WGU C468 Knowledge Checks 2 Questions and Answers Latest 2022
Document Content and Description Below
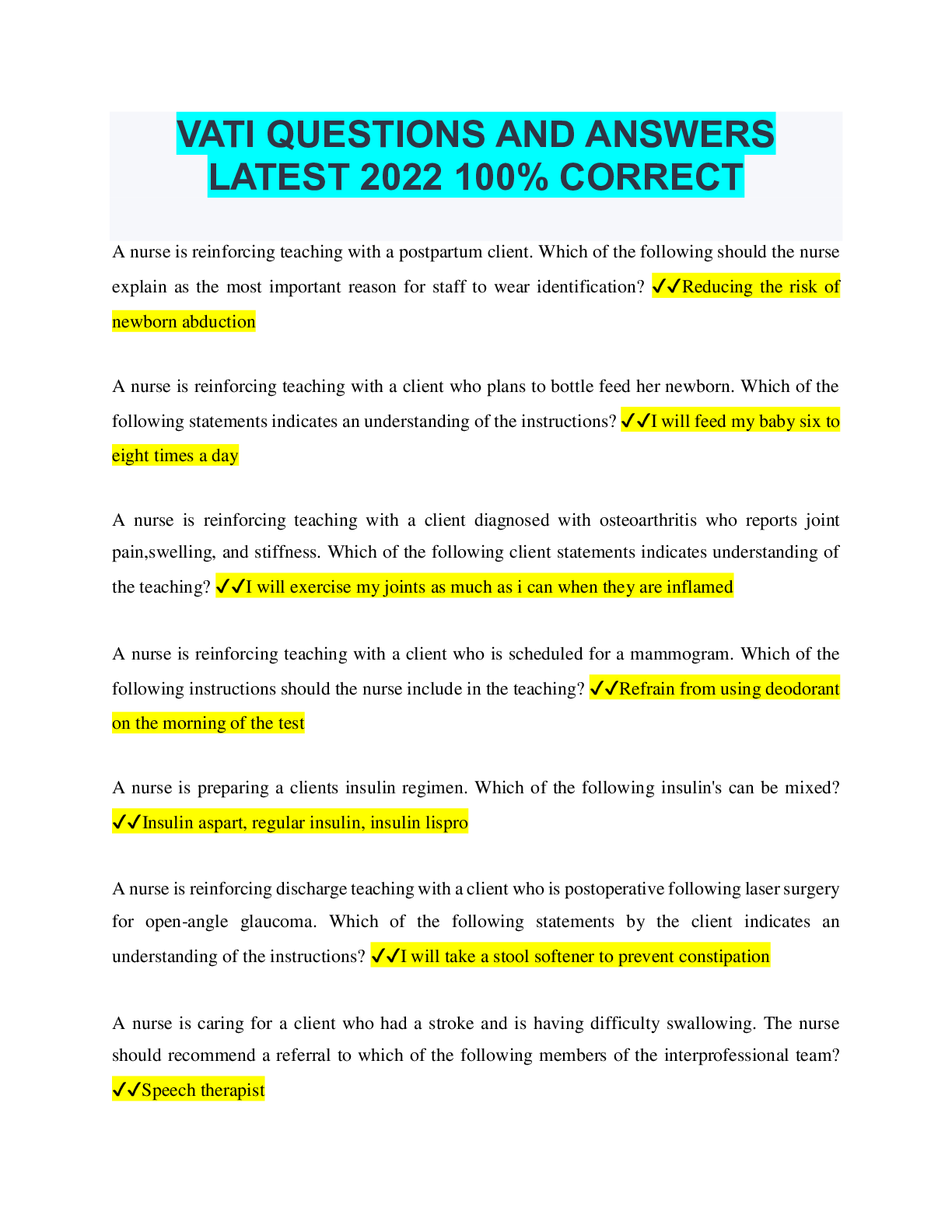
System security involves protection against ✔✔deliberate attacks, errors, omissions, disasters and viruses Which of the following is a mechanism that logs the user off a system after a specified... period of inactivity on the terminal or computer? ✔✔automatic sign off The sharing of private information in a situation in which a relationship has been established for the purpose of treatment with the understanding this information will remain protected is ✔✔Confidentiality ____ is a combo of hardware and software that forms a barrier between systems or different parts of a single system to protect those systems from unauthorized access ✔✔Firewall The ability to use a health enterprise's information system from outside locations such as a physician's office is known as ___________. ✔✔Remote access What are forces behind the Health Information Exchange ✔✔Federal legislation and demands for safer more efficient healthcare How do Health Information Exchanges (HIEs) impact healthcare delivery? ✔✔HIEs increase the efficiency and potentially the quality of the healthcare delivery system Information & Data privacy ✔✔includes the right to choose the condition and extent to w [Show More]
Last updated: 1 year ago
Preview 1 out of 5 pages
.png)
Also available in bundle (1)
.png)
Bundle for WGU C468 Tests Compilation | Updated & Verified | Everything you need!!
Bundle for WGU C468 Tests Compilation | Updated & Verified | Everything you need!!
By Annah 1 year ago
$35
33
Reviews( 0 )
Document information
Connected school, study & course
About the document
Uploaded On
Sep 07, 2022
Number of pages
5
Written in
Additional information
This document has been written for:
Uploaded
Sep 07, 2022
Downloads
0
Views
48

.png)
.png)


.png)
.png)
.png)
.png)
.png)

.png)