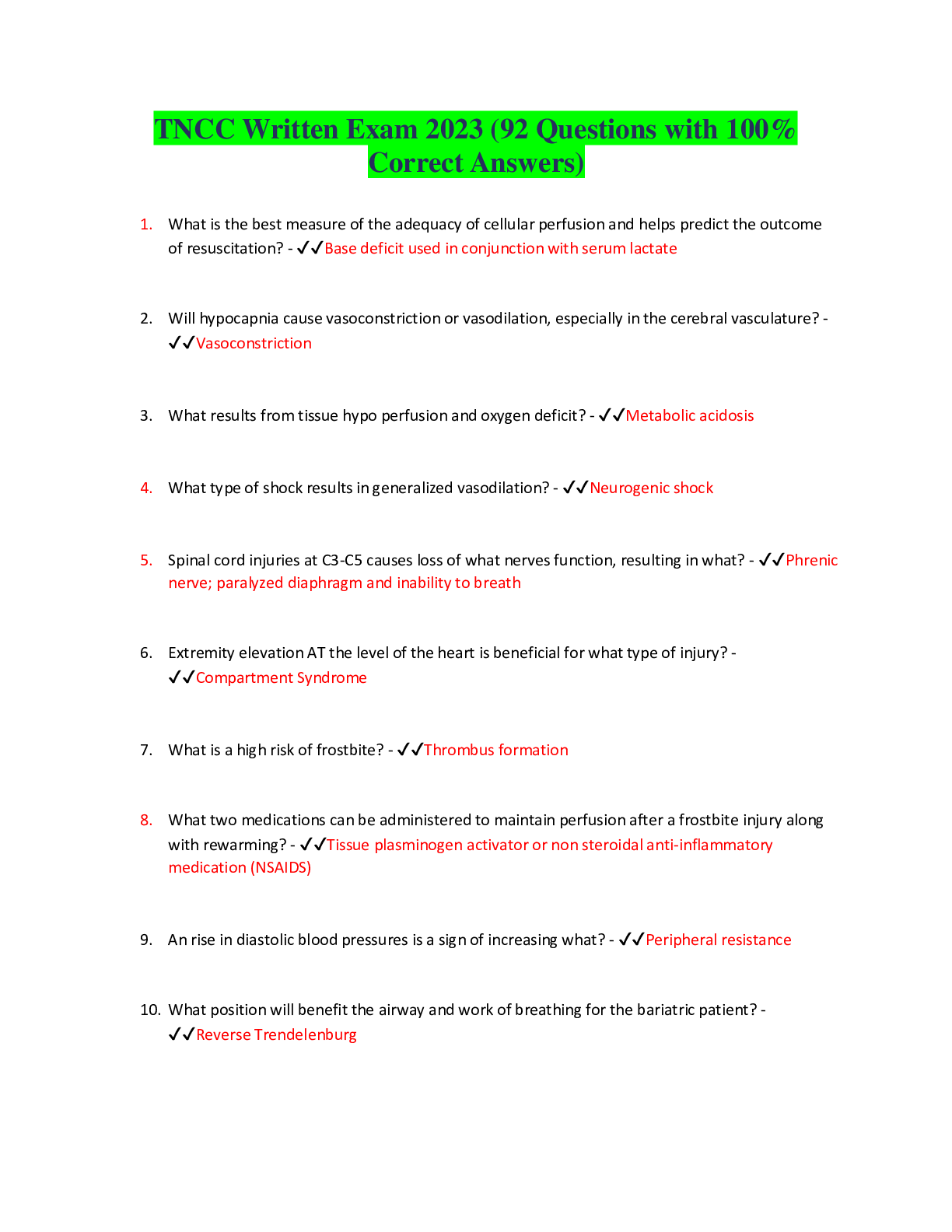
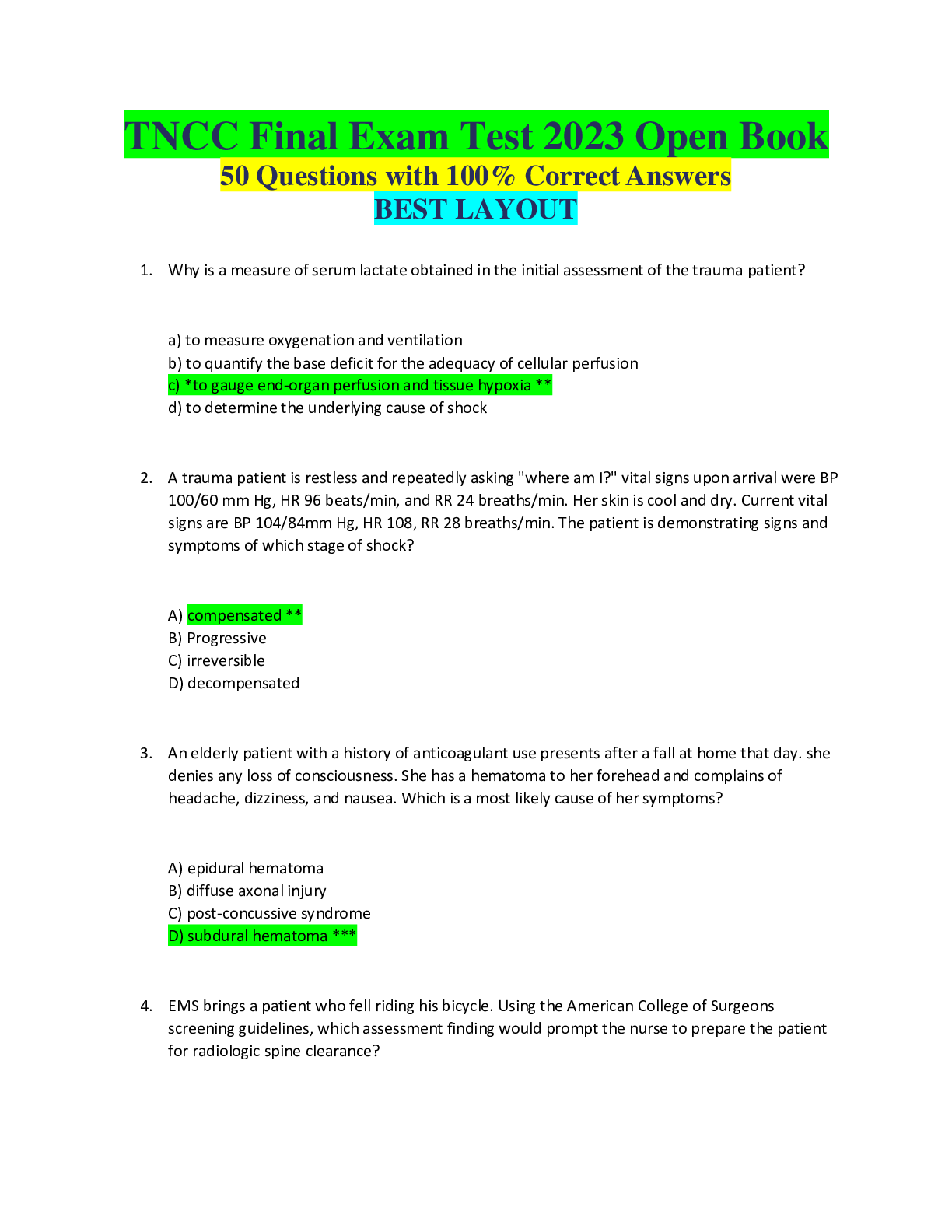
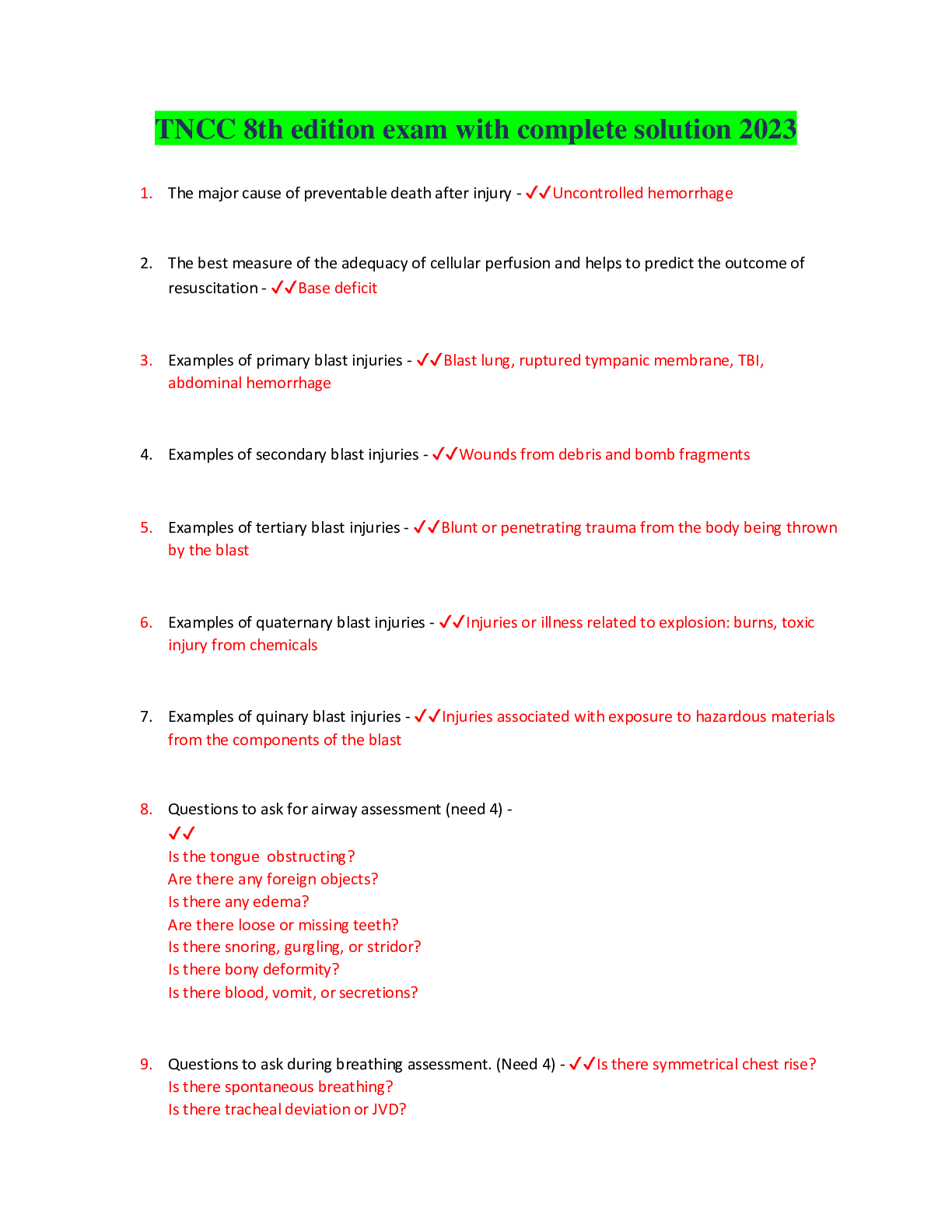
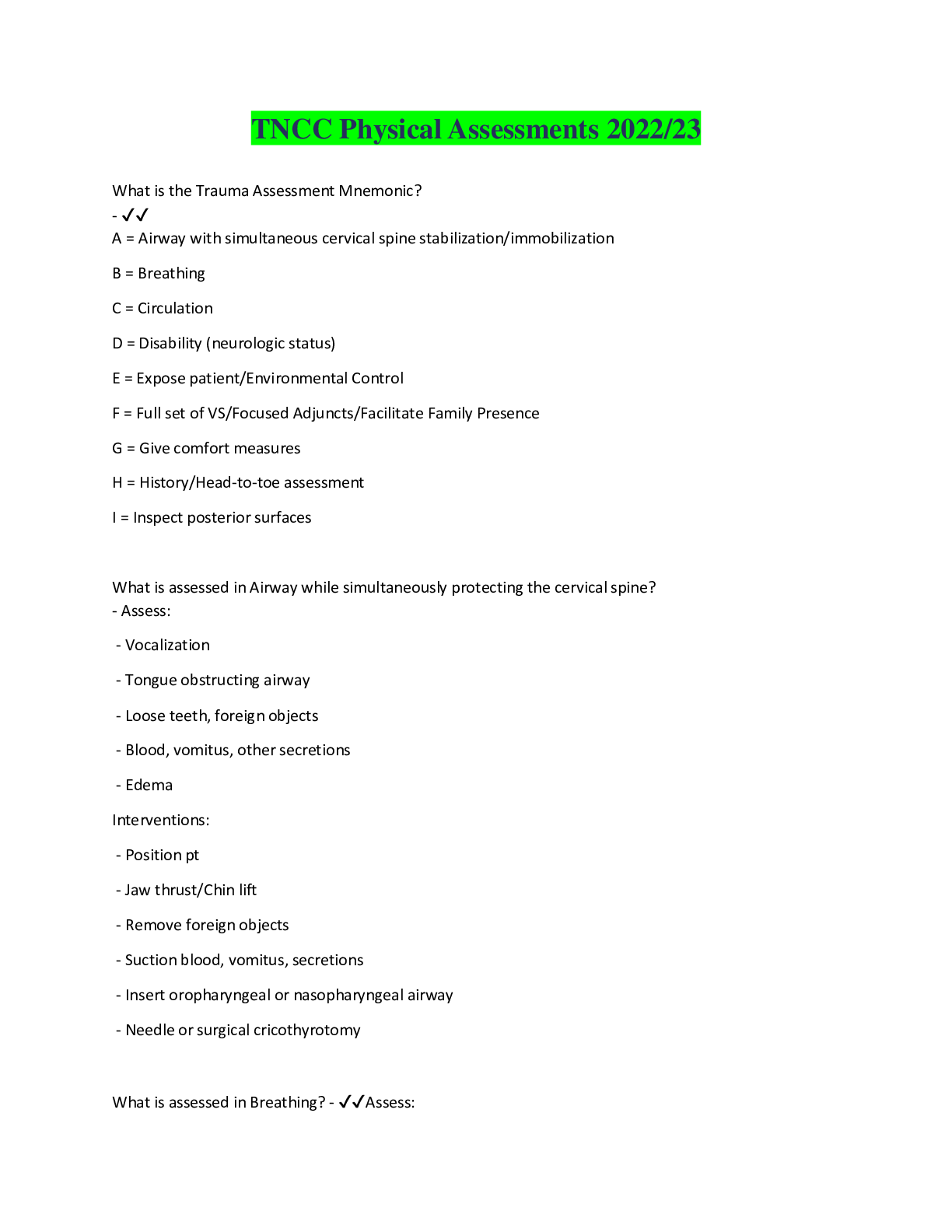
Computer Science > EXAM > CyberArk Defender Exam | 60 Questions with 100% Correct Answers (All)
CyberArk Defender Exam | 60 Questions with 100% Correct Answers
Document Content and Description Below
In order to connect to a target device through PSM, the account credentials used for the connection must be stored in the vault? - ✔✔FALSE. Because the user can also enter credentials manually u... sing Secure Connect Which CyberArk components or products can be used to discover Windows Services of Scheduled Taks that use privileged accounts? - ✔✔Discovery and Audit (DNA) Auto Detection (AD) Accounts Discovery What conditions must be met in order to login into the vault as the Master user? - ✔✔Logon must be originated from the console of the Vault server or an EmergencyStation defined in DBParm.ini User must provide the correct master password.] Logon requires the Recovery Private Key to be accessible to the vault. When managing SSH keys, CPM automatically pushed the Public Key to the target systems. - ✔✔TRUE Which of the following can be configured in the Master Policy? - ✔✔Dual Control Exclusive Passwords One Time Passwords Password Aging Rules The primary purpose of exclusive accounts is to ensure non-repudiation (individual accountability). - ✔✔TRUE If a user is a member of more than one group that has authorizations on a safe, by default that user is granted [Show More]
Last updated: 1 year ago
Preview 1 out of 6 pages

Also available in bundle (1)
Bundle for CyberArk Defender Exams Compilation
Bundle for CyberArk Defender Exams Compilation
By Tessa 1 year ago
$12
3
Reviews( 1 )

by jnkdog96 · 1 year ago
Document information
Connected school, study & course
About the document
Uploaded On
Aug 12, 2022
Number of pages
6
Written in
Additional information
This document has been written for:
Uploaded
Aug 12, 2022
Downloads
1
Views
158



.png)
.png)
.png)

.png)
.png)

