Business > EXAM > BCIS 3610 Basic Information Systems > BCIS 3610 EXAM 1 (all questions and answers,all correct) (All)
BCIS 3610 Basic Information Systems > BCIS 3610 EXAM 1 (all questions and answers,all correct)
Document Content and Description Below
BCIS 3610 EXAM 1 1) Collaboration occurs when a number of people . A) come together to perform tasks that are different B) work together to achieve a common goal C) perform independent tasks tha... t are important D) work without having to critically analyze each other's work Page Ref: 33 AACSB: Use of Information Technology; Communication Abilities Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 1 2) occurs when a group of people working together to achieve a common goal via a process of feedback and iteration. A) Systems thinking B) Collaboration C) Groupthink D) Experimentation Page Ref: 33 AACSB: Use of Information Technology; Communication Abilities Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 1 3) Which of the following is a key difference between collaboration and cooperation? A) Unlike cooperation, collaboration occurs when a job has to be accomplished. B) Cooperation requires people to have a common goal, whereas collaboration occurs even without a common goal. C) People should work together to cooperate, whereas they need not work together to collaborate. D) Unlike cooperation, collaboration gives importance to iteration and feedback. Page Ref: 33 AACSB: Communication Abilities Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 1 4) A student team, which is assigned a term project, meets and divides the work into sections and then team members work independently on their individual pieces. An hour before the project is due the team members meet again to assemble their independent pieces into a whole. Which of the following is lacking in this activity? A) collaboration B) cooperation C) systems thinking D) interdependence Page Ref: 33 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 1 5) Andrea, the floor supervisor at a call center, calls Bryan, a call attendant, to her office. She reports observing a few critical omissions in his calls, a finding supported by recent customer surveys. Bryan feels that Andrea is just throwing her weight around. Which of the following is a valid observation of this scenario? A) Andrea failed to express an unpopular viewpoint. B) Bryan needs to learn to receive feedback. C) The office lacks a communication system. D) Bryan is self-managing and requires low supervision. Page Ref: 33 AACSB: Analytic Skills; Communication Abilities Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 1 6) Being is one of the most important characteristics of an effective collaborator. A) a well organized and popular person B) able to give negative feedback C) experienced in collaborating D) a dynamic and persuasive presenter Page Ref: 34 AACSB: Communication Abilities Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 1 7) Which of the following is the most important trait that an effective collaborator should have? A) ability to identify and not raise unpopular viewpoints B) persuasive presentation skills C) willingness to enter into difficult conversations D) previous experience as a collaborator Page Ref: 34 AACSB: Communication Abilities Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 1 8) Identify the least important characteristic for an effective collaborator. A) willingness to enter difficult conversations B) being an experienced businessperson C) showing ability to receive negative feedback D) being skillful at giving negative feedback Page Ref: 34 AACSB: Communication Abilities Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 1 9) According to Hackman, which of the following is a primary criterion for judging team success? A) growth in team capability B) experience in collaborating C) ability to be dynamic D) availability of external help Page Ref: 36 Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 2 10) Which of the following is a primary purpose of collaboration? A) combining pieces of work B) becoming informed C) evaluating coworkers D) performing routine tasks Page Ref: 37 AACSB: Communication Abilities Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 11) decisions are decisions that support day-to-day activities. A) Operational B) Tactical C) Strategic D) Managerial Page Ref: 38 AACSB: Use of Information Technology; Communication Abilities Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 12) Kyra, a plant supervisor, orders 500 units of Type-2 steel beams for the coming month. In doing so, she has made a(n) decision. A) managerial B) tactical C) strategic D) operational Page Ref: 38 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 13) A decision is called an operational decision if it . A) is made by an individual rather than a group B) is made by managers C) involves allocation of resources D) concerns day-to-day activities Page Ref: 38 AACSB: Analytic Skills Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 14) Project leaders have to take decisions on the allocation and utilization of materials and labor. Such decisions are called decisions. A) operational B) top-level C) managerial D) strategic Page Ref: 38 AACSB: Analytic Skills Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 15) Departmental heads should determine the computer hardware and programs that are needed for their department. This is an example of a(n) decision. A) operational B) strategic C) procedural D) managerial Page Ref: 38 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 16) Managerial decisions in an organization concern . A) the utilization of resources B) broad organizational issues C) the day-to-day activities D) strategic decision making Page Ref: 38 AACSB: Use of Information Technology; Communication Abilities Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 17) decisions are those that support broad-scope, organizational issues. A) Operational B) Strategic C) Mid-level D) Managerial Answer: B Page Ref: 38 Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 18) The directors of a company meet to decide if they should start a new product line or not. This is an example of a(n) decision. A) operational B) strategic C) managerial D) procedural Page Ref: 38 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 19) Which of the following is an example of a strategic decision? A) deciding to increase the salaries of a group of employees B) deciding to open a centralized distribution system C) deciding to increase the reorder quantity of raw materials D) deciding to give an employee certain tasks and responsibilities Page Ref: 38 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 20) Which of the following is a key difference between strategic decisions and managerial decisions? A) Strategic decisions deal with the allocation and utilization of resources, whereas managerial decisions deal with day-to-day activities. B) Managerial decisions concern organizational issues, whereas strategic decisions concern external issues. C) Managerial decisions concern allocation and utilization of resources, whereas strategic decisions concern organizational issues. D) Strategic decisions involve financial issues, whereas managerial decisions do not involve financial issues. Page Ref: 38 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 21) Identify a key difference between managerial decisions and operational decisions. A) Managerial decisions concern the allocation of resources, whereas operational decisions concern day-to-day activities. B) Managerial decisions are corporate decisions, whereas operational decisions concern the utilization of resources. C) Managerial decisions deal with the allocation of resources, whereas operational decisions deal with the utilization of resources. D) Operational decisions have broad scope, whereas the scope of managerial decisions is limited to day-to-day activities. Page Ref: 38 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 22) Using a standardized procedure to calculate the incentives of employees is an example of a(n) decision. A) sequential B) structured C) unstructured D) parallel Page Ref: 39 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 23) An organization uses a formula to compute the reorder quantity of an item in inventory. This is an example of a(n) decision process. A) structured B) organizational C) corporate D) strategic Page Ref: 39 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 24) A company's top managers meet to decide on a potential merger with one of its competitors. They discuss various aspects of the merger, such as business valuations and conducting due diligence. This is an example of decision making. A) asynchronous B) unstructured C) programmed D) operational Page Ref: 39 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 25) Which of the following questions is best answered through unstructured decision making? A) How many overtime hours should be used to fill this order? B) Should we continue to outsource our bookkeeping processes? C) What is the acceptable defect ratio for this product? D) When should the next batch be scheduled to reduce idle time? Page Ref: 39 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 26) Which of the following decisions is least likely to involve collaboration? A) How much of product A should be ordered from vendor B? B) What products should we include in the new product line? C) Should our company acquire company A? D) What type of relationship should the company maintain with company A? Page Ref: 39 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 27) Which of the following observations about the relationship between decision type and decision process is true? A) Managerial decisions tend to be highly structured, whereas operational decisions are unstructured. B) The higher levels of decision making are associated with unstructured decision processes. C) Higher-level organizational decisions should be highly structured. D) Need for collaboration is highly significant for lower-level, structured decisions. Page Ref: 39 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 28) The need for collaboration is greatest for decisions. A) operational B) procedural C) strategic D) managerial Page Ref: 39 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 29) decisions are the most structured and have very little need for collaboration. A) Operational B) Tactical C) Managerial D) Strategic Page Ref: 39 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 30) The fundamental purpose of the starting phase of a project is . A) accomplishing the project tasks effectively B) outlining the tasks to be accomplished C) managing tasks and budgets D) setting the ground rules for the collaboration Page Ref: 40 AACSB: Communication Abilities Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 31) An organization defines the rules that govern a project that it needs to undertake and the people who should perform the tasks. The project is in the phase of project management. A) starting B) finalizing C) doing D) planning Page Ref: 40 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 32) The decision about team members' roles and authorities is made during the phase of a project. A) starting B) planning C) doing D) evaluating Page Ref: 40 AACSB: Communication Abilities Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 33) The main purpose of the planning phase in a project is to . A) set up the project scope and initial budget B) accomplish the project tasks effectively C) determine who will do what and by when D) decide if the task status reporting process is needed or not Page Ref: 41 AACSB: Communication Abilities Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 34) Which of the following tasks should be performed during the planning phase of project management? A) reporting project progress B) determining schedule C) performing project tasks D) preparing archival documents Page Ref: 41 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 35) A project manager defines the tasks that her team members have to perform and determines the schedule for carrying out each of the tasks. This project is in the phase of project management. A) planning B) starting C) doing D) finalizing Page Ref: 41 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 36) A project manager has to manage tasks and budgets and solve problems during the phase of project management. A) planning B) starting C) doing D) finalizing Page Ref: 41 AACSB: Analytic Skills Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 37) One of the procedures of a collaboration project is task status reporting. This is performed in the phase of the project. A) starting B) planning C) doing D) following Page Ref: 41 AACSB: Analytic Skills Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 38) Identify the project management phase in which the tasks of a project are performed. A) finalizing B) doing C) planning D) starting Page Ref: 41 AACSB: Analytic Skills Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 39) Project teams should document project results and learnings. Which of the following is the project management phase in which the teams perform this function? A) doing B) planning C) starting D) finalizing Page Ref: 41 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 3 40) Project data is data that is . A) part of the collaboration's work product B) used to manage a project C) used as a pointer to task data D) part of documents such as schedules and budgets Page Ref: 42 AACSB: Use of Information Technology Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 4 41) Project metadata is data that is . A) part of the collaboration's work product B) utilized to manage the project C) developed to design new offerings D) used in documents to describe recommended solutions Page Ref: 42 AACSB: Use of Information Technology Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 4 42) Which of the following is an example of project data? A) list of project tasks B) schedule C) budget D) design document Page Ref: 42 AACSB: Use of Information Technology Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 4 43) Which of the following collaboration activities is mainly concerned with content sharing rather than communication? A) promoting team growth B) feedback C) iteration D) increasing team satisfaction Page Ref: 42 AACSB: Analytic Skills Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 4 44) Which of the following information system requirements falls into the content sharing category? A) providing for team and member recognition B) tracking versions of many documents C) presenting intrateam learning D) offering easy-to-use multiparty communication Page Ref: 42 AACSB: Use of Information Technology Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 4 45) communication occurs within a team when all team members meet at the same time. A) Synchronous B) Sequential C) Virtual D) Unidirectional Page Ref: 43 AACSB: Communication Abilities Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 5 46) Asynchronous communication occurs when team members . A) cannot arrive at a common consensus after discussions B) engage in conflicting discussions C) do not meet at the same time D) communicate in a sequential manner Page Ref: 43 AACSB: Communication Abilities Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 5 47) The use of a conference call is an example of communication. A) sequential B) synchronous C) indirect D) unidirectional Page Ref: 44 AACSB: Communication Abilities Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 5 48) Who is most likely to use asynchronous communication? A) members of a team who work in different time zones B) managers who work in the same office C) employees who work in an assembly line D) a group of directors who periodically meet for board meetings Page Ref: 44 AACSB: Communication Abilities Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 5 49) Which of the following tools facilitates asynchronous communication? A) videoconferencing B) webinar C) discussion forum D) screen-sharing application Page Ref: 44 AACSB: Use of Information Technology; Communication Abilities Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 5 50) is a popular commercial webinar product used in virtual sales presentations. A) Microsoft SharePoint B) MS Office Web C) WebEx D) Google Drive Page Ref: 45 AACSB: Use of Information Technology Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 5 51) Which of the following is a reason why discussion forums are better than emails in asynchronous communication? A) They are best suited to transmit personalized information. B) They facilitate real-time communication between participants. C) They keep the discussion from getting off track. D) They ensure that all team members are involved in the discussion. Page Ref: 46 AACSB: Use of Information Technology; Communication Abilities Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 5 52) The term refers to a collaboration tool where team members can easily respond and the management can easily identify the people who have not responded to a request. A) discussion forums B) wikis C) webinars D) team surveys Page Ref: 46 AACSB: Use of Information Technology Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 5 53) Which of the following alternatives for sharing content provides version control? A) Windows Live SkyDrive B) Wikis C) Google Drive D) Microsoft SharePoint Page Ref: 47 AACSB: Use of Information Technology Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 6 54) Version-management systems . A) provide version control of documents B) track changes to shared documents C) allow checkout of documents before they are edited D) provide workflow control to manage the activities that are predefined by the group Page Ref: 50 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 6 55) Which of the following statements is true about working with Google Drive? A) Google accounts are not necessarily required to edit documents. B) Documents are stored on the user's computer. C) Users are not allowed to simultaneously see and edit documents. D) Google tracks document revisions, with brief summaries of changes made. Page Ref: 50 AACSB: Use of Information Technology Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 6 56) is a process that occurs when the collaboration tool limits, and sometimes even directs, user activity. A) Document monitoring B) Version control C) Document tracking D) Version management Page Ref: 50 AACSB: Use of Information Technology Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 6 57) With version-control systems, shared documents are placed into shared directories called . A) caches B) data cubes C) libraries D) data mines Page Ref: 53 AACSB: Use of Information Technology Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 6 58) Which of the following tools does not allow a document to be changed by other users while it is being worked on? A) Windows Live SkyDrive B) Wikis C) Microsoft SharePoint D) Google Drive Page Ref: 53 AACSB: Use of Information Technology Difficulty: Easy Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 6 59) Which of the following is a comprehensive tool for content sharing? A) Skype B) SharePoint C) Google Drive D) Microsoft Lync Page Ref: 57 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 7 60) Which of the following is a feature of Microsoft Lync? A) multi-party text chat B) content management and control C) concurrent editing D) discussion forums Page Ref: 57 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Explain how IS can enhance systems of collaboration and teamwork Chapter LO: 7 1) states that the number of transistors per square inch on an integrated chip doubles every 18 months. A) Nielsen's Law B) Faraday's Law C) Moore's Law D) Newton's Law Page Ref: 5 AACSB: Use of Information Technology Difficulty: Easy Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 1 2) According to Moore's Law, the . A) price of integrated chips will increase once in eighteen months B) size of computing devices and integrated chips doubles every year C) number of transistors per square inch on an integrated chip doubles every 18 months D) size of computing devices and integrated chips reduce by fifty percent every year Page Ref: 5 AACSB: Use of Information Technology Difficulty: Easy Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 1 3) Which of the following is a major implication of Moore's Law? A) Data processing activities have become complex and time consuming. B) Costs of computing and processing have increased. C) Physical size of integrated chips has increased. D) Costs of data communications and storage have become very low. Page Ref: 5 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 1 4) Which of the following ratios has fallen as a result of Moore's Law? A) price/performance B) output/price C) performance/input D) performance/output Page Ref: 6 AACSB: Use of Information Technology Difficulty: Easy Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 1 5) Which of the following types of skills is most likely be outsourced to the lowest bidder? A) ability to experiment B) accounting skills C) ability to collaborate D) abstract reasoning skills Page Ref: 7 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 1 6) Which of the following is a nonroutine cognitive skill? A) computer programming skill B) marketing knowledge C) tax accounting skill D) systems thinking ability Page Ref: 7 AACSB: Analytic Skills Difficulty: Easy Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 1 7) Kerin is a business student interning at Benson and Hodgson, a firm specializing in exports of sophisticated equipment to other countries. She finds that she is unable to create a representative chart depicting the relation between processes such as procurement, shipping, and billing. This indicates that she lacks skills. A) abstract reasoning B) collaborative C) experimental D) systems thinking Page Ref: 8 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 1 8) Abstract reasoning is the ability to . A) work with others when performing tasks B) make and manipulate models C) act quickly on a problem D) analyze and perform routine tasks Page Ref: 8 AACSB: Use of Information Technology Difficulty: Easy Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 1 9) refers to the ability to model components and show how the components' inputs and outputs relate to one another. A) Abstract reasoning B) Systems thinking C) Dynamic correlation D) Operational logic Page Ref: 8 AACSB: Use of Information Technology Difficulty: Easy Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 1 10) A manager will essentially require skills to clearly understand how the resources that his or her company uses are converted to desired outputs. A) collaboration B) experimentation C) interpersonal D) systems thinking Page Ref: 8 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 1 11) You constantly analyze your work in terms of the contribution that you make to the overall output of your organization. This shows your skill. A) collaboration B) experimentation C) systems thinking D) interpersonal Page Ref: 8 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 1 12) When presenting an idea to her colleagues, Marjorie failed to consider others' perspectives and got defensive when people asked her questions. This situation indicates that Majorie lacks skills. A) systems thinking B) collaboration C) abstract reasoning D) experimentation Page Ref: 8 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 1 13) is the activity of two or more people working together to achieve a common goal, result, or work product. A) Systems thinking B) Abstract reasoning C) Collaboration D) Experimentation Page Ref: 8 AACSB: Use of Information Technology Difficulty: Easy Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 1 14) Edwin leads a team of fifteen programmers. He constantly changes the procedures that he uses to monitor, evaluate, and control the way his subordinates function. This shows his ability to . A) involve in systems thinking B) experiment C) make abstractions D) relate outputs and inputs Page Ref: 9 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 1 15) refers to making a reasoned analysis of an opportunity, envisioning potential solutions, evaluating those possibilities, and developing the most promising ones, consistent with the resources one has. A) Systems thinking B) Abstraction C) Collaboration D) Experimentation Page Ref: 9 AACSB: Use of Information Technology Difficulty: Easy Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 1 16) Which of the following is an example of computer hardware? A) a computer monitor B) a browser C) a spreadsheet D) a user manual Page Ref: 10-11 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 2 17) The storage disk in your computer is an example of the systems. A) hardware B) software C) database D) procedure Page Ref: 10-11 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 2 18) An operating system like Windows or Linux is an example of the information system. A) software B) hardware C) data D) procedure Page Ref: 11 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 2 component of information component of an 19) Adobe Acrobat is an application that allows users to create and edit digital documents. Adobe Acrobat is an example of a . A) hardware B) procedure C) database D) software Page Ref: 11 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 2 20) A customer relationship management (CRM) system contains the names and phone numbers of customers. Such things stored in a CRM system are part of the component. A) software B) data C) procedure D) people Page Ref: 11 AACSB: Use of Information Technology; Analytic Skills Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 2 21) You follow certain steps to access the supplementary readings for a course when using your organization's library management system. These steps that you follow are examples of the component of an information system. A) procedure B) data C) software D) hardware Page Ref: 11 AACSB: Use of Information Technology; Analytic Skills Difficulty: Moderate Course LO: Describe the components of an information system (IS) Chapter LO: 2 22) The words that you type in an MS Word document is an example of . A) procedures B) data C) processes D) software Page Ref: 11 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 2 23) The five-component framework considers individuals who maintain the data and who support the networks of computers as components. A) procedural B) people C) data D) networking Page Ref: 11 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Describe the components of an information system (IS) Chapter LO: 2 24) Business users who administer the development of information systems should . A) have the skills to be a programmer or a database designer B) take an active role in that system's development C) refrain from involving themselves in software development D) have a good understanding of programming concepts Page Ref: 11 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss the role of information systems in supporting business processes Chapter LO: 2 25) According to the five-component model of information systems, the component functions as instructions for the people who use information systems. A) software B) data C) hardware D) procedure Page Ref: 12 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 3 26) The process of automation is a process of moving work from . A) processes to procedures B) actors to instructions C) instructions to actors D) human side to computer side Page Ref: 12-13 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different methods for developing information systems Chapter LO: 3 27) Which of the following components in the five-component model of information systems is considered an actor? A) software B) hardware C) data D) procedure Page Ref: 13 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 3 28) The hardware components of an information system will act as a(n) . A) bridge between computer side and human side B) actor on the human side C) instruction on the computer side D) actor on the computer side Page Ref: 13 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 3 29) Your company uses a software tool to manage its supply chain. This software tool is an of your company's information system. A) instruction on the computer side B) actor on the human side C) instruction on the human side D) actor on the computer side Page Ref: 13 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 3 30) The component in the five-component model of information systems is considered a bridge that connects the computer side and the human side. A) software B) procedure C) data D) hardware Page Ref: 13 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 3 31) Which of the following components constitute the computer side of information systems? A) software and data B) data and hardware C) people and procedures D) hardware and software Page Ref: 13 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 3 32) Which of the following components constitute the human side of information systems? A) software and procedures B) data and people C) people and procedures D) hardware and people Page Ref: 13 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 3 33) Which of the following is a low-tech information system? A) an inventory tracking system that produces reports every 24 hours B) a file of email addresses stored in an email program C) a customer support system that keeps track of product issues D) a decision support system that analyzes multiple variables Page Ref: 13 AACSB: Use of Information Technology; Analytic Skills Difficulty: Moderate Course LO: Compare and contrast different methods for developing information systems Chapter LO: 3 34) Which of the following components of an information system is the easiest to change and causes the least amount of organizational disruption when changed? A) hardware B) software C) developer D) procedure Page Ref: 15 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 3 35) Drother Sports Inc. is a sports equipment provider that markets its products through a chain of retail outlets in three states. As part of its expansion strategy, the company decides to open outlets in six more states and decides to revise its existing business processes. According to the five-component model of information systems, which of the following processes will be the least disruptive to the organization? A) collecting demographic data from the new markets B) developing new CRM software for the existing and new outlets C) moving existing employees and hiring new employees D) buying and installing new computers in the new outlets Page Ref: 15 AACSB: Use of Information Technology; Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 3 36) Which of the following would be the most disruptive to an organization when implementing an information system? A) installing new hardware components B) creating new databases C) developing new programs D) changing reporting relationships Page Ref: 15 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 3 37) It is generally more difficult to make changes to the of an information system than to the database itself. A) software B) hardware C) programs D) procedures Page Ref: 15 AACSB: Use of Information Technology Difficulty: Easy Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 3 38) Glazer & Hicks is a firm that offers enterprise software solutions to independent retailers. The firm recently bagged a contract from a major national retail chain to develop and implement proprietary software that tracks inventory, restocking, and supplier information. Which of the following actions will be most difficult to perform when implementing the new information system? A) upgrading the computer systems used by the retail chain B) writing the programs for creating the software C) changing the structure of existing databases that reflect supplier and customer data D) training the employees to use and manage the new system Page Ref: 15 AACSB: Use of Information Technology; Analytic Skills Difficulty: Hard Course LO: Discuss the key issues involved in managing the components of IT infrastructure Chapter LO: 3 39) Identify how information technology differs from information systems. A) You can buy information technology, but not information systems. B) People are an important component of information technology, but not of information systems. C) Information systems form a subset of information technology. D) Unlike information systems, information technology is used for producing information. Page Ref: 15 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss the role of information systems in supporting business processes Chapter LO: 4 40) Which of the following is a component of an information system, but not of information technology? A) hardware B) data C) people D) software Page Ref: 15 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 4 41) Which of the following statements regarding information technology (IT) is true? A) Information technology (IT) refers to the products, methods, inventions, and standards that are used for the purpose of producing information. B) Information technology is an umbrella term that covers information systems and the products, methods, inventions, and standards used to produce information. C) Information technology and information systems are synonymous with each other and can be used interchangeably. D) Information technology is an assembly of hardware, software, data, procedures, and people that produces information. Page Ref: 15 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 4 42) Which of the following is considered information rather than mere data? A) a list of property prices in a neighborhood B) the return on investment of an advertising campaign C) the total number of students in a school D) the price of a company's shares on a given day Page Ref: 16 AACSB: Analytic Skills Difficulty: Moderate Course LO: Describe the components of an information system (IS) Chapter LO: 5 43) Which of the following is a common description of information? A) collection of unprocessed data B) unbiased, non-contextual data C) knowledge derived from data D) list of recorded facts or figures Page Ref: 16 AACSB: Analytic Skills Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 5 44) Which of the following is the best description of data? A) information presented in a meaningful context B) unbiased information C) recorded facts or figures D) knowledge derived from facts or figures Page Ref: 16 AACSB: Analytic Skills Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 5 45) You have a spreadsheet that provides the airfares to different cities from New York. If this is used to make a decision, it will be considered as . A) knowledge B) data C) information D) interpretation Answer: B Page Ref: 16 AACSB: Analytic Skills Difficulty: Moderate Course LO: Describe the components of an information system (IS) Chapter LO: 5 46) Which of the following is a critical characteristic of good information? A) abundance of details B) accuracy C) low cost D) ease of creation Page Ref: 17 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss the role of information systems in supporting business processes Chapter LO: 6 47) You are the production manager at a cola manufacturer's bottling plant. You receive a report that contains the list of raw materials stored in the warehouse. You find that the list includes items that are not present in the warehouse. The list that you received would qualify as bad information because it is . A) inaccurate B) late C) voluminous D) too narrow in scope Page Ref: 17 AACSB: Analytic Skills Difficulty: Moderate Course LO: Discuss the role of information systems in supporting business processes Chapter LO: 6 48) Which of the following statements is true of good information? A) Good information should go well beyond the scope of the purpose for which it is generated. B) Information should be relevant to the subject and not to the context. C) Good information should be based on correct and complete data. D) Good information is recovered from sources of information that provide information for free. Page Ref: 17 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Discuss the role of information systems in supporting business processes Chapter LO: 6 49) The CEO of an organization asks the human resources manager to send information about the rate of employee turnover in the organization for the last quarter. The manager sends the salary details of new hires during this period. This information is likely to be of little use to the CEO because it is . A) inaccurate B) not timely C) irrelevant D) too expensive Page Ref: 20 AACSB: Analytic Skills Difficulty: Moderate Course LO: Discuss the role of information systems in supporting business processes Chapter LO: 6 50) The CEO of a large company asks the sales manager to report the sales figures of the previous quarter. The manager immediately sends her the details of each invoice drawn up in the previous quarter. This information is not good because it is . A) too narrow in scope B) inaccurate C) not timely D) more than what is required Page Ref: 20 AACSB: Analytic Skills Difficulty: Moderate Course LO: Discuss the role of information systems in supporting business processes Chapter LO: 6 51) Good information must be . A) inexpensive B) relevant C) widely available D) voluminous Page Ref: 20 AACSB: Analytic Skills Difficulty: Easy Course LO: Discuss the role of information systems in supporting business processes Chapter LO: 6 52) You are looking to buy a home that costs less than $700,000, but your real estate agent keeps sending you fliers for homes that cost $1,000,000 or more. This information is likely to be useless because it is . A) inaccurate B) late C) irrelevant D) not reliable Page Ref: 20 AACSB: Analytic Skills Difficulty: Moderate Course LO: Discuss the role of information systems in supporting business processes Chapter LO: 6 53) Information is considered to be inefficient if . A) its level of accuracy is too high B) it is availed ahead of time C) it is just barely sufficient D) it is irrelevant to the subject Page Ref: 20 AACSB: Analytic Skills Difficulty: Easy Course LO: Discuss the role of information systems in supporting business processes Chapter LO: 6 54) Which of the following is the least critical aspect of good information? A) data accuracy B) timeliness of data C) additional data D) relevance of data Page Ref: 20 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss the role of information systems in supporting business processes Chapter LO: 6 55) You ask your secretary to send information on the meetings that you need to attend in the month. He provides you the details immediately, but he leaves out certain additional details that he deems to be surplus to your requirements. Judge your secretary's action. A) The information that your secretary provided was partly good as it was timely, but insufficient. B) The secretary provided adequate and timely information, but the information did not add value to you. C) The information that your secretary gave will be considered as good information. D) The information that you obtained through the secretary was not timely and worth its cost. Page Ref: 20 AACSB: Analytic Skills Difficulty: Hard Course LO: Discuss the role of information systems in supporting business processes Chapter LO: 6 56) Which of the following is true about the quality of information? A) Information should be just barely sufficient for its purpose. B) There is no such thing as bad information. C) Information needs to be relevant to the subject, not to the context. D) The more information you receive, the less you can afford to ignore. Page Ref: 20 AACSB: Analytic Skills Difficulty: Easy Course LO: Discuss the role of information systems in supporting business processes Chapter LO: 6 57) Which among the following is the most appropriate technique for creating memorable, strong passwords? A) base your password on the first letters of the words in a phrase B) use your favorite foreign words C) use dictionary words or phrases as passwords D) use a collection of randomly picked letters, numbers, and special characters Page Ref: 24 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Describe different methods of managing IS security Chapter LO: 7 58) Vera wants to create a password. Which of the following is the strongest password that she can use? A) Vera@123 B) Vera@Vera C) NewYork56$ D) NOOCSmyPw$42 Page Ref: 24 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Describe different methods of managing IS security Chapter LO: 7 59) Which of the following is a valid guideline for maintaining good password etiquette? A) Write down your password in an accessible location. B) Never ask someone else for their password. C) Give your password to your coworkers if you anticipate that they may need it in your absence. D) Share your password with the IT staff in your organization. Page Ref: 24 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss the ethical and social issues raised by the use of information systems Chapter LO: 7 60) As the IT manager of your organization, you need to use a coworker's account to access some information. In keeping with password etiquette, how would you go about getting his password? A) You ask the coworker to type in the password where required, while you look away. B) You explain the urgency of the situation and ask the coworker to send you the password through email. C) You submit a formal letter to your coworker's manager, explaining the situation and requesting that the password be sent to you. D) You try out various combinations to see if you can guess your coworker's password. Page Ref: 25 AACSB: Use of Information Technology; Analytic Skills Difficulty: Moderate Course LO: Discuss the ethical and social issues raised by the use of information systems Chapter LO: 7 1) Which of the following factors determines the structure, features, and functions of an information system used in a company? A) the competitive strategy B) the value of its brands C) the size of the company D) the technology used by competitors Page Ref: 73 AACSB: Communication Abilities Difficulty: Easy Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 1 2) Porter's five forces model is used to assess . A) industry structure B) market share C) internal competition D) lifecycles of products Page Ref: 74 AACSB: Communication Abilities Difficulty: Easy Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 2 3) According to Porter's five forces model, which of the following firms would be least affected by the threat of substitutes? A) a used car dealership in New York B) a convenience store that sells retail products C) a firm that sells the only drug for a disease D) corner latte shops in Atlanta Page Ref: 74 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 2 4) According to Porter's five forces model, which of the following would be most affected by the threat of substitutes? A) Microsoft Windows OS B) Boeing jets C) Southwest Airlines D) Google Adwords Page Ref: 74 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 2 5) According to Porter's five forces model, in which of the following situations would the suppliers have the highest bargaining power? A) a single vendor providing raw materials to many department stores B) a fashion outlet catering to a niche market C) a bank liquidating during a fire sale D) a large retailer buying goods from many small suppliers Page Ref: 74 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 2 6) According to Porter's five forces model, in which of the following examples would rivalry be considered as a weak force affecting the market? A) military services B) used car dealers C) book sellers D) packaged food manufacturers Page Ref: 74 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 2 7) A new drug that has shown promise in curing lung cancer has been discovered by a famous chemical laboratory. This is the only drug effective for treatment of this disease. The laboratory obtains a patent for the product and decides to sell it. This situation is characterized by . A) low threat of substitutions B) high bargaining power of customers C) high threat of new entrants D) low bargaining power of suppliers Page Ref: 74 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 2 8) A group of grain farmers in a surplus year will have reduced . A) bargaining power B) threat of substitutes C) risk of rivalry D) threat of new entrants Page Ref: 74 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 2 9) Bargaining power of customers is likely to be the highest for markets involving . A) public transportation B) industrial products C) patented drugs D) luxury goods Page Ref: 74 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 2 10) The automobile industry is characterized by many manufacturers and intense competition among them. This statement illustrates . A) low threat of substitutions B) high bargaining power of suppliers C) high levels of rivalry D) low bargaining power of customers Page Ref: 74 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 2 11) ABC Motors is the largest manufacturer of cars. The company purchases raw materials from many small-sized sellers across the globe. In this case, ABC Motors is characterized by . A) very low threat of substitute products B) high bargaining power over its suppliers C) very low threat of new entrants to market D) very high bargaining power over its customers Page Ref: 74 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 2 12) N-joi Ice Cream recently faced competition against their flagship brand of "black currant ice cream." The competitor made significant in-roads into this market by offering three varieties of "black currant ice cream." N-joi decided to counter this threat by introducing five new varieties of ice creams. Which competitive strategy is N-joi implementing? A) cost leadership B) product differentiation C) cost differentiation in the segment D) service focus Page Ref: 75 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 3 13) An automobile company decides to improve the quality of all its products and bring more variety into its product line. The company has decided to adopt . A) focused cost-leadership B) industry-wide differentiation C) industry-wide cost leadership D) focused differentiation Page Ref: 75 AACSB: Analytic Skills Difficulty: Hard Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 3 14) Focused differentiation occurs when . A) a better product is provided within an industry segment B) there is limited competition in an industry C) the customers are highly price sensitive D) product quality improves across an entire industry Page Ref: 75 AACSB: Communication Abilities Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 3 15) Focused cost leadership is observed when a product has the lowest cost . A) within an industry segment B) across the product range offered by a company C) within an industry D) within the supply chain of a company Page Ref: 75 AACSB: Communication Abilities Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 3 16) The difference between the value that an activity generates and the cost of the activity is called the . A) margin B) turnover C) revenue D) value-addition Page Ref: 78 AACSB: Communication Abilities Difficulty: Easy Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 4 17) Porter defined value as the . A) amount of money that a customer is willing to pay for an offering B) extent of after-sale service provided to customers C) perceived satisfaction of the customers and sellers after a transaction D) actual money exchanged in return of a product/service Page Ref: 78 AACSB: Communication Abilities Difficulty: Easy Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 4 18) Identify the activity in the value chain that involves receiving and handling of raw materials and other inputs to the product. A) inbound logistics B) procurement C) operations D) outbound logistics Page Ref: 78 AACSB: Communication Abilities Difficulty: Easy Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 4 19) The difference between the total value added and the total costs incurred is called the of the value chain. A) actual value B) total margin C) gross revenue D) gross turnover Page Ref: 78 AACSB: Communication Abilities Difficulty: Easy Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 4 20) A retail marketing company sells such products as agricultural produce and consumer products. The company procures materials from farmers and local producers. This process of obtaining the inputs needed for a business is called . A) outbound logistics B) inbound logistics C) operations D) internal marketing Page Ref: 79 AACSB: Analytic Skills Difficulty: Easy Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 4 21) Which of the following value chain activities involves transforming raw materials into a finished product or service? A) operations B) inbound logistics C) marketing D) maintenance Page Ref: 79 AACSB: Communication Abilities Difficulty: Easy Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 4 22) Which of the following value chain activities involves collecting, storing, and physically distributing the product to buyers? A) inbound logistics B) operations C) customer service D) outbound logistics Page Ref: 79 AACSB: Communication Abilities Difficulty: Easy Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 4 23) Which of the following value chain activities involves inducing buyers to purchase a product and providing a means for them to do so? A) inbound logistics B) operations C) sales and marketing D) outbound logistics Page Ref: 79 AACSB: Communication Abilities Difficulty: Easy Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 4 24) Which of the following value chain activities involves assisting users with handling of the products after sale, thus maintaining and enhancing the products' value? A) inbound logistics B) customer service C) operations D) outbound logistics Page Ref: 79 AACSB: Communication Abilities Difficulty: Easy Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 4 25) Which of the following is a primary activity in the value chain? A) receiving and disseminating inputs to the product B) negotiating prices with vendors C) finding suitable vendors to supply raw materials D) setting up contractual arrangements with various suppliers Page Ref: 79 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 4 26) Mae manages delivery at a custom-kitchen outlet. Based on her customer's feedback, she contacts Gem Cabinets and places an order for a full-motion wall mount. Which of the following primary activities is Mae performing here? A) inbound logistics B) operations C) customer service D) marketing Page Ref: 79 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 4 27) Lynn, the manager of a transportation company, is going through this week's delivery schedule. She calls her team and assigns territories for each executive. She contacts the fleet supervisor to arrange trucks for transportation. Which activity of the value chain is Lynn executing? A) inbound logistics B) marketing C) customer service D) outbound logistics Page Ref: 79 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 4 28) Which of the following is a support activity in the value chain? A) receiving inputs to operationalize the production B) distributing the products to retailers or buyers directly C) assisting customers in using the product or service D) setting up contractual arrangements for procurement Page Ref: 79 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 4 29) Which of the following is considered a support activity in the value chain of a business? A) operations B) customer service C) contract negotiation D) marketing Page Ref: 79 AACSB: Communication Abilities Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 4 30) According to Porter's model of business activities, interactions across value activities are called . A) support activities B) models C) linkages D) cross-functionalities Page Ref: 80 AACSB: Communication Abilities Difficulty: Easy Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 4 31) Which of the following statements is consistent with the central idea of business process design? A) Technology should be used to supplement the existing value chain. B) Business processes should not focus on the core competencies of organizations. C) Organizations should create new business processes rather than improve existing systems. D) Technology should be used to modify and improve standard business processes. Page Ref: 80 AACSB: Communication Abilities Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 4 32) argues that firms should create new, more efficient business processes that integrate the activities of all departments involved in a value chain. A) Internal supply chain design B) Product differentiation model C) Market differentiation model D) Business process design Page Ref: 80 AACSB: Communication Abilities Difficulty: Easy Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 4 33) A(n) is a network of activities that generate value by transforming inputs into outputs. A) business process B) competitive strategy C) linkage D) information system Page Ref: 80 AACSB: Communication Abilities Difficulty: Easy Course LO: Discuss the role of information systems in supporting business processes Chapter LO: 5 34) The cost of the business process is the sum of the cost of the inputs and the . A) cost of the activities B) cost of the outputs C) value of the outputs D) value of the products Page Ref: 80 AACSB: Communication Abilities Difficulty: Easy Course LO: Discuss the role of information systems in supporting business processes Chapter LO: 5 35) A is a collection of something, such as data and raw materials. A) value chain B) cache C) linkage D) repository Page Ref: 80 AACSB: Communication Abilities Difficulty: Easy Course LO: Discuss the role of information systems in supporting business processes Chapter LO: 5 36) A database is an example of a . A) repository B) procedure C) linkage D) value chain Page Ref: 80 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss the role of information systems in supporting business processes Chapter LO: 5 37) In a manufacturing business, the transforms finished goods into cash. A) inbound operation B) manufacturing process C) sales process D) inbound logistic Page Ref: 80 AACSB: Communication Abilities Difficulty: Easy Course LO: Discuss the role of information systems in supporting business processes Chapter LO: 5 38) Material ordering is a part of . A) outbound logistics B) marketing C) operations D) inbound logistics Page Ref: 81 AACSB: Analytic Skills Difficulty: Moderate Course LO: Discuss the role of information systems in supporting business processes Chapter LO: 5 39) Which of the following statements is true of business process designs? A) Most process designs require people to work in new ways. B) Business process designs do not involve following different procedures. C) Business process designs should be accompanied by a change in management. D) Process designs attract very little employee resistance. Page Ref: 81 AACSB: Communication Abilities Difficulty: Easy Course LO: Discuss the role of information systems in supporting business processes Chapter LO: 5 40) RAC Associates is a car rental company. The company rents cars to customers in the United States. The company uses controls and procedures to prevent car theft. Such procedures are examples of . A) primary business processes B) core activities C) strategic activities D) supporting business processes Page Ref: 84 AACSB: Analytic Skills Difficulty: Moderate Course LO: Discuss the role of information systems in supporting business processes Chapter LO: 6 41) RedDart is a premium freight provider in the United States. The company offers premium shipment services to its customers. The company ships faster than its competitors and uses tamperproof containers to ship its products. RedDart distinguishes itself from competitors by . A) providing an enhanced service B) locking in its suppliers C) locking in its customers D) offering low-cost operations and services Page Ref: 85 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 7 42) Which of the following principles of competitive advantage is associated with product implementations? A) locking in customers B) differentiating service offerings C) locking in suppliers D) establishing alliances Page Ref: 85 AACSB: Communication Abilities Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 7 43) Which of the following principles of competitive advantage is related to process implementations? A) creating new products B) enhancing services C) locking in suppliers D) differentiating products Page Ref: 85 AACSB: Communication Abilities Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 7 44) Huen Software, an application provider to the gaming industry, decided to increase its portfolio by developing 3-D graphics-enabled games for the mobile gaming industry. By doing this, which competitive strategy is Huen Software implementing? A) creation of entry barriers B) product differentiation C) reduction of cost D) locking in suppliers Page Ref: 85 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 7 45) PowerCruise, a holiday cruise firm, recently offered its existing customers, who had registered for a two-year membership, an extension of six months to their membership without any additional charges. By doing this, which competitive strategy did PowerCruise implement? A) creation of a new service B) product differentiation C) locking in customers D) locking in suppliers Page Ref: 85 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 7 46) An organization wants to achieve competitive advantage through process implementations. Which of the following actions would help them do that? A) establishing alliances B) creating new products C) enhancing products D) differentiating services Page Ref: 85 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 7 47) Synapz, a manufacturer of office automation products, recently received a patent for an advanced therapeutic ergonomics technology. By doing this, Synapz has . A) created an entry barrier B) introduced product differentiation C) locked in its suppliers D) reduced the cost of operations Page Ref: 85 AACSB: Analytic Skills Difficulty: Hard Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 7 48) Locking in customers by making it difficult or expensive for customers to move to another product is called establishing high . A) entry barriers B) switching costs C) product standards D) value differentiation Page Ref: 85 AACSB: Communication Abilities Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 7 49) July Networks provides digital television services across the country. They have a cutting- edge technology that provides high-resolution visuals. Customers are required to pay an up-front fee to cover the first two years of the subscription, when registering with July Networks. By doing this, which competitive strategy is July Networks implementing? A) differentiating the product B) enhancing the product C) locking in customers D) standardizing the product Page Ref: 85 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 7 50) A large software manufacturer attempts to lock in customers by making it difficult for customers to change to another product. The strategy used is . A) switching costs strategy B) low cost operation strategy C) differentiation strategy D) consumerist strategy Page Ref: 85 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 7 51) Organizations can lock in suppliers by making it difficult to switch to another organization or by . A) making it easy for the customers to switch products B) reducing investments in their supply chain C) making it easy to work with the organization D) reducing the bargaining power of consumers Page Ref: 85 AACSB: Communication Abilities Difficulty: Easy Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 7 52) A group of manufacturing organizations purchases raw materials collectively to obtain better deals. This is an example of obtaining competitive advantage by . A) differentiating the industry B) establishing standards C) establishing alliances D) enhancing the products Page Ref: 85 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 7 53) An organization implements an information system to optimize its supply chain. The system helps the organization reduce wastages and inventory charges. Hence, the system provides a competitive advantage to the organization. Here, the information system helped the organization achieve competitive advantage by . A) locking in customers B) reducing costs C) locking in suppliers D) differentiating the products Page Ref: 85 AACSB: Analytic Skills Difficulty: Moderate Course LO: Explain how IS can be used to gain and sustain competitive advantage Chapter LO: 7 54) Reduction in production cost results in . A) decreased profitability B) lower shareholder value C) increased profitability D) increased competition Page Ref: 85 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 7 1) Which of the following devices is used during the processing stage of computing? A) UPC reader B) main memory C) printer D) bar code scanner Page Ref: 104 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 1 2) Which of the following is an input hardware device? A) plotter B) bar code scanner C) projector D) printer Page Ref: 104 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 1 3) Which of the following is an output device? A) video camera B) projector C) mouse D) bar code scanner Page Ref: 104 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 1 4) The is called the "brain" of the computer. A) random access memory B) read only memory C) storage hardware D) central processing unit Page Ref: 104 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 1 5) Which of the following devices is an example of an output hardware device? A) overhead projector B) keyboard C) mouse D) bar code scanner Page Ref: 104 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 1 6) Main memory is also known as . A) cache memory B) random access memory C) read-only memory D) optical memory Page Ref: 104 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 1 7) Which of the following devices is an example of a storage hardware device? A) universal serial bus B) central processing unit C) optical disk D) random access memory Page Ref: 104 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 1 8) Which of the following terms refers to a collection of servers? A) server database B) server farm C) portal D) data server Page Ref: 104 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 1 9) Bits are used for computer data because they . A) do not support multiple voltage levels B) are easy to represent electronically C) are used in common calculations D) do not function as switches in networks Page Ref: 105 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Describe the components of an information system (IS) Chapter LO: 1 10) Bits are grouped into 8-bit chunks called . A) switches B) strings C) bytes D) nibbles Page Ref: 106 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 1 11) A is equivalent to 1,024 bytes. A) gigabyte B) kilobyte C) terabyte D) megabyte Page Ref: 106 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 1 12) 10 TB is equivalent to gigabytes. A) 10,240 B) 1,000 C) 1,024 D) 102.4 Page Ref: 106 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 1 13) To run a program or process data, the computer first transfers the program or data from disk to the . A) cache memory B) main memory C) input device D) central processing unit Page Ref: 106 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Describe the components of an information system (IS) Chapter LO: 1 14) When using volatile memory, the . A) processor heats up during operation B) files are stored permanently C) processing becomes very slow D) contents are lost when power is off Page Ref: 106 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 1 15) Which of the following is a nonvolatile memory device? A) optical memory device B) main memory C) cache memory D) random access memory Page Ref: 106 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Describe the components of an information system (IS) Chapter LO: 1 16) Which of the following memory devices is volatile in nature? A) magnetic disk B) cache C) hard drive D) optical disk Page Ref: 106 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Describe the components of an information system (IS) Chapter LO: 1 17) Server application programs are programs that . A) control the client computer's resources B) are processed on client computers C) are processed on server computers D) control the server computer's resources Page Ref: 107 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 2 18) Which of the following is an example of an application program? A) Microsoft Word B) Unix C) Linux D) Windows Page Ref: 107 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 2 19) Which of the following is a function of an application program? A) allocating main memory to programs B) performing memory swapping C) accessing a customer database D) allocating resources to a computer Page Ref: 107 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 2 20) are commands that the central processing unit can process. A) Recursive functions B) Instruction sets C) Operational bits D) Application programs Page Ref: 107 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 2 21) Which of the following is the operating system designed by Apple? A) Android B) Unix C) Linux D) Mac OS Page Ref: 108 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 2 22) is a version of Unix that was developed by an open source community. A) Symbian OS B) Android C) Linux D) Mac OS Page Ref: 109 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 2 23) Linux is an example of a(n) . A) open source operating system B) mobile operating system C) user community D) application software that creates documents Page Ref: 109 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 2 24) Which of the following is a mobile operating system licensed by Google? A) Blackberry OS B) Symbian C) Android D) Windows mobile Page Ref: 110 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 2 25) Virtualization is the process by which . A) a single server is used to host the operations of a work station B) many computers are used to control a server C) one computer hosts the appearance of many computers D) a single operating system is licensed for multiple computers Page Ref: 110 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 2 26) With , a computer, such as a desktop or portable computer, hosts several different operating systems. A) PC virtualization B) parallel computing C) cloud computing D) grid computing Page Ref: 111 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 2 27) Ronald runs both Windows 7 and Linux on his desktop computer. This process is called . A) PC virtualization B) server virtualization C) cloud computing D) desktop virtualization Page Ref: 111 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 2 28) With server virtualization, a server computer hosts . A) multiple operating systems B) one or more server computers C) virtual host operating systems D) databases that contain information about servers Page Ref: 111 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 2 29) Which of the following terms refers to the process of a single server hosting many versions of desktop operating systems? A) PC virtualization B) cloud computing C) desktop virtualization D) server virtualization Page Ref: 111 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different business intelligence systems Chapter LO: 2 30) When you buy an operating system for your personal computer, you are actually buying a software . A) copyright B) upgrade C) patent D) license Page Ref: 112 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Describe the components of an information system (IS) Chapter LO: 2 31) Programs that perform business functions, such as general ledger and accounting, are known as . A) application software B) system software C) firmware D) operating systems Page Ref: 112 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 2 32) A spreadsheet program is an example of a(n) . A) vertical-market application software B) operating system C) firmware D) horizontal-market application software Page Ref: 112 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different business intelligence systems Chapter LO: 2 33) Which of the following is an example of a vertical-market application software? A) inventory tracking software for an auto manufacturer B) at-home tax preparation software C) Adobe suite used by graphic designers D) Microsoft PowerPoint used to create presentations Page Ref: 112 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Compare and contrast different business intelligence systems Chapter LO: 2 34) DenTimes, a software package for dentists, is an example of a . A) horizontal-market application software B) vertical-market application software C) generic market application software D) one-of-a-kind application software Page Ref: 112 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Compare and contrast different business intelligence systems Chapter LO: 2 35) is installed in special, read-only memory in devices like printers or communication devices. A) Vertical-market software B) Application software C) Firmware D) Operating system Page Ref: 116 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 2 36) Which of the following statements is true of firmware? A) The software is coded differently from other software. B) Users do not need to load firmware into the a device's memory. C) Firmware is the same as system cache. D) Firmware cannot be changed or upgraded. Page Ref: 116 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the major types of computer hardware and software used by companies Chapter LO: 2 37) Which of the following is an open source browser? A) Internet Explorer B) Ubuntu C) Firefox D) Apache Page Ref: 116 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the major types of computer hardware and software used by companies Chapter LO: 3 38) Which of the following is an example of an open source operating system? A) MS Office B) Apache C) MySQL D) Ubuntu Page Ref: 116 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the major types of computer hardware and software used by companies Chapter LO: 3 39) The term "open source" means that the source code of the program is . A) less stable and platform dependent B) available to the public C) available for licensing if desired D) available only to carefully vetted contractors Page Ref: 117 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the major types of computer hardware and software used by companies Chapter LO: 3 40) Source code is computer code . A) as written by humans B) that is not understandable by humans C) that is represented as bits and bytes D) as processed by a computer Page Ref: 117 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the major types of computer hardware and software used by companies Chapter LO: 3 41) Machine code . A) is written in high-level languages B) cannot be modified by humans C) is usually written by humans D) is the simplest mode of communicating with computers Page Ref: 117 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 3 42) Which of the following statements is true of closed source projects? A) Only users and developers are allowed to alter the source code in closed source projects. B) Anyone can obtain the source code for a closed source project. C) Only trusted programmers are allowed to make changes to a closed source project. D) Programmers alter or add to closed source code based on their interests and goals. Page Ref: 117 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the major types of computer hardware and software used by companies Chapter LO: 3 43) Which of the following is an example of a closed source project? A) Firefox B) Android C) Microsoft Office D) Ubuntu Page Ref: 117 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the major types of computer hardware and software used by companies Chapter LO: 3 44) Mac OS and iOS applications are constructed using . A) Objective C B) C# C) Java D) VB.Net Page Ref: 118 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Describe the major types of computer hardware and software used by companies Chapter LO: 4 45) Linux applications are developed using . A) Objective C B) C# C) Java D) VB.Net Page Ref: 118 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Describe the major types of computer hardware and software used by companies Chapter LO: 4 46) Android applications are developed using . A) Objective C B) C# C) Java D) VB.Net Page Ref: 118 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Describe the major types of computer hardware and software used by companies Chapter LO: 4 47) Java, C# and VB.Net are examples of . A) native applications B) client operating systems C) structured queries D) object-oriented languages Page Ref: 118 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Describe the components of an information system (IS) Chapter LO: 4 48) A client-server application that requires nothing more than a browser is called a . A) thick-client application B) desktop application C) firmware D) thin-client application Page Ref: 119 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different business intelligence systems Chapter LO: 4 49) An application that requires support beyond a browser on the user's computer is known as a(n) . A) thick-client application B) cloud application C) open source program D) thin-client application Page Ref: 119 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different business intelligence systems Chapter LO: 4 50) Thin-client applications are developed using . A) HTML5 B) Java C) Objective-C D) C# Page Ref: 119 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Describe the major types of computer hardware and software used by companies Chapter LO: 4 51) Thin-client applications are limited by the capabilities of the . A) programing language B) browser C) hardware D) operating system Page Ref: 120 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the major types of computer hardware and software used by companies Chapter LO: 4 52) A is a small, lightweight, power-conserving, computing device that is capable of wireless access. A) PC B) mainframe computer C) server D) mobile device Page Ref: 124 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the major types of computer hardware and software used by companies Chapter LO: 5 53) Which of the following is an example of a mobile device? A) smartphone B) Xbox C) desktop D) Play Station 3 Page Ref: 124 AACSB: Analytic Skills Difficulty: Moderate Course LO: Describe the major types of computer hardware and software used by companies Chapter LO: 5 54) is data delivered to the user at the precise time it is needed. A) Real-time data B) Just-in-time data C) Block data D) Raw data Page Ref: 127 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 5 55) A user interface (UI) is the format of an application. A) underdeveloped B) graphical C) web-based D) presentation Page Ref: 128 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 6 56) is a term that refers to the visual overhead in a computer display. A) Chrome B) Charm C) Prime D) UX Page Ref: 128 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 6 57) occurs when users move their activities, especially long-running transactions, across devices. A) Tracking B) Reaping C) Formatting D) Roaming Page Ref: 131 AACSB: Use of Information Technology Difficulty: Easy Course LO: Describe the components of an information system (IS) Chapter LO: 6 58) Which of the following is an advantage to the organization, if its BYOD policy offers wireless network to mobile devices? A) The organization can sniff employees' mobile traffic. B) Employees gain public access from any device, not just mobile devices. C) The policy appears to be permissive without actually being so. D) Employees resist turning over the management of their own hardware to the organization. Page Ref: 134 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Discuss the role of information systems in supporting business processes Chapter LO: 7 59) Which of the following is an advantage to the organization, if its BYOD policy holds the employee responsible for any kind of damage? A) The organization can sniff employees' mobile traffic. B) Employees gain public access from any device, not just mobile devices. C) The policy appears to be permissive without actually being so. D) Employees resist turning over the management of their own hardware to the organization. Page Ref: 135 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Discuss the role of information systems in supporting business processes Chapter LO: 7 60) install and update software, back up and restore mobile devices, wipe software and data from devices in the event the device is lost or the employee leaves the company, report usage, and provide other mobile device management data. A) MDM software B) Data managers C) BYOD managers D) IS departments Page Ref: 135 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Discuss the role of information systems in supporting business processes Chapter LO: 7 1) The purpose of a(n) is to keep track of things. A) cloud B) database C) storage folder D) application software Page Ref: 151 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 1 2) Which of the following is the smallest data element in a database? A) field B) record C) byte D) file Page Ref: 152 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 2 3) The columns in a database are called . A) records B) tables C) files D) fields Page Ref: 152 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 2 4) The rows in a database are called . A) records B) tables C) files D) fields Page Ref: 152 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 2 5) The tables that appear in a database are known as . A) records B) files C) fields D) applications Page Ref: 152 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 2 6) Which of the following data elements is placed higher than records in the data hierarchy? A) file B) field C) character D) byte Page Ref: 153 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 2 7) A primary key used in a database is a . A) group of rows that are formed to identify a unique table or file B) column or group of columns that identifies a unique row in a table C) character or byte that represents fields or columns D) group of tables or files formed to identify a unique field or row Page Ref: 153 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 2 8) Albert creates a relational database to store employee performance statistics. He stores each employee's data in independent rows and creates a column named "Employee Number" to assign unique numbers to each employee. This column is referred to as a(n) . A) primary key B) identifier C) foreign key D) primary record Page Ref: 153 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Discuss best practices for using and managing databases Chapter LO: 2 9) Columns that belong to a different table than the one in which they reside are called . A) attributes B) foreign keys C) primary keys D) internal records Page Ref: 154 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 2 10) Relational databases represent relationships using . A) foreign keys B) file systems C) metadata D) unique identifiers Page Ref: 154 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 2 11) Metadata are . A) data stored on the main server B) error logs of databases C) data that describe data D) encrypted data transmissions Page Ref: 155 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 2 12) A(n) is a program used to create, process, and administer a database. A) operating system B) DBMS C) KMS D) data mart Page Ref: 156 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 3 13) Which of the following is an example of a database management system? A) MS Excel B) Unix C) Ubuntu D) Access Page Ref: 158 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 3 14) From among the following, identify the open source DBMS product. A) MySQL B) DB2 C) Access D) Oracle Database Page Ref: 158 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 3 15) Which of the following is a valid observation of MySQL? A) It is offered by Oracle. B) It is license-free for most applications. C) It is a closed-source database product. D) It is yet to be widely adopted. Page Ref: 158 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 3 16) When you modify or delete data present in a database, you are . A) creating a new database B) forming a data model C) simplifying the data structure D) processing the database Page Ref: 158 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 3 17) Which of the following is an international standard language for processing a database? A) Paradox B) DB2 C) SQL D) MS Access Page Ref: 160 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 3 18) Which of the following is a developmental task of database administration? A) creating and staffing the DBA function B) monitoring backup procedures C) conducting training for users D) managing configuration changes in systems Page Ref: 161 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 3 19) Identify the type of task that a database administrator is performing when validating the data model to be used in a database management system. A) development B) adaptation C) recovery D) operation Page Ref: 161 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 3 20) The database administrator of an organization constantly manages the processing rights and responsibilities of employees. This is an example of a(n) task. A) development B) recovery C) adaptation D) operational Page Ref: 161 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 3 21) Which of the following database administration tasks is related to adaptation? A) monitoring backup procedures B) conducting training for users C) monitoring database performance D) managing configuration changes in systems Page Ref: 161 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 3 22) A is a collection of forms, reports, queries, and programs that process a database. A) database application B) database design C) data field D) data model Page Ref: 161 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 4 23) forms are used to read, insert, modify, and delete data. A) Reporting B) Data entry C) Query D) Request Page Ref: 161 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 4 24) A is a request for data from a database. A) data entry B) report C) query D) command Page Ref: 162 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 4 25) Brenda, the sales manager of a firm, wants to generate a particular report containing sales analyses of the second and third quarter of the year. After accessing the DBMS, she should type the keyword into a form to obtain the information that she wants. A) report B) reference C) data entry D) query Page Ref: 162 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Discuss best practices for using and managing databases Chapter LO: 4 26) Which of the following refers to the problem that exists in database applications when two users update the same data item, but only one of those changes is recorded? A) lost-update problem B) crow's-foot paradigm C) bullwhip effect D) update query problem Page Ref: 163 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Discuss best practices for using and managing databases Chapter LO: 4 27) A(n) DBMS is designed to process large organizational and workgroup databases. A) operational B) process C) personal D) enterprise Page Ref: 164 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 4 28) An organization buys a proprietary database application to be used by a small workgroup of five people. This is an example of a(n) DBMS. A) enterprise B) interenterprise C) personal D) open source Page Ref: 164 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Discuss best practices for using and managing databases Chapter LO: 4 29) Which of the following is an example of an enterprise DBMS? A) Access B) SQL Server C) Paradox D) FoxPro Page Ref: 164 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 4 30) Which of the following types of DBMS products is designed for smaller and simpler database applications? A) object-oriented DBMS B) strategic DBMS C) personal DBMS D) enterprise DBMS Page Ref: 164 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 4 31) is an example of a personal DBMS. A) SQL Server B) DB2 C) Oracle Database D) Access Page Ref: 164 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 4 32) A describes the data and relationships that will be stored in a database. A) data aggregator B) query model C) data model D) data application Page Ref: 165 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 5 33) An administrator should create before developing a database design. A) data aggregator B) query model C) data model D) data application Page Ref: 165 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 5 34) A data model is a . A) logical representation of database data B) repository of unprocessed data C) collection of isolated databases D) set of programs to retrieve data Page Ref: 165 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 5 35) In a data model, a(n) is something that a user wants to track. A) record B) byte C) entity D) primary key Page Ref: 165 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 5 36) Brad, a project manager, wants to build a database to integrate information about employees and tasks that they handle. Brad wants to track information such as task name, percentage completed, and employee name. These aspects that Brad wants to track are called . A) identifiers B) records C) primary keys D) entities Page Ref: 165 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Discuss best practices for using and managing databases Chapter LO: 5 37) Entities in a data model have that describe the characteristics of the entity. A) characters B) primary keys C) codes D) attributes Page Ref: 165 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 5 38) Each entity in a database has a unique attribute called a(n) . A) public key B) identifier C) foreign key D) index field Page Ref: 165 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 5 39) In an E-R diagram, a line between two entities represents a(n) . A) attribute B) identifier C) cardinality D) relationship Page Ref: 167 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 5 40) The forked lines on the right side of a line on an E-R diagram that indicates a 1:N relationship between two entities is referred to as . A) Kerberos B) maximum cardinality C) crow's feet D) minimum cardinality Page Ref: 167 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 5 41) Which of the following is true of N:M relationships? A) The number of entities on each side must be equal. B) They are common examples of minimum cardinalities. C) They are also called one-to-many relationships. D) They can have more than one entity on each side of the relationship. Page Ref: 167 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Discuss best practices for using and managing databases Chapter LO: 5 42) A student management system allows students to have multiple majors and advisers are assigned to handle multiple students and courses. This is an example of a(n) relationship. A) 1:N B) 1:1 C) N:M D) M:1 Page Ref: 167 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Discuss best practices for using and managing databases Chapter LO: 5 43) Minimum cardinalities in an E-R diagram refer to the minimum number of entities required in a(n) . A) department B) database C) attribute D) relationship Page Ref: 168 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 5 44) Constraints on the number of entities in a relationship are called cardinalities. A) specific B) minimum C) primary D) critical Page Ref: 168 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 5 45) In an E-R diagram, a(n) on a line means that at least one entity of that type is required. A) small oval B) vertical bar C) arrow D) triangular block Page Ref: 168 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 5 46) Which of the following formations on a line in an E-R diagram means that the relationship need not have an entity of that type? A) vertical bar B) arrow C) double line D) small oval Page Ref: 168 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 5 47) is the process of converting a data model into tables, relationships, and data constraints. A) Database design B) Database querying C) Data mining D) Database aggregation Page Ref: 168 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 6 48) A database design team transforms entities into tables and expresses relationships by defining . A) cardinalities B) attributes C) foreign keys D) departments Page Ref: 168 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 6 49) is the process of converting a poorly- structured table into two or more well- structured tables. A) Optimization B) Normalization C) Refactoring D) Standardization Page Ref: 168 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 6 50) In a database, when data items disagree with one another, this leads to a(n) . A) data integrity problem B) crow's-foot paradigm C) adaptation conflict D) lost-update problem Page Ref: 169 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 6 51) A data integrity problem will occur only if . A) there are multiple administrators B) data are duplicated C) the database is very large D) there are complex relationships Page Ref: 169 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 6 52) Every table in a normalized database has . A) duplicated data model B) single theme C) maximum cardinality D) specialized query format Page Ref: 169 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 6 53) Identify the first step in transforming a data model into a relational database design. A) representing the data relationships B) normalizing the data and files C) creating foreign keys D) creating a table for each entity Page Ref: 170 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 6 54) When using the relational model to represent data, one must . A) add a foreign key to one of the tables B) have more than ten tables in the model C) establish only N:M relationships between tables D) use metadata instead of foreign keys Page Ref: 170 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 6 55) Which of the following is true about the database development process? A) The database structure cannot be changed during the data modeling stage. B) Changing a relationship from 1:N to N:M is simply a matter of changing the notations. C) User review of the data model is avoided as it is not helpful in data modeling. D) A database is a model of how the developers view their business world. Page Ref: 173 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Discuss best practices for using and managing databases Chapter LO: 7 56) are the final judges as to what data the database should contain and how the records in that database should be related to one another. A) Administrators B) Developers C) Users D) Designers Page Ref: 173 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 7 57) Which of the following is a nonrelational data store developed by Amazon? A) Cassandra B) Dynamo C) SharePoint D) Bigtable Page Ref: 174 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 8 58) Which of the following is a nonrelational data store developed by Google? A) Cassandra B) Dynamo C) SharePoint D) Bigtable Page Ref: 174 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 8 59) Which of the following is a nonrelational data store developed by Facebook? A) Cassandra B) Dynamo C) Bigtable D) SharePoint Page Ref: 174 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss best practices for using and managing databases Chapter LO: 8 1) A computer is a collection of computers that communicate with one another over transmission lines or wirelessly. A) database B) application C) network D) server Page Ref: 189 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 1 2) Which of the following is the distinguishing feature of a LAN as compared to a WAN? A) single location B) number of users C) bandwidth D) hardware requirements Page Ref: 189 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 1 3) Computers that reside in different geographic locations are connected using a(n) . A) WAN B) LAN C) URL D) IP address Page Ref: 189 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 1 4) A private internet that is used exclusively within an organization is called a(n) . A) Ethernet B) intranet C) cloud D) server Page Ref: 190 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 1 5) A is a set of rules that programs on two communicating devices follow. A) codec B) URL C) packet D) protocol Page Ref: 190 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 1 6) To enable the seamless flow of data across the networks that comprise an internet, an elaborate scheme called a is used. A) layered protocol B) virtual private network C) three-tier system D) remote access system Page Ref: 190 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 1 7) A is a special-purpose computer that receives and transmits wired traffic on the LAN. A) codec B) modem C) switch D) port Page Ref: 190 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 2 8) Which of the following is the device that connects a computer's or printer's circuitry to network wires? A) port B) switch C) router D) NIC Page Ref: 191 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 2 9) Most LAN connections are made using . A) Sc/TP cable B) UTP cable C) STP cable D) F/TP cable Page Ref: 191 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 2 10) For a printer or laptop to connect to a wireless LAN, it must have a . A) hyperlink B) UTP cable C) WNIC D) DSL Page Ref: 191 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 2 11) Which of the following is a component of a LAN device that processes wireless traffic and communicates with the wired switch? A) access point B) packet C) server D) router Page Ref: 191 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 2 12) The IEEE 802.3 protocol standard is also known as . A) Bluetooth B) Ethernet C) Intranet D) Internet Page Ref: 192 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 2 13) Which of the following statements is true about IEEE 802.3? A) It is the protocol for wireless LAN connections. B) It is the protocol for Bluetooth. C) It is the protocol for wired LAN connections. D) It is the universal standard protocol for WNICs. Page Ref: 192 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 2 14) Communications speeds are expressed in . A) bits B) bytes C) hertz D) packets Page Ref: 192 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 2 15) Which of the following statements is true about the IEEE 802.11 protocol? A) It is also known as Ethernet. B) It is used for wired LAN connections. C) It cannot be processed by access points. D) It allows speeds of up to 600 Mbps. Page Ref: 192 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 2 16) is a wireless protocol designed for transmitting data over short distances, replacing cables. A) IPv6 B) PaaS C) Bluetooth D) Silverlight Page Ref: 192 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 2 17) Which of the following is a function of an ISP? A) It transmits data over short distances, replacing cables. B) It serves as a gateway to the Internet. C) It describes how messages must be processed for wired transmission. D) It connects computers within a LAN. Page Ref: 192 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 2 18) Which of the following transmission lines is used for Local Area Networks? A) DSL Telephone B) Cable TV Lines C) UTP D) Wireless connection Page Ref: 193 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 2 19) Which of the following is true of DSL modems? A) DSL modem signals do not interfere with telephone signals. B) DSL modems use the same protocols as cable modems for data transmission. C) DSL modem signals replace phone signals and are sent to the ISP. D) DSL data transmission and telephone conversations cannot occur simultaneously. Page Ref: 193 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 2 20) modems modulate in such a way that they do not interfere with TV signals, even though they use the same lines. A) DSL B) Dial-up C) Cable D) ADSL Page Ref: 193 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 2 21) Which of the following is true about cable modems? A) They provide high-speed data transmission using telephone cables. B) They offer consistent performance, irrespective of the number of users sending and receiving data. C) They rely on high-capacity optical fiber cables and use their own protocols for data transmission. D) They provide faster download speeds than DSL modems. Page Ref: 193 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 2 22) typically have transmission speeds less than 56 Kbps. A) Narrowband lines B) Digital subscriber lines C) Cable modems D) WAN wireless connections Page Ref: 194 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 2 23) The protocols used on the Internet are arranged according to a structure known as the protocol architecture. A) FTP B) VOIP C) ICANN D) TCP/IP Page Ref: 196 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 3 24) The top layer of TCP/IP Protocol architecture is related to . A) internets B) transport C) applications D) data links Page Ref: 196 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 3 25) Which of the following protocols is concerned with the application layer of TCP/IP Protocol architecture? A) HTTP B) IEEE 802.3 C) IEEE 802.11 D) IP Page Ref: 197 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 3 26) Which of the following protocols guarantees secure data transmission? A) HTTP B) FTP C) HTTPS D) SMTP Page Ref: 197 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 3 27) Which of the following TCP/IP application-layer protocols is used for email transmission? A) FTP B) HTTPS C) SMTP D) IP Page Ref: 197 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 3 28) Which of the following TCP/IP application-layer protocols is used to move files over the Internet and to maintain Web sites? A) FTP B) IP C) HTTPS D) HTTP Page Ref: 197 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 3 29) The primary protocol of the Internet layer of the TCP/IP protocol architecture is called . A) IP B) SMTP C) HTTP D) TCP Page Ref: 198 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 3 30) A(n) is a piece of a message that is handled by programs that implement IP. A) email B) packet C) tag D) attribute Page Ref: 198 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 3 31) A(n) is a special-purpose computer that moves packet traffic according to the rules of the IP protocol. A) router B) modem C) narrowband D) access point Page Ref: 198 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 3 32) A(n) is a number that identifies a particular device. A) domain B) IP address C) hyperlink D) href Page Ref: 198 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 3 33) The organization responsible for assigning public IP addresses is called . A) CERN B) IEEE C) ICANN D) ISO Page Ref: 198 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 3 34) Which of the following is the most common format for IP addresses? A) IPv4 B) TCP C) IPv6 D) HTTP Page Ref: 199 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 3 35) A is a worldwide-unique name that is affiliated with a public IP address. A) URL B) domain name C) tag D) trademark Page Ref: 199 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 3 36) When you visit the Web page of the luxury brand Bang & Olufsen, the address bar in your browser reads "http://www.bang-olufsen.com/", which is the of the Web page. A) URL B) IP address C) protocol D) email ID Page Ref: 200 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 3 37) A(n) uses the Internet to create the appearance of private point-to-point connections. A) VPN B) ISP C) router D) DSL Page Ref: 200 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 3 38) The connection between a VPN client and a VPN server is called a(n) . A) data highway B) hyperlink C) tunnel D) access point Page Ref: 200 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 3 39) Which of the following is true about a VPN? A) It encrypts messages to ensure secure transmissions. B) It does not provide users with remote access. C) It utilizes private networks instead of the public network. D) It appears as a secure connection, though it is not. Page Ref: 200 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 3 40) What are the three tiers in three-tier architecture? A) TCP, IP, and HTTP B) HTML, XML, and SGML C) user, server, and database D) router, switch, and access point Page Ref: 204 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 4 41) The tier of three-tier architecture consists of computers, phones, and other devices that have browsers that request and process Web pages. A) user B) server C) database D) data link Page Ref: 204 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 4 42) are programs that run on a server-tier computer and that manage HTTP traffic by sending and receiving Web pages to and from clients. A) Web servers B) Web browsers C) Web sites D) Web farms Page Ref: 205 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 4 43) is the most common language for defining the structure and layout of Web pages. A) HTML B) XML C) URL D) DSL Page Ref: 206 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 4 44) A(n) is a notation used to define a data element, for display or other purposes, in Web pages. A) HTML tag B) IP address C) domain D) hyperlink Page Ref: 206 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 4 45) An HTML document has a(n) that provides metadata about the page. A) href B) attribute C) tag D) heading Page Ref: 207 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 4 46) A(n) contains the URL of the Web page to find when a user clicks on it. A) access point B) IP address C) Web server D) hyperlink Page Ref: 207 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 4 47) An and its value indicate which Web page is to be displayed when a user clicks on a link. A) href B) IPv4 C) IaaS D) IPv6 Page Ref: 207 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 4 48) A(n) is a variable used to provide properties about a tag. A) HTML Tag B) attribute C) URL D) code Page Ref: 207 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 4 49) The attribute for hyperlink is called . A) href B) reference C) tag D) pointer Page Ref: 207 AACSB: Use of Information Technology Difficulty: Easy Course LO: Compare and contrast different ways of connecting to the Internet Chapter LO: 4 50) Which of the following is defined as the elastic leasing of pooled computer resources over the Internet? A) broadband B) wiki C) the cloud D) Bluetooth Page Ref: 208 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss the key issues involved in managing the components of IT infrastructure Chapter LO: 5 51) In cloud computing, resources are said to be "pooled" because . A) organizations use the public Internet to create the appearance of a private connection B) organizations use open source standards which enable users to modify a program's source code C) organizations offer their services to each other free of charge, in a give-and-take arrangement D) organizations share the same physical hardware through virtualization Page Ref: 208 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Discuss the key issues involved in managing the components of IT infrastructure Chapter LO: 5 52) Compared to in-house hosting, cloud-based hosting . A) provides better disaster preparedness capabilities B) minimizes the risk of investing in technology that will soon become obsolete C) provides greater control over the location of data D) requires a significant amount of capital Page Ref: 209 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Discuss the key issues involved in managing the components of IT infrastructure Chapter LO: 5 53) Which of the following is a benefit of in-house hosting? A) superior flexibility and adaptability to growing or fluctuating demand B) lower capital requirements C) in depth visibility of security and disaster preparedness D) fewer training requirements Page Ref: 209 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Discuss the key issues involved in managing the components of IT infrastructure Chapter LO: 5 54) In-house hosting, delivered via Web service standards that can be configured dynamically, is referred to as . A) the private cloud B) a virtual private network C) a wide area network D) the tunnel Page Ref: 210 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss the key issues involved in managing the components of IT infrastructure Chapter LO: 5 55) Which of the following is the most basic cloud offering? A) SaaS B) PaaS C) IaaS D) VPN Page Ref: 211 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss the key issues involved in managing the components of IT infrastructure Chapter LO: 6 56) A cloud vendor who provides hosted computers, an operating system, and a DBMS is offering which of the following services? A) SaaS B) PaaS C) IaaS D) VPN Page Ref: 211 AACSB: Use of Information Technology Difficulty: Easy Course LO: Discuss the key issues involved in managing the components of IT infrastructure Chapter LO: 6 57) Which of the following is an example of a PaaS? A) Apple iCloud B) Amazon EC2 C) Oracle on Demand D) Office 365 Page Ref: 211 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Discuss the key issues involved in managing the components of IT infrastructure Chapter LO: 6 58) Which of the following is an example of IaaS? A) Apple iCloud B) Microsoft Azure C) Office 365 D) Amazon EC2 Page Ref: 211 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Discuss the key issues involved in managing the components of IT infrastructure Chapter LO: 6 59) Amazon S3 (Simple Storage Service) is an example of . A) SaaS B) PaaS C) IaaS D) VPN Page Ref: 211 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Discuss the key issues involved in managing the components of IT infrastructure Chapter LO: 6 60) Which of the following would be a consequence of teleaction? A) The need for local support staff would decrease. B) The value of robotics would increase. C) The requirement for high-skill employees would decrease. D) Only high-value industries would be able to properly utilize it. Page Ref: 212 AACSB: Use of Information Technology Difficulty: Moderate Course LO: Discuss the key issues involved in managing the components of IT infrastructure Chapter LO: 7 [Show More]
Last updated: 1 year ago
Preview 1 out of 115 pages
Instant download
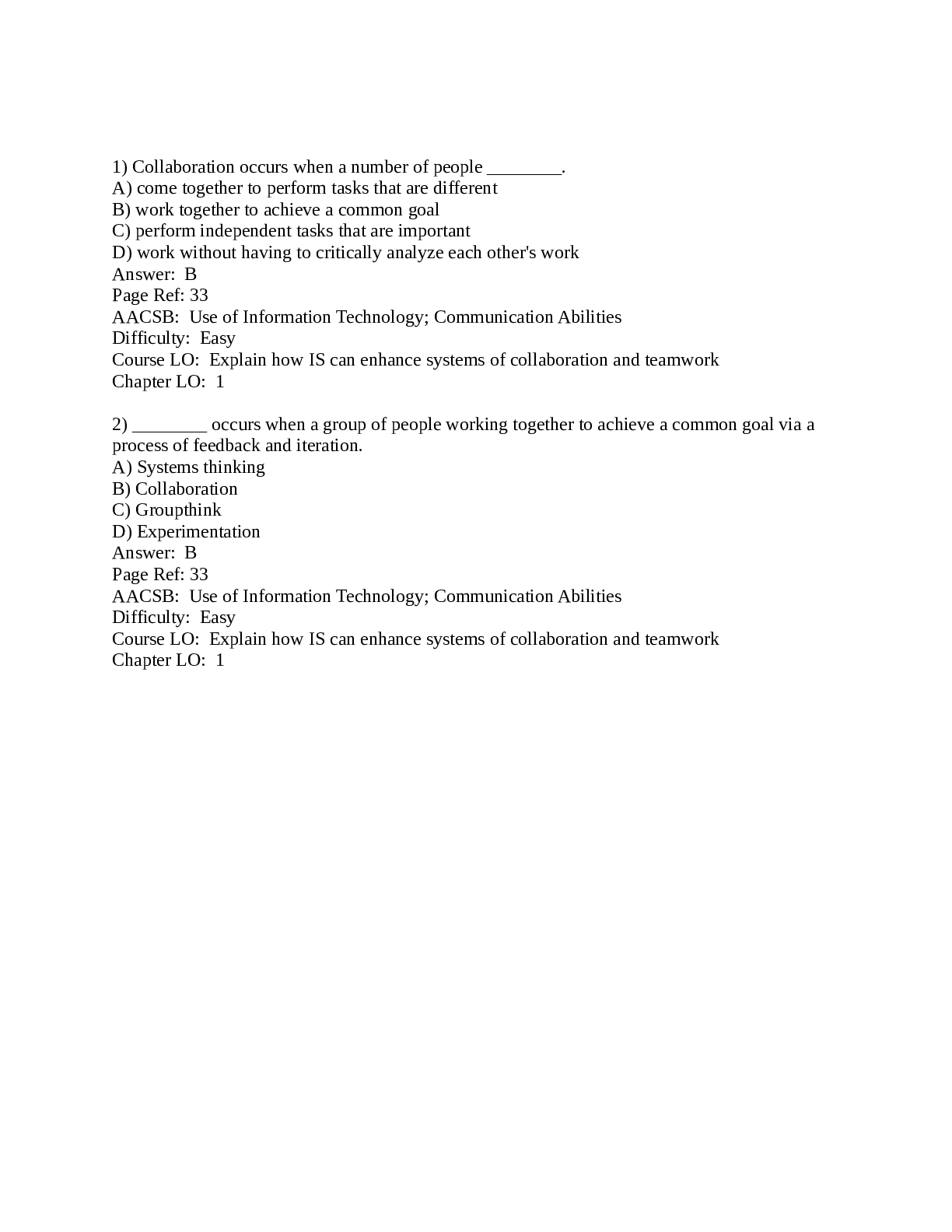
Buy this document to get the full access instantly
Instant Download Access after purchase
Add to cartInstant download
Reviews( 0 )
Document information
Connected school, study & course
About the document
Uploaded On
Aug 06, 2021
Number of pages
115
Written in
Additional information
This document has been written for:
Uploaded
Aug 06, 2021
Downloads
0
Views
41

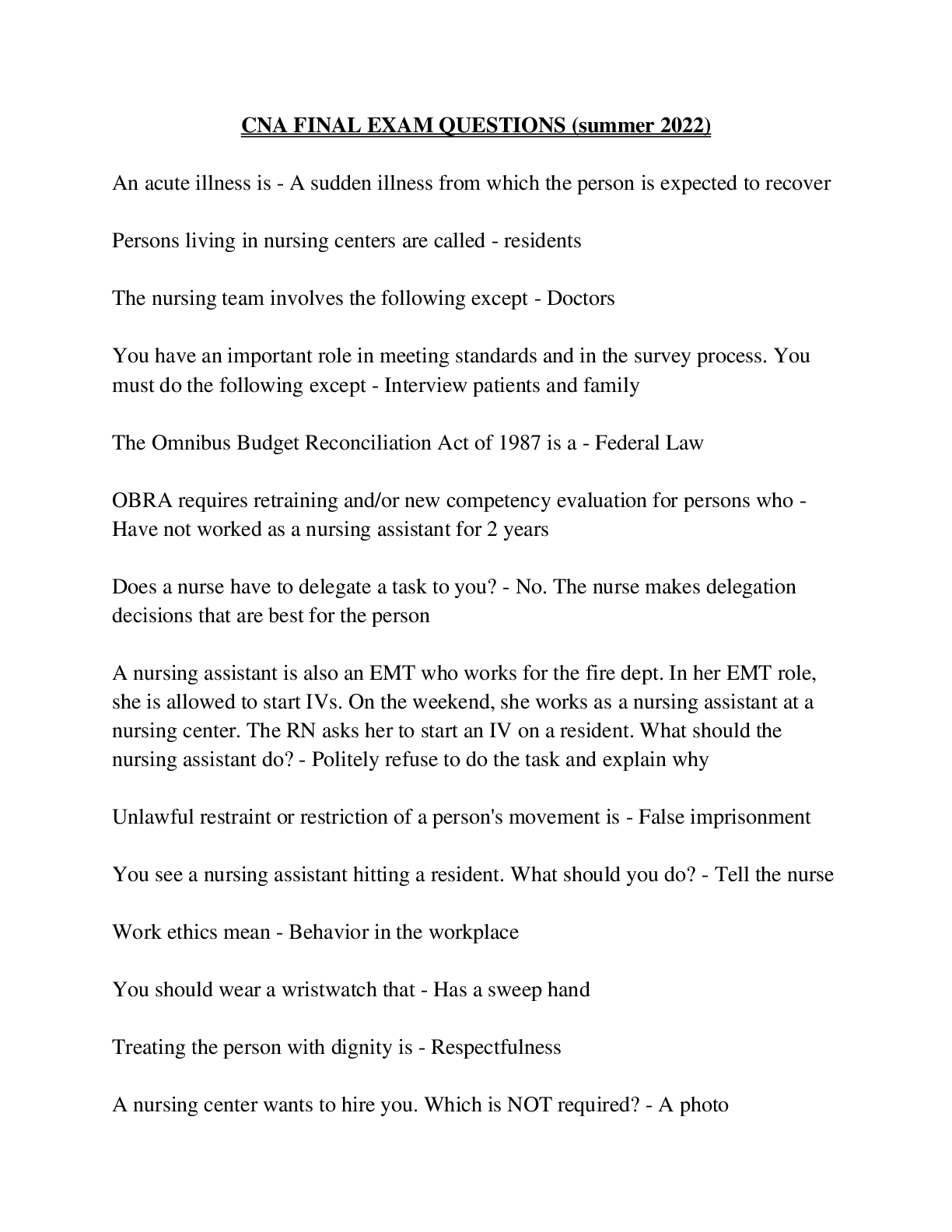
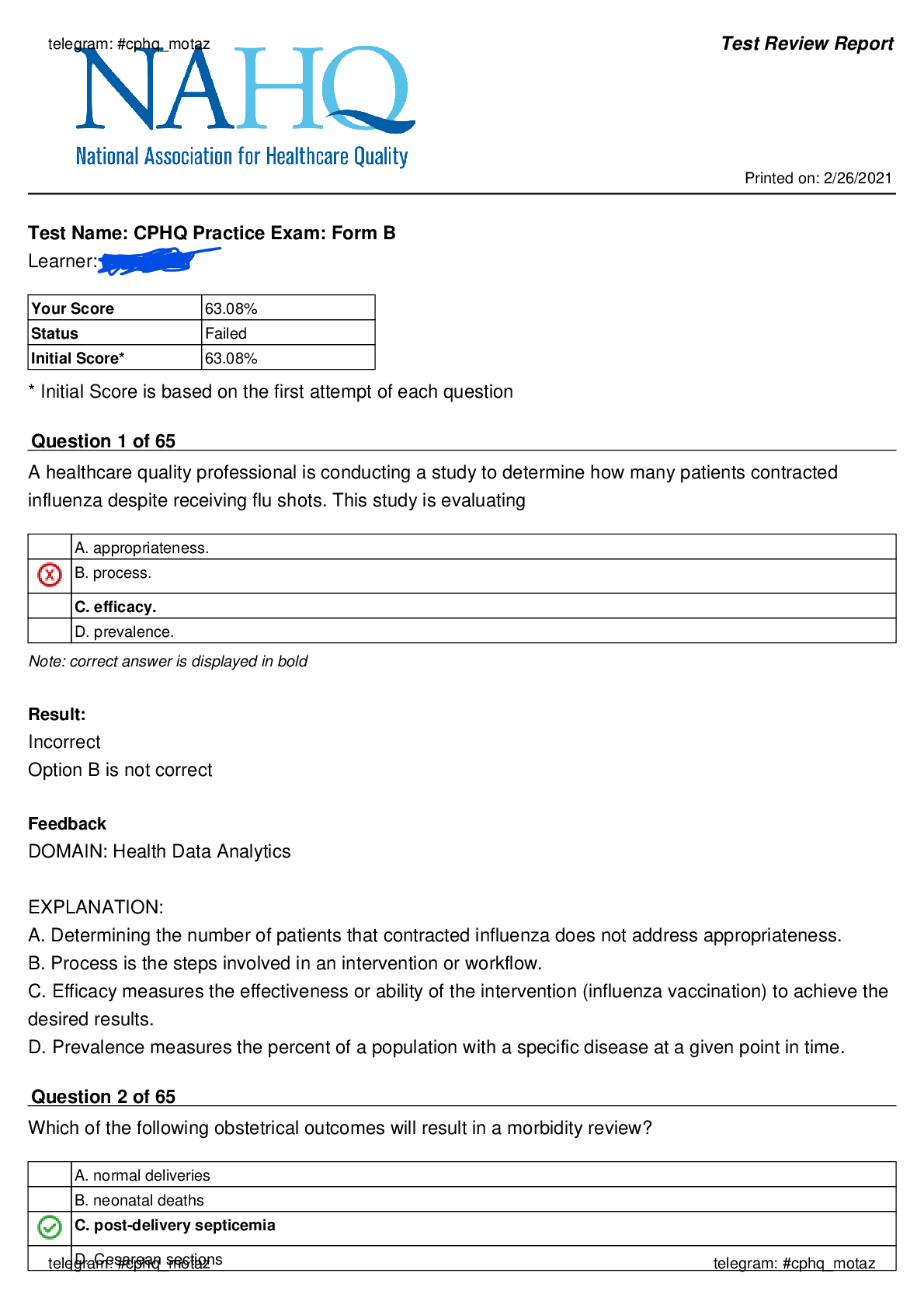
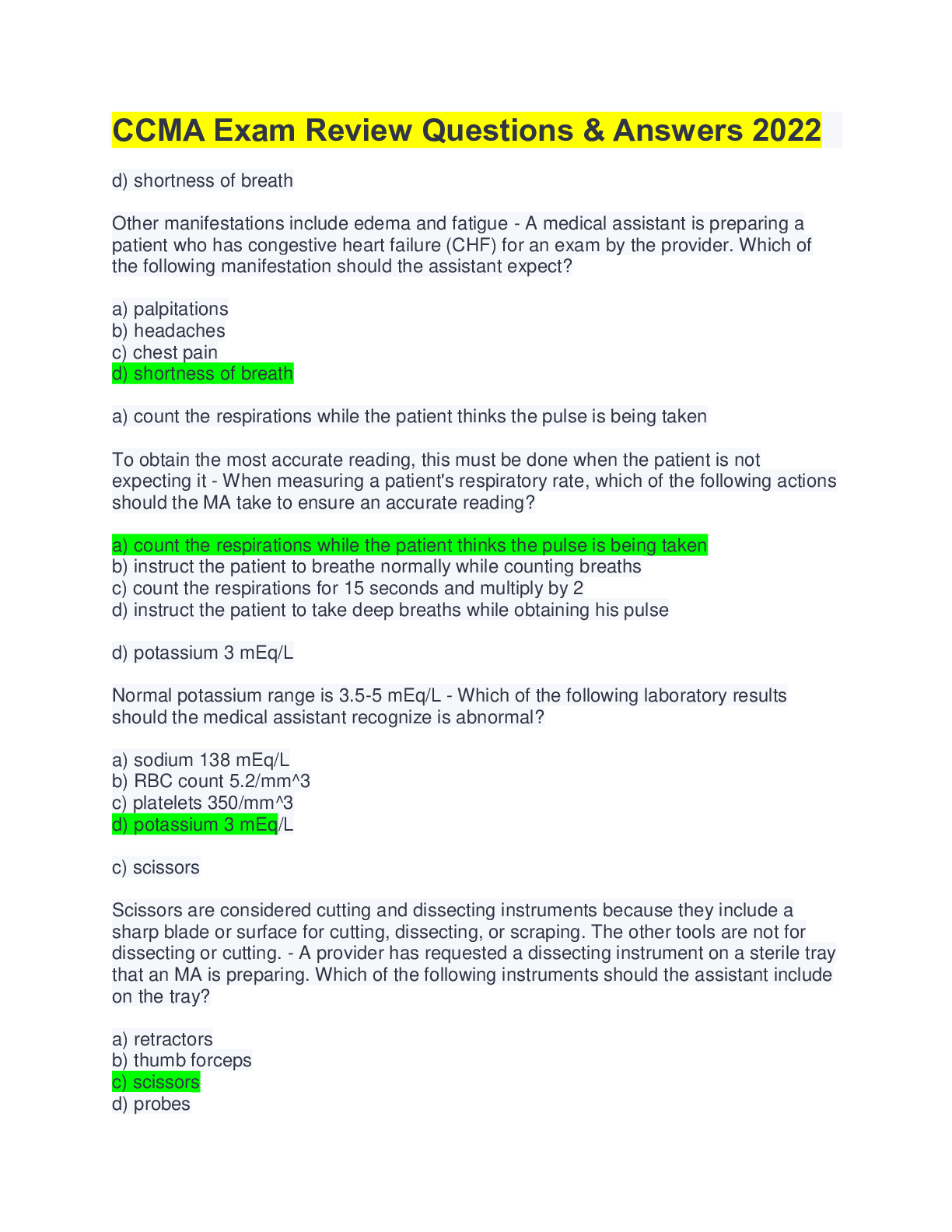
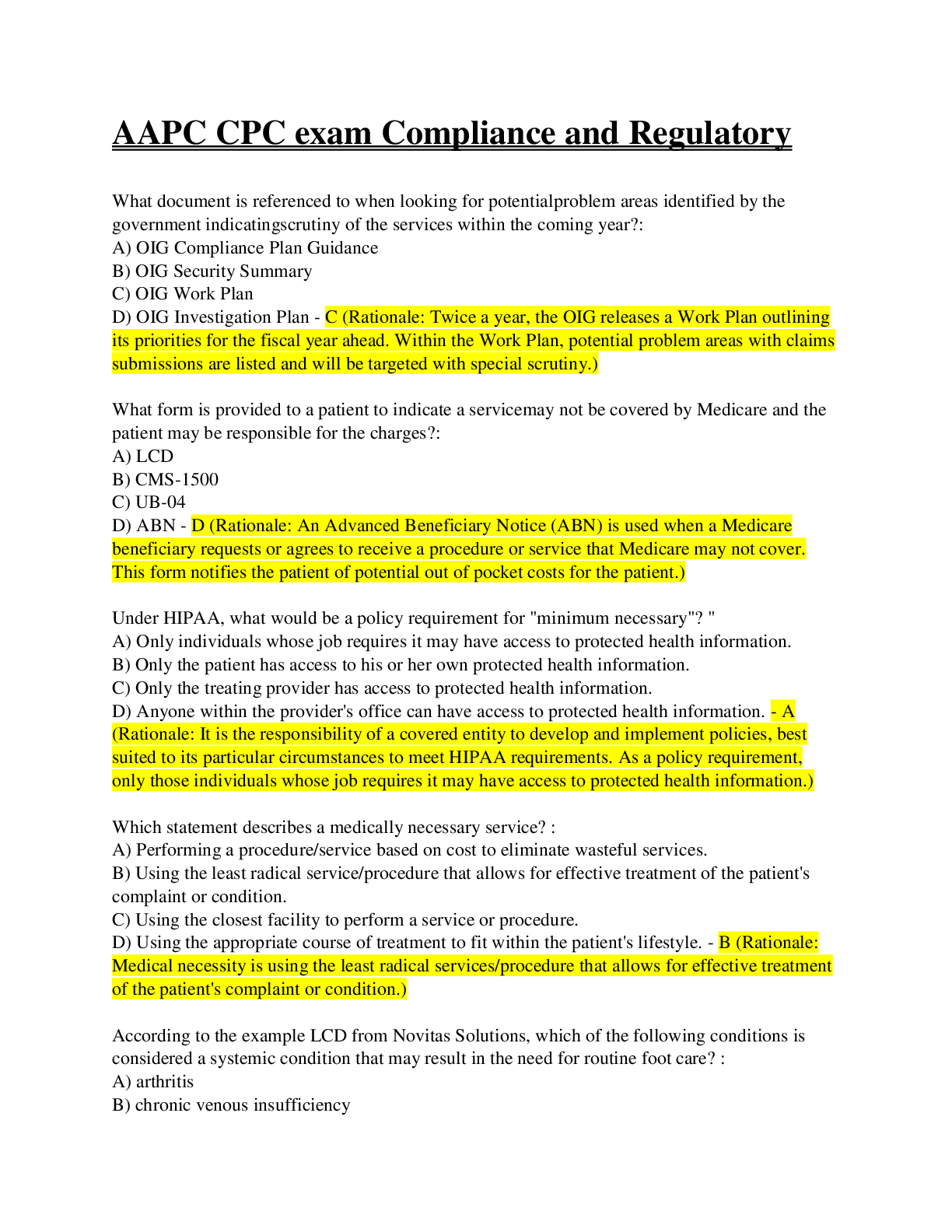
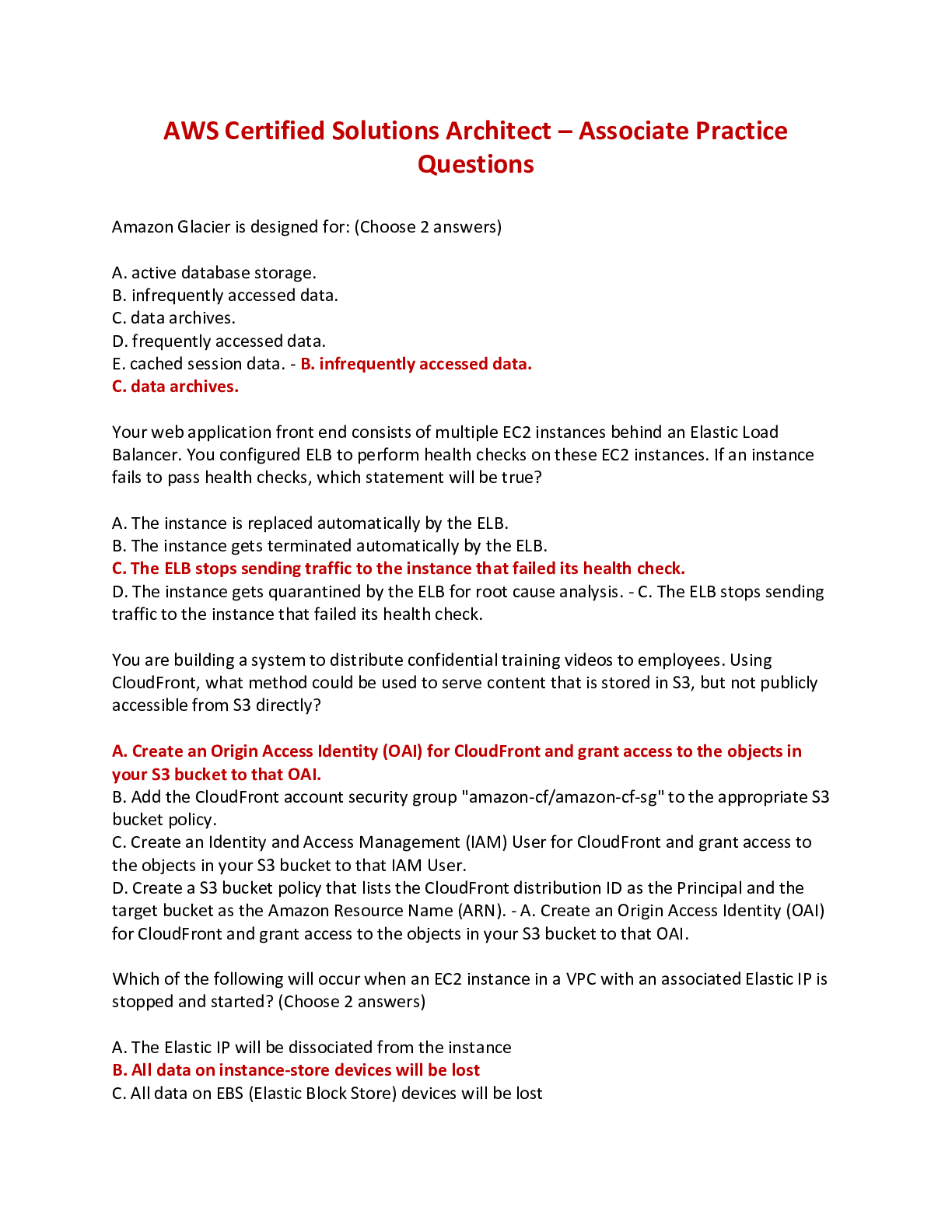
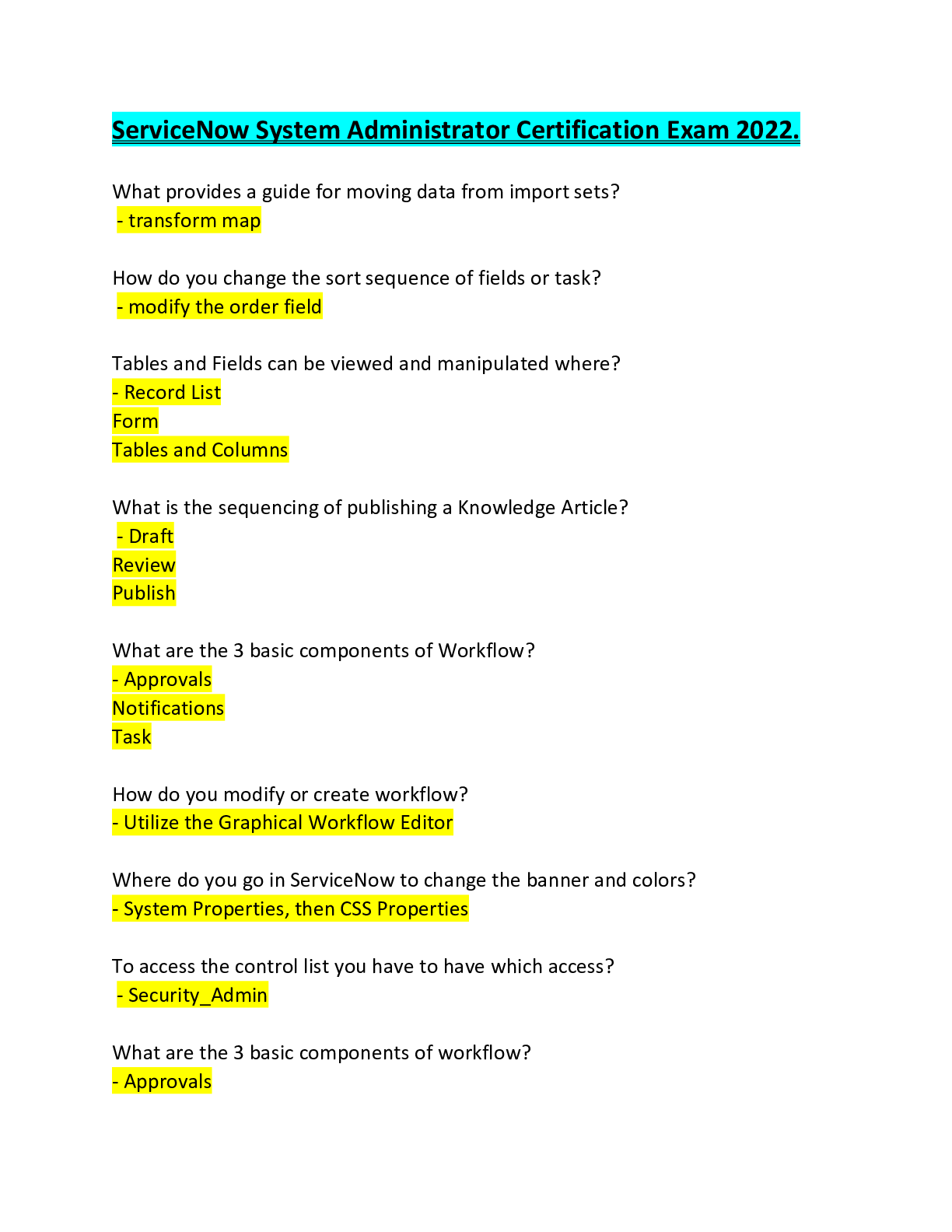
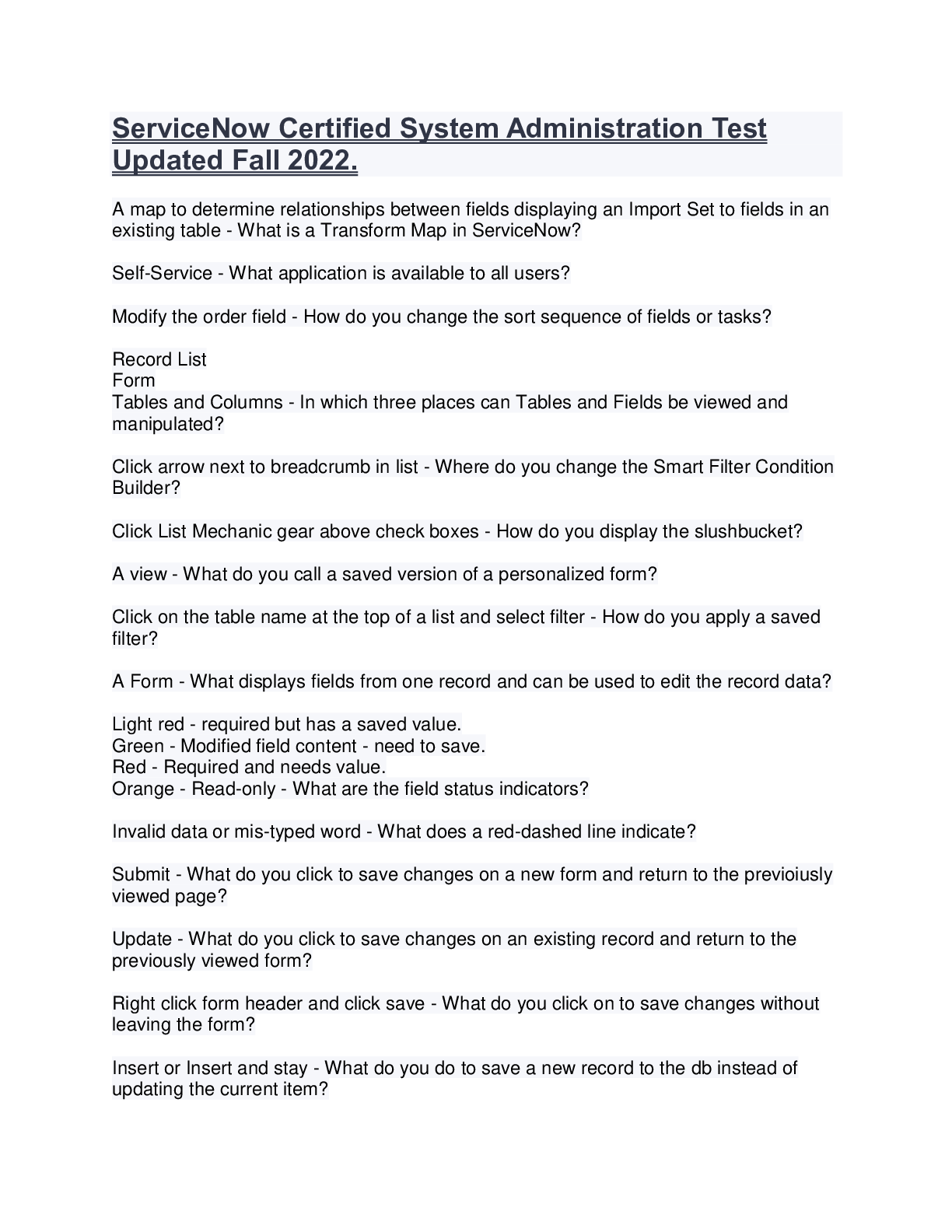
 Exam.png)
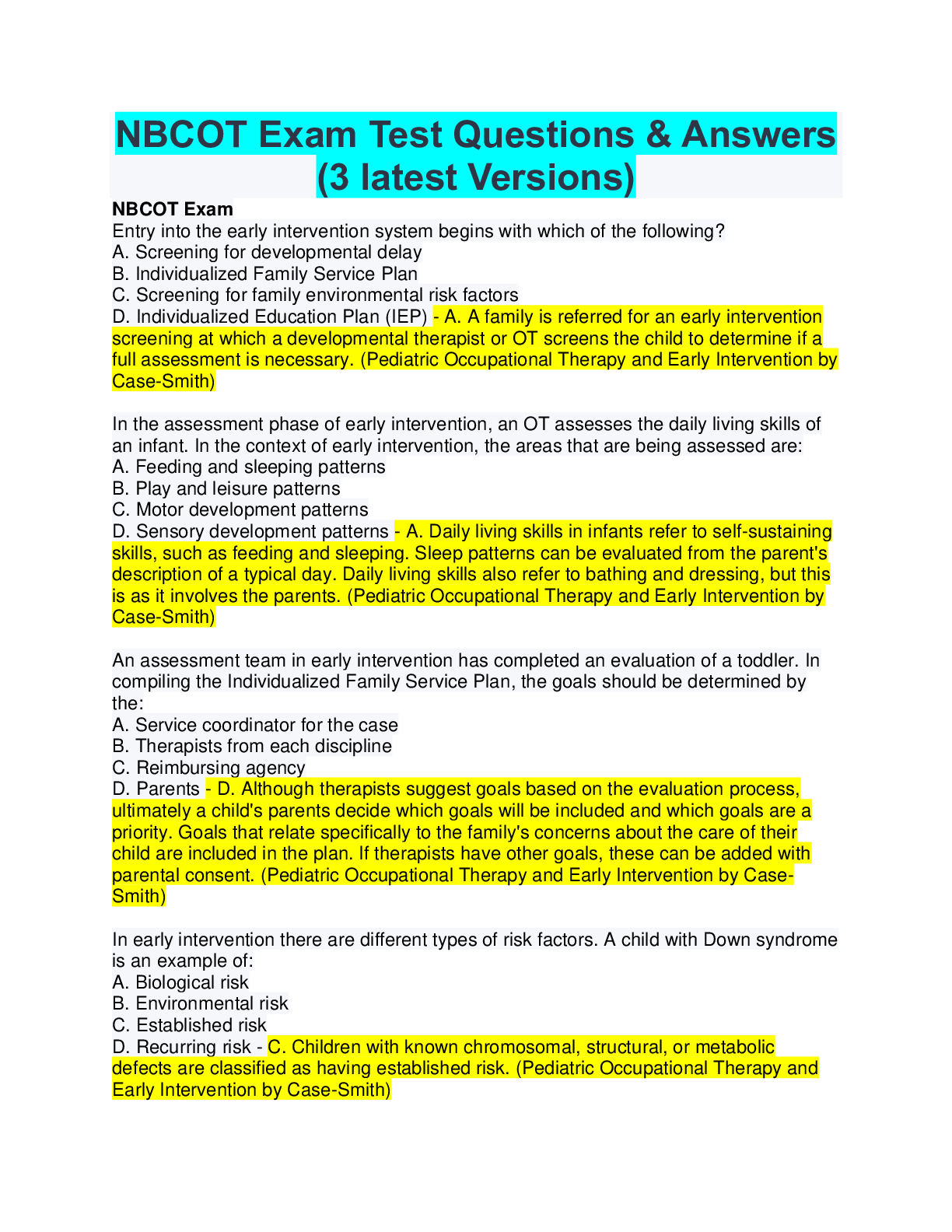
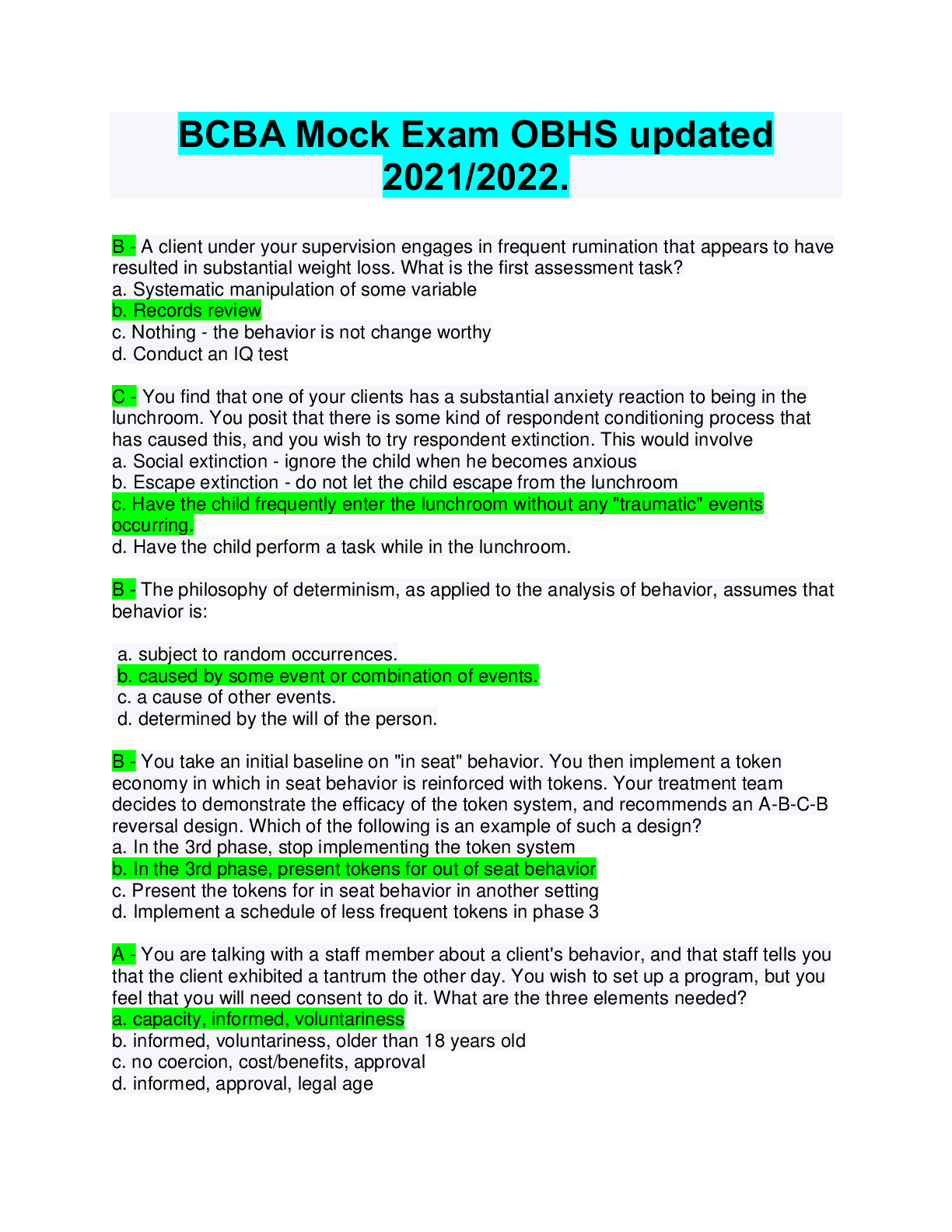
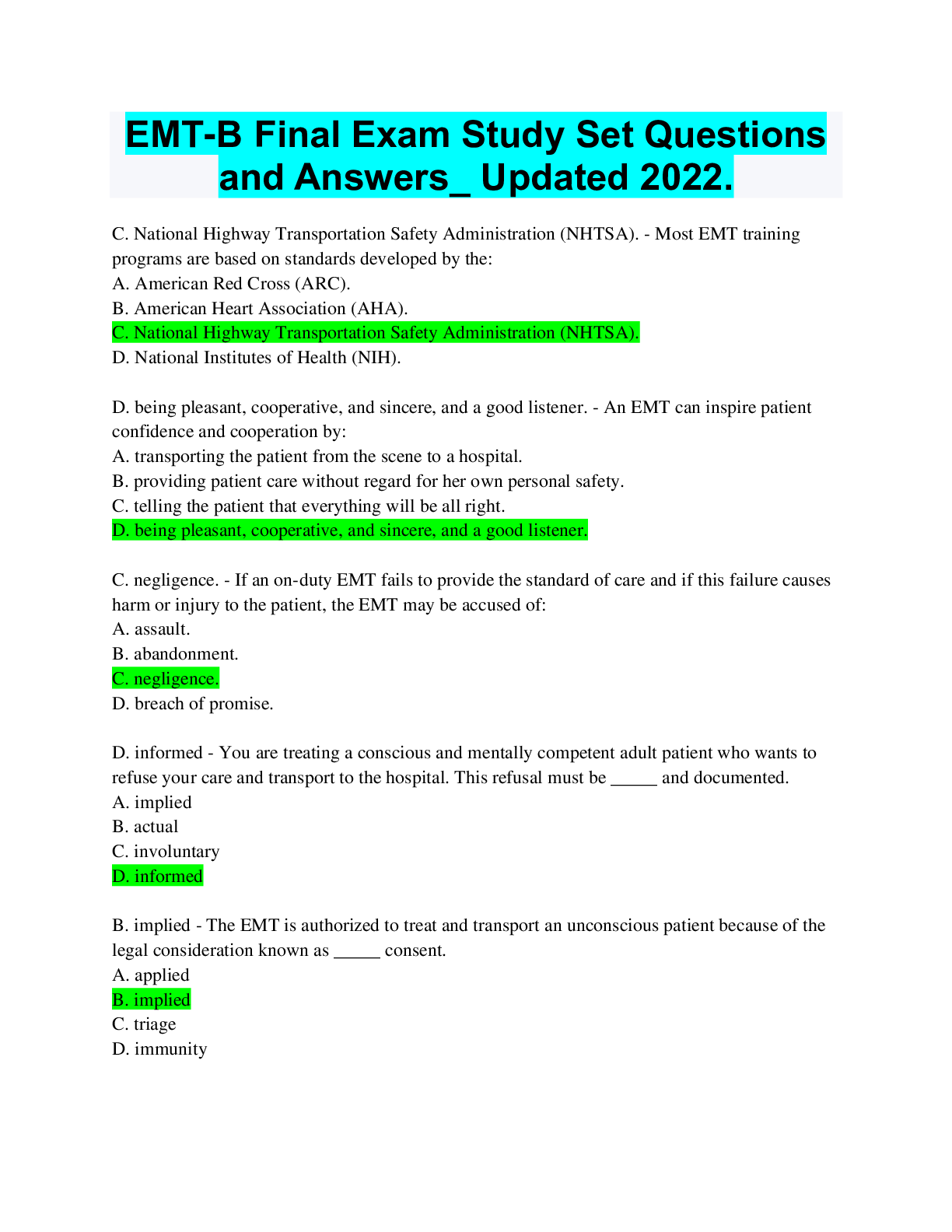
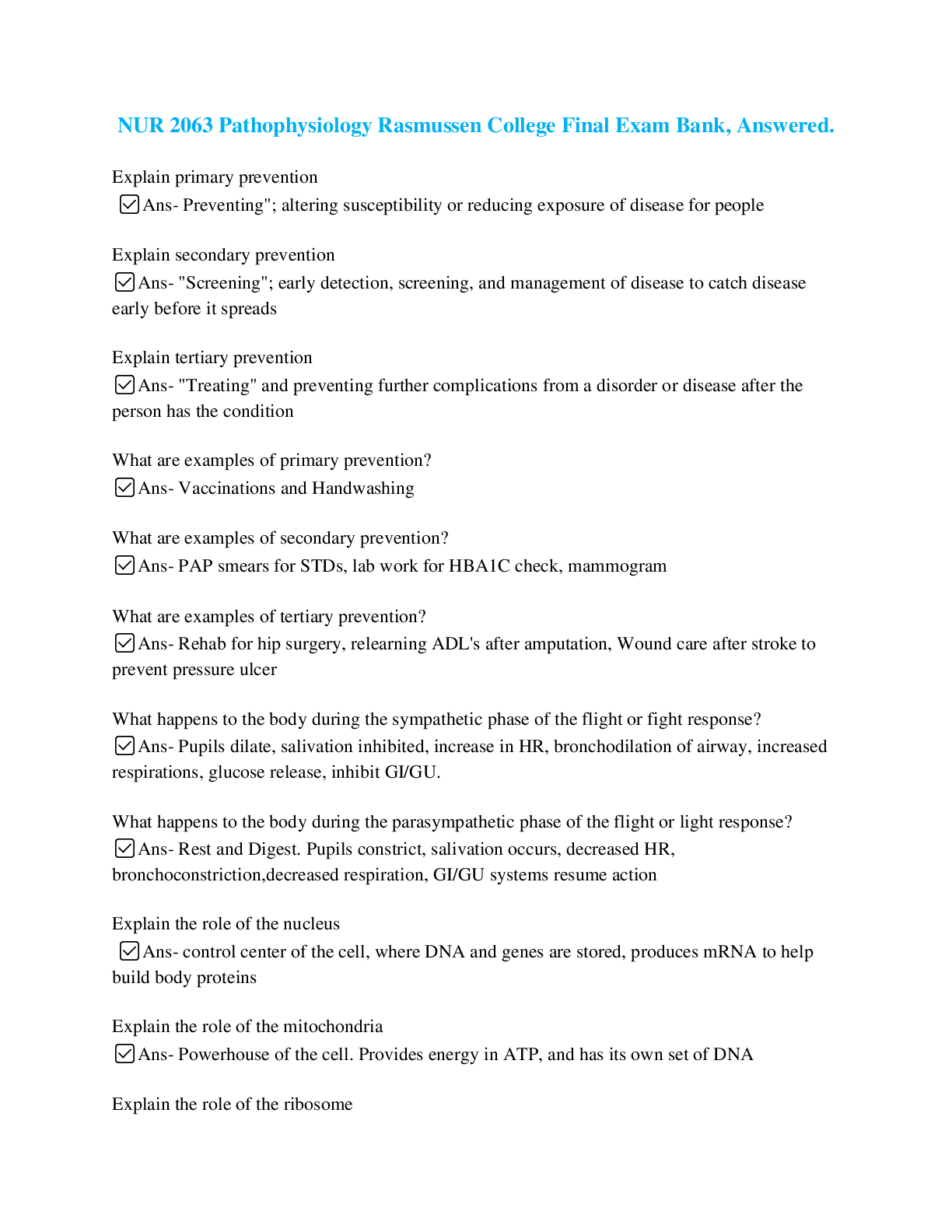

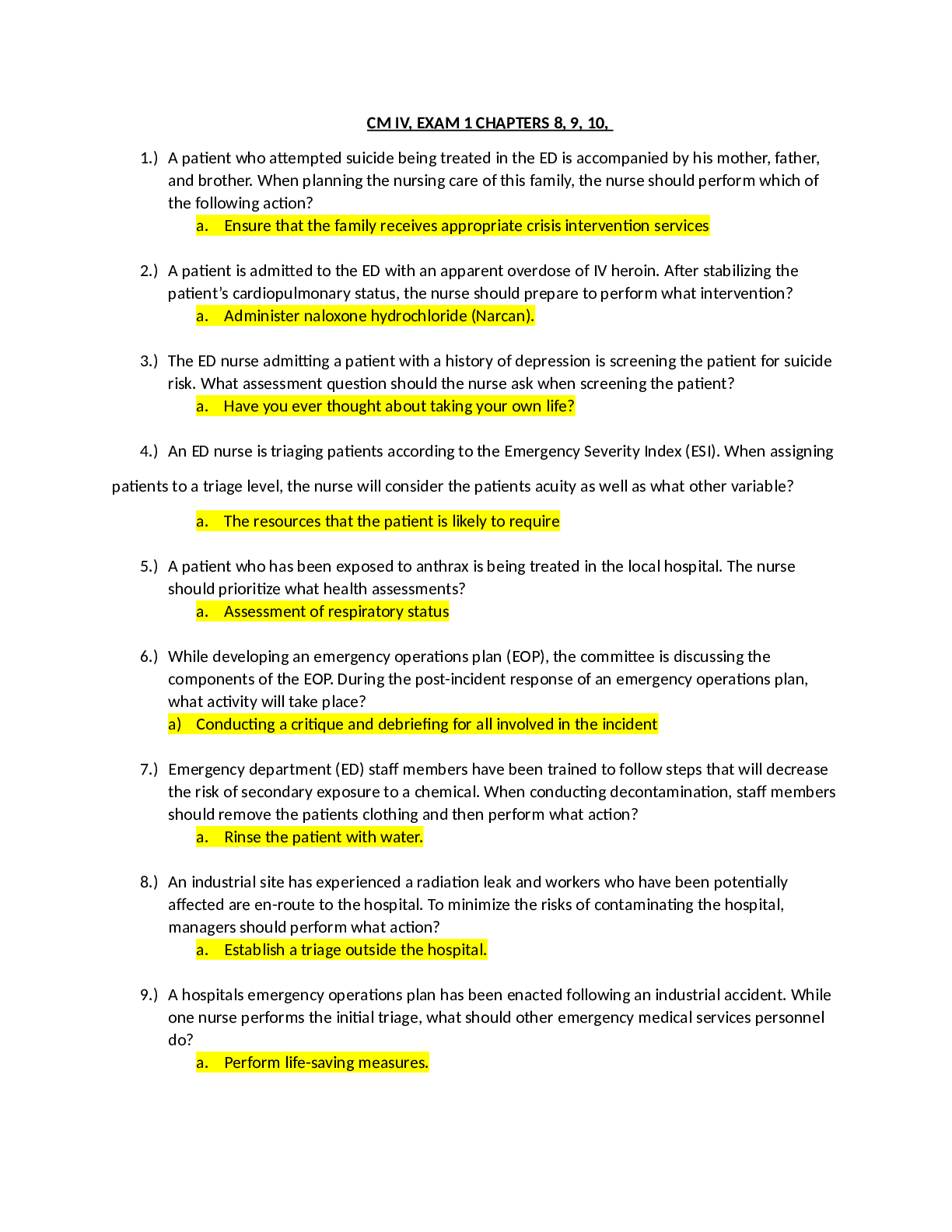
.png)

