Computer Science > Research Paper > University of Maryland, University College CYB 670 Attack Vector and Attribution Analysis CYB670 Cap (All)
University of Maryland, University College CYB 670 Attack Vector and Attribution Analysis CYB670 Capstone in Cybersecurity. Team Canada
Document Content and Description Below
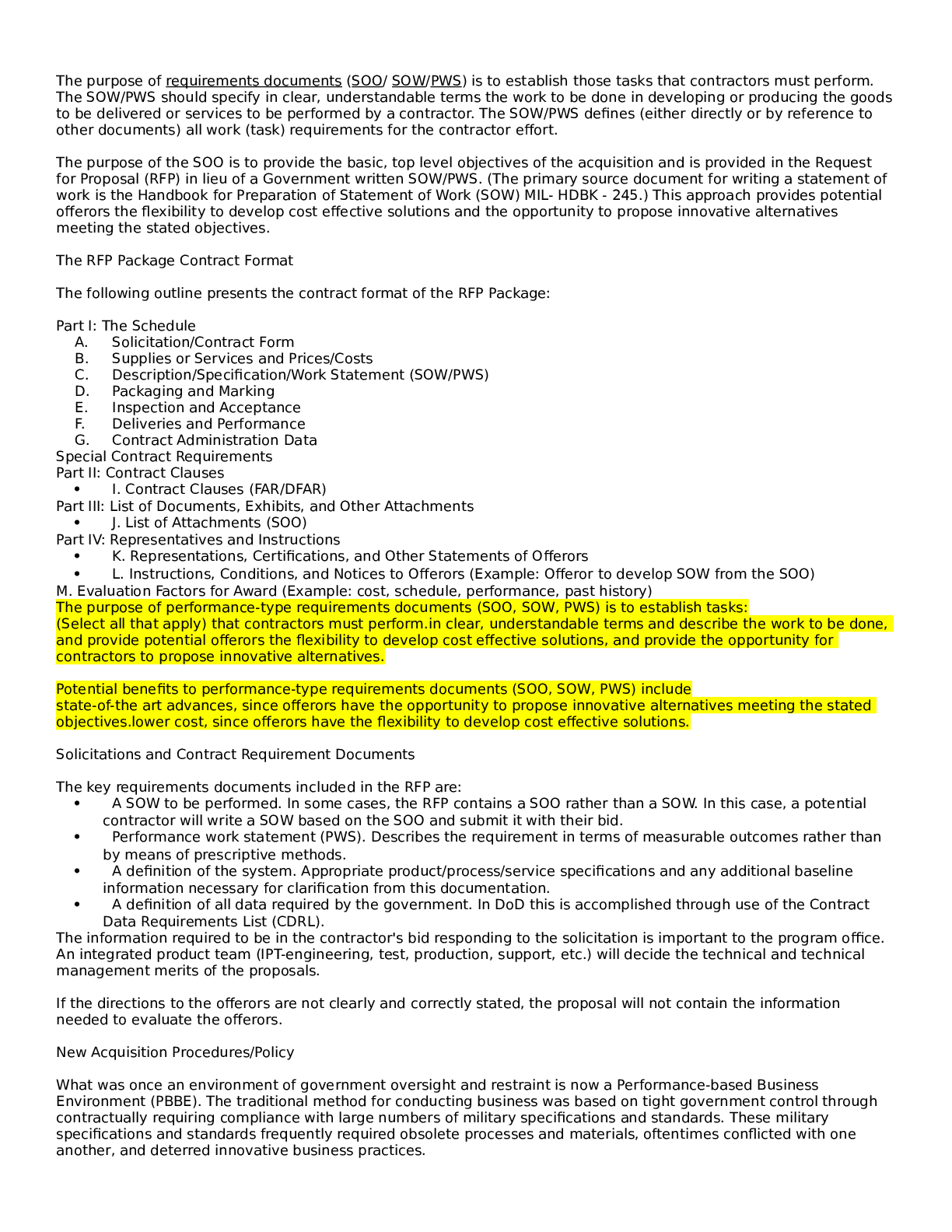
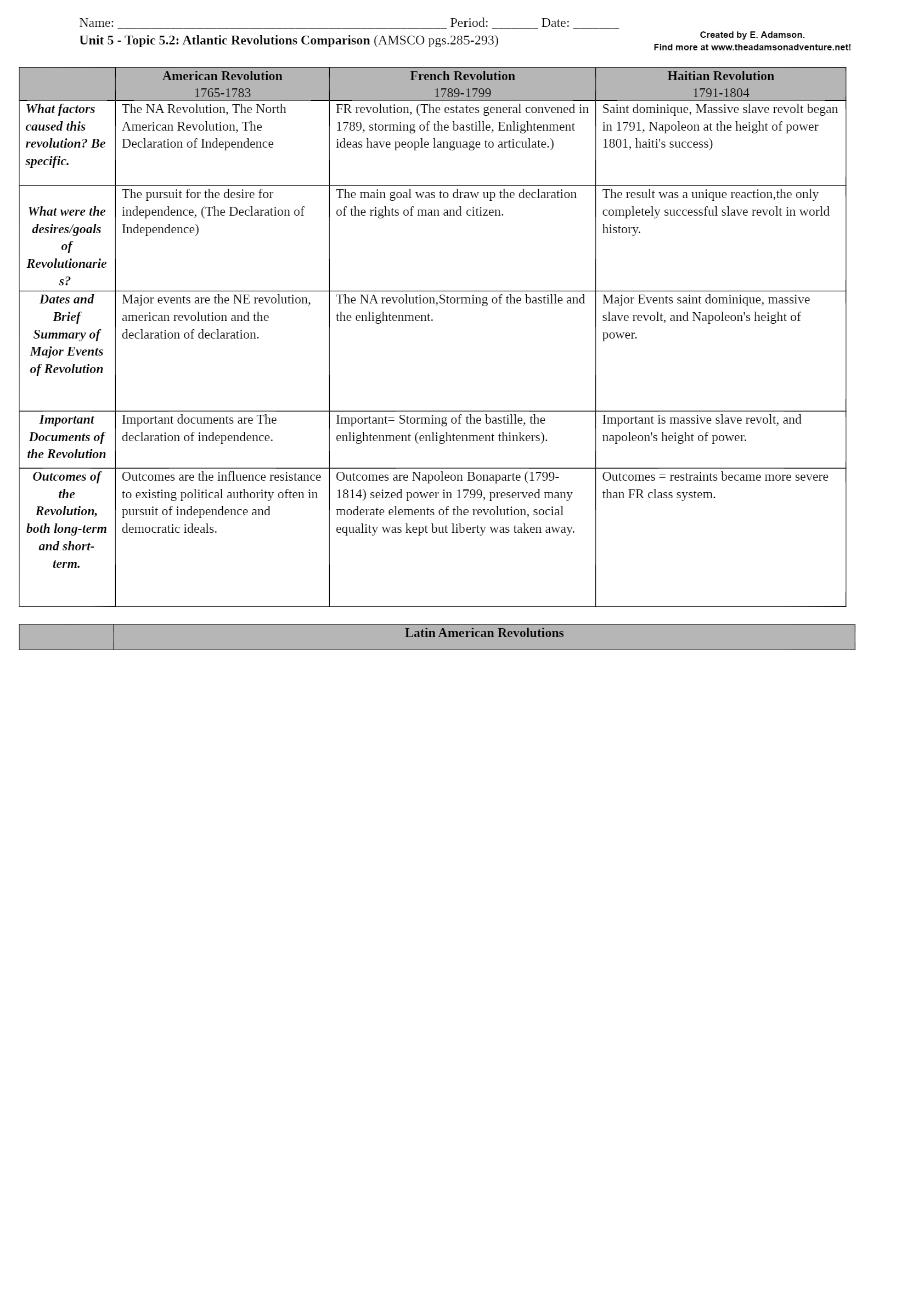
University of Maryland, University College CYB 670 Attack Vector and Attribution Analysis CYB670 Capstone in Cybersecurity Table of Contents Introduction........3 Attack Vectors3 Hardwa... re........3 Software4 Operating System (OS)....5 Human Factors........5 Telecommunications........6 Attribution......7 Conclusion.....8 References.9 Introduction Malicious actors use various procedures and techniques to infiltrate into a network. Most component that make up the information technology infrastructure of an organization may be targeted by malicious actors. Attack vectors are not limited to hardware and software; telecommunication equipment and humans are often targeted. The operating system (OS) is another attack vector that is targeted and may have devastating effects. This report aims to analyze attack vectors and attribution of the same. To do this, an understanding of known attack vectors is key to patch weaknesses and vulnerabilities. Attack Vectors Attack vectors exist in computers systems. According to UMUC, “Attack vectors are paths by which malicious actors gain unauthorized access to a computer system or data (UMUC, n.d.). These paths are targeted by malicious actors to find weaknesses and gain access to the system. It is important for an organization to identify weaknesses and vulnerabilities to remedy them before they are exploited. Cybercriminals will attack their victims by targeting hardware, software, OSs, telecommunications, and human factors. Securing hardware is often overlooked giving malicious actors an area to exploit. Hardware Computing hardware is all around and ever evolving. We become more and more dependent on the use of electronic devices to do things for us. Cybercriminals know how important our electronic devices are and will find ways to exploit vulnerabilities in hardware for malicious purposes. According to Peganini, attackers will often target hardware by: · Manufacturer backdoors. · Eavesdropping by gaining access to memory without opening other hardware. · Inducing faults. · Modifying hardware with malicious intent. · Creating backdoors to bypass authentication mechanisms. These attacks are targeted at different pieces of hardware. Among them are access control systems, network appliances, industrial control systems, surveillance systems, and communication components (Peganini, 2013). Hardware is not the only thing malicious actors will target; software is another prime target. Software The paths available to carry out an attack via software are immense. Malicious actors can affect a computer system by installing malware, injecting malicious code, hijacking a user’s session, and key logging to name a few. Table 1 lists common attacks, their description, and what the attack does. Table 1. Common Cyber Attacks (Melnick, 2018, and Metivier, 2018) [Show More]
Last updated: 1 year ago
Preview 1 out of 10 pages
Reviews( 0 )
Document information
Connected school, study & course
About the document
Uploaded On
Nov 16, 2022
Number of pages
10
Written in
Additional information
This document has been written for:
Uploaded
Nov 16, 2022
Downloads
0
Views
54