Information Technology > EXAM > Introduction to IT - C182 WGU Questions and Answers (100% Correct Elaborations) (All)
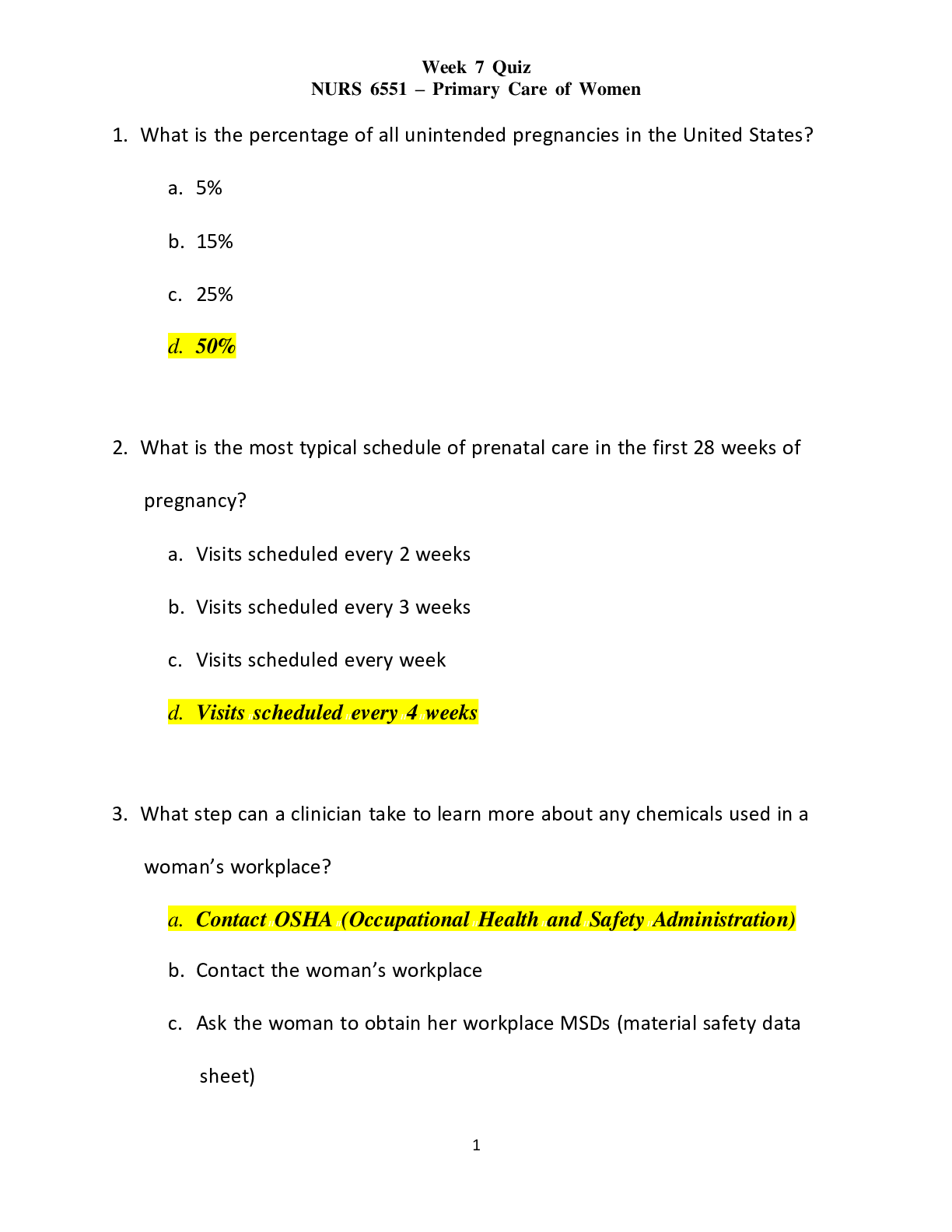
Introduction to IT - C182 WGU Questions and Answers (100% Correct Elaborations)
Document Content and Description Below
What are core components of IT? Hardware Software People What are some visions and goals of IT? Communication, both internal and external Sharing of resources Facilitating the integration o... f Departments Management of Information Ensuring that the organization runs according to ethical practices Why is IT viewed as a system? A system is a combination of independent parts all working together to accomplish a goal. What are some skills needed by IT personnel? Troubleshooting and problem solving. Knowledge of operating systems. System level programming. System security Hardware Describe trouble shooting (IT Skill) Detect and diagnose a problem, then find a solution. Examples: Poor processor performance, full hard drive, virus or other malware. Describe knowledge of OS's (IT Skill) Operating system installation, application software installation, user account creation, system monitoring. Examples: versions of Windows, Mac OS, Linux, Unix, etc. Describe system level programming (IT Skill) Shell scripts to automate processes, manipulating configuration files for system services. Examples: Bash, Csh scripts, Ruby scripts, C/C++ programs Describe system security (IT Skill) Ensuring proper system security is in place. Following or drafting policies for users. Monitoring for threats. Examples: Keeping security patches up to date, configuring a system firewall, installing anti-malware software, examining log files of evidence of breaches or attacks. Describe hardware (IT Skill) Installing and configuring new hardware. Troubleshooting, repairing, or replacing defective hardware. Examples: replacing CPUs and disk drives, connecting network cables to network hubs, switches, routers. What are some System Administrator duties? Account management: creating new user accounts and deleting obsolete user accounts. Password management: making sure that all users have passwords that agree with the security policy. File protection management: making sure that files are appropriately protected (for instance, making sure that important documents are not writable by the outside world) and performing timely backups of the file system Installing and configuring new hardware and troubleshooting hardware including the network. Installing and configuring new software including updating new operating system (OS) patches, and troubleshooting software. Providing documentation, support, and training for computer users. Performing system-level programming as necessary (usually through scripting languages rather than writing large-scale applications or systems software). Security: installing and maintaining a firewall, examining log files to see if there are any odd patterns of attempted logins, and examining suspicious processes that perhaps should not be running. What are some Network Administrator duties? physically laying down cable. making connections. working with the network hardware (for instance, routers and switches). like the system administrator, the network administrator will edit configuration files, install software (related to the network), and so forth. Troubleshooting the network may combine physical troubleshooting (e.g., is a cable bad?) and software troubleshooting. There is also a security aspect to the computer network. Both the system administrator and network administrator may work on system firewalls. Editing configuration files, writing shell scripts, and installing software and patches will all be part of a network administrators tasks. Describe a Database Administrator's duties. Like system administrators, database administrators have a long list of important responsibilities, but with a focus on the design, development, and support of database management systems (DBMSs). Tasks will include installation, maintenance, performance analysis, and troubleshooting as with the other administrative areas. There are specific applications, performance tuning parameters, account creation, and procedures associated with the DBMS that are separate from those of system administrators and web administrators. The database administrator may also be involved with the integration of data from older systems to new ones. As many or most database systems are now available over the Internet (or at least over local area networks), the administrator must also ensure proper security measures for remote access. Describe a Security Administrator's duties. Must stay informed of the many different types of attacks, such as denial of service attacks on web servers, IP spoofing to intercept messages, and buffer overflow that allows a hacker to invade computer memory with their own code. Although these are all known forms of attacks, it does not necessarily mean that a system is protected against them. And as these attacks are known, newer attacks are being thought of. It is the responsibility of the security administrator to install, configure, and administer appropriate firewall security to protect the organization's systems and to work proactively against such intrusions. Describe a Web Administrator's (aka Webmaster) duties. The web administrator, also known as a webmaster, but more precisely referred to as a web server administrator, is responsible for maintaining websites. This responsibility differs from the development of websites. Specifically, the web administrator must install, configure, maintain, secure, and troubleshoot the web server. The web server is software that runs on one or more computers. The web administrator may or may not be responsible for the hardware. Typically, the web administrator is not a system administrator on that or those computers. Therefore, the web administrator will have to work with the system administrator on some aspects of installation and configuration. Securing the web server becomes critical for businesses. Individuals outside and inside the organization may have reason to access data on the web-server without authorization thus requiring the need for securing the web server. The web administrator may be required to set up password files and establish locations where server scripts can be stored and tested. Security may be implemented directly through the web server software, or added through the operating system, or some combination. Security issues may be discovered by analyzing log files that are also used for data mining. What are the two most common support IT roles asides from administrators? training, and help desk. Training occurs as needed, but many help desks are available 24/7. What is information technology? Task of gathering data and processing it into information. The ability to disseminate information using technology. The technology itself that permits these tasks. The collection of people who are in charge of maintaining the IT infrastructure (the computers, the networks, the operating system). Generic definition of IT. We will consider IT to be the technology used in creating, maintaining, and making information accessible. In other words, IT combines people with computing resources, software, data, and computer networks. IT personnel, sometimes referred to collectively as "IT," are those people whose job it is to supply and support IT. These include computer engineers who design and build computer chips, computer scientists who write software for computers, and administrators who provide the IT infrastructure for organizations. Define information. Information is often defined as processed data. That is, raw data are the input and information is the output of some process. In fact, more generically, we should think of information as any form of interpreted data. What does DIKW Hierarchy stand for and what is it's purpose? Data, Information, Knowledge, Wisdom. It describes the transition of data to information to knowledge to wisdom. Define data in relation to DIKW Hierarchy. Data is the input directly received by the human or computer. Describe ways a computer may receive data (relates to DIKW). User entered values from application, camera, microphone, bar code reader, sensor, pen tablet, etc. When does data become usable? After it's been converted to a relevant form, for computers this would be binary representation. In the DIKW Hierarchy what do we mean when we say information has been inferred from data? That one or more processes have been applied to the data to transform it into a more useful form. Define Knowledge in the DIKW Hierarchy. Knowledge is sometimes defined as information that has been put to use. In other cases, knowledge is a synthesis of several different sources of information. One way to think of knowledge is that it is information placed into a context, perhaps the result of experience gained from using information. Additionally, we might think of knowledge as being refined information such that the user of the knowledge is able to call forth only relevant portions of information when needed. As an example, one may learn how to solve algebraic problems by studying algebraic laws. The laws represent information, whereas the practice of selecting the proper law to apply in a given situation is knowledge. Define Wisdom in the DIKW Hierarchy. Some refer to wisdom as an understanding of "why"—whether this is "why things happened the way they did" or "why people do what they do." Wisdom can only come by having both knowledge and experience. Knowledge, on the other hand, can be learned from others who have it. Wisdom is the ultimate goal for a human in that it improves the person's ability to function in the modern world and to make informed decisions that take into account beliefs and values. Define information system. An information system is in essence a collection of data and information used to support management of an organization. The term also refers to the technical components and human resources that enable the assembly, storage, and processing of data, and the delivery of information. Give three examples of information systems. A company's directory, a company's customer database, a university course catalog. List the characteristics of quality data? (hint: RTTAR) Relevance, Timely, Thorough, Accurate, Reliable. What are the four operations a computer performs? (hint: IPOS) Input, Processing, Output, Storage. Describe input in relation to IPOS cycle. Raw data is entered by the user. Describe processing in relation to IPOS cycle. Raw data is organized or structured for usefulness. Describe output in relation to IPOS cycle. Information output so user can see results. Describe storage in relation to IPOS cycle. Processed information is stored for permanent record. Define computer system (system for short). A collection of components that work together to meet the needs of the user. These components are typically categorized as either hardware or software. In addition, networks and users are often considered to be part of a computer system. Define system software. Systems software includes the operating system and all the utilities that enable the computer to function. Define application software. Applications software includes programs that do real work for users. For example, word processors, spreadsheets, and database management systems fall under the category of applications software. Who were the earliest computer users? The engineers who built and programmed them. Computers were so complicated and expensive that no one else would have access. What led to computer users learning computers with little or no training? GUI (Graphical User Interface) operating systems. How was most processing performed in early days of computers? Most—if not all—processing was done without human interaction at all. The user specified the program, the source of input, the location of output, and sent the program off to run. The user would see the results once the computer ran the program, which might have been immediately, or many hours later! Define network. A network is a collection of computers and resources connected by various media so that they can communicate with each other. Name some advantages of a network. The ability to share information, share hardware such as a printer, and even share software. What do computers need to communicate over a network? An appropriate protocol. What is the most common network protocol? TCP/IP (Transmission Control Protocol/Internet Protocol), which is a requirement of all computers that communicate over the Internet. Note: TCP/IP is really a collection of protocols and is sometimes referred to as a protocol stack. Early generations of computers, due to their size and limited capacity were limited mostly to? Scientific tasks and some business tasks like accounting that processed large volumes of transactional data. Why did hardware become ubiquitous? Because of the reduction in size, increase in capability, and reduction in prices most everyone was able to have a computer. What are the 4 components of most computer systems? CPU (processor) Memory Input/output (I/O) subsystem Bus What does the CPU do? The CPU is the device that not only executes your programs' instructions, but also commands the various components in the computer. What does memory do? Memory stores the program(s) being executed and the data that each program is using. What makes up the I/O subsystem? The I/O subsystem includes all peripheral devices (input, output, storage, network) where storage consists of the long-term storage devices (disk drives, tape). What does the bus do? The bus is the device that permits information to move between each component. The bus then is the device that allows this electrical current to flow between each component in the computer system. What does the bus consist of? The bus consists of a number of wires, each wire allows 1 bit (a single 1 or 0, high or low current) to flow over it. What 2 parts make up the CPU? The control unit (CU) and the arithmetic logic unit (ALU). What does the control unit do? It retrieves the instructions and the raw data that is input, and coordinates or controls the sending of those instructions and data to the ALU. What does the ALU do? The ALU does the actual processing of the data, from mathematical calculations and logical operations (comparing values that can be numeric or alphabetical) to conversion of keyboard text entry to output display on your screen. What does the system clock do? The system clock controls the speed at which instructions are processed. Processing speed is listed in terms of megahertz (MHz), (millions of processes per second) or gigahertz (GHz) (billions of processes per second). What factors can affect processing speed? System clock speed Having multiple CPUs, RAM available to store data as it's processed, The wiring of electrical circuits. What are the two main forms of RAM? Dynamic RAM (DRAM) which is typically called main memory, and static RAM (SRAM), which is cache memory and registers. RAM is referred to as __________ memory, while hard disk storage is referred to as _________ memory. primary (RAM), secondary (disk storage) What are the 3 primary roles of peripherals? Input Output Storage What industry standards are used to connect peripherals to computers? Bays (house CDs and DVDs) Typically on front. Slots (modem cards, wireless access cards, other pc cards) Ports (connect additional input, output, storage and communication devices) 3 most typical types of computers? Desktop - designed for use in one physical location Laptops - lightweight and portable Handheld - variety of forms including tablets, smartphones, and mp3 players. Key differences between peripheral devices of standard PC computer and smartphone? The smartphone has items normally thought of as peripherals such as keyboard and monitor built in, whereas with the desktop computer the peripherals are largely external. Key difference between PC desktop and laptops? The peripherals and system unit of a notebook/laptop are sold as a single unit. When did the first generation of computers occur? The mid 1940's till about 1959. When did the second generation of computers occur? From around 1959 until 1965. When did the third generation of computers occur? From 1965 until early 1970's. When did the fourth generation of computers occur? From early 1970's through today. What was the first digital, general purpose, programmable computer? The ENIAC (Electronic Numerical Integrator and Computer). What are some characteristics of first generation computers? All were one-of-a-kind machines. Classified not only by time period but reliance on vacuum tubes, relay switches, and the need to program in machine language. What innovation around 1959 replaced vacuum tubes in computers? Transistors. They could be mass produced and were far cheaper, used less power, and produced much less heat than vacuum tubes. They were much more robust than vacuum tubes. Tubes would last at most a few thousand hours, whereas transistors could last up to 50 years. What innovation along with transistors helped usher in the second generation of computers? Magnetic core memory. Magnetic core memory consists of small rings made of magnetic materials, placed in a wire-mesh framework. Each ring stores one bit by having magnetic current rotate in either clockwise or counterclockwise fashion. What are some characteristics of the second generation of computers? The second generation found cheaper, faster, easier to program, and more reliable computers. Computers no longer limited to government labs and university labs. Largely referred to as mainframes because of being built around a solid metal frame. What innovation ushered in the third generation of computers? Silicon chips (also known as printed circuits or integrated circuits (ICs). One IC could incorporate dozens of transistors. Why were integrated circuits referred to as semi-conductors? The IC would be a pattern of transistors etched onto the surface of a piece of silicon, which would conduct electricity, thus the term semiconductor. Pins would allow the IC, or chip, to be attached to a socket, so that electrical current could flow from one location in the computer through the circuit and out to another location. Why did integrated circuits replace transistors and magnetic core memory? ICs take up less space reducing distance current has to flow, could be mass produced. They could be used for computation and for storage. What are some differences between a mainframe and a mini computer? (Third generation) Mini-computers were scaled down versions of mainframes. They used same type of processor but had reduced number of registers, reduced memory, etc. A main frame might support thousands of people, whereas a minicomputer might only support tens or hundreds of people. Why did companies start producing families of computers during the third generation? The idea was that any computer in a given family should be able to run the same programs without having to alter the program code. This was largely attributable to computers of the same family using the same processor, or at least processors that had the same instruction set (machine language). The computer family gave birth to the software development field; code could be written for an entire family and the program sold to potentially dozens or hundreds of customers. What input/output device allowed users to access computers remotely? (third generation) Dumb terminals with no memory or processor. What major innovation in 1974 by IBM ushered in the fourth generation of computers? The single chip processor, also known as microprocessor. Up until this point, all processors were distributed over several, perhaps dozens, of chips. By creating a single-chip processor one could build a small computer around the single chip. These computers were called microcomputers. Such a computer would be small enough to sit on a person's desk. This ushered in the most recent generation, the fourth generation. What was the first microcomputer sold mainly to hobbyists? The Mark 8. The most significant change to occur to computers since 1974 is _____________. Miniaturization. The third-generation computers comprised multiple circuit boards, interconnected in a chassis. Each board contained numerous ICs and each IC would contain a few dozen transistors (up to a few hundred by the end of the 1960s). By the 1970s, it was possible to miniaturize thousands of transistors to be placed onto a single chip. As time went on, the trend of miniaturizing transistors continued at an exponential rate. Which generation of computers was the first to use boolean operators? The second generation. Which generation of computers was the first to use mainframe computers? The second generation. Which generation of computers introduced computer networks? The third generation. One of the founder's of Intel, ___________ ____________, noticed which trend that was later named after him? Gordon Moore first noticed this rapidly increasing "transistor count" phenomenon. In a 1965 paper, Moore observed that the trend from 1958 to 1965 was that the number of transistors on a chip was doubling every year. This phenomenon has been dubbed "Moore's law." Moore predicted that this trend would continue for at least 10 more years. In a ___________ CPU the fetch-execute cycle is performed in an overlapped fashion on several instructions. For instance, while instruction 1 is being executed, instruction 2 is being decoded and instruction 3 is being fetched. This would result in three instructions all being in some state of execution at the same time. pipelined. Early computer programs were written in ________ ____________. Machine language. Often for a specific machine, often by the engineers who built and ran the computers. Entering the program was not a simple matter of typing it in but of connecting memory locations to computational circuits by means of cable, much like a telephone operator used to connect calls. Once the program was executed, one would have to "rewire" the entire computer to run the next program. By 1959 the improved class of language translators was known as ___________, and the languages were called ____ ____ _______. Compilers High Level Languages The first compiler was for the __________ language. FORTRAN (FORmula TRANslator). FORTRAN was primarily intended for mathematical/scientific computing. A business oriented language produced roughly at the same time as FORTRAN is known as ___________. COBOL (Common Business Oriented Language). In the early 1960's the operating system was called a ________ _______. Resident monitor.It would always be resident in memory, available to be called upon by any user. It was known as a monitor because it would monitor user requests. The requests were largely limited to running a program, specifying the location of the input (which tape drive or disk drive, which file(s)), and the destination of the output (printer, disk file, tape file, etc.). By the mid 1960's the resident monitor was being called an __________ ___________, a program that allowed a user to operate a computer. Operating system. In _____________ _______________ the programmer is limited to high level control constructs such as while loops, for loops, and if-else statements, and is not allowed to use the more primitive GOTO statement. This ushered in a new era of high level languages, C and Pascal being among the most notable. structured programming Object-oriented programming (OOP) was first introduced in the language __________ in the 1970's and early 1980's. Smalltalk In the mid 1980's Smalltalk's object oriented capabilities were incorporated into a new version of __ called ____. C C++ The first windowing operating system developed by ______ was used to demonstrate the use of OOP. Xerox The ___ programming language developed at the end of the 1950's for artificial intelligence research used an __________. This allowed programmers to test out one instruction at a time so they could build their program piecemeal. Lisp interpreter What is the main difference between a compiled language and an interpreted language? The interpreted language runs inside of a special environment called the interpreter. The programmer enters a command, then the interpreter converts that command to machine language and executes it. Interpreters rely on a __________. Session Examples of scripting languages are? Perl php ruby python asp All computers no matter their generation use the _______ system for programming. binary A _______ ___________ is a collection of computers and computer resources (e.g., printers, file servers) connected in such a way that the computers can communicate with each other and their resources. computer network In networks we define computers as being _______ or ________. local remote The most common form of network connection used today is __________________ and _____________. UTP (Unshielded Twisted Pair) Fiber optic cable Both coaxial cable and twisted wire transmit information using using _________ ______voltage (e.g. 10BASET uses +2.5V or -2.5V), whereas fiber optic cable uses _______ _________. electromagnetic waves light pulses ____________ is the transfer rate permissible over the media, described as some number of bits per second (bps or b/s). Modern _________s are on the order of millions or billions of bits per second (Mbits/second, Mbps or Gbits/second, Gbps). Older technologies such as computer MODEMs (described later) were limited to hundreds or thousands of bits per second, such as 56 Kbps or 56,000 bits per second. Bandwidth A device that connects multiple computers together. When there are multiple computers connected to this device a message received by the device is forwarded to all ports on the device. A destination address attached to the message indicates which computer the message is intended for, but it does not prevent other computers from picking up the message. The device broadcasts the transmission, as it sends the data to every device in the network. Network hub A ________ ________ is a more functional connection than a hub. For one, it records and recognizes the local network addresses [Media Access Control (MAC) addresses or IP addresses] of all computers connected to the switch. A message is then only passed along to the computer that matches the destination address. Thus, the switch is able to utilize network bandwidth more efficiently. While this device can be used to broadcast to all computers in a network, its purpose is to only send transmissions to a specific, intended computer. network switch The ________ is a device that connects multiple networks together. Although you can use the device to directly connect computers in a network, the devices are typically used instead in specific locations in a network so that messages can be routed to other networks. router What are some differences between hubs, routers and switches? Externally, there is little to differentiate a hub from a switch from a router (other than perhaps the size). Internally, the switch has more hardware, including storage space for MAC and IP addresses, than a hub. A router contains programmable routing tables and includes at least one input that comes from another network. A _______ switched network requires that a full pathway, or ________, be established before transmission can begin and maintained during the entire transmission. The telephone network is a __________ switched network. Because the path exists during the entire conversation, communication in either direction can occur simultaneously. circuit In a _________ switched network, a message's pathway is only established as it is sent. When a message is received at one location, if it is not the destination location, then the message is forwarded on to another location. The choice of pathway is based on network availability and amount of message traffic. Most computer networks are _______ switched, with the Internet being the most well-known and commonly cited example. packet We can also classify networks by the role that computers play within the network. Specifically, we refer to networks as either ___________ or ___________ networks. peer-to-peer client-server A _____ means that each computer is roughly equal to every other computer. peer When discussing a network, the ______ is a computer that will request information from another computer. The ______ is a computer that takes requests and responds with the requested information. The _________ network then is a network that contains one or more servers client server client-server A ________ ____________ is a software emulator program that permits a computer user to use multiple computers and multiple platforms without the expense of purchasing multiple computers. In a business ecosystem, this allows for improved collaboration that is not restricted by platform software. virtual machine (VM) A ___________ _____________ is an illusionary computer that is stored in computer memory and made available by software in order to permit a computer user to use multiple computers and multiple platforms without the expense of purchasing multiple computers. virtual machine The term server may be used to refer to what three different things? The first is a dedicated computer used to provide a service. Servers are typically high-performance computers with large hard disk drives. The second use of the term server is of the software that is run on the machine. Server software includes print service, ftp server, web server, e-mail server, database server, and file server. The software server must be installed, configured, and managed. These steps may be involved. For instance, configuring and managing the Apache web server could potentially be a job by itself rather than one left up to either a system administrator or web developer. The third usage for server is the collection of hardware, software, and data that together constitutes the server. For instance, we might refer to a web server as hardware, software, and the documents stored there. In the case of a ______ ________, the server's role is to send files over the network at the request of clients. file server This is a special type of file server in that it still stores data files (web pages) and programs (scripts). web server Name several duties the web server that the file server does not. running server side scripts logging requests and errors handling security. Which type of server responds to client database queries with responses pulled from the database. database server A _____ server monitors print jobs and replies with an acknowledgment that the print job has completed, or an error message. print A ____ server functions by: one submits e-mail to the server to be sent to another e-mail server. The two e-mail servers communicate with each other, and once the e-mail is received at its destination, the recipient server informs the recipient user that new e-mail has arrived. mail An ___ server is much like a web server or file server in that requests are for files and responses are the files. FTP In a ___ network, devices are connected along a single cable. bus In a ____ network, each device is connected to a central device, such as a hub or switch. star In a ____ network, every device is connected directly to every other device in the network. mesh In a ____ network, each device is connected directly to its neighbors, and messages are forwarded from device to device until the proper destination is reached. ring In the ___ network, all devices listen to any communications over the single cable and ignore all messages that are not intended for them. The ___ provides a dynamic network in that devices can be added and removed from the network at any time as long as there are still "T" connectors available. This is also the cheapest of all network topologies and a very reliable form of network. It does not degrade if a resource is either removed from the network or crashes. In spite of this, the network topology has a large drawback. All messages travel along the single cable and so the network's efficiency degrades as more devices are connected to it. bus The ____ network is in some ways the opposite of the bus network. In the star network, all devices have a single point-to-point connection with a central device. This dedicated device acts as a communication hub, routing messages from one machine to the destination. The advantages of the network are its simplicity, ease of adding (or removing) devices, and the efficiency of message transferal. The network does not have to contend with message traffic like the bus network (although the hub can quickly become a bottleneck if there are a lot of simultaneous messages). The number of links that it takes for any message to reach its destination is always two (or one if the message is intended for the hub device). The network has two detractors. First, it does require a dedicated device, making it a more expensive network than the bus. The hub of the network may be a hub or switch. The hub of the network may also be a server, which would make the network more expensive. Second, although losing any single device would not degrade the network, if the hub is lost, all devices lose connectivity. star In the ____ network, devices have point-to-point connections with their neighbors. Communication between devices requires sending a message to a neighbor and having that neighbor forward the message along the ____ until it reaches its destination. The ____ is easily expanded by adding new devices between any two nodes. However, the larger the ring becomes, the greater the potential distance that a message might have to travel. This, in turn, can create lengthier transmission times. ____s are cheap, like buses, in that there is no dedicated resource that serves as a central point. A ring network could be unidirectional or bidirectional in terms of the direction that messages travel. In a unidirectional ____, if a device were to go offline, it would detach the network into two such that some devices could no longer communicate with others. Assume, for instance, that the ____ topology shown above were unidirectional and all communication traveled clockwise around the ____. If the topmost device were to fail, the device to the immediate left of the failed device would not be able to reach any other device, whereas the device to the immediate right of the failed device would not be able to receive communication from any other device. A bidirectional ____ would require losing two devices before portions of the network became isolated. ring The ____ network, also known as a fully connected network, requires that every device have a point-to-point connection with every other device. If there are n devices in the network, there are as many as (n - 1)^2 connections. Any device can directly communicate with any other device without concern of message traffic, and if any device were removed, it would not harm the connectivity of the network. However, the ____ network is impractical because of the cost. Not only does it require an excessive number of connections, it requires that every device have n - 1 ports available to make those connections. The ____ network is typically found in high-performance parallel processing computers but not used in computer networks. A small ____ network of six devices is shown in the image above. With six devices, there are a total of 25 connections. Imagine the number of connections required for a ____ of 50 devices instead. This would require 2401 connections! mesh Authentication is often done by proving who you are via these three "what you" statements. What you know What you have (encryption key, physical keys, etc) What you are (biometrics, finger prints, etc) Intranet A LAN that uses the Internet Protocol is known as an intranet. The advantage of an intranet is that applications intended for Internet usage (e-mail, web browsing, telnet/ssh, etc.) will work internally as easily as they work externally. Cloud Computing Cloud computing combines several different technologies: distributed computing, computer networks, and storage area networks. The idea is to offer, as a service, the ability to offload computation and storage from your local computer to the cloud. Kernel The core components of the operating system are referred to as the kernel. The kernel is loaded when the computer is first booted. Included in the kernel are the components that handle process management, resource management, and memory management. Device Drivers Another piece of the operating system is the collection of device drivers. Device drivers provide specific interfaces between the OS running a computer and hardware. Shell The shell is an interface for the user, often personalized for that given user. The shell provides access to the kernel. For instance, a GUI shell will translate mouse motions into calls to kernel routines (e.g., open a file, start a program, move a file). Desktop elements include shortcut icons, the theme of the windows, menus and background, the appearance of toolbars and programs on the start menu, and desktop gadgets. Services Services, or daemons, are operating system programs that are usually started when the operating system is loaded and initialized, but they run in the background. This means that the program, while it is active, does not take up any CPU time until it is called upon to do so. Utility Programs System utilities are programs that allow the user to monitor and improve system performance. Utilities greatly range in function. Role of a Web server is The role of a web server is to respond to HTTP requests. HTTP requests most typically come from web browsers, but other software and users can also submit requests. A proxy server is used in an organization to A proxy server is used in an organization to act as a giant cache of web pages that anyone in the organization has recently retrieved. An FTP server is An FTP server is like a webserver in that it hosts files and allows clients to access those files. However, with FTP, access is in the form of uploading files and downloading files. Any files downloaded are saved to disk unlike the web service where most files are loaded directly into the client's web browser. A file server is A file server is in essence a computer with a large hard disk storing files that any or many users of the network may wish to access. The more complex file servers are used to not only store data files but also to store software to be run over the network. E-mail Server An e-mail server provides e-mail service. Its job is to accept e-mail requests from clients, send messages out to other e-mail servers, receive e-mails from other servers, and alert the user that e-mail has arrived. Copyrights protect an Copyrights protect an original work (in its tangible, expressed form), but not the ideas behind the work. The copyright holder has the exclusive right to make copies, prepare derivative works, and distribute copies of the work for the duration of the author's life plus 70 years. "Fair use" provides an exception to this by allowing nonprofits or educational institutions to use the copyrighted work. Copyrighted works are registered as a matter of public record. However, copyright law may be interpreted inconsistently and the protections may not be very strong. Therefore, the use of patents has become more common. Patents protect the Patents protect the creation of inventive concepts as well as the tangible work product (not just the tangible work, as copyrights do). To receive a patent, the applicant must be able to show that the idea is original, useful, and not obvious to someone of "ordinary skill" in the field. The patent owner can then prevent others from making, selling, or using the patented invention for 20 years from the patent application filing date. The U.S. patent system is intended to encourage innovation. The GNUs Public License is used for The GNUs Public License is used for free software and is designed so that it will stay free regardless of who modifies the software. Copyleft is a play-on-words of copyright: instead of using rights to limit users (as proprietary software does), it promotes freedom and flexibility of use. A language translator is A language translator is a program that takes one program, written in a high-level language, as input, and creates a machine language program as output. These high-level languages are also called programming languages, which are a vocabulary and set of rules for instructing a computer to perform certain tasks. Compiled Language Translates the entire program, creating an executable program, which can be run at a later time. Interpreted Language Takes the most recently entered instruction, translates it into machine language, and executes it. Scripts have traditionally been used more for _________ than for software development. automation Algorithm An algorithm is a formula or procedure for solving a problem. It can also be described as a set of steps that are followed in order to complete a computer process. In typical n-tier development projects, the tiers are divided between the The presentation tier The logic tier The data tier Presentation tier The presentation tier is where the user interface for the system is developed. The notion behind a user interface is to shield the user from the underlying logic of the system as well as the underlying data structures. Logic Tier The logic tier sits between the user interface and the data. As such the logic tier is a conduit through which the data flows to the user from the databases as well as how data input from the user is used to update the underlying records in the database. Data Tier The data tier also resides on the organization's servers and usually on a separate database server. The data tier is where data are stored, retrieved, and updated from database tables. By separating the data from the application logic in the logic-tier the data is made independent of the application. The Model The model can take on different forms depending on the complexity of the application. In certain instances, the model is an actual object that is an actual implementation of the application. Using our e-commerce example, the model could be of a company's product. So the product would be the model. The Controller The controller is the part of an application that interacts with the user (via the view) and passes along the user requests to the model. The results from the model will determine the type of view the controller uses in the interface presented to the user. It is in the controller layer that the input logic is designed. The View The view is the part of the application that represents the user interface. The view is used to capture input from the user to be passed on via the controller to the model. The information returned by the model is then presented to the user via the view. It is in the view layer of the application that the user interface logic is designed. The ___ model is one application where the various design logic (input, business and interface) are logically separated. This differs from the n-tier development model where each tier is a separate application. MVC Alphanumeric text characters (string data) Integer a whole number Floating-point a number with a decimal point (numeric data) Date / Time data type used for storing date/time information. Boolean / Logical True / False Flat File Database It is one large single table without the relations between tables that a relational format provides. The most common example of a flat file is a CSV file (comma separated values). Records in a flat file are separated by a delimiter. In a CSV file, that delimiter is a comma. One of the advantages of the flat file format, is that these files can be easily imported into other programs that use a different file format; data can be captured through one program and then imported into another. Relational Database A relational database is the most common structure for databases. A relational database has multiple tables (relations) with interrelated fields. When you perform a query in a relational database, data can be pulled from any number of relations that may be contained in multiple databases. Relational databases can also create new tables out of requested information in a query. Hierarchical Databases A hierarchical database format organizes data using a tree-like or organizational chart type structure. The main data points can have multiple sub-data points associated with them referred to as a parent-child model; however, the sub-data points can only have one main data point, i.e. the child can only have one parent. A database is A database is an organized collection of data. We typically create, manipulate, and access the data in a database through some form of database management system (DBMS). DBMSs include Microsoft Access, SQL, and its variations (MySQL, Microsoft SQL, PostgreSQL, etc., and Oracle, to name a few). tuples Rows/records in a database. Attributes Fields in a database (column headers) Field The modules referred to this as the physical contents of a column in one row in a table, but in the real world a column header is a better way to think of them (ie LastName, Gender, etc) A projection is A projection is another form of query that returns all of the records from the relation, but only select attributes or fields. Note: I've been a database programmer 20+ years and I've never heard of anyone refer to a projection query in the workplace. I'm sure this is technically correct, but the vast majority of queries you will perform in the real world will be "projection" queries since you will request specific fields instead of every field in most cases. Database administrators Database administrators have a long list of important responsibilities, with a focus on the design, development, and support of database management systems (DBMSs). Their tasks include installation, maintenance, performance analysis, and troubleshooting. There are specific applications, performance tuning parameters, account creation, and procedures associated with the DBMS that are separate from those of system administrators and web administrators. The database administrator may also be involved with the integration of data from older systems to new. As many or most database systems are now available over the Internet (or at least over local area networks), the administrator must also ensure proper security measures for remote access. A database administrator is often expected to play a role in application design and development. This may be by assisting the application developers with the design of the databases needed to effectively support those applications. This requires a unique set of skills that include database modeling, schema development, normalization, and performance tuning. Business intelligence Business intelligence is a special application of the DIKW hierarchy when employed as a specific information system to help an organization reach its strategic goals. One of the main purposes of a BI system is to improve the timeliness and quality of the information that goes into making strategic decisions. Unlike an operational decision (e.g., how much and when to order new supplies), a strategic decision is typically one that covers a long time frame (e.g., five years) and may involve such issues as whether or not an organization should expand into a new geographic region ETL Extract, Transform, Load Data Warehouse A collection of organized databases. Data Mart the means by which users obtain data or information out of the data warehouse. OLTP Online Transaction Processing OLAP Online Analytical Processing. In OLAP data are processed through a suite of analysis software tools. You might think of OLAP as sitting on top of the data warehouse so that the user can retrieve data from the data warehouse and analyze the data without having to separate the database management system (DBMS) operations from the more advanced analysis operations. OLAP operations include slicing, dicing, drilling down (or up), rolling-up, and pivoting the data. Slicing creates a subset of the data by reducing the data from multiple dimensions to one dimension. Dicing is the same as slicing except that the result can be in multiple dimensions, but still obtaining a subset of the data. Drilling up and down merely shifts the view of the data. Drilling down provides more detail and drilling up provides summarized data. Rolling up is similar to drilling up in that it summarizes data, but in doing so, it collapses the data from multiple items (possible over more than one dimension) into a single value. Pivot rotates data to view the data from a different perspective. ODBC Open Database Connectivity JDBC Java Database Connectivity SQL Structured Query Language (SQL). SQL is a standard query language that is used to communicate in many DBMSs. SELECT is used to inform the DBMS what fields or attributes are of interest FROM is used to inform the DBMS what tables are to be interrogated by the query and, if more than one table contains the data of interest, how they are to be combined or joined. WHERE is used to inform the DBMS of the specific criteria the data should match to be returned as the output of the query. What does an IT department do? The obvious answer is that an IT department supports the day-to-day technology needs of an organization. More broadly, an IT department is charged with helping an organization achieve its strategic goals. Mission identifies the reason the organization exists, including the people it serves and the principles and standards of practice that should guide everyday operations. Vision describes future aspirations of the organization. Goals translate the organization's philosophy into specific, measurable outcomes the organization plans to achieve. Network administrators Are responsible for the installation and maintenance of hardware and software that make up a computer network. Network administrators may also be required to secure the network; this task may be accomplished in conjunction with other IT personnel such as system administrators. Systems administrators The system administrator will, at a minimum, be required to install and configure operating systems on the organization's machines, install new hardware, perform software upgrades and maintenance, and handle user administration. Other duties include performing backup and recovery, system monitoring, performance tuning, and troubleshooting. The system administrator may also be involved with application development and deployment, system security and reliability, and have to work with networked file systems. The system administrator would most likely have to perform some programming through shell scripting so that repetitive tasks can be automated. A greater amount of programming might be required depending on the organization's size and staff. Policy creation and IT infrastructure planning may also be tasks assigned to system administrators. Web administrator also known as a webmaster, but more precisely referred to as a web server administrator, is responsible for maintaining websites. This differs from the development of websites. Specifically, the web administrator must install, configure, maintain, secure, and troubleshoot the web server. The web administrator may or may not be responsible for the hardware. Database administrators have a long list of important responsibilities, but with a focus on the design, development, and support of database management systems (DBMSs). Tasks will include installation, maintenance, performance analysis, and troubleshooting as with the other administrative areas. There are specific applications, performance tuning parameters, and procedures associated with the DBMS that are separate from those of system administrators and web administrators. The database administrator may also be involved with the integration of data from older systems to newer systems. As many or most database systems are now available over the Internet (or at least over local-area networks), the administrator must ensure proper security measures for remote access as well. Unlike a web administrator who will probably not be involved in web development, a database administrator is often expected to play a role in application design and development. Computer support specialist is somewhat of an umbrella term. Certainly, some of the roles of the support specialist could be a responsibility of a system administrator. The support specialist primarily operates as a trainer and troubleshooter. Training tasks may include the production of material such as technical manuals, documentation, and training scripts. What are the four project phases? Initiation Planning Executing & controlling Closing Project management is the application of knowledge, skills and techniques to execute projects effectively and efficiently. Project Initiation consists of three key elements: problem definition, resource allocation, and risk assessment Project Planning During the planning phase of a project, the team must determine the objectives and activities, organize the activities, and estimate time and costs required to successfully complete the project. Project Executing the Plan and Controlling the Project With proper preparation in place, the team begins to execute the plan. This may involve hiring or training personnel, purchasing hardware, and developing, testing, and deploying a product or service. The specifics of this phase are dependent on the previously identified project scope. While the plan is being executed, the project manager must track the progress of the project in order to mitigate any problems that could impact the project. The project manager uses the information from Phases 1 and 2 to help ensure the project stays on track in terms of time, capital, and scope, and will be completed successfully. To facilitate this process, the project manager generates the various reports described below and uses these on an ongoing basis. Variance Reports indicate differences between planned resources (what has been allocated for each activity or task) and actual resources (what has been used thus far in the project). Status Reports indicate the state of the project. The status report provides specific information on the achievement of objectives and completion of activities. It is critical to track such progress, particularly for those activities that are dependent on other activities. Resource Allocation Reports indicate how time and capital have been used thus far for the project. This report, which is tied to the budget, keeps everyone informed of where the project is in relation to the resources originally allocated for the project. Together, all of these reports provide a project manager and the team with valuable information and transparency that can facilitate keeping a project on track, within budget, and successful. Project Closing Once all deliverables have been met, a project is considered closed. In reality, though, organizations often build in a testing phase to gather data about aspects of a project that may need to be fine-tuned in the future. Scope Creep the team or other individuals may realize that additional features are needed or could be beneficial. This is commonly referred to as scope creep. Unnecessary Requirements during the early phases of a project, requirements that are not actually needed are included in the project plan. Often, these requirements are in the form of "nice to have" features, which are mistaken for essentials or included without thought of how this may impact resource allocation. These unnecessary requirements consume resources that may be better used elsewhere and create an unintended risk. SDLC System Development Life Cycle is a process for planning, creating, testing, and deploying information systems, including hardware and software. 6 steps in SDLC Preliminary investigation Analysis Logical design Physical design Implementation Maintenance Preliminary investigation SDLC begins when an organization discovers a problem or opportunity that a new system could be developed to address. During this first step, the team assesses the feasibility of the proposed project and selects a development methodology. Analysis The team determines the user requirements for the new system and develops logical models of the system (i.e., graphic displays that demonstrate the relationships between resources, activities, and outputs and outcomes). Logical design During this step, the logical models developed during the second step are revised to ensure that the new system will meet the user requirements identified in the first step. Physical design The logical models are converted into physical models. These physical models are still abstractions of the system that will be built later, but they are now more complete and may include network maps and descriptions of servers and other devices to be used in the system. Implementation Programmers begin converting the models from the previous steps into the actual system, for instance, by developing databases and other software programs that will be needed. This step also includes installing hardware, testing the system, and training the end users. Maintenance During this step, modifications or corrections to the system are made. Alpha Testing occurs where the system will be used. For example, software may be tested by a client or by a specific department within an organization. During alpha testing, system developers often assist end users as they interact with the new system. It is common for simulated data to be used to prevent any damage to a user's actual data. Beta testing the tests are performed by the end user without any assistance from the system developers. Beta testing uses actual (i.e., live) data in the real working environment. User acceptance testing is employed to assess whether the system does what the user expects and to ensure that it functions in a way that is useful to the user. Alpha testing, beta testing, and user acceptance occur during the ____________ phase. implementation During deployment what 3 things usually occur? System conversion (which means replacing the old system with the new system) Final documentation End-user training Direct Conversion The old system is "turned off" and the new system is "turned on" at a specific date and time. After the conversion, the old system is no longer available to end users. Parallel Conversion There is a period of time in which both systems (the old and the new) are operating concurrently. This is done so that the output of the new system can be compared with the output of the old system. Once it is confirmed that everything is working as expected, the old system is shut down and the new system continues to operate. Pilot Conversion This involves starting the conversion with a portion of the end users, for instance in a specific geographic region or a department in an organization. The team can roll this out using either the direct approach, or the parallel approach. Once the pilot program is confirmed to be operating according to plan, the system is deployed on a larger scale. Phased Conversion The team deploys a subset of the system first, rather than deploying the whole system at once. The old system continues to offer some functionality until all subsets of the new system have been turned on and the new system is confirmed to be working effectively. What is Business Continuity? Business continuity is the activity performed by an organization to ensure that critical business functions will be available to customers, suppliers, regulators, and other entities that must have access to those functions. Full backup when everything on the hard drive is copied each and every time a backup is performed. Incremental backup An initial, full backup is completed and then subsequent backups only capture the changes since the last backup. Data Mirroring the operating system writes data (and changes to the data) to multiple hard drives at the same time. Off-Site Storage Organizations may choose to use a hot site, cold site, or site sharing. Hot site a physical location where an organization can move its operations. A hot site includes everything for normal business operations, including HVAC systems, hardware, software, and backed-up data. Hot sites allow for the quickest return to business (often without any delay), but they are expensive. Cold site a physical location, but unlike a hot site, it is not equipped with hardware, servers, and the full range of items a hot site has. A cold site is more like a shell that can be used for operations should the need arise. It is less costly than a hot site, but the organization must be able to purchase, receive, and install all the necessary hardware and software before operations can continue. Site sharing refers to having multiple data centers located in disparate regions. This approach is typically used by large organizations, which can shift critical functions to other sites when one site is impacted by a disaster. The Internet of Things (IoT) refers to the myriad types of devices that can and will be connected to the Internet in the next few years. Big Data refers to data sets that are so enormous and multifaceted that they will require more sophisticated database management/processing tools than we currently use. SaaS Through Software as a Service (SaaS), businesses can access and use software through the Internet. Companies in many industries now use Google Docs and other programs that use SaaS. With SaaS, companies no longer have to purchase hardware and software to manage tasks such as payroll and e-mail, and these applications can be accessed by employees anywhere, anytime. PaaS The intention with Platform as a Service is to be able to quickly and reliably develop and deliver applications. Now, teams of developers located around the world can collaborate on the development of an app by accessing the same environment in real-time. This form of cloud computing is offered as a service by some major organizations, such as Amazon and Google, and used extensively by app developers. IaaS With Infrastructure as a Service, all the resources (e.g., servers, data storage) an IT department needs are located outside of the organization and are accessible by anyone, anywhere. Ethics defined as a code of moral conduct or a set of principles that govern behavior. Privacy under what circumstances should an administrator view other people's files? Under what circumstances should a company use the data accumulated about its customers? Ownership who owns the data accumulated and the products produced by the organization? Control to what degree will employee actions be monitored? Accuracy to whom does the responsibility of accuracy fall, specific employees or all employees? To what extent does the company work to ensure that potential errors in data are eliminated? Security to what extent does the company ensure the integrity of its data and systems? CIA Confidentiality Integrity Availability Confidentiality requires that data be kept secure so that they are not accidentally provided to unauthorized individuals and cannot be obtained by unauthorized users. Integrity requires that data is correct. This requires at a minimum three different efforts. First, data gathering must include a component that ensures the accuracy of the collected data. Second, data must be entered into the system accurately. But third and most importantly, data modification must be tracked. Availability requires that information is available when needed. Authenticity ensures that the data, information, or resource is genuine. This allows a valid transaction to take place (whether in person or over the Internet). Authenticity is most commonly implemented by security certificates or other form of digital signature. Non-repudiation is a legal obligation to follow through on a contract between two parties. In e-commerce, this would mean that the customer is obligated to pay for the transaction and the business is obligated to perform the service or provide the object purchased. HIPAA Health Insurance Portability and Accountability Act. This act protects the privacy of an individual's health records. Privacy Act of 1974 the earliest piece of legislation that pertains to the collection and usage of personal data, this act limits actions of the federal government. The act states that: No agency shall disclose any record which is contained in a system of records by any means of communication to any person, or to another agency, except pursuant to a written request by, or with prior written consent of, the individual to whom the record pertains. The act also states that federal agencies must publicly make available the data that they are collecting, the reason for the collection of the data, and the ability for any individual to consult the data collected on them to ensure its integrity. The Family Educational Rights and Privacy Act of 1974 (FERPA) gives students the right to access their own educational records, amend those records should information be missing or inaccurate, and prevent schools from disseminating student records without prior authorization. This is an important act because it prevents faculty from sharing student information (e.g., grades) with students' parents unless explicitly permitted by the students. In addition, it requires student authorization to release transcripts to, for instance, graduate schools or prospective employers. Electronic Communication Privacy Act of 1986 this act establishes regulations and requirements to perform electronic wiretapping over computer networks (among other forms of wiretapping). Computer Matching and Privacy Protection Act of 1988 amends the Privacy Act of 1974 by limiting the use of database and other matching programs to match data across different databases. Without this act, one agency could potentially access data from other agencies to build a profile on a particular individual. Drivers Privacy Protection Act of 1994 prohibits states from selling data gathered in the process of registering drivers with drivers' licenses (e.g., addresses, social security numbers, height, weight, eye color, photographs). Digital Millennium Copyright Act of 1998 (DMCA) implements two worldwide copyright treaties that makes it illegal to violate copyrights by disseminating digitized material over computer. This law includes clauses that make it illegal to post on websites or download from websites copyrighted material whether that material originally existed as text, sound, video, or program code. Additionally, the act removes liability from Internet Service Providers who are providing Internet access for a criminal prosecuted under this act. As a result of this law, YouTube was not held liable for copyrighted content posted to the YouTube site by various users; however, as a result, YouTube often orders the removal of copyrighted material at the request of the copyright holder. Digital Signature and Electronic Authentication Law of 1998 (SEAL) permits the use of authenticated digital signatures in financial transactions and requires compliance of the digital signature mechanisms. It also places standards on cryptographic algorithms used in digital signatures. This was followed 2 years later with the Electronic Signatures in Global and National Commerce Act. Security Breach Notification Laws since 2002, most U.S. states have adopted laws that require any company (including nonprofit organizations and state institutions) notify all parties whose data records may have been compromised, lost, or stolen in the event that such data has been both unencrypted and compromised. Public public information might include names and addresses (since this information is available through the phone book). Sensitive might include e-mail addresses. Although this is not public information, it is information that will not be considered a threat to a person's privacy if others were to learn of it. Private is information that could be a threat if disclosed to others such as social security and credit card numbers, or health and education information. This information is often protected from disclosure by federal legislation. Confidential consists of information that an organization will keep secret, such as patentable information and business plans. Strategic Risk Analysis steps Identify information assets. Identify vulnerability of assets. Determine threats based on vulnerabilities. Prioritize risks. Develop and enact policies as necessary. [Show More]
Last updated: 10 months ago
Preview 1 out of 68 pages
Buy this document to get the full access instantly
Instant Download Access after purchase
Add to cartInstant download
We Accept:
Reviews( 0 )
$11.50
Document information
Connected school, study & course
About the document
Uploaded On
Sep 01, 2023
Number of pages
68
Written in
Additional information
This document has been written for:
Uploaded
Sep 01, 2023
Downloads
0
Views
85

.png)