Computer Science > QUESTIONS & ANSWERS > CyberRookie CSX Fundamentals - Roles in Cybersecurity Questions with Complete Answers (All)
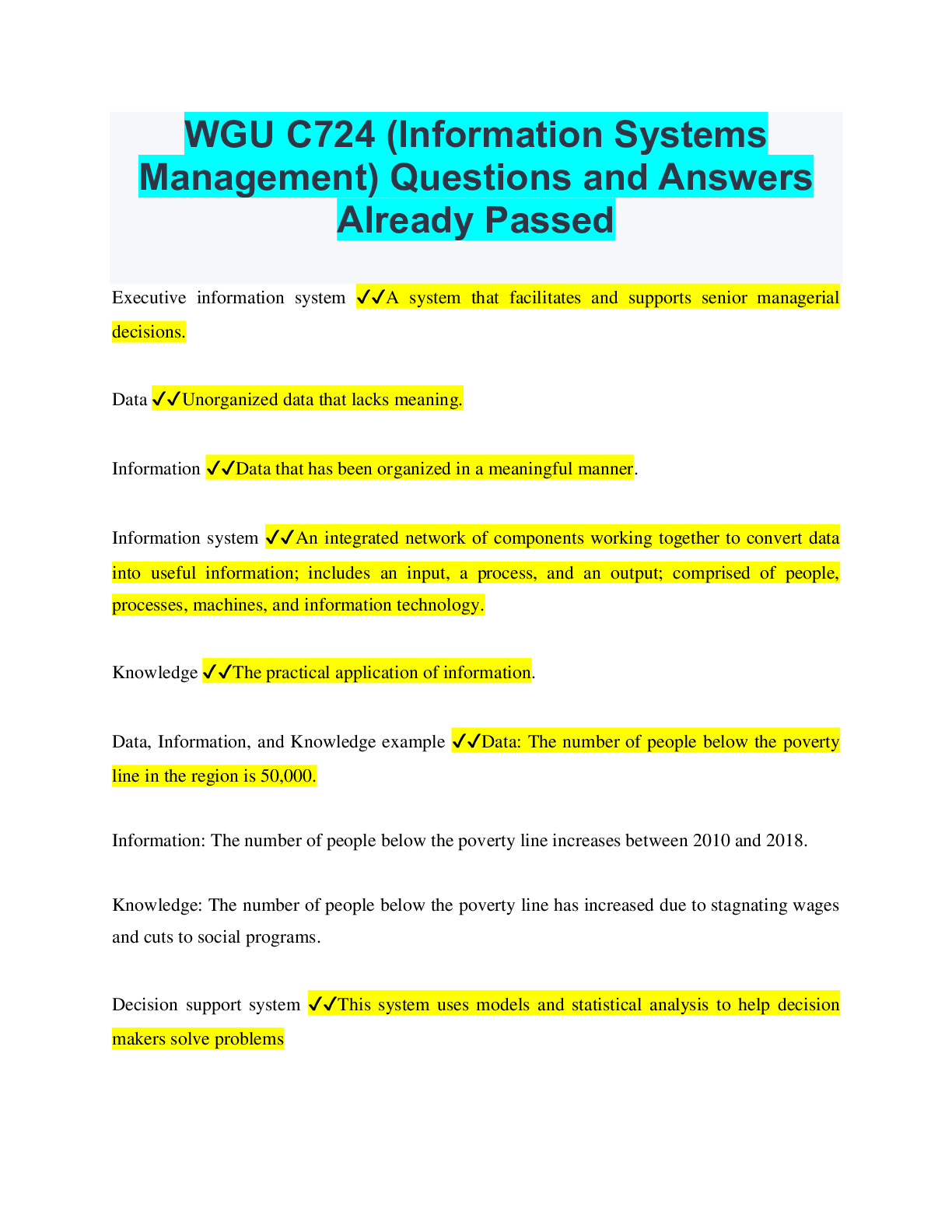
CyberRookie CSX Fundamentals - Roles in Cybersecurity Questions with Complete Answers
Document Content and Description Below
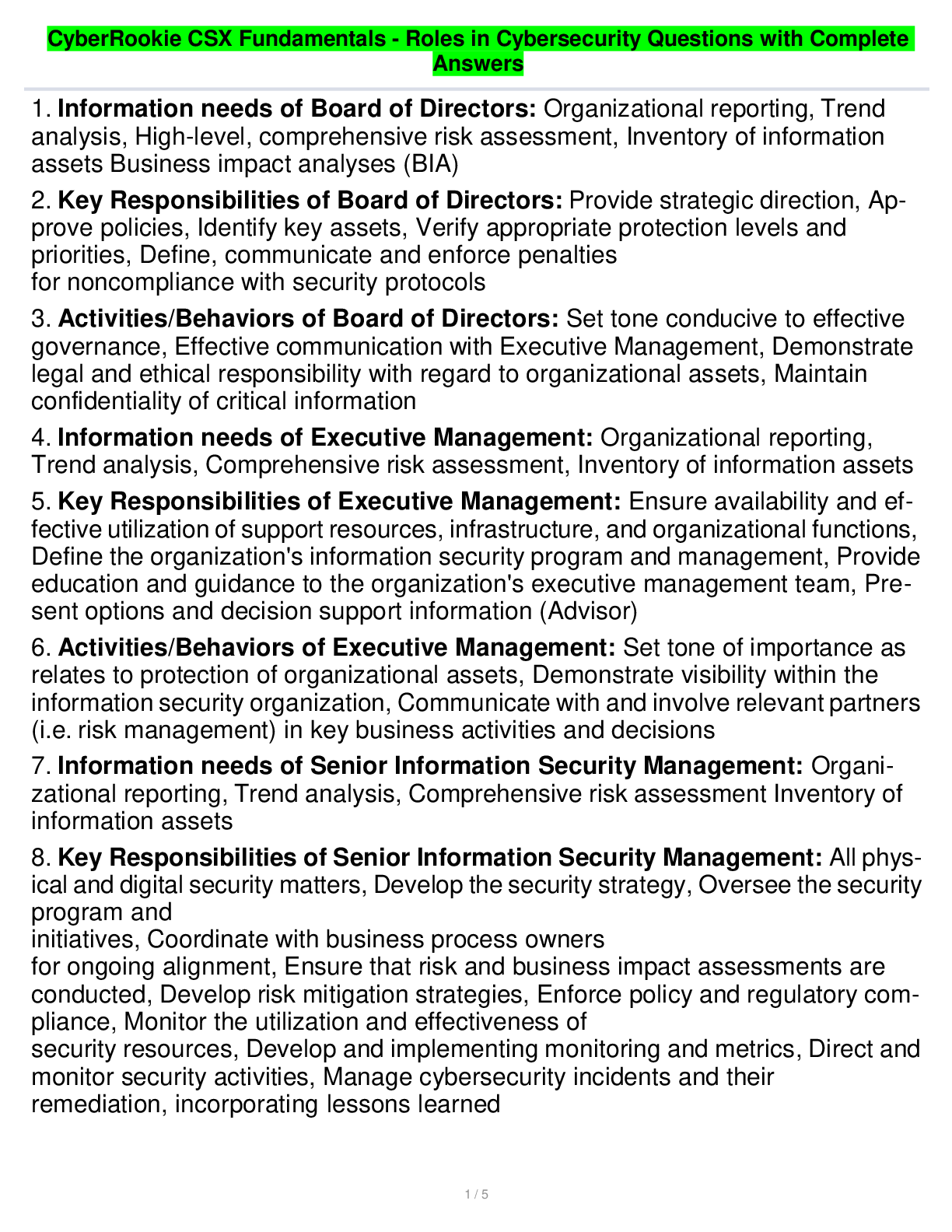
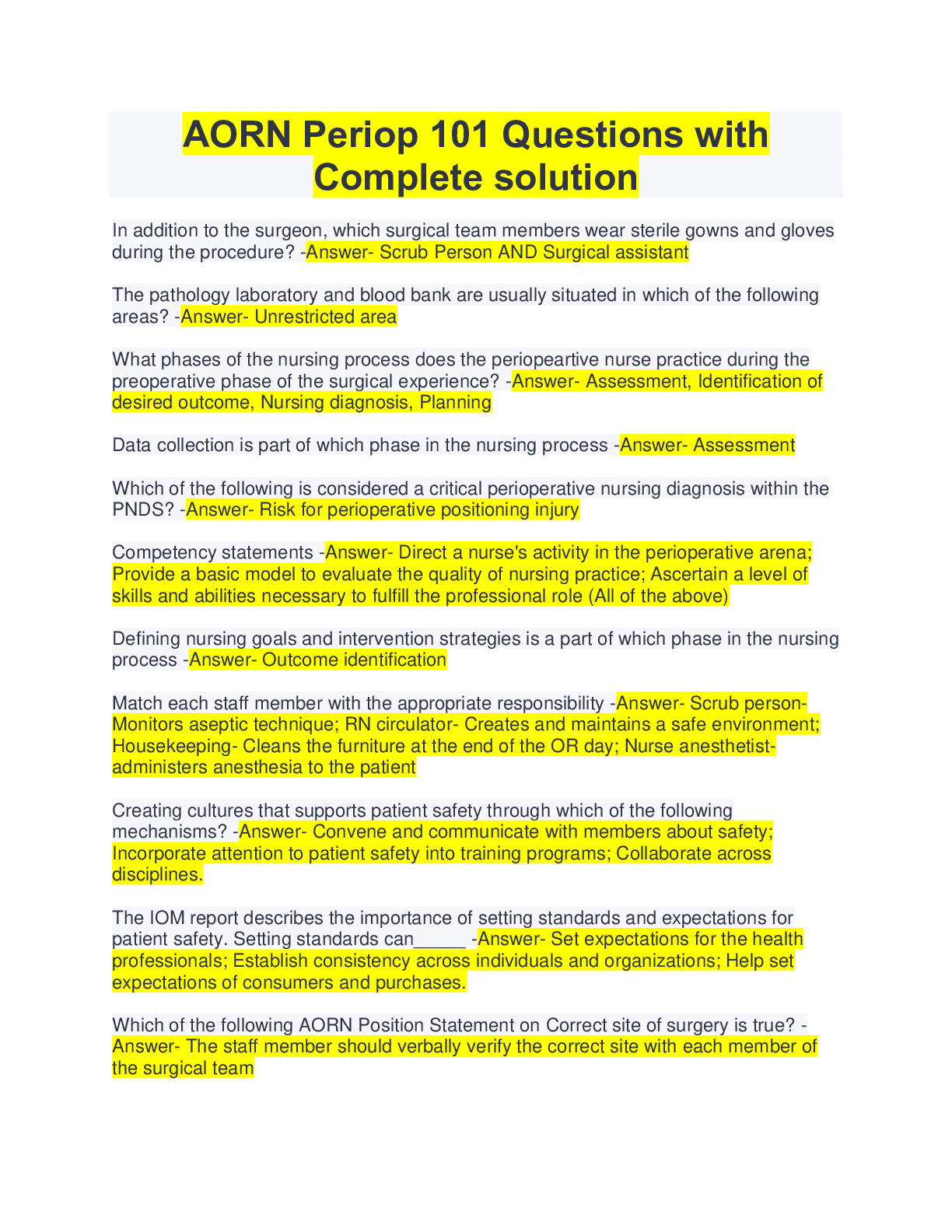
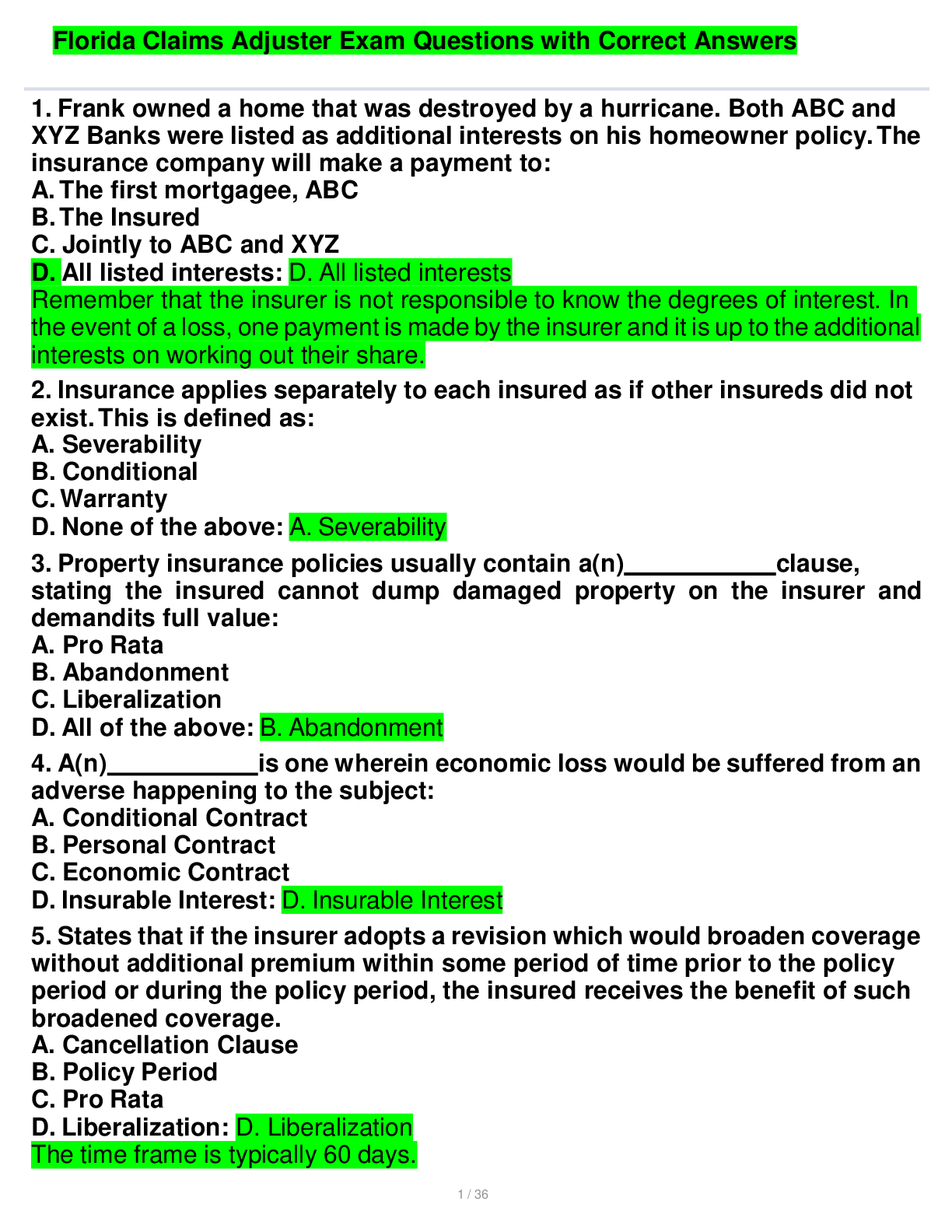
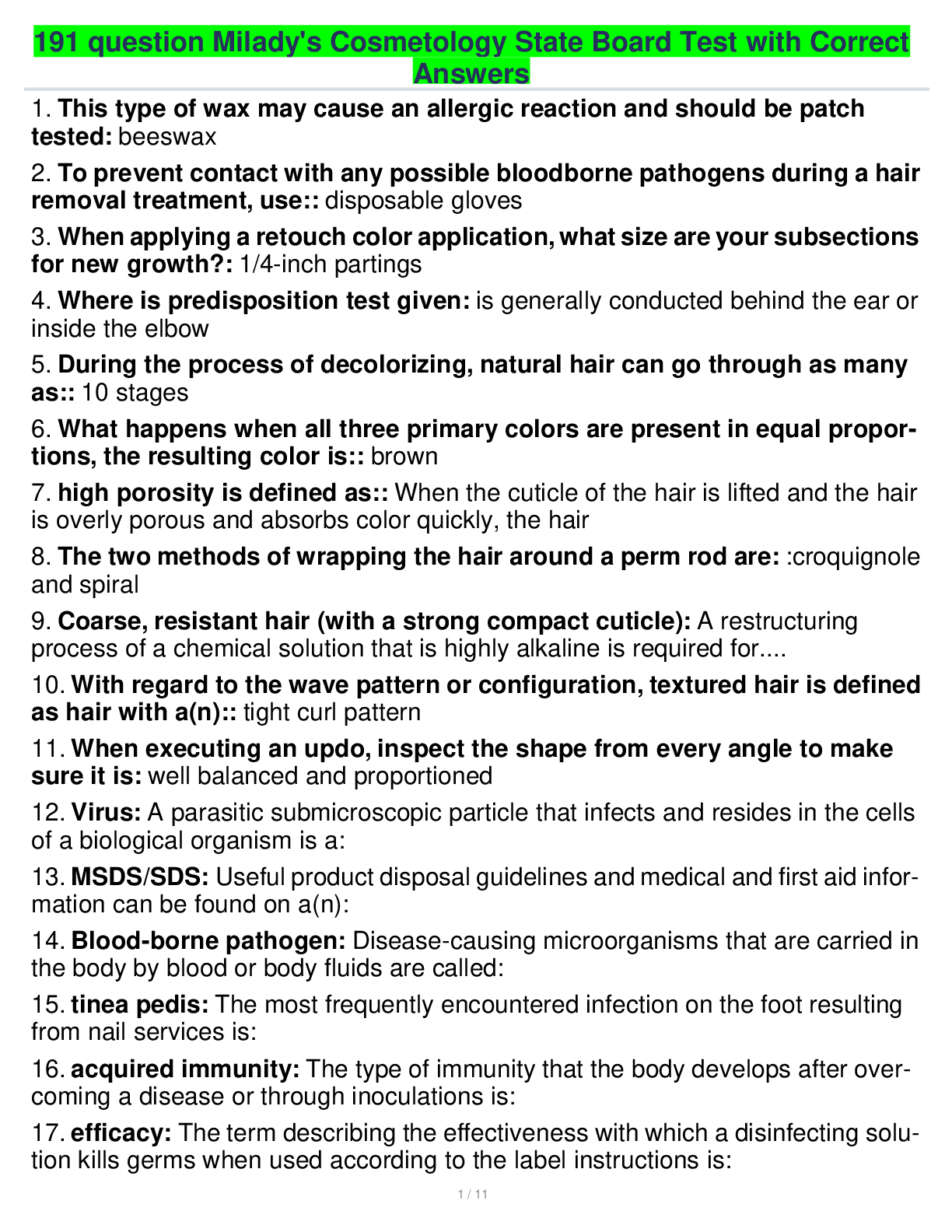
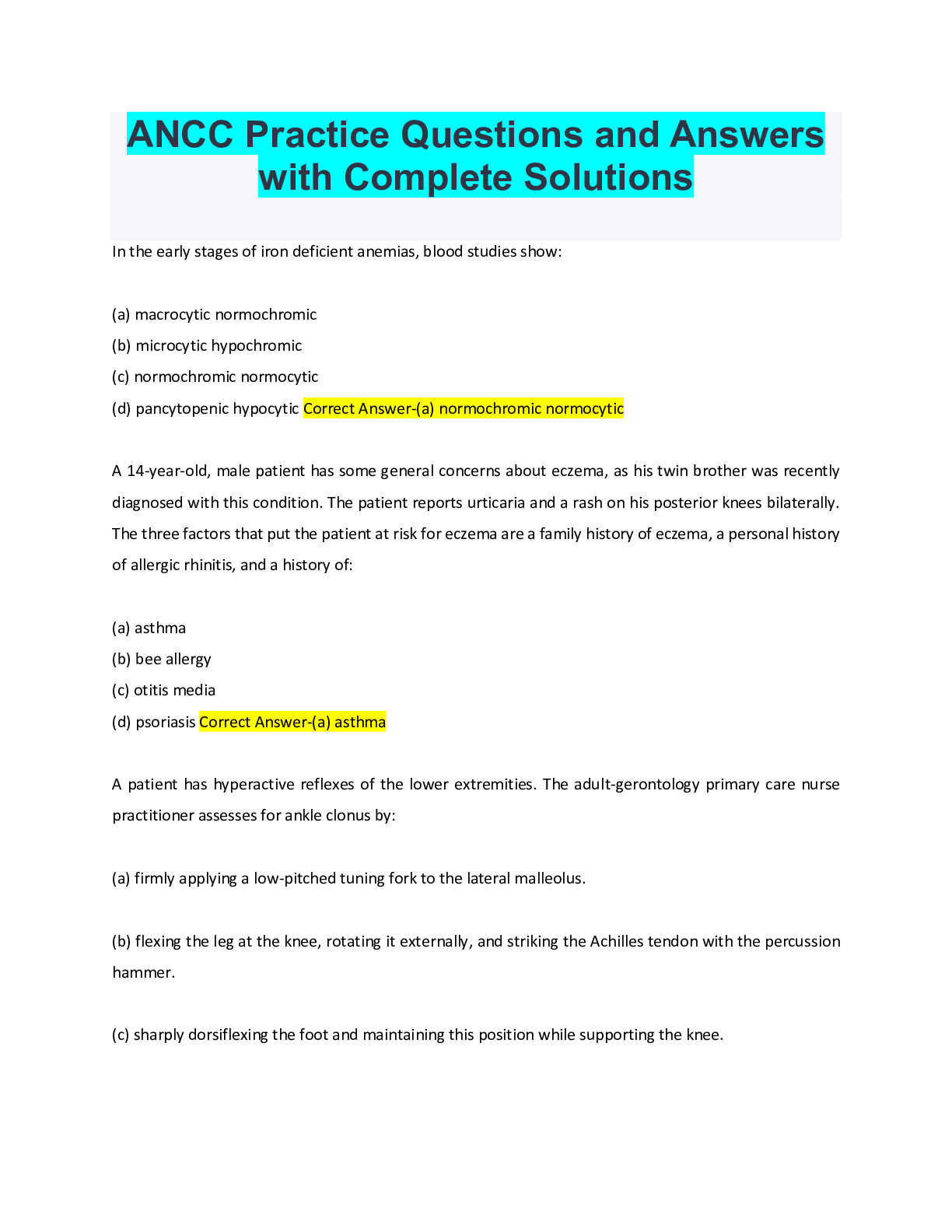
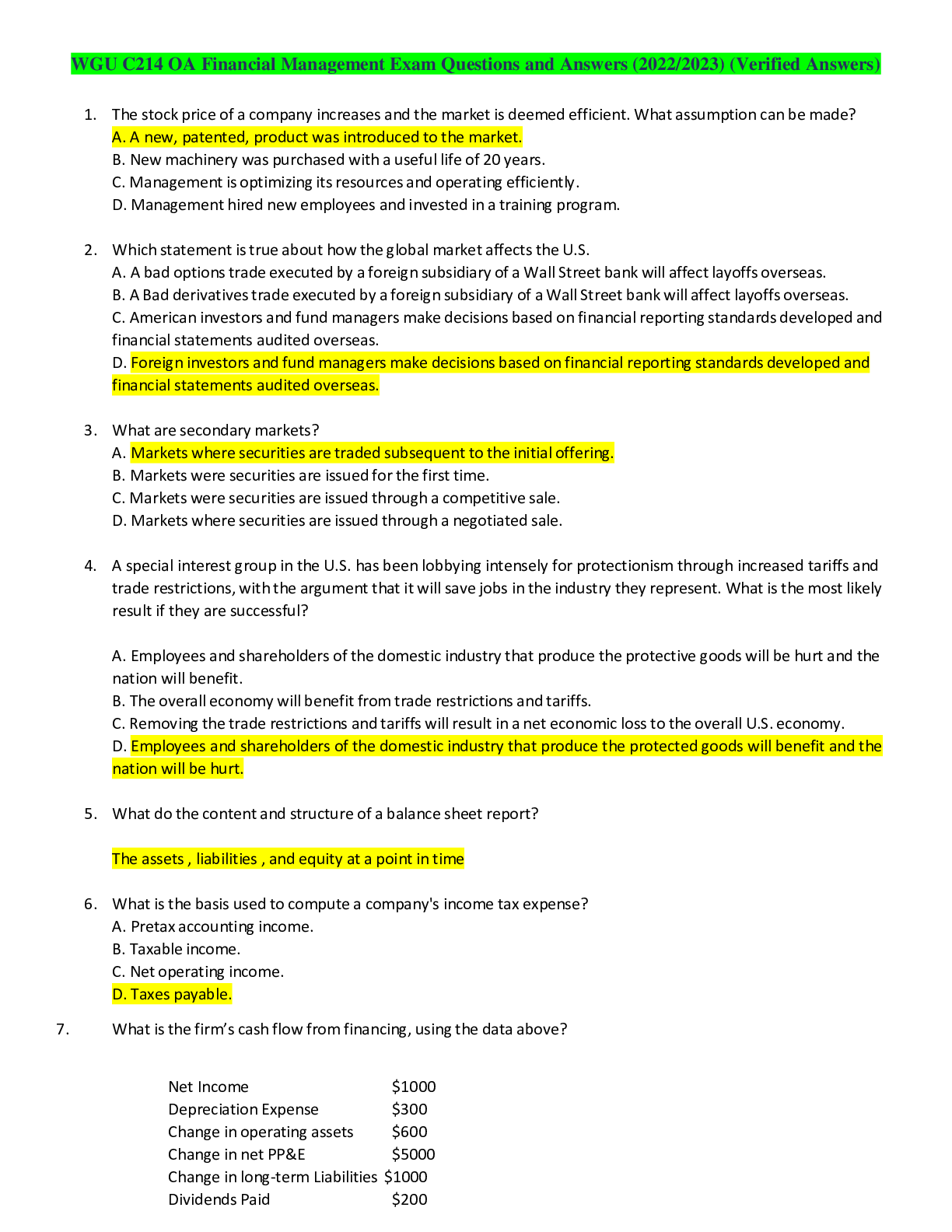
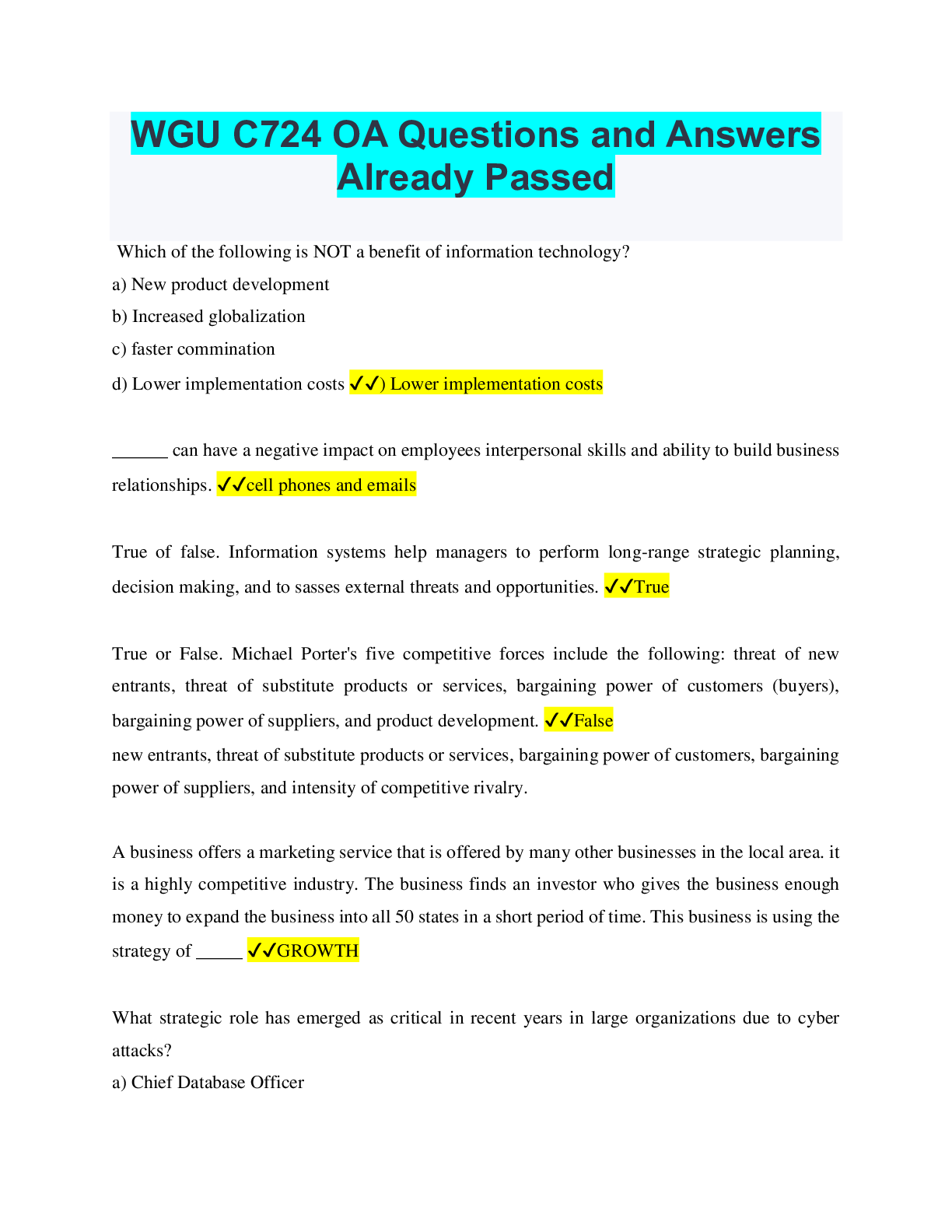
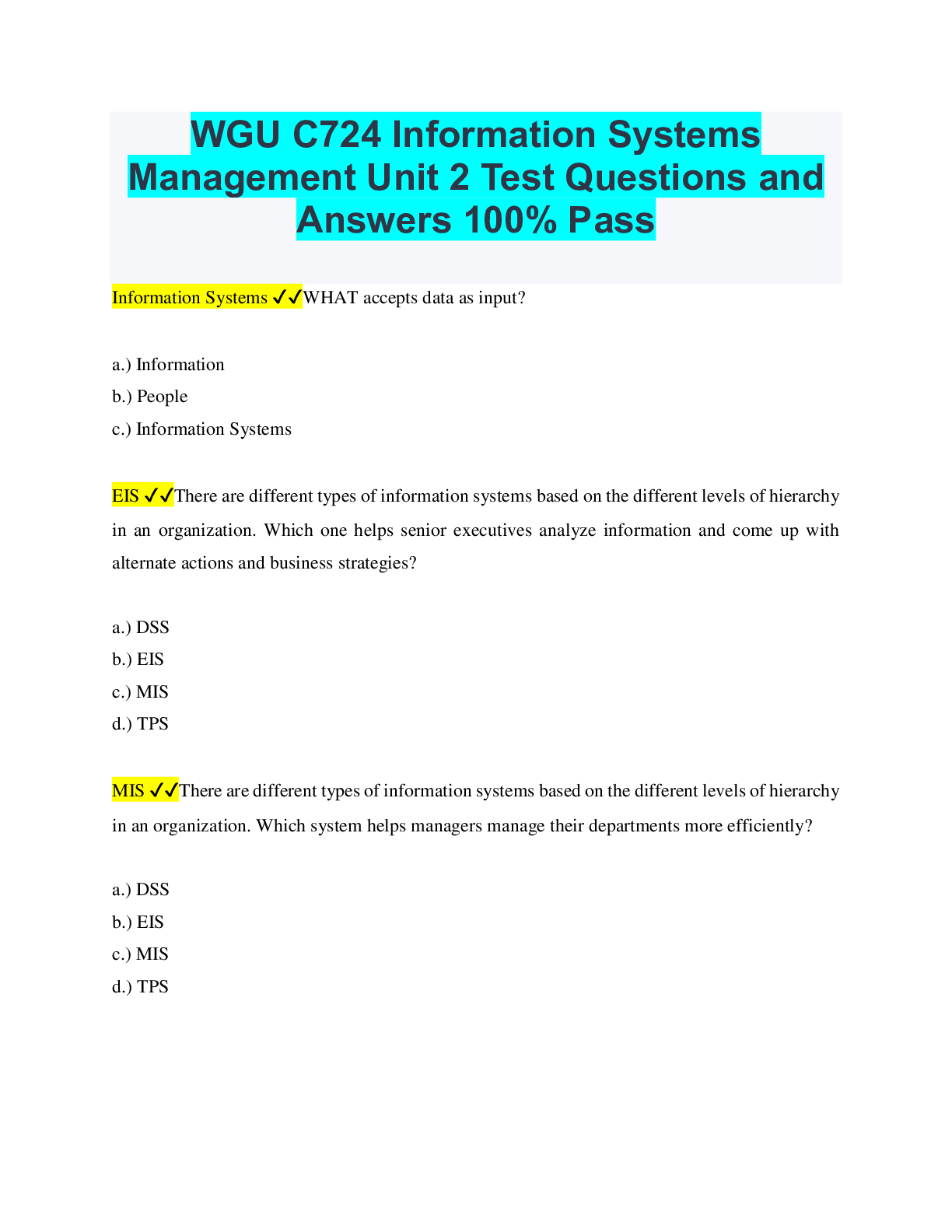
CyberRookie CSX Fundamentals - Roles in Cybersecurity Questions with Complete Answers 1 / 5 1. Information needs of Board of Directors: Organizational reporting, Trend analysis, High-level, compre... hensive risk assessment, Inventory of information assets Business impact analyses (BIA) 2. Key Responsibilities of Board of Directors: Provide strategic direction, Approve policies, Identify key assets, Verify appropriate protection levels and priorities, Define, communicate and enforce penalties for noncompliance with security protocols 3. Activities/Behaviors of Board of Directors: Set tone conducive to effective governance, Effective communication with Executive Management, Demonstrate legal and ethical responsibility with regard to organizational assets, Maintain confidentiality of critical information 4. Information needs of Executive Management: Organizational reporting, Trend analysis, Comprehensive risk assessment, Inventory of information assets 5. Key Responsibilities of Executive Management: Ensure availability and effective utilization of support resources, infrastructure, and organizational functions, Define the organization's information security program and management, Provide education and guidance to the organization's executive management team, Present options and decision support information (Advisor) 6. Activities/Behaviors of Executive Management: Set tone of importance as relates to protection of organizational assets, Demonstrate visibility within the information security organization, Communicate with and involve relevant partners (i.e. risk management) in key business activities and decisions 7. Information needs of Senior Information Security Management: Organizational reporting, Trend analysis, Comprehensive risk assessment Inventory of information assets 8. Key Responsibilities of Senior Information Security Management: All physical and digital security matters, Develop the security strategy, Oversee the security program and initiatives, Coordinate with business process owners for ongoing alignment, Ensure that risk and business impact assessments are conducted, Develop risk mitigation strategies, Enforce policy and regulatory compliance, Monitor the utilization and effectiveness of security resources, Develop and implementing monitoring and metrics, Direct and monitor security activities, Manage cybersecurity incidents and their remediation, incorporating lessons learned [Show More]
Last updated: 1 year ago
Preview 1 out of 5 pages
Buy this document to get the full access instantly
Instant Download Access after purchase
Add to cartInstant download
We Accept:
Reviews( 0 )
$7.00
Document information
Connected school, study & course
About the document
Uploaded On
Nov 01, 2022
Number of pages
5
Written in
Additional information
This document has been written for:
Uploaded
Nov 01, 2022
Downloads
0
Views
97

.png)
.png)

.png)
 Questions with Complete Answers.png)
 Questions with Complete Answers.png)
 Questions with Complete Answers.png)
 Questions with Complete Answers.png)

