Information Technology > QUESTIONS & ANSWERS > Intro to Cryptography WGU C839 Module 3 Questions and Answers 100% Pass (All)
Intro to Cryptography WGU C839 Module 3 Questions and Answers 100% Pass
Document Content and Description Below
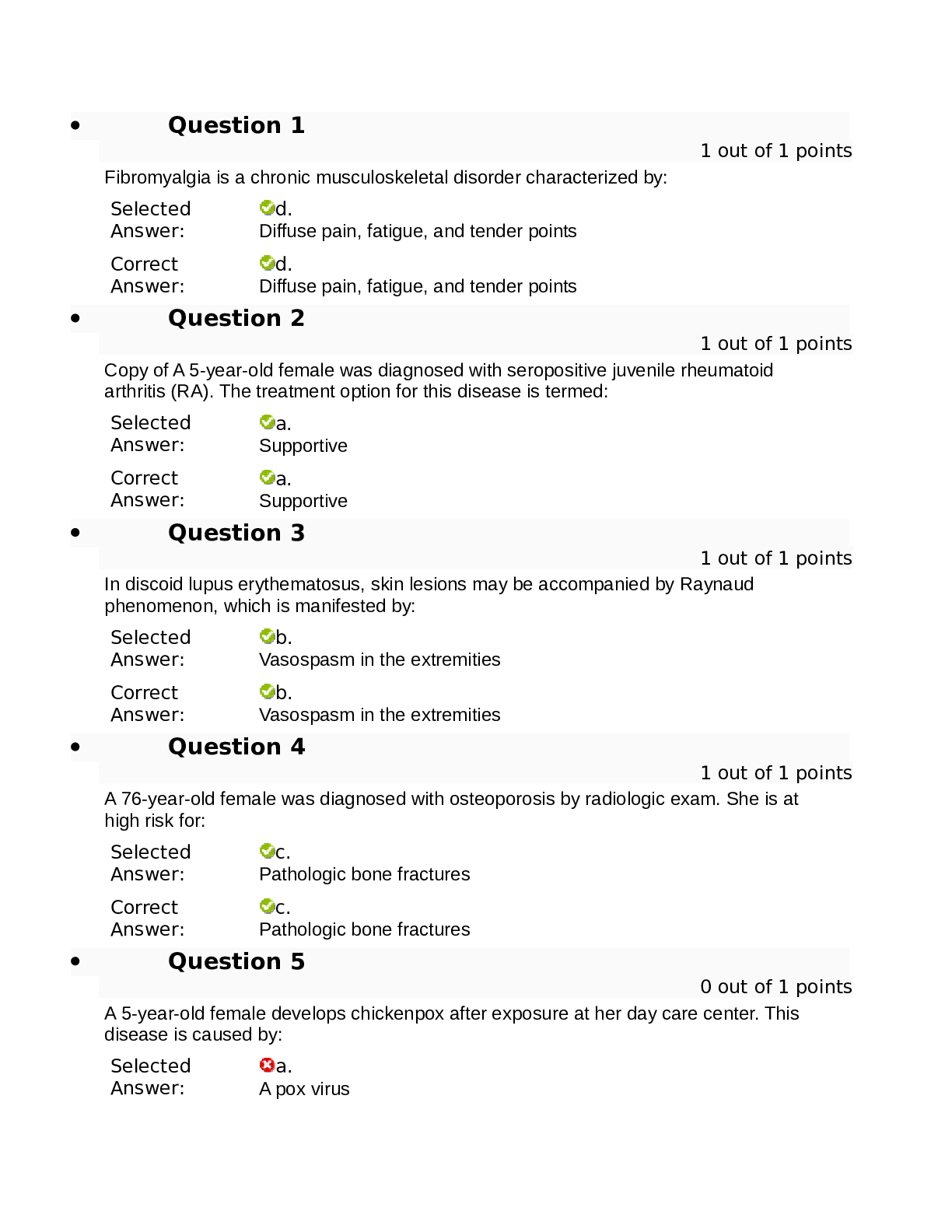
Consists of public and private keys The public key is made public by publishing to a directory or installed on a computer. The private key is kept secret Does not involve exchanging a secret key or... key exchange The public key is used to encrypt messages only the recipients private key can decrypt ✔✔Asymmetric Cryptography Slower then Symmetric algorithms provides a secure way to communicate provides a method of validation Non-repudiation ✔✔Disadvantages and Advantages of Asymmetric Crypto Denotes the natural numbers. These are also sometimes called the counting numbers. they are 1, 2, 3, etc. ✔✔N Denotes the integers. These are whole numbers -1, 0, 1, 2, etc. The natural numbers combined with zero and and the negative numbers ✔✔Z Denotes the rational number (ratios of integers). Any number that can be expressed as a ratio of two integers. i.e. 3/2, 17/4, 1/5 ✔✔Q Denotes the real numbers. This includes the rational numbers as well as numbers that cannot be expressed as a ratio of two integers, such as √2 ✔✔R Denotes imaginary numbers. These are numbers whose square is a negative √-1 - 1i ✔✔i [Show More]
Last updated: 1 year ago
Preview 1 out of 6 pages
Instant download
.png)
Buy this document to get the full access instantly
Instant Download Access after purchase
Add to cartInstant download
Reviews( 0 )
Document information
Connected school, study & course
About the document
Uploaded On
Oct 12, 2022
Number of pages
6
Written in
Additional information
This document has been written for:
Uploaded
Oct 12, 2022
Downloads
0
Views
104

.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
 answers.png)

 Coronary Artery Disease and Acute Coronary Syndrome.png)
.png)