Computer Science > QUESTIONS & ANSWERS > CyberRookie CSX Fundamentals - Section 5: Incident Response Questions with Complete Answers (All)
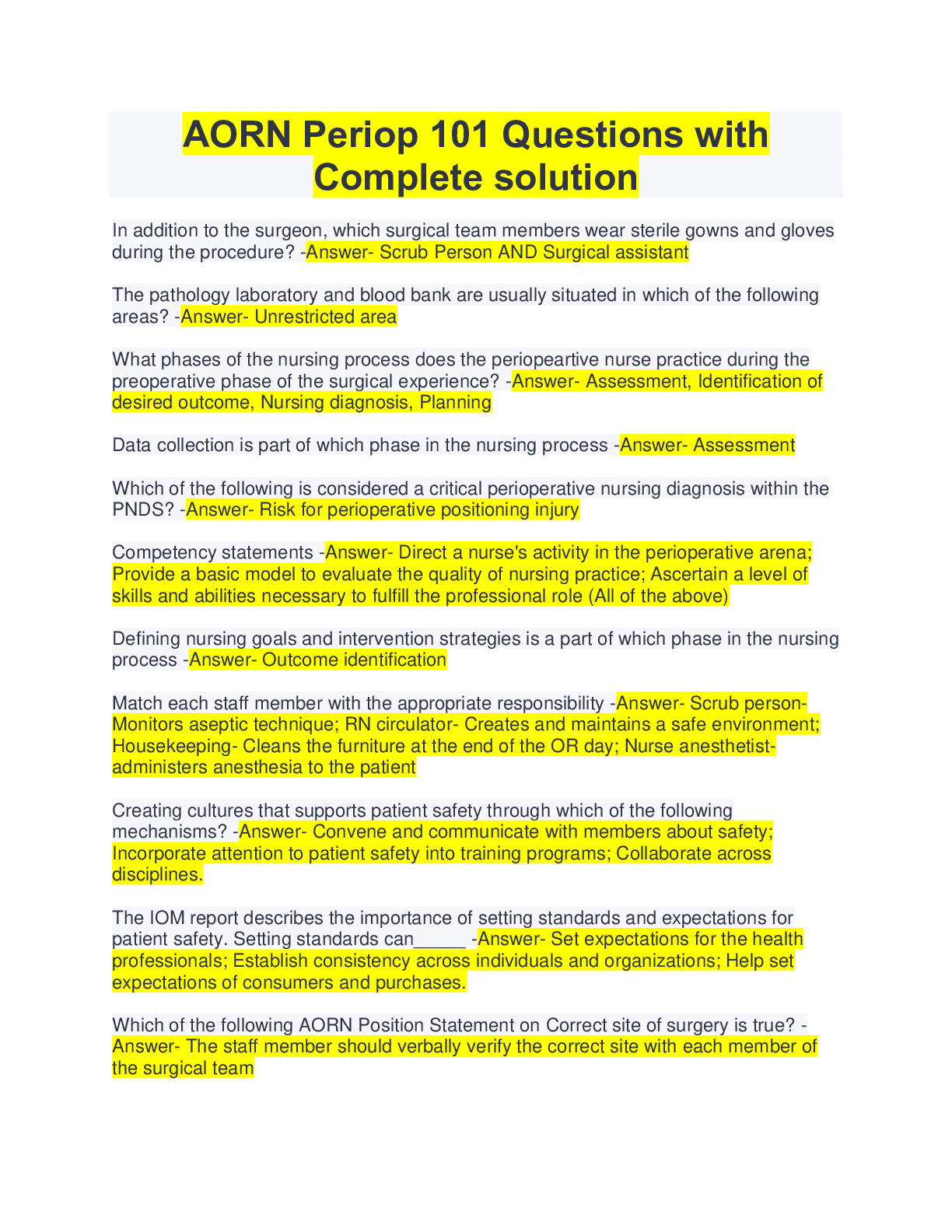
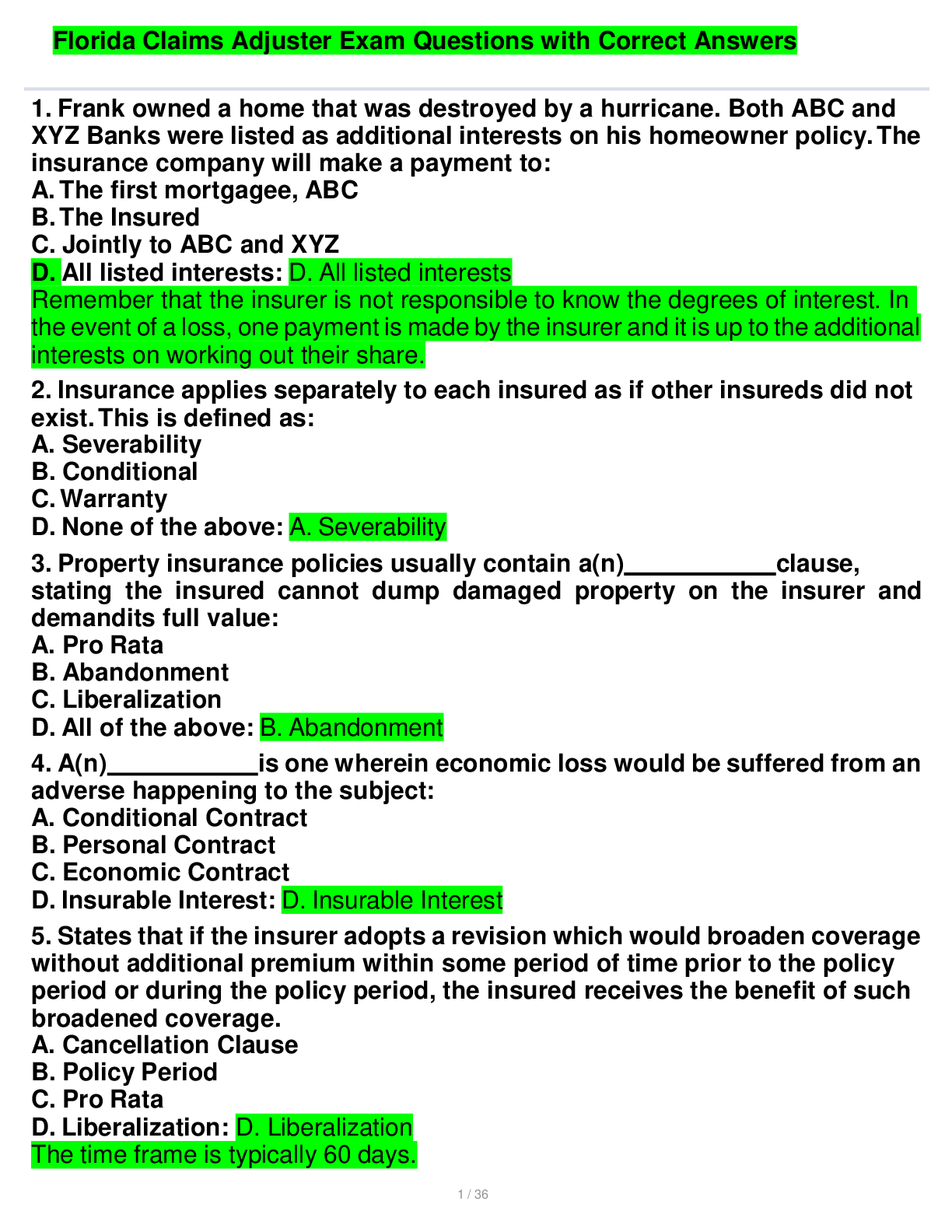
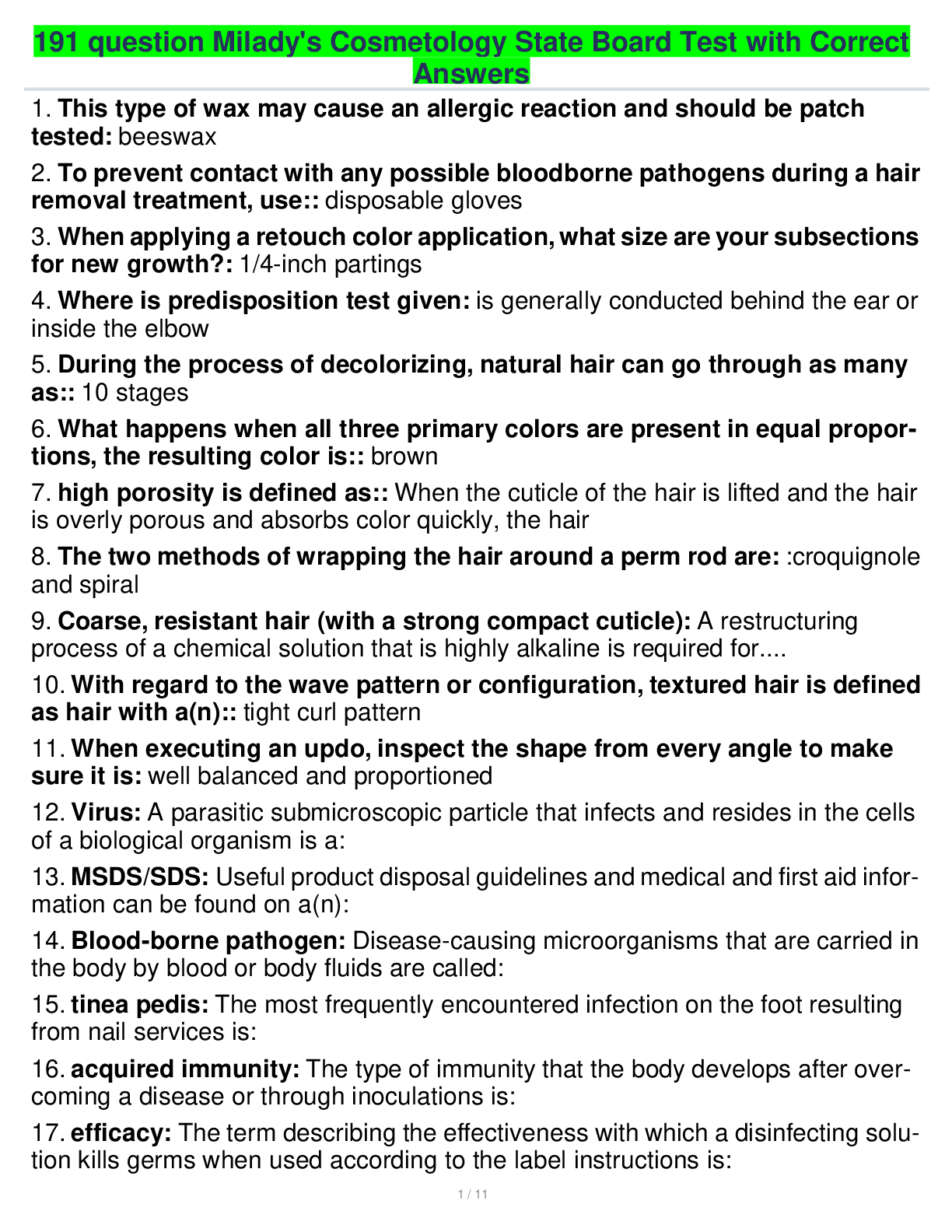
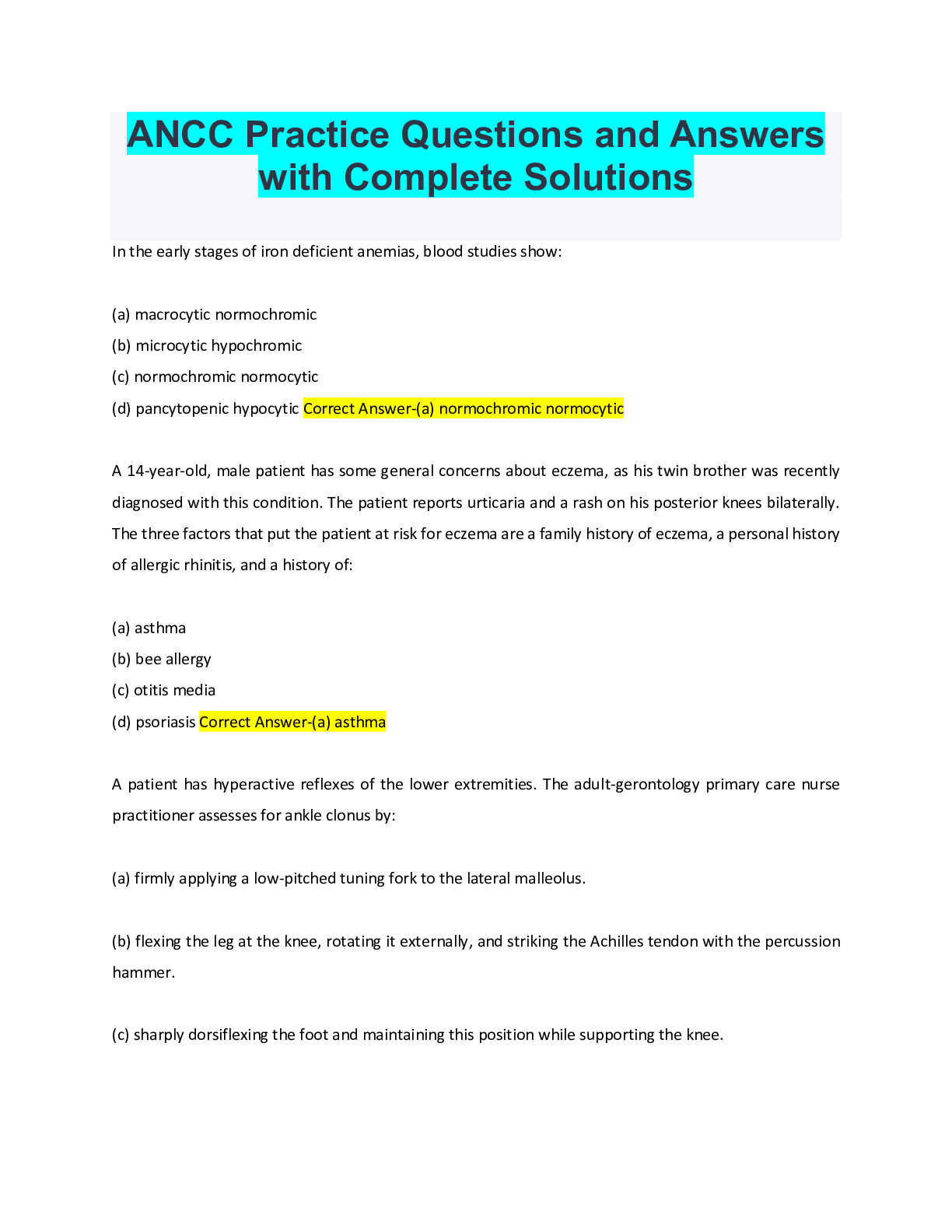
CyberRookie CSX Fundamentals - Section 5: Incident Response Questions with Complete Answers
Document Content and Description Below
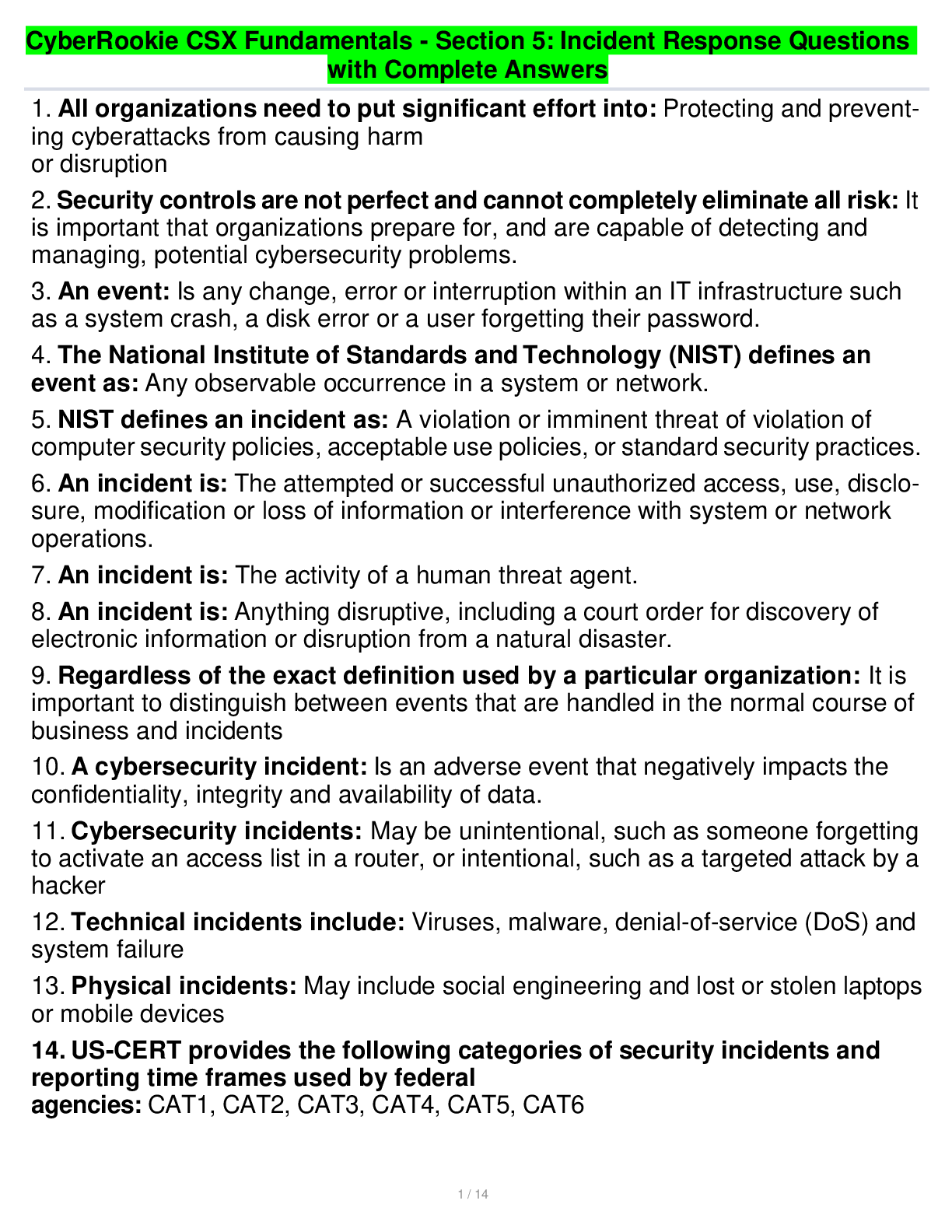
CyberRookie CSX Fundamentals - Section 5: Incident Response Questions with Complete Answers 1 / 14 1. All organizations need to put significant effort into: Protecting and preventing cyberattacks f... rom causing harm or disruption 2. Security controls are not perfect and cannot completely eliminate all risk: It is important that organizations prepare for, and are capable of detecting and managing, potential cybersecurity problems. 3. An event: Is any change, error or interruption within an IT infrastructure such as a system crash, a disk error or a user forgetting their password. 4. The National Institute of Standards and Technology (NIST) defines an event as: Any observable occurrence in a system or network. 5. NIST defines an incident as: A violation or imminent threat of violation of computer security policies, acceptable use policies, or standard security practices. 6. An incident is: The attempted or successful unauthorized access, use, disclosure, modification or loss of information or interference with system or network operations. 7. An incident is: The activity of a human threat agent. 8. An incident is: Anything disruptive, including a court order for discovery of electronic information or disruption from a natural disaster. 9. Regardless of the exact definition used by a particular organization: It is important to distinguish between events that are handled in the normal course of business and incidents 10. A cybersecurity incident: Is an adverse event that negatively impacts the confidentiality, integrity and availability of data. 11. Cybersecurity incidents: May be unintentional, such as someone forgetting to activate an access list in a router, or intentional, such as a targeted attack by a hacker 12. Technical incidents include: Viruses, malware, denial-of-service (DoS) and system failure 13. Physical incidents: May include social engineering and lost or stolen laptops or mobile devices 14. US-CERT provides the following categories of security incidents and reporting time frames used by federal agencies: CAT1, CAT2, CAT3, CAT4, CAT5, CAT6CyberRookie CSX Fundamentals - Section 5: Incident Response Questions with Complete Answers 2 / 14 15. CAT 1: Unauthorized Access, An individual gains logical or physical access without permission to a network, system, application, data or other resource. Within 1 hour of discovery/detection 16. CAT2: Denial-of-service (DoS), An attack that successfully prevents or impairs normal authorized functionality of networks, systems or applications by exhausting resources. Within 2 hours of discovery/ detection if the successful attack is still ongoing 17. CAT3: Malicious Code, Successful installation of malicious software (e.g., virus, worm, Trojan horse or other code-based malicious entity) that infects an operating system or application. Daily; within 1 hour of discovery/detection if widespread 18. CAT4: Improper Usage, A person violates acceptable computing use policies. Weekly 19. CAT5: Scans/Probes/Attempted Access, Any activity that seeks to access or identify a computer, open ports, protocols, service or any combination. Monthly 20. CAT6: Investigation, Unconfirmed incidents that are potentially malicious or anomalous activity. 21. Incident response: Is a formal program that prepares an entity for an incident. 22. Incident response generally includes: Preparation, Detection and Analysis, Investigation, Mitigation and Recovery, Postincident Analysis 23. Preparation: To establish roles, responsibilities and plans for how an incident will be handled 24. Detection and Analysis: Capabilities to identify incidents as early as possible and effectively assess the nature of the incident 25. Investigation: Capability if identifying an adversary is required 26. Mitigation and Recovery: Procedures to contain the incident, reduce losses and return operations to normal [Show More]
Last updated: 1 year ago
Preview 1 out of 14 pages
Buy this document to get the full access instantly
Instant Download Access after purchase
Add to cartInstant download
We Accept:
Reviews( 0 )
$8.00
Document information
Connected school, study & course
About the document
Uploaded On
Nov 01, 2022
Number of pages
14
Written in
Additional information
This document has been written for:
Uploaded
Nov 01, 2022
Downloads
0
Views
92

.png)
.png)

.png)
 A Total Of 100 Questions With Complete Solutions And Verified Answers.png)
 Questions With Complete Solutions And Answers.png)
.png)
.png)
.png)
.png)
.png)
 A Total Of 100 Questions With Complete Solutions And Verified Answers.png)

