Computer Science > QUESTIONS & ANSWERS > Qualys Reporting Strategies and Best Practices Exam Questions and Answers with complete solution (All)
Qualys Reporting Strategies and Best Practices Exam Questions and Answers with complete solution
Document Content and Description Below
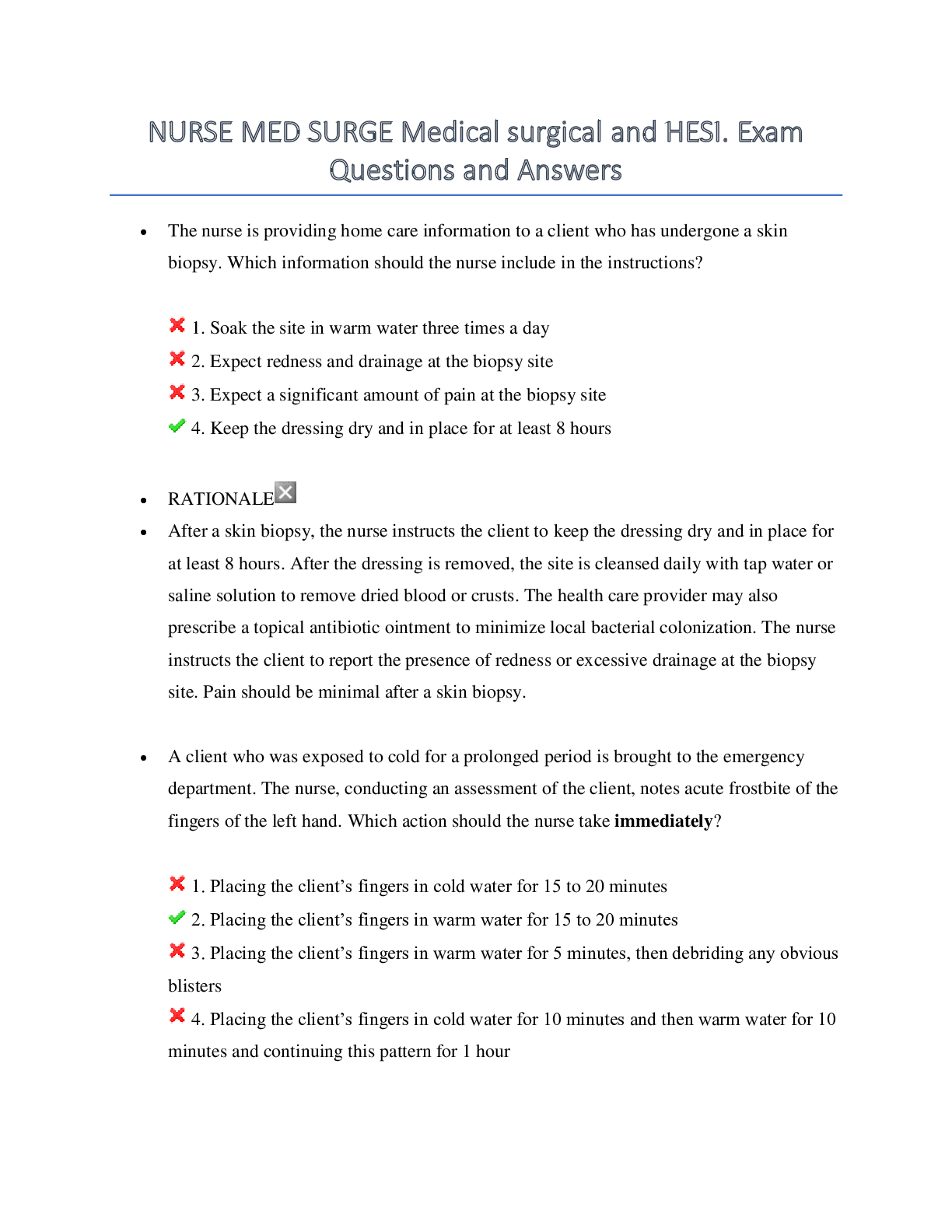
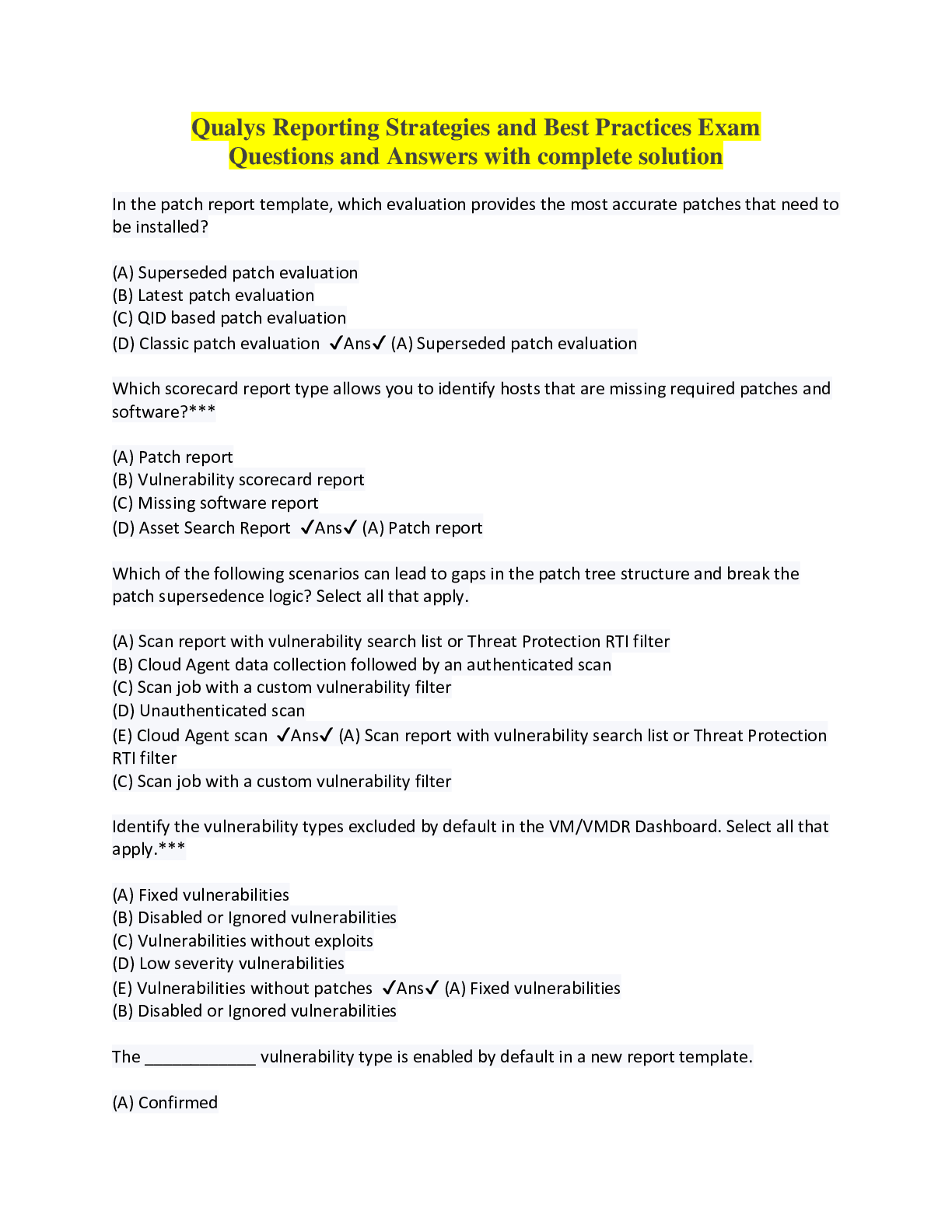
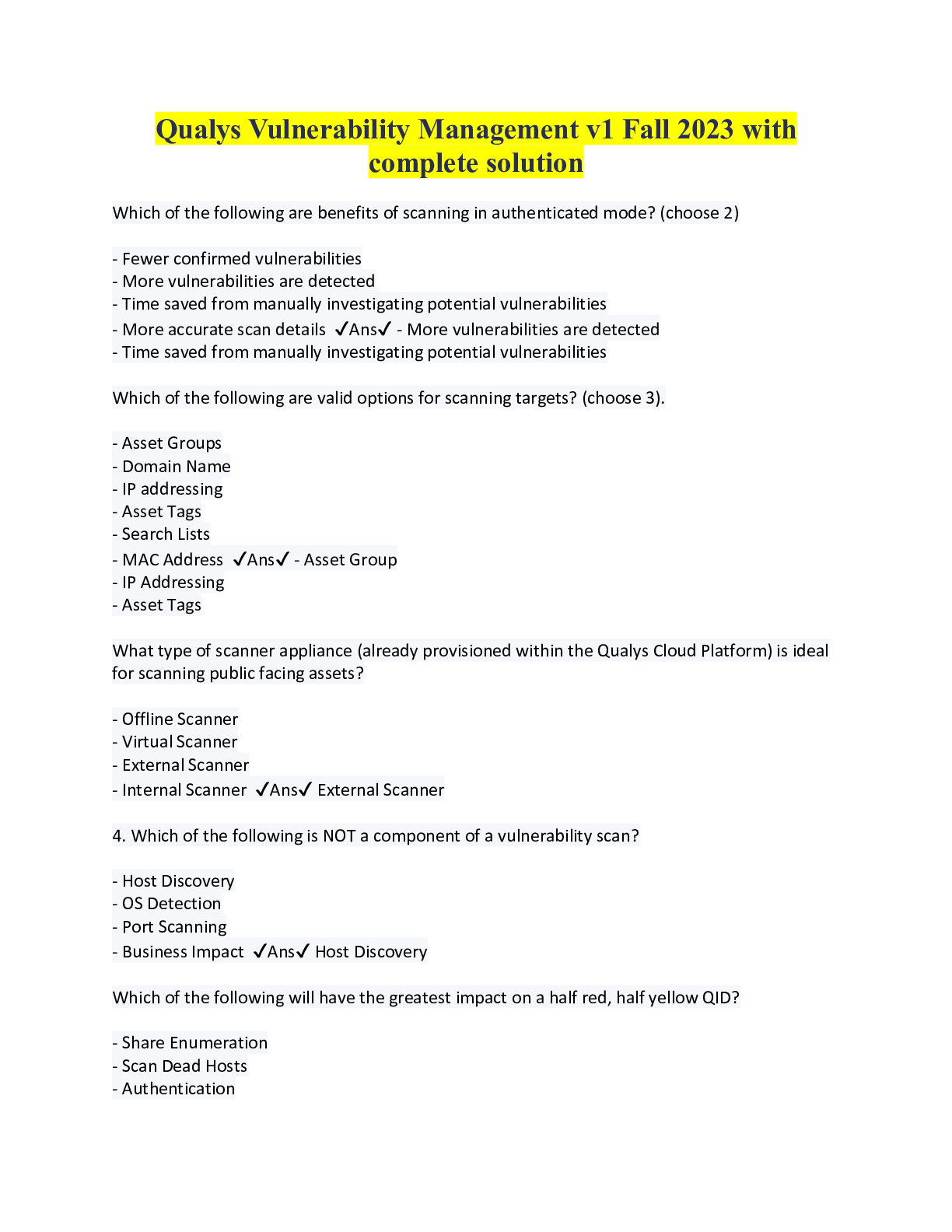
Qualys Reporting Strategies and Best Practices Exam Questions and Answers with complete solution In the patch report template, which evaluation provides the most accurate patches that need to be i... nstalled? (A) Superseded patch evaluation (B) Latest patch evaluation (C) QID based patch evaluation (D) Classic patch evaluation ✔Ans✔ (A) Superseded patch evaluation Which scorecard report type allows you to identify hosts that are missing required patches and software?*** (A) Patch report (B) Vulnerability scorecard report (C) Missing software report (D) Asset Search Report ✔Ans✔ (A) Patch report Which of the following scenarios can lead to gaps in the patch tree structure and break the patch supersedence logic? Select all that apply. (A) Scan report with vulnerability search list or Threat Protection RTI filter (B) Cloud Agent data collection followed by an authenticated scan (C) Scan job with a custom vulnerability filter (D) Unauthenticated scan (E) Cloud Agent scan ✔Ans✔ (A) Scan report with vulnerability search list or Threat Protection RTI filter (C) Scan job with a custom vulnerability filter Identify the vulnerability types excluded by default in the VM/VMDR Dashboard. Select all that apply.*** (A) Fixed vulnerabilities (B) Disabled or Ignored vulnerabilities (C) Vulnerabilities without exploits (D) Low severity vulnerabilities (E) Vulnerabilities without patches ✔Ans✔ (A) Fixed vulnerabilities (B) Disabled or Ignored vulnerabilities The ____________ vulnerability type is enabled by default in a new report template. (A) Confirmed (B) Potential (C) Patched (D) Information Gathered ✔Ans✔ (B) Potential Stale asset and vulnerability data can affect your security risk and business risk calculations. *** (A) False (B) True ✔Ans✔ (B) True Adding non-Qualys user's email in the distribution group helps you distribute the scheduled report to such users. *** (A) True (B) False ✔Ans✔ (A) True When using host-based findings, which of these needs to be turned on to toggle the inclusion of Fixed vulnerabilities in the report?*** (A) Trending (B) (C) (D) ✔Ans✔ (A) Trending Which finding type allows you to include trending data in your reports?*** (A) Scanner based findings (B) San-based finding (C) Cloud Agent-based findings (D) Host-based findings ✔Ans✔ (D) Host-based findings Threat Protection RTIs are used in the___________ in VMDR to identify the potential impact of discovered vulnerabilities, as well as vulnerabilities that have known or existing threats. *** (A) Prioritization report (B) Remediation report (C) Scorecard report (D) Patch report ✔Ans✔ (A) Prioritization report Identify the factor from the following that does not affect the report generation process.*** (A) Number of detections (B) Trending period (C) Number of assets (D) Number of graphics ✔Ans✔ (D) Number of graphics [Show More]
Last updated: 1 year ago
Preview 1 out of 9 pages
Buy this document to get the full access instantly
Instant Download Access after purchase
Add to cartInstant download
We Accept:
Reviews( 0 )
$9.00
Document information
Connected school, study & course
About the document
Uploaded On
Feb 18, 2023
Number of pages
9
Written in
Additional information
This document has been written for:
Uploaded
Feb 18, 2023
Downloads
0
Views
75


.png)