Statistics > STUDY GUIDE > NURS 211>CIST 1601 Study Guide. (All)
NURS 211>CIST 1601 Study Guide.
Document Content and Description Below
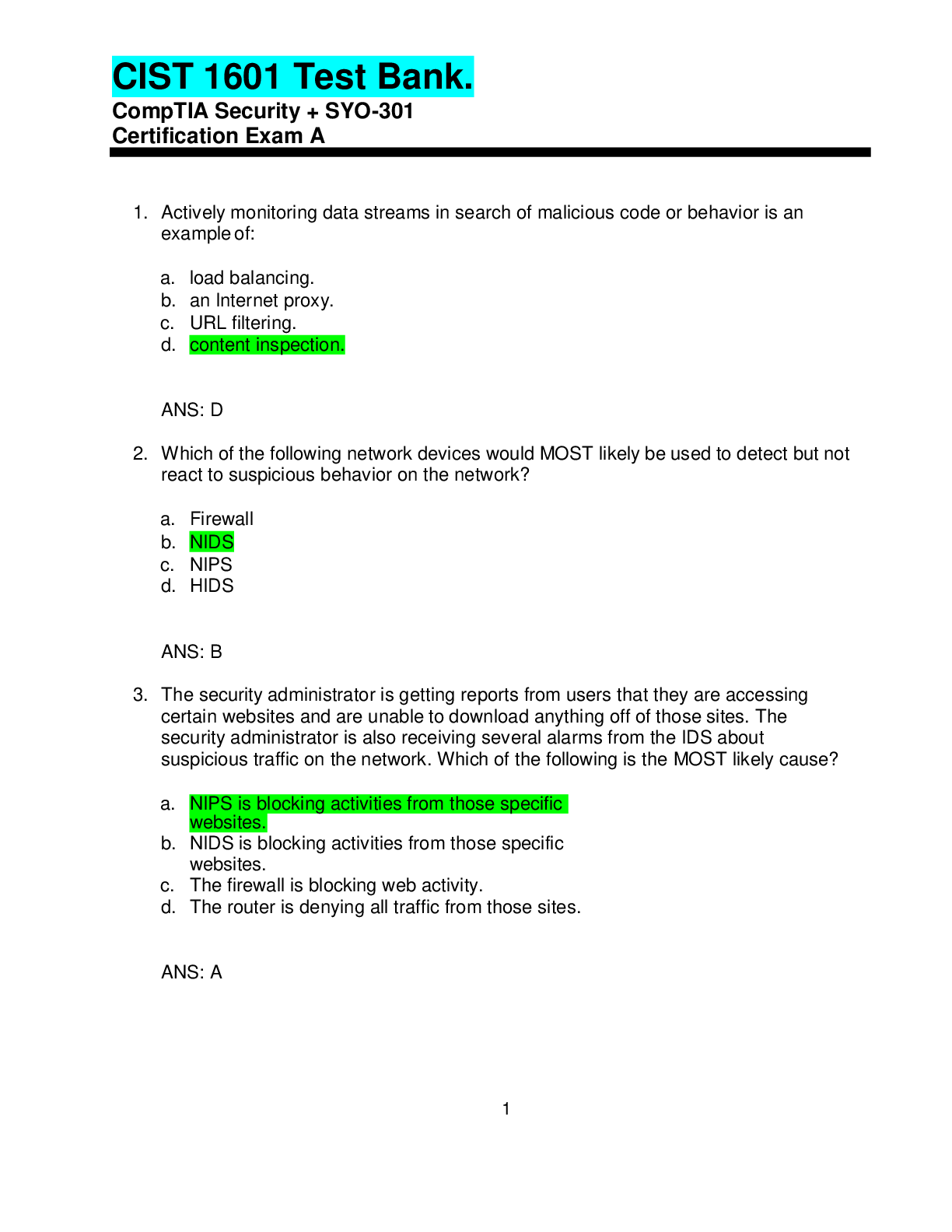
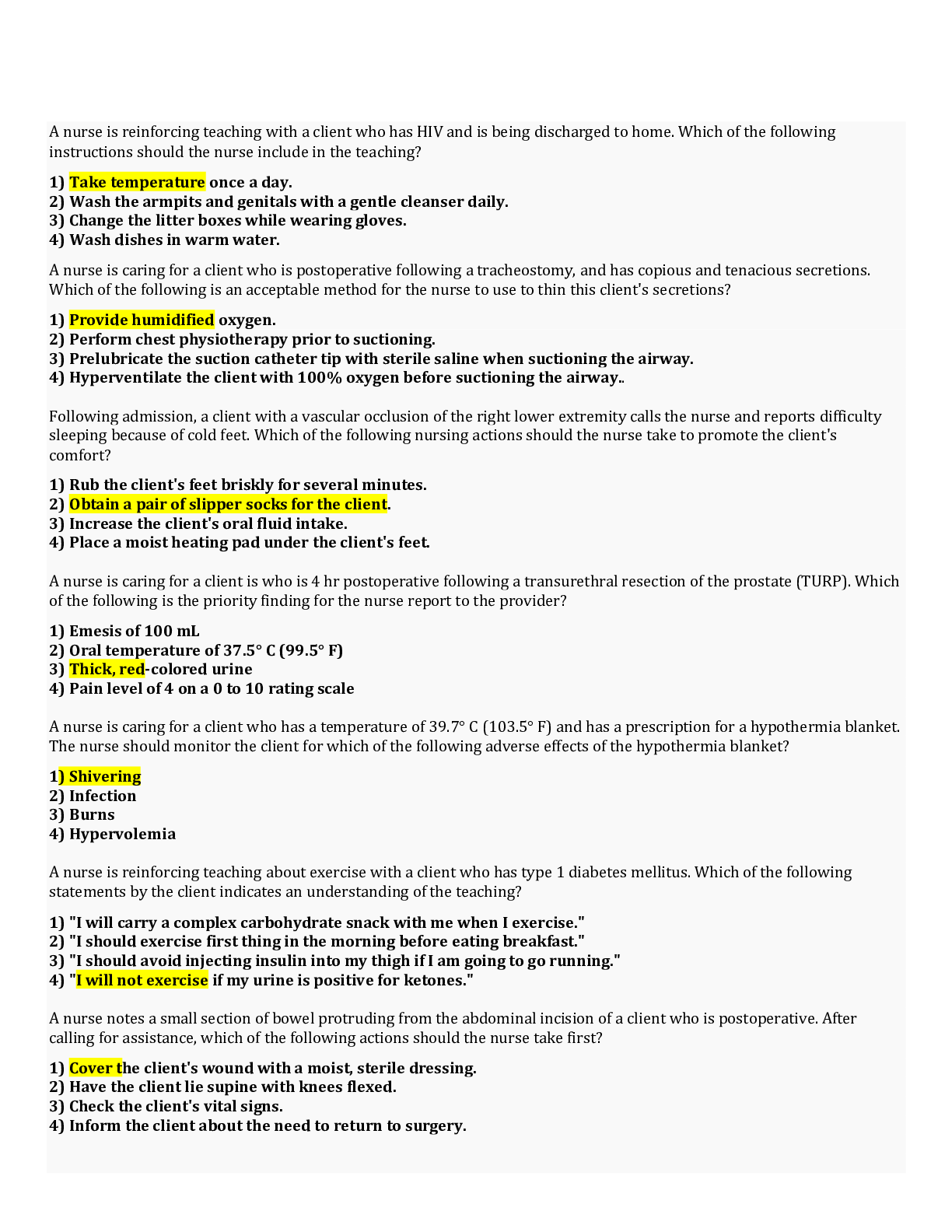
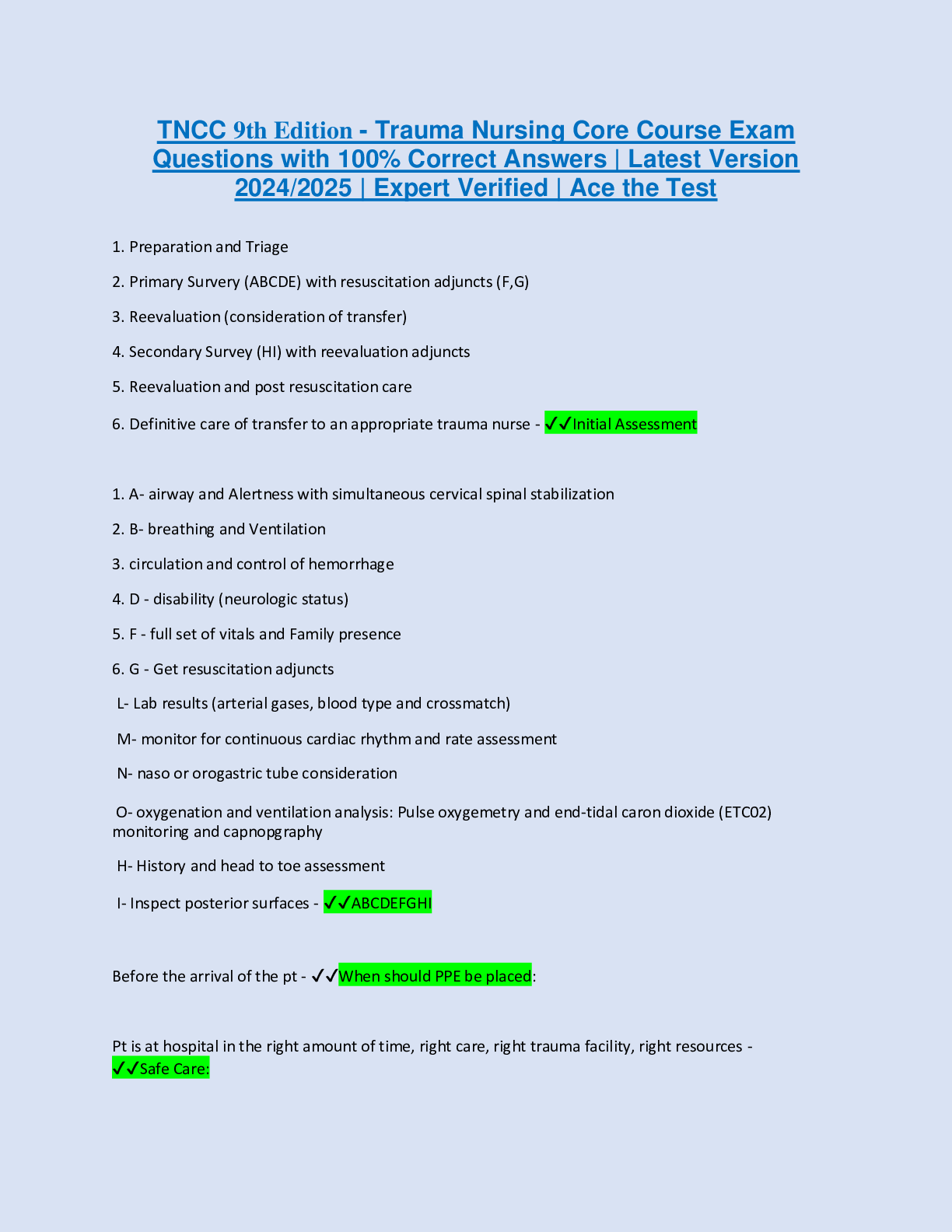
1. Actively monitoring data streams in search of malicious code or behavior is an example of: a. load balancing. b. an Internet proxy. c. URL filtering. d. content inspection. ANS: D 2. Which o... f the following network devices would MOST likely be used to detect but not react to suspicious behavior on the network? a. Firewall b. NIDS c. NIPS d. HIDS ANS: B 3. The security administrator is getting reports from users that they are accessing certain websites and are unable to download anything off of those sites. The security administrator is also receiving several alarms from the IDS about suspicious traffic on the network. Which of the following is the MOST likely cause? a. NIPS is blocking activities from those specific websites. b. NIDS is blocking activities from those specific websites. c. The firewall is blocking web activity. d. The router is denying all traffic from those sites. ANS: A 2 4. Which of the following tools provides the ability to determine if an application is transmitting a password in clear-text? a. Protocol analyzer b. Port scanner c. Vulnerability scanner d. Honeypot ANS: A 5. Which of the following can a security administrator implement to help identify smurf attacks? a. Load balancer b. Spam filters c. NIDS d. Firewall ANS: C 6. Which of the following functions is MOST likely performed by a web security gateway? a. Protocol analyzer b. Content filtering c. Spam filtering d. Flood guard ANS: B 7. Which of the following devices is often used to cache and filter content? a. Proxies b. Firewall c. VPN d. Load balancer ANS: A 3 8. Which of the following devices is used to optimize and distribute data workloads across multiple computers or networks? a. Load balancer b. URL filter c. VPN concentrator d. Protocol analyzer ANS: A 9. An IT administrator wants to provide 250 staff with secure remoteaccess to the corporate network. Which of the following BEST achieves this requirement? a. Software based firewall b. Mandatory Access Control (MAC) c. VPN concentrator d. Web security gateway ANS: C 10. Which of the following should be installed to prevent employees fromreceiving unsolicited emails? a. Pop-up blockers b. Virus definitions c. Spyware definitions d. Spam filters ANS: D [Show More]
Last updated: 1 year ago
Preview 1 out of 139 pages
Instant download
Instant download
Reviews( 0 )
Document information
Connected school, study & course
About the document
Uploaded On
Oct 07, 2020
Number of pages
139
Written in
Additional information
This document has been written for:
Uploaded
Oct 07, 2020
Downloads
0
Views
35

.png)