CyberRookie CSX Fundamentals - Quiz 104 questions- WITH COMPLETE ANSWERS
Document Content and Description Below
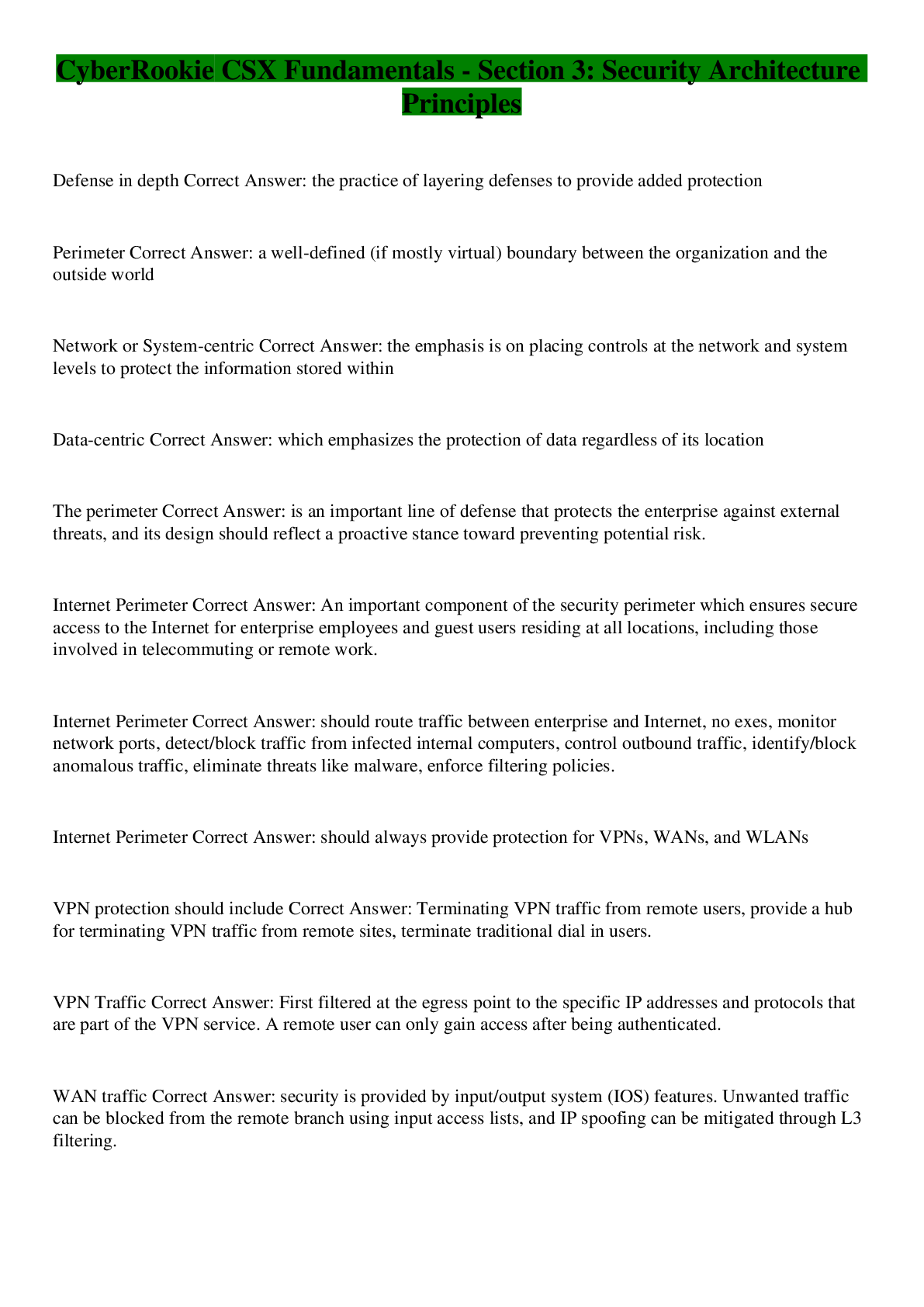
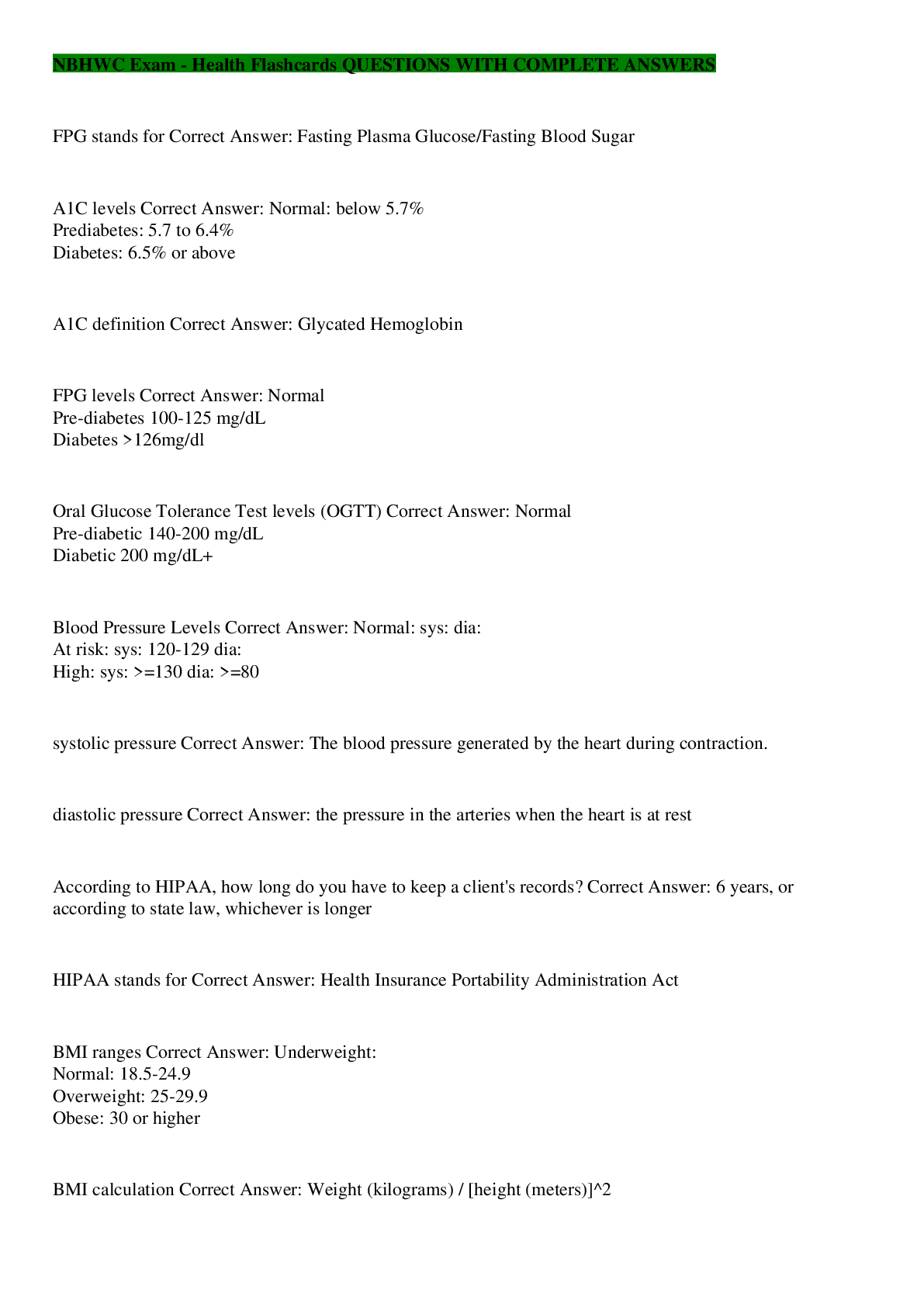
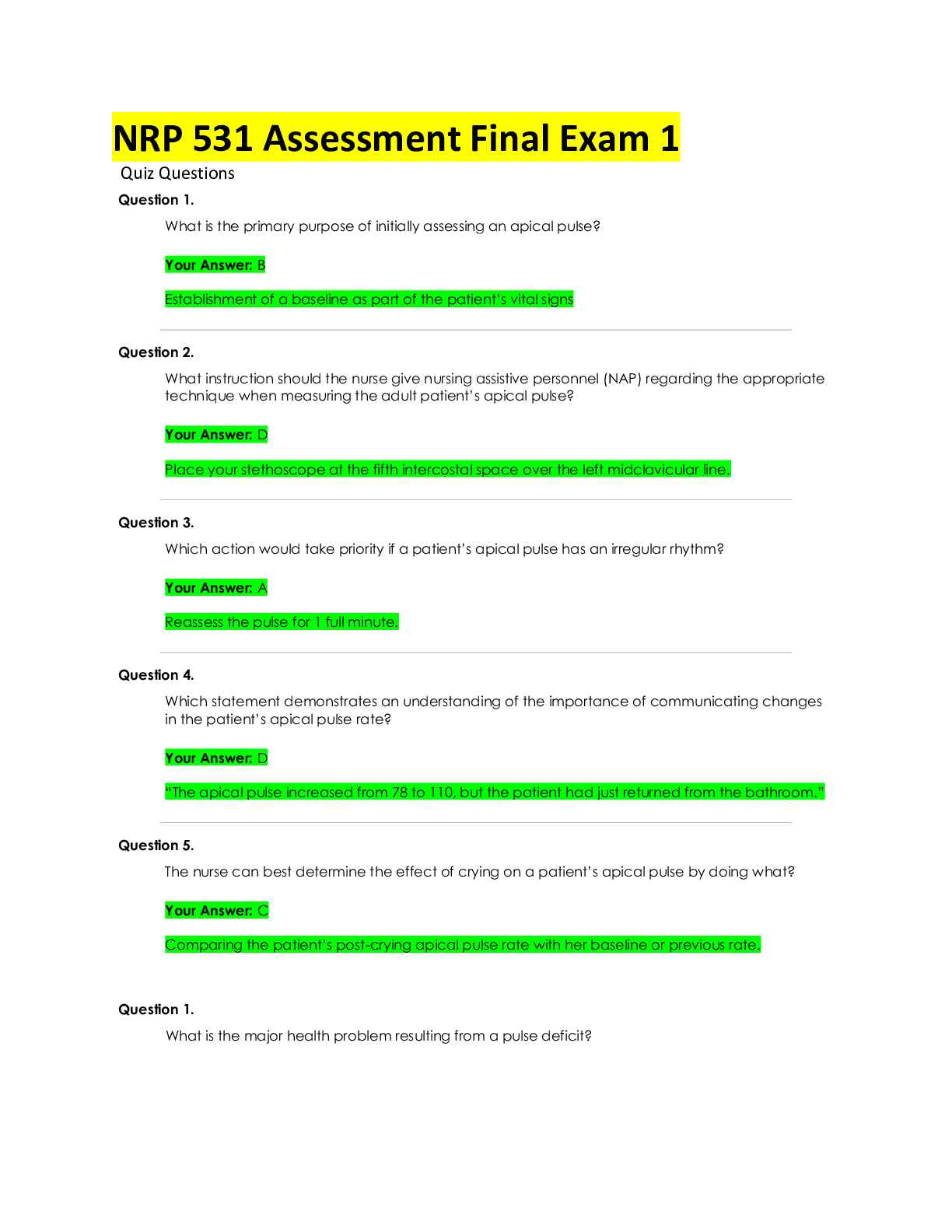
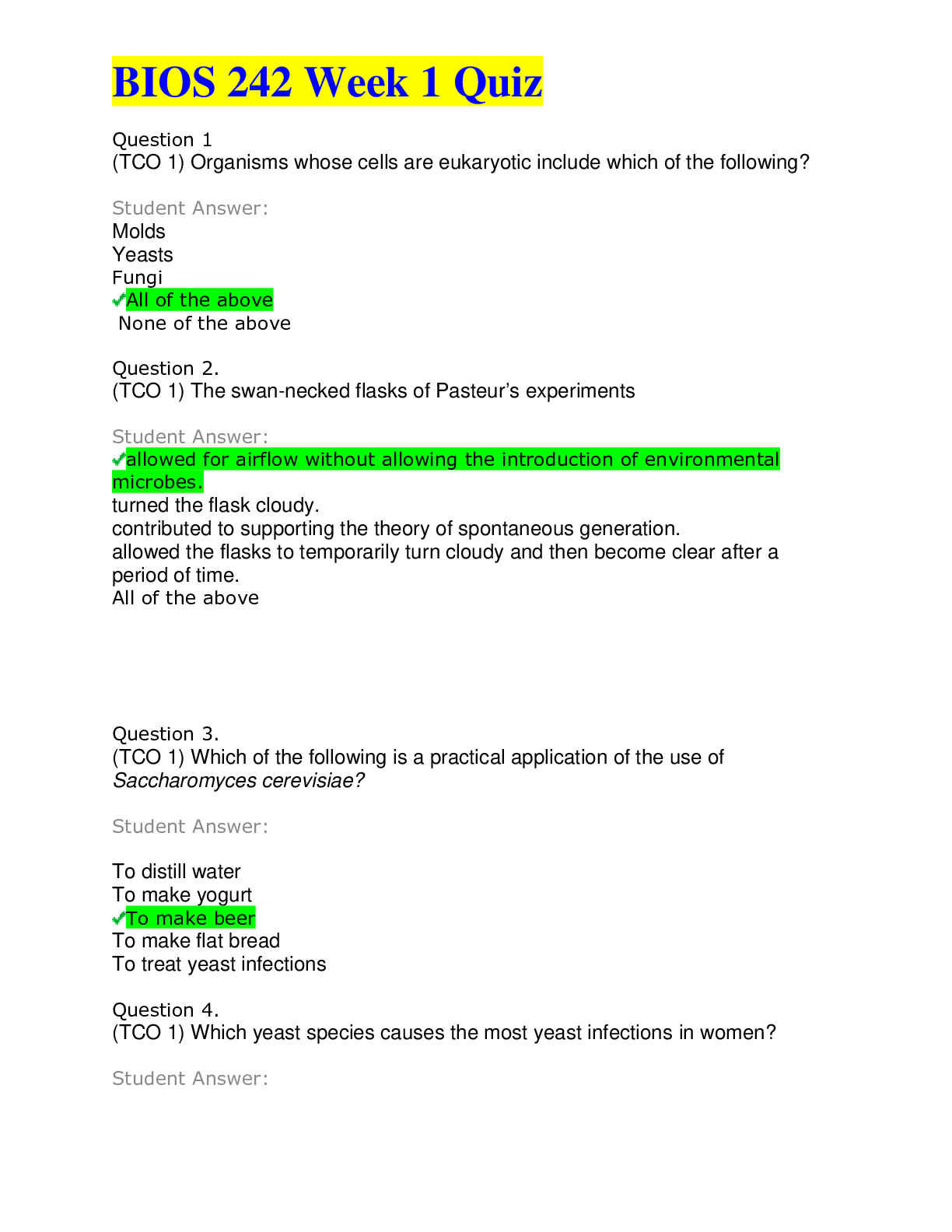
Three common controls used to protect the availability of information are Correct Answer: Redundancy, backups and access controls Governance has several goals, including Correct Answer: Providing... strategic direction, Ensuring that objectives are achieved, Verifying that organizational resources are being used appropriately, Ascertaining whether risk is being managed properly. According to the NIST framework, which of the following are considered key functions necessary for the protection of digital assets? Correct Answer: Protect, Recover, Identify The best definition for cybersecurity? Correct Answer: Protecting information assets by addressing threats to information that is processed, stored or transported by interworked information systems Cybersecurity role that is charged with the duty of managing incidents and remediation? Correct Answer: Cybersecurity management The core duty of cybersecurity is to identify, respond and manage Correct Answer: risk to an organization's digital assets. A threat Correct Answer: is anything capable of acting against an asset in a manner that can cause harm. A asset Correct Answer: is something of value worth protecting. A vulnerability Correct Answer: is a weakness in the design, implementation, operation or internal controls in a process that could be exploited to violate the system security The path or route used to gain access to the target asset is known as a Correct Answer: attack vector In an attack, the container that delivers the exploit to the target is called Correct Answer: payload Policies Correct Answer: communicate required and prohibited activities and behaviors. Rootkit Correct Answer: is a class of malware that hides the existence of other malware by modifying the underlying operating system. Procedures Correct Answer: provide details on how to comply with policies and standards. Guidelines Correct Answer: contain step-by-step instructions to carry out procedures. [Show More]
Last updated: 1 year ago
Preview 1 out of 8 pages
Buy this document to get the full access instantly
Instant Download Access after purchase
Add to cartInstant download
We Accept:
Reviews( 0 )
$10.00
Document information
Connected school, study & course
About the document
Uploaded On
Oct 31, 2022
Number of pages
8
Written in
Additional information
This document has been written for:
Uploaded
Oct 31, 2022
Downloads
0
Views
27



.png)