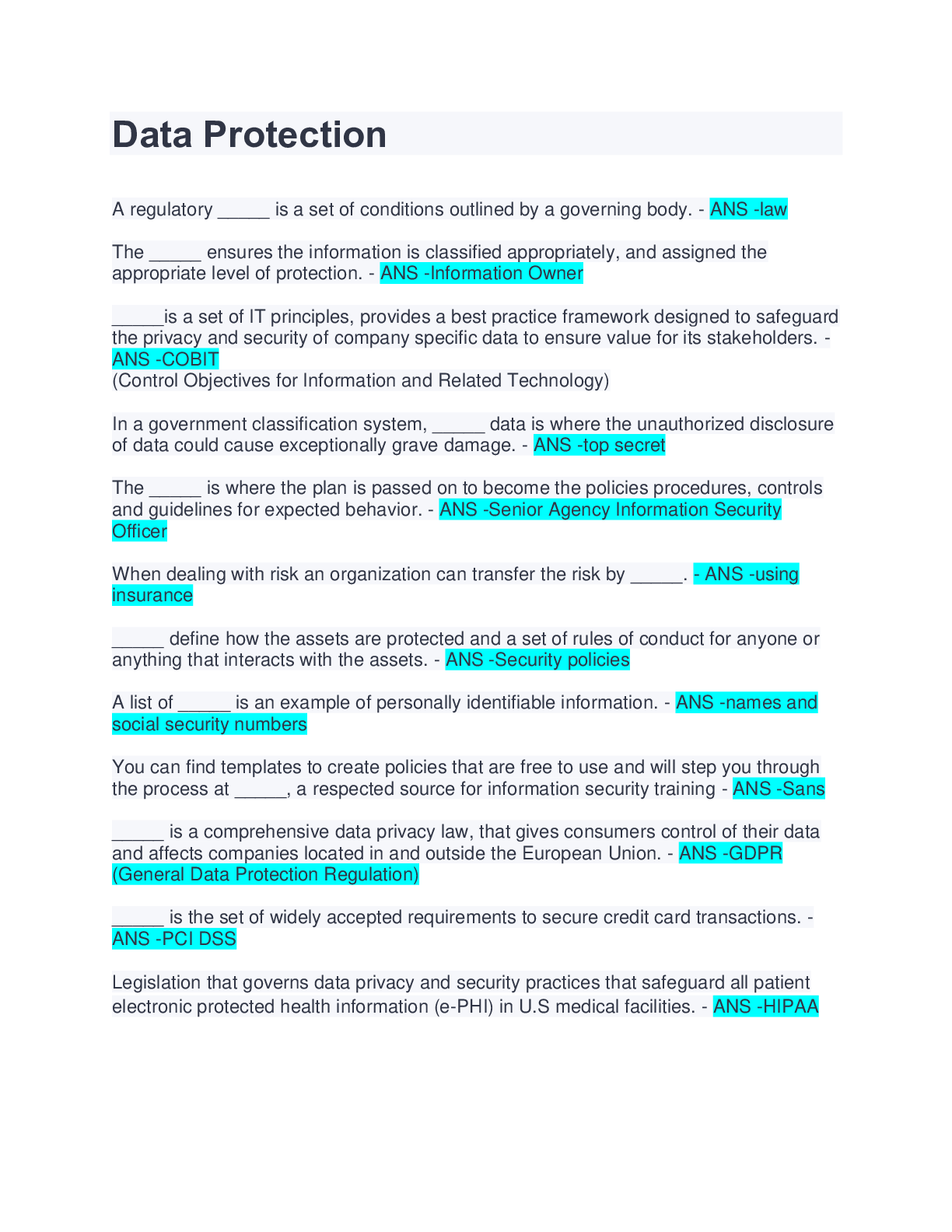
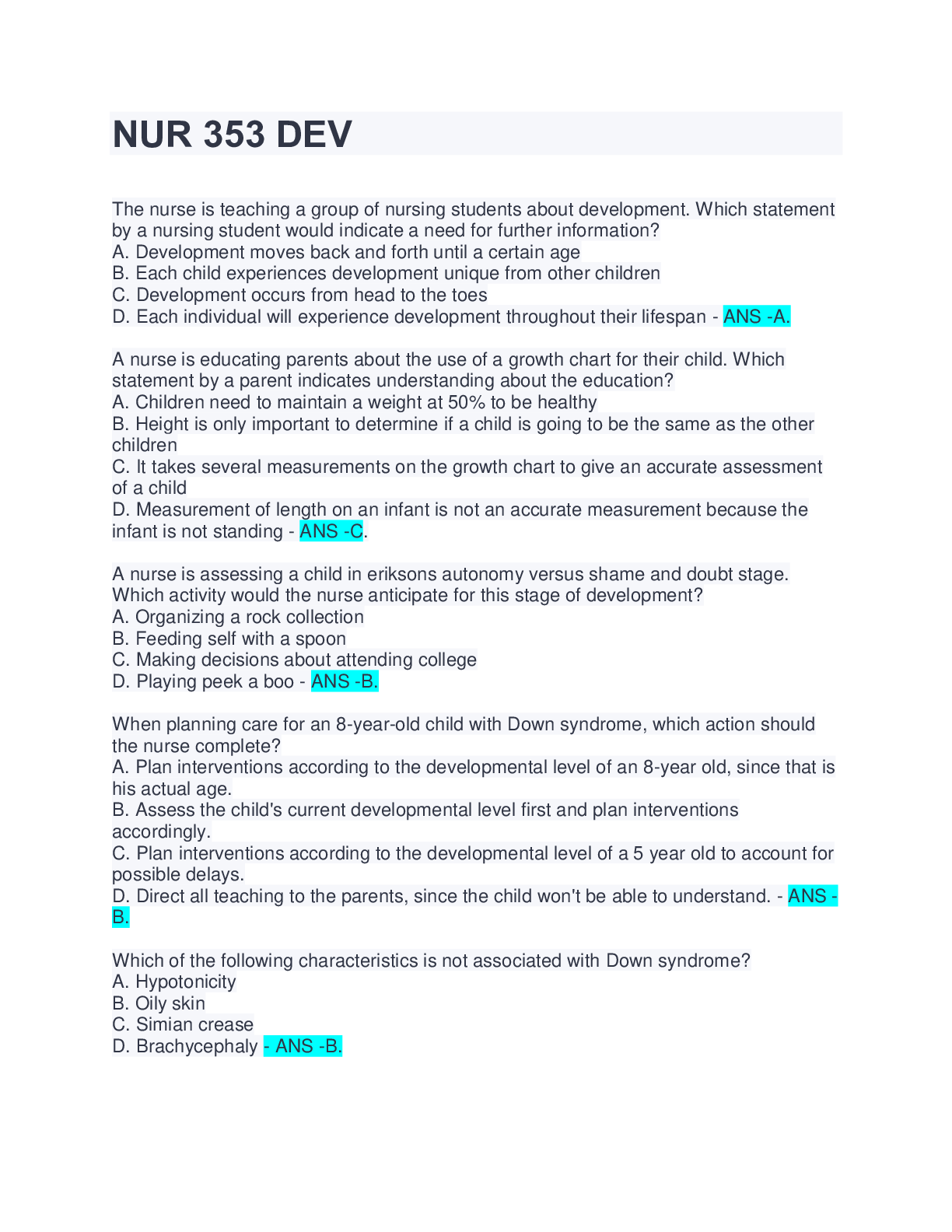
According to the terminology, AWS or Amazon Web Services is defined as a platform which is designed to provide secure cloud services, computing power to clients, database storage options, content deli... very and many other services which are all intended towards business development and growth. - ANS -Define Amazon Web Services or AWS. Amazon Route 53: This is a DNS (Domain Name Service) web service. Easy Email Service: This service allows customers and clients to address email utilization through normal SMTP or RESTFUL API. Identity and Access Management: This has been designed in order to provide heightened identity control and protection for a client's AWS account. S3 or Simple Storage Device: It is a very well-known utility among all the AWS Services and is mainly used in warehouse equipment. EC2 or Elastic Compute Cloud: This is a utility designed to manage variable workloads and gives clients the ability to afford on-demand computing sources for hosting. EBS or Elastic Block Store: This particular utility is used to expand beyond EC2 and is designed to connect EC2 to enable the lifespan of data beyond the capacities of EC2. Cloud Watch: This is mainly a crisis management utility and is designed to help managers inspect and obtain additional resources in the light of a crisis. - ANS -List out the main components of AWS. A buffer is necessary in any cloud computing technology in order to maintain seamless integration across a huge flow of traffic and loads. The Elastic Load Balancer in Amazon Web Services has been designed in a way to ensure that all the incoming traffic is optimally distributed across all channels of AWS instances. The presence of a buffer enables the components to work in an unstable situation and receive and process requests as it gets them. Essentially the presence of a buffer is needed to create an equilibrium between all the apparatus and provide them with an identical ability to supply more rapid services. - ANS -What do you know about Buffer in AWS? One of the most important aspects of cloud computing is its security. It must be ensured at all times that no individual or organization is able to seize the data of a client while in a transition from one point to another and also there shouldn't be any leakage of information from any of the several storerooms in the cloud. Thus one of the most effective ways of securing information is by segregating it and then encrypting the same [Show More]
Last updated: 1 year ago
Preview 1 out of 10 pages
Buy this document to get the full access instantly
Instant Download Access after purchase
Add to cartInstant download
We Accept:
Reviews( 0 )
$3.00
Document information
Connected school, study & course
About the document
Uploaded On
Oct 23, 2022
Number of pages
10
Written in
Additional information
This document has been written for:
Uploaded
Oct 23, 2022
Downloads
0
Views
30