Computer Science > EXAM > CISSP Domain 5: Questions & Answers: A+ Score (All)
CISSP Domain 5: Questions & Answers: A+ Score
Document Content and Description Below
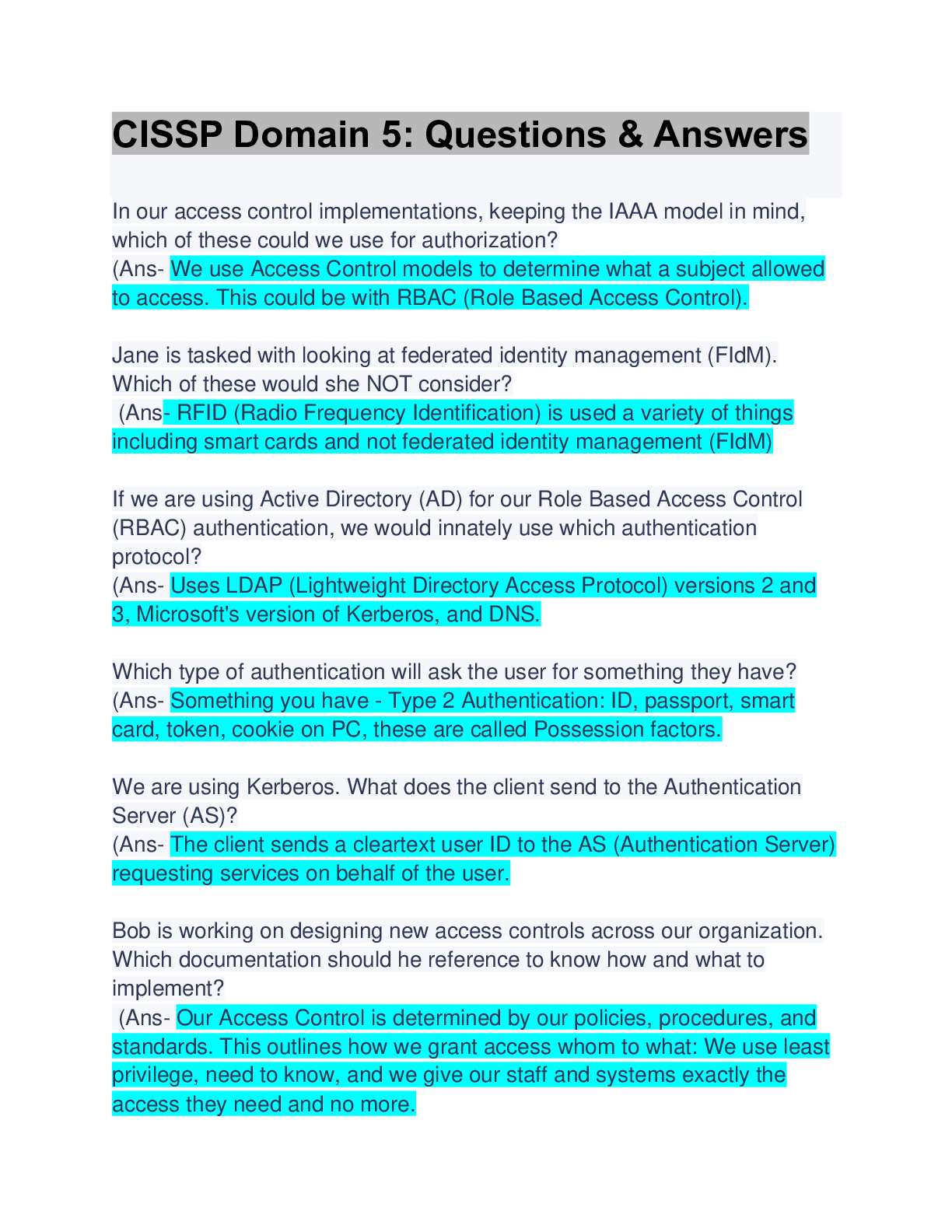
our access control implementations, keeping the IAAA model in mind, which of these could we use for authorization? (Ans- We use Access Control models to determine what a subject allowed to access. Thi... s could be with RBAC (Role Based Access Control). Jane is tasked with looking at federated identity management (FIdM). Which of these would she NOT consider? (Ans- RFID (Radio Frequency Identification) is used a variety of things including smart cards and not federated identity management (FIdM) If we are using Active Directory (AD) for our Role Based Access Control (RBAC) authentication, we would innately use which authentication protocol? (Ans- Uses LDAP (Lightweight Directory Access Protocol) versions 2 and 3, Microsoft's version of Kerberos, and DNS. Which type of authentication will ask the user for something they have? (Ans- Something you have - Type 2 Authentication: ID, passport, smart card, token, cookie on PC, these are called Possession factors. We are using Kerberos. What does the client send to the Authentication Server (AS)? (Ans- The client sends a cleartext user ID to the AS (Authentication Server) requesting services on behalf of the user. Bob is working on designing new access controls across our organization. Which documentation should he reference to know how [Show More]
Last updated: 6 months ago
Preview 1 out of 10 pages
Reviews( 0 )
Document information
Connected school, study & course
About the document
Uploaded On
Nov 05, 2023
Number of pages
10
Written in
Additional information
This document has been written for:
Uploaded
Nov 05, 2023
Downloads
0
Views
43