Computer Science > EXAM > CyberRookie CSX Fundamentals - Section 4: Security of Networks, Systems, Applications and Data (All)
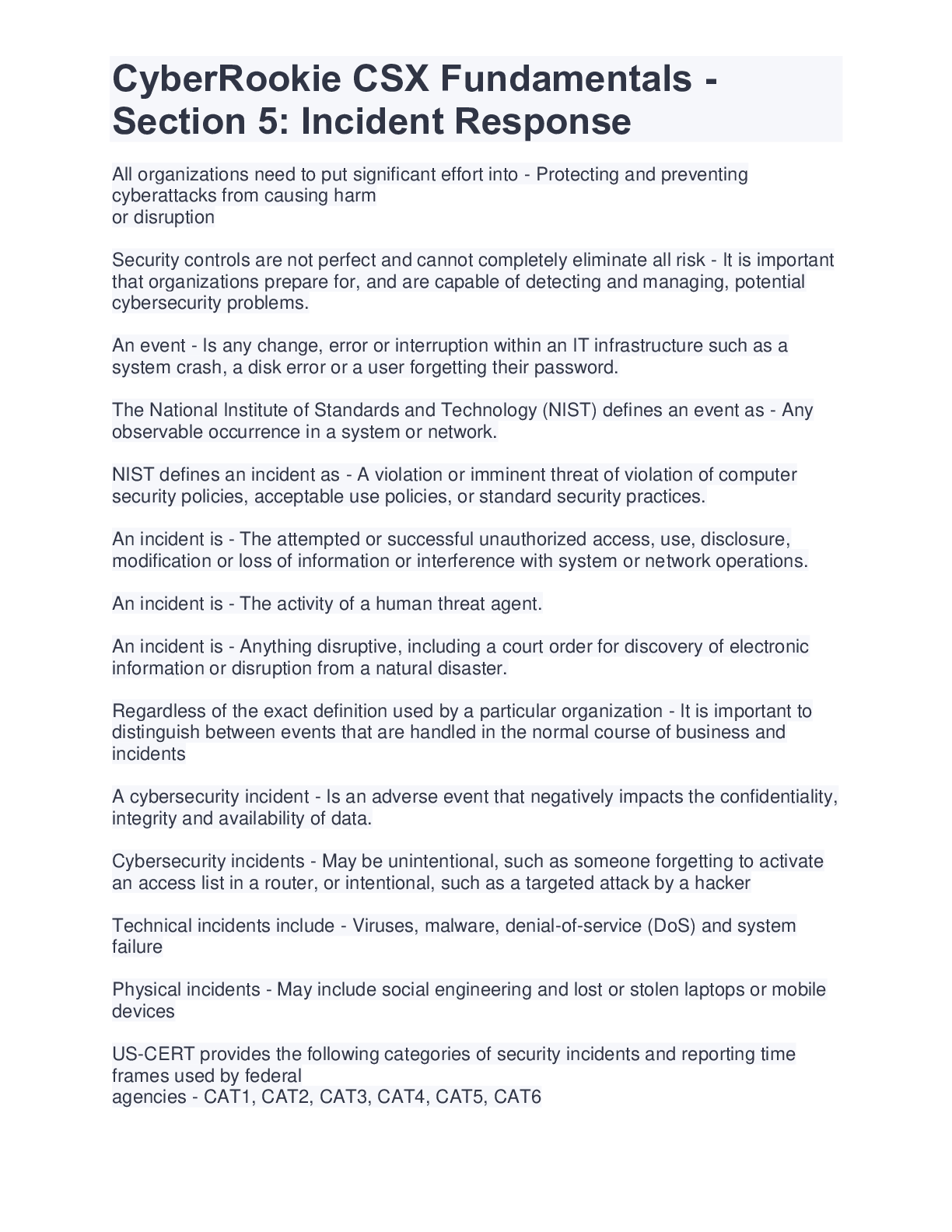
CyberRookie CSX Fundamentals - Section 4: Security of Networks, Systems, Applications and Data
Document Content and Description Below
risk Correct Answer: Is defined as the possibility of loss of a digital asset resulting from a threat exploiting a vulnerability cyberrisk assessment Correct Answer: Of these attributes of risk m... ust be analyzed to determine an organization's particular risk. risk assessment methodology inputs Correct Answer: Asset identification, threat assessment and vulnerability assessment cyberrisk assessment Correct Answer: Process begins with an examination of the risk sources (threats and vulnerabilities) for their positive and negative consequences. risk Correct Answer: Can be ranked according to likelihood and impact. Information used to estimate impact and likelihood usually comes from Correct Answer: Past experience or data and records, Reliable practices, international standards or guidelines, Market research and analysis, Experiments and prototypes, Economic, engineering or other models, Specialist and expert advice cyberrisk assessment Correct Answer: Existing controls and other mitigation strategies are evaluated to determine the level and effectiveness of risk mitigation currently in place and identify deficiencies and gaps that require attention. If risk is not properly analyzed Correct Answer: The implementation of security is left to guesswork. risk analyses Correct Answer: Can be oriented toward one of the inputs, making the risk assessment asset-oriented, threat-oriented or vulnerability-oriented Asset Correct Answer: Important assets are defined first, and then potential threats to those assets are analyzed. Vulnerabilities are identified that may be exploited to access the asset. Threat Correct Answer: Potential threats are determined first, and then threat scenarios are developed. Based on the scenarios, vulnerabilities and assets of interest to the adversary are determined in relation to the threat. Vulnerability Correct Answer: Vulnerabilities and deficiencies are identified first, then the exposed assets, and then the threat events that could be taken advantage of are determined. risk assessments Correct Answer: Some organizations will perform these from more than one orientation to compensate for the potential bias and generate a more thorough analysis. Once risk is identified and prioritized Correct Answer: Existing controls should be analyzed to determine their effectiveness in mitigating the risk. This analysis will result in a final risk ranking based on risk that has adequate controls, inadequate controls and no controls. A very important criterion in control selection and evaluation Correct Answer: Is that the cost of the control (including its operation) should not exceed value of the asset it is protecting. Takes considerable planning and knowledge of specific risk assessment methodologies Correct Answer: Choosing the exact method of analysis, including qualitative or quantitative approaches and determining the analysis orientation For the risk assessment to be successful Correct Answer: The risk assessment process should fit the goals of the organization, adequately address the environment being assessed and use assessment methodologies that fit the data that can be collected Assessment scope Correct Answer: Must be clearly defined and understood by everyone involved in the risk assessment process When performing a risk assessment Correct Answer: It is important to understand the organization's unique risk appetite and cultural considerations Can have a significant impact on risk management. Correct Answer: Cultural aspects like financial institutions or small entrepreneurial start-ups risk assessment Correct Answer: Is not a one-off process. No organization is static Correct Answer: Technology, business, regulatory and statutory requirements, people, vulnerabilities and threats are continuously evolving and changing. successful risk assessment Correct Answer: Is an ongoing process to identify new risk and changes to the characteristics [Show More]
Last updated: 1 year ago
Preview 1 out of 27 pages

Reviews( 0 )
Document information
Connected school, study & course
About the document
Uploaded On
Nov 01, 2022
Number of pages
27
Written in
Additional information
This document has been written for:
Uploaded
Nov 01, 2022
Downloads
0
Views
21