Computer Science > QUESTIONS & ANSWERS > CIST 1601 - Test Bank Complete study guide; A+ work (latest 2019/20) Augusta Technical College. (All)
CIST 1601 - Test Bank Complete study guide; A+ work (latest 2019/20) Augusta Technical College.
Document Content and Description Below
CIST 1601 Test Bank. CompTIA Security + SYO-301 Certification Exam A 1. Actively monitoring data streams in search of malicious code or behavior is an example of: a. load balancing. b. an... Internet proxy. c. URL filtering. d. content inspection. 2. Which of the following network devices would MOST likely be used to detect but not react to suspicious behavior on the network? a. Firewall b. NIDS c. NIPS d. HIDS 3. The security administrator is getting reports from users that they are accessing certain websites and are unable to download anything off of those sites. The security administrator is also receiving several alarms from the IDS about suspicious traffic on the network. Which of the following is the MOST likely cause? a. NIPS is blocking activities from those specific websites. b. NIDS is blocking activities from those specific websites. c. The firewall is blocking web activity. d. The router is denying all traffic from those sites. 4. Which of the following tools provides the ability to determine if an application is transmitting a password in clear-text? a. Protocol analyzer b. Port scanner c. Vulnerability scanner d. Honeypot 5. Which of the following can a security administrator implement to help identify smurf attacks? a. Load balancer b. Spam filters c. NIDS d. Firewall 6. Which of the following functions is MOST likely performed by a web security gateway? a. Protocol analyzer b. Content filtering c. Spam filtering d. Flood guard 7. Which of the following devices is often used to cache and filter content? a. Proxies b. Firewall c. VPN d. Load balancer 8. Which of the following devices is used to optimize and distribute data workloads across multiple computers or networks? a. Load balancer b. URL filter c. VPN concentrator d. Protocol analyzer 9. An IT administrator wants to provide 250 staff with secure remote access to the corporate network. Which of the following BEST achieves this requirement? a. Software based firewall b. Mandatory Access Control (MAC) c. VPN concentrator d. Web security gateway 10. Which of the following should be installed to prevent employees from receiving unsolicited emails? a. Pop-up blockers b. Virus definitions c. Spyware definitions d. Spam filters 11. Which of the following should a security administrator implement to prevent users from disrupting network connectivity, if a user connects both ends of a network cable to different switch ports? a. VLAN separation b. Access control c. Loop protection d. DMZ 12. A user is no longer able to transfer files to the FTP server. The security administrator has verified the ports are open on the network firewall. Which of the following should the security administrator check? a. Anti-virus software b. ACLs c. Anti-spam software d. NIDS 13. Which of the following BEST describes the proper method and reason to implement port security? a. Apply a security control which ties specific ports to end-device MAC addresses and prevents additional devices from being connected to the network. b. Apply a security control which ties specific networks to end-device IP addresses and prevents new devices from being connected to the network. c. Apply a security control which ties specific ports to end-device MAC addresses and prevents all devices from being connected to the network. d. Apply a security control which ties specific ports to end-device IP addresses and prevents mobile devices from being connected to the network. 14. Which of the following would need to be configured correctly to allow remote access to the network? a. ACLs b. Kerberos c. Tokens d. Biometrics 15. By default, which of the following stops network traffic when the traffic is not identified in the firewall ruleset? a. Access control lists b. Explicit allow c. Explicit deny d. Implicit deny 16. Based on logs from file servers, remote access systems, and IDS, a malicious insider was stealing data using a personal laptop while connected by VPN. The affected company wants access to the laptop to determine lossut the insider's lawyer insists the laptop cannot be identified. Which of the following would BEST be used to identify the specific computer used by the insider? a. IP address b. User profiles c. MAC address d. Computer name 17. Applying detailed instructions to manage the flow of network traffic at the edge of the network, including allowing or denying traffic based on port, protocol, address, or direction is an implementation of which of the following? a. Virtualization b. Port security c. IPSec d. Firewall rules 18. Which of the following is the default rule found in a corporate firewall's access control list? a. Anti-spoofing b. Permit all c. Multicast list d. Deny all 19. Which of the following is BEST used to prevent ARP poisoning attacks across a network? a. VLAN segregation b. IPSec c. IP filters d. Log analysis 20. A small company needs to invest in a new expensive database. The company's budget does not include the purchase of additional servers or personnel. Which of the following solutions would allow the small company to save money on hiring additional personnel and minimize the footprint in their current datacenter? a. Allow users to telecommute b. Setup a load balancer c. Infrastructure as a Service d. Software as a Service 21. Which of the following is MOST likely to be the last rule contained on any firewall? a. IP allow any any b. Implicit deny c. Separation of duties d. Time of day restrictions 22. Which of the following cloud computing concepts is BEST described as providing an easy-to- configure OS and on-demand computing for customers? a. Platform as a Service b. Software as a Service c. Infrastructure as a Service d. Trusted OS as a Service 23. MAC filtering is a form of which of the following? a. Virtualization b. Network Access Control c. Virtual Private Networking d. Network Address Translation 24. Reviewing an access control list on a firewall reveals a Drop All statement at the end of the rules. Which of the following describes this form of access control? a. Discretionary b. Time of day restrictions c. Implicit deny d. Mandatory 25. An administrator is taking an image of a server and converting it to a virtual instance. Which of the following BEST describes the information security requirements of a virtualized server? a. Virtual servers require OS hardening but not patching or antivirus. b. Virtual servers have the same information security requirements as physical servers. c. Virtual servers inherit information security controls from the hypervisor. d. Virtual servers only require data security controls and do not require licenses. 26. Webmail is classified under which of the following cloud-based technologies? a. Demand Computing b. Infrastructure as a Service (IaaS) c. Software as a Service (SaaS) d. Platform as a Service (PaaS) 27. A security engineer is troubleshooting a server in the DMZ, which cannot be reached from the Internet or the internal network. All other servers on the DMZ are able to communicate with this server. Which of the following is the MOST likely cause? a. The server is configured to reject ICMP packets. b. The server is on the external zone and it is configured for DNS only. c. The server is missing the default gateway. d. The server is on the internal zone and it is configured for DHCP only. 28. Which of the following may cause a useronnected to a NAC-enabled network, to not be prompted for credentials? a. The user's PC is missing the authentication agent. b. The user's PC is not fully patched. c. The user's PC is not at the latest service pack. d. The user's PC has out-of-date antivirus software. 29. Which of the following would be implemented to allow access to services while segmenting access to the internal network? a. IPSec b. VPN c. NAT d. DMZ 30. A security administrator needs to separate two departments. Which of the following would the administrator implement to perform this? a. Cloud computing b. VLAN c. Load balancer d. MAC filtering 31. Which of the following is a security control that is lost when using cloud computing? a. Logical control of the data b. Access to the application's administrative settings c. Administrative access to the data d. Physical control of the data 32. Which of the following protocols should be blocked at the network perimeter to prevent host enumeration by sweep devices? a. HTTPS b. SSH c. IPv4 d. ICMP 33. Which of the following uses TCP port 22 by default? a. SSL, SCP, and TFTP b. SSH, SCP, and SFTP c. HTTPS, SFTP, and TFTP d. TLS, TELNET, and SCP 34. Which of the following allows a security administrator to set device traps? a. SNMP b. TLS c. ICMP d. SSH 35. A security administrator needs to implement a site-to-site VPN tunnel between the main office and a remote branch. Which of the following protocols should be used for the tunnel? a. RTP b. SNMP c. IPSec d. 802.1X 36. Which of the following protocols would be the MOST secure method to transfer files from a host machine? a. SFTP b. WEP c. TFTP d. FTP 37. Which of the following port numbers is used for SCPy default? a. 22 b. 69 c. 80 d. 443 38. Which of the following is the MOST secure method of utilizing FTP? a. FTP active b. FTP passive c. SCP d. FTPS 39. Which of the following protocols can be implemented to monitor network devices? a. IPSec b. FTPS c. SFTP d. SNMP 40. Which of the following protocols would an administrator MOST likely use to monitor the parameters of network devices? a. SNMP b. NetBIOS c. ICMP d. SMTP 41. A remote office is reporting they are unable to access any of the network resources from the main office. The security administrator realizes the error and corrects it. The administrator then tries to ping the router at the remote office and receives no reply; however, the technician is able to telnet to that router. Which of the following is the MOST likely cause of the security administrator being unable to ping the router? a. The remote switch is turned off. b. The remote router has ICMP blocked. c. The remote router has IPSec blocked. d. The main office's router has ICMP blocked. 42. A network administrator is implementing a network addressing scheme that uses a long string of both numbers and alphanumeric characters to create addressing options and avoid duplicates. Which of the following describes a protocol built for this purpose? a. IPv6 b. ICMP c. IGMP d. IPv4 43. In which of the following locations would a forensic analyst look to find a hooked process? a. BIOS b. Slack space c. RAM d. Rootkit 44. Which of the following file transfer protocols is an extension of SSH? a. FTP b. TFTP c. SFTP d. FTPS 45. Which of the following secure protocols is MOST commonly used to remotely administer Unix/Linux systems? a. SSH b. SCP c. SFTP d. SNMP 46. The security administrator notices a number of TCP connections from the development department to the test network segregation. Large volumes of data are being transmitted between the two networks only on port 22. Which of the following is MOST likely occurring? a. The development team is transferring data to test systems using FTP and TFTP. b. The development team is transferring data to test systems using SCP and TELNET. c. The development team is transferring data to test systems using SFTP and SCP. d. The development team is transferring data to test systems using SSL and SFTP. 47. An administrator who wishes to block all database ports at the firewall should include which of the following ports in the block list? a. 445 b. 1433 c. 1501 d. 3389 48. If a security administrator wants to TELNET into a router to make configuration changes, which of the following ports would need to be open by default? a. 23 b. 135 c. 161 d. 3389 49. Which of the following wireless security controls can be easily and quickly circumvented using only a network sniffer? (Select TWO). a. MAC filtering b. Disabled SSID broadcast c. WPA2-Enterprise d. EAP-TLS e. WEP with 802.1x 50. In order to provide flexible working conditions, a company has decided to allow some employees remote access into corporate headquarters. Which of the following security technologies could be used to provide remote access? (Select TWO). a. Subnetting b. NAT c. Firewall d. NAC e. VPN Exam B 1. Which of the following ports would a security administrator block if the administrator wanted to stop users from accessing outside SMTP services? a. 21 b. 25 c. 110 d. 143 PTS: 1 2. A network consists of various remote sites that connect back to two main locations. The security administrator needs to block TELNET access into the network. Which of the followingy default, would be the BEST choice to accomplish this goal? a. Block port 23 on the L2 switch at each remote site. b. Block port 23 on the network firewall. c. Block port 25 on the L2 switch at each remote site. d. Block port 25 on the network firewall. PTS: 1 3. In an 802.11n network, which of the following provides the MOST secure method of both encryption and authorization? a. WEP with 802.1x b. WPA Enterprise c. WPA2-PSK d. WPA with TKIP PTS: 1 4. Isolation mode on an AP provides which of the following functionality types? a. Segmentation of each wireless user from other wireless users. b. Disallows all users from communicating directly with the AP. c. Hides the service set identifier. d. Makes the router invisible to other routers. PTS: 1 5. Which of the following is the BEST choice for encryption on a wireless network? a. WPA2-PSK b. AES c. WPA d. WEP PTS: 1 6. A user reports that their 802.11n capable interface connects and disconnects frequently to an access point that was recently installed. The user has a Bluetooth enabled laptop. A company in the next building had their wireless network breached last month. Which of the following is MOST likely causing the disconnections? a. An attacker inside the company is performing a bluejacking attack on the user's laptop. b. Another user's Bluetooth device is causing interference with the Bluetooth on the laptop. c. The new access point was mis-configured and is interfering with another nearby access point. d. The attacker that breached the nearby company is in the parking lot implementing a war driving attack. PTS: 1 7. Which of the following should the security administrator look at FIRST when implementing an AP to gain more coverage? a. Encryption methods b. Power levels c. SSID d. Radio frequency PTS: 1 8. Which of the following protocols requires the use of a CA based authentication process? a. FTPS implicit b. FTPS explicit c. MD5 d. PEAP-TLS PTS: 1 9. When configuring multiple computers for RDP on the same wireless router, it may be necessary to do which of the following? a. Forward to different RDP listening ports. b. Turn off port forwarding for each computer. c. Enable DMZ for each computer. d. Enable AP isolation on the router. PTS: 1 10. A technician needs to limit the wireless signal from reaching outside of a building. Which of the following actions should the technician take? a. Disable the SSID broadcast on the WAP. b. Place the WAP antenna on the exterior wall of the building. c. Decrease the power levels on the WAP. d. Enable MAC filtering in the WAP. PTS: 1 11. Which of the following will provide the HIGHEST level of wireless network security? a. WPA2 b. SSH c. SSID d. WEP PTS: 1 12. Which of the following facilitates computing for heavily utilized systems and networks? a. Remote access b. Provider cloud c. VPN concentrator d. Telephony PTS: 1 13. Risk can be managed in the following ways EXCEPT: a. mitigation. b. acceptance. c. elimination. d. transference. PTS: 1 14. A company that purchases insurance to reduce risk is an example of which of the following? a. Risk deterrence b. Risk acceptance c. Risk avoidance d. Risk transference PTS: 1 15. Which of the following is a best practice to identify fraud from an employee in a sensitive position? a. Acceptable usage policy b. Separation of duties c. False positives d. Mandatory vacations PTS: 1 16. A security administrator with full administrative rights on the network is forced to temporarily take time off of their duties. Which of the following describes this form of access control? a. Separation of duties b. Discretionary c. Mandatory vacation d. Least privilege PTS: 1 17. Instead of giving a security administrator full administrative rights on the network, the administrator is given rights only to review logs and update security related network devices. Additional rights are handed out to network administrators for the areas that fall within their job description. Which of the following describes this form of access control? a. Mandatory vacation b. Least privilege c. Discretionary d. Job rotation PTS: 1 18. A security administrator wants to determine what data is allowed to be collected from users of the corporate Internet-facing web application. Which of the following should be referenced? a. Privacy policy b. Human Resources policy c. Appropriate use policy d. Security policy PTS: 1 19. An administrator is updating firmware on routers throughout the company. Where should the administrator document this work? a. Event Viewer b. Router's System Log c. Change Management System d. Compliance Review System PTS: 1 20. Due to sensitive data concerns, a security administrator has enacted a policy preventing the use of flash drives. Additionally, which of the following can the administrator implement to reduce the risk of data leakage? a. Enact a policy that all work files are to be password protected. b. Enact a policy banning users from bringing in personal music devices. c. Provide users with unencrypted storage devices that remain on-site. d. Disallow users from saving data to any network share. PTS: 1 21. Performing routine security audits is a form of which of the following controls? a. Preventive b. Detective c. Protective d. Proactive PTS: 1 22. Which of the following is MOST commonly a part of routine system audits? a. Job rotation b. Business impact analysis c. User rights and permissions reviews d. Penetration testing PTS: 1 23. Which of the following is a method to prevent ad-hoc configuration mistakes? a. Implement an auditing strategy b. Implement an incident management strategy c. Implement a patch management strategy d. Implement a change management strategy PTS: 1 24. Which of the following should be reviewed periodically to ensure a server maintains the correct security configuration? a. NIDS configuration b. Firewall logs c. User rights d. Incident management PTS: 1 25. A security administrator finished taking a forensic image of a computer's memory. Which of the following should the administrator do to ensure image integrity? a. Run the image through AES128. b. Run the image through a symmetric encryption algorithm. c. Compress the image to a password protected archive. d. Run the image through SHA256. PTS: 1 26. Which of the following BEST explains the security benefit of a standardized server image? a. All current security updates for the operating system will have already been applied. b. Mandated security configurations have been made to the operating system. c. Anti-virus software will be installed and current. d. Operating system license use is easier to track. PTS: 1 27. Which of the following describes when forensic hashing should occur on a drive? a. After the imaging process and before the forensic image is captured. b. Before the imaging process and then after the forensic image is created. c. After the imaging process and after the forensic image is captured. d. Before and after the imaging process and then hash the forensic image. PTS: 1 28. Which of the following assists in identifying if a system was properly handled during transport? a. Take a device system image b. Review network traffic and logs c. Track man hours and incident expense d. Chain of custody PTS: 1 29. Which of the following describes the purpose of chain of custody as applied to forensic image retention? a. To provide proof the evidence has not been tampered with or modified. b. To provide verification that the forensic examiner is qualified. c. To provide documentation as to who has handled the evidence. d. To provide a baseline reference. PTS: 1 30. Which of the following is a policy that would force all users to organize their areas as well as help in reducing the risk of possible data theft? a. Password behaviors b. Clean desk policy c. Data handling d. Data disposal PTS: 1 31. Which of the following will educate employees about malicious attempts from an attacker to obtain bank account information? a. Password complexity requirements b. Phishing techniques c. Handling PII d. Tailgating techniques PTS: 1 32. Which of the following is a reason to perform user awareness and training? a. To enforce physical security requirements by staff b. To minimize the organizational risk posed by users c. To comply with law and vendor software best practices d. To identify the staff's personally owned electronic devices PTS: 1 33. On-going annual awareness security training should be coupled with: a. succession planning. b. implementation of security controls. c. user rights and permissions review. d. signing of a user agreement. PTS: 1 34. Which of the following risks may result from improper use of social networking and P2P software? a. Shoulder surfing b. Denial of service c. Information disclosure d. Data loss prevention PTS: 1 35. Which of the following is the MAIN reason to require data labeling? a. To ensure that staff understands what data they are handling and processing. b. To ensure that new viruses do not transfer to removable media. c. To ensure that all media sanitization requirements are met. d. To ensure that phishing attacks are identified and labeled properly. PTS: 1 36. DRPs should contain which of the following? a. Hierarchical list of non-critical personnel b. Hierarchical list of critical systems c. Hierarchical access control lists d. Identification of single points of failure PTS: 1 37. Recovery Point Objectives and Recovery Time Objectives directly relate to which of the following BCP concepts? a. Succession planning b. Remove single points of failure c. Risk management d. Business impact analysis PTS: 1 38. A security firm has been engaged to assess a software application. A production-like test environment, login details, production documentation and source code have been provided. Which of the following types of testing is being described? a. White box b. Gray box c. Black box d. Red teaming PTS: 1 39. Which of the following environmental controls would BEST be used to regulate cooling within a datacenter? a. Fire suppression b. Video monitoring c. EMI shielding d. Hot and cold aisles PTS: 1 40. Which of the following environmental variables reduces the potential for static discharges? a. EMI b. Temperature c. UPS d. Humidity PTS: 1 41. Which of the following should be considered when trying to prevent somebody from capturing network traffic? a. Video monitoring b. Hot aisles c. HVAC controls d. EMI shielding PTS: 1 42. With which of the following is RAID MOST concerned? a. Integrity b. Confidentiality c. Availability d. Baselining PTS: 1 43. Which of the following reduces the likelihood of a single point of failure when a server fails? a. Clustering b. Virtualization c. RAID d. Cold site PTS: 1 44. Which of the following is the BEST way to secure data for the purpose of retention? a. Off-site backup b. RAID 5 on-site backup c. On-site clustering d. Virtualization PTS: 1 45. A security administrator is in charge of a datacenter, a hot site and a cold site. Due to a recent disaster, the administrator needs to ensure that their cold site is ready to go in case of a disaster. Which of the following does the administrator need to ensure is in place for a cold site? a. Location with all required equipment loaded with all current patches and updates. b. Location with duplicate systems found in the datacenter. c. Location near the datacenter that meets power requirements. d. Location that meets power and connectivity requirements. PTS: 1 46. A critical system in the datacenter is not connected to a UPS. The security administrator has coordinated an authorized service interruption to resolve this issue. This is an example of which of the following? a. Fault tolerance b. Continuity of operations c. Succession planning d. Data handling error PTS: 1 47. In order to ensure high availability of all critical serversackups of the main datacenter are done in the middle of the night and then the backup tapes are taken to an offsite location. Which of the following would ensure the minimal amount of downtime in the case of a disaster? a. Having the offsite location of tapes also be the standby server. b. Having the offsite location of tapes also be the warm site. c. Having the offsite location of tapes also be the cold site. d. Having the offsite location of tapes also be the hot site. PTS: 1 48. Which of the following are the default ports for HTTP and HTTPS protocols? (Select TWO). a. 21 b. 80 c. 135 d. 443 e. 445 PTS: 1 49. Used in conjunction, which of the following are PII? (Select TWO). a. Marital status b. Favorite movie c. Pet's name d. Birthday e. Full name PTS: 1 50. A security administrator is tasked with ensuring that all servers are highly available and that hard drive failure will not affect an individual server. Which of the following configurations will allow for high availability? (Select TWO). a. Hardware RAID 5 b. Load sharing c. Server clustering d. Software RAID 1 e. Load balancing PTS: 1 Exam C 1. Which of the following concepts ensures that the data is only viewable to authorized users? a. Availability b. Biometrics c. Integrity d. Confidentiality PTS: 1 2. A bulk update process fails and writes incorrect data throughout the database. Which of the following concepts describes what has been compromised? a. Authenticity b. Integrity c. Availability d. Confidentiality PTS: 1 3. While browsing the Internet, an administrator notices their browser behaves erratically, appears to download something, and then crashes. Upon restarting the PC, the administrator notices performance is extremely slow and there are hundreds of outbound connections to various websites. Which of the following BEST describes what has occurred? a. The PC has become part of a botnet. b. The PC has become infected with spyware. c. The PC has become a spam host. d. The PC has become infected with adware. PTS: 1 4. Which of the following is the primary difference between a virus and a worm? a. A worm is undetectable b. A virus is typically larger c. A virus is easily removed d. A worm is self-replicating PTS: 1 5. A user downloads a keygen to install pirated software. After running the keygen, system performance is extremely slow and numerous antivirus alerts are displayed. Which of the following BEST describes this type of malware? a. Logic bomb b. Worm c. Trojan d. Adware PTS: 1 6. Logs from an IDS show that a computer has been compromised with a botnet and is actively communicating with a command and control server. If the computer is powered off, which of the following data types will be unavailable for later investigation? a. Swap files, system processes, and master boot record b. Memory, temporary file system, and archival storage c. System diskmail, and log files d. Memory, network processes, and system processes PTS: 1 7. Upon investigation, an administrator finds a suspicious system-level kernel module which modifies file system operations. This is an example of which of the following? a. Trojan b. Virus c. Logic bomb d. Rootkit PTS: 1 8. Which of the following is the MOST likely cause of a single computer communicating with an unknown IRC server and scanning other systems on the network? a. Worm b. Spyware c. Botnet d. Rootkit PTS: 1 9. Which of the following malware types is MOST commonly installed through the use of thumb drives to compromise systems and provide unauthorized access? a. Trojans b. Botnets c. Adware d. Logic bomb PTS: 1 10. A system administrator could have a user level account and an administrator account to prevent: a. password sharing. b. escalation of privileges. c. implicit deny. d. administrative account lockout. PTS: 1 11. When examining HTTP server logs the security administrator notices that the company's online store crashes after a particular search string is executed by a single external user. Which of the following BEST describes this type of attack? a. Spim b. DDoS c. Spoofing d. DoS PTS: 1 12. Which of the following would allow traffic to be redirected through a malicious machine by sending false hardware address updates to a switch? a. ARP poisoning b. MAC spoofing c. pWWN spoofing d. DNS poisoning PTS: 1 13. Which of the following threats corresponds with an attacker targeting specific employees of a company? a. Spear phishing b. Phishing c. Pharming d. Man-in-the-middle PTS: 1 14. A user receives an automated call which appears to be from their bank. The automated recording provides details about the bank's privacy policy, security policy and requests that the user clearly state their nameirthday and enter the banking details to validate the user's identity. Which of the following BEST describes this type of attack? a. Phishing b. Spoofing c. Vishing d. Pharming PTS: 1 15. Which of the following is a technique designed to obtain information from a specific person? a. Smurf attack b. Spear phishing c. DNS poisoning d. Pharming PTS: 1 16. Which of the following is another name for a malicious attacker? a. Black hat b. White hat c. Penetration tester d. Fuzzer PTS: 1 17. Which of the following logical controls does a flood guard protect against? a. Spanning tree b. Xmas attacks c. Botnet attack d. SYN attacks PTS: 1 18. Which of the following attacks is BEST described as the interruption of network traffic accompanied by the insertion of malicious code? a. Spoofing b. Man-in-the-middle c. Spear phishing d. DoS PTS: 1 19. A targeted email attack sent to the company's Chief Executive Officer (CEO) is known as which of the following? a. Whaling b. Bluesnarfing c. Vishing d. Dumpster diving PTS: 1 20. Which of the following security threats does shredding mitigate? a. Shoulder surfing b. Document retention c. Tailgating d. Dumpster diving PTS: 1 21. Which of the following attacks would password masking help mitigate? a. Shoulder surfing b. Brute force c. Tailgating d. Impersonation PTS: 1 22. Which of the following is an example of allowing another user physical access to a secured area without validation of their credentials? a. Evil twin b. Tailgating c. Impersonation d. Shoulder surfing PTS: 1 23. Which of the following is specific to a buffer overflow attack? a. Memory addressing b. Directory traversal c. Initial vector d. Session cookies PTS: 1 24. Which of the following wireless attacks uses a counterfeit base station with the same SSID name as a nearby intended wireless network? a. War driving b. Evil twin c. Rogue access point d. War chalking PTS: 1 25. Data can potentially be stolen from a disk encrypted, screen-lock protected, smartphone by which of the following? a. Bluesnarfing b. IV attack c. Honeynet d. SIM cloning PTS: 1 26. Which of the following is an unauthorized wireless router that allows access to a secure network? a. Interference b. War driving c. Evil twin d. Rogue access point PTS: 1 27. A security administrator performs several war driving routes each month and recently has noticed a certain area with a large number of unauthorized devices. Which of the following attack types is MOST likely occurring? a. Interference b. Rogue access points c. IV attack d. Bluejacking PTS: 1 28. Proper wireless antenna placement and radio power setting reduces the success of which of the following reconnaissance methods? a. Rogue APs b. War driving c. Packet analysis d. RF interference PTS: 1 29. A rogue access point with the same SSID as the production wireless network is found. Which of the following BEST describes this attack? a. Evil twin b. Vishing c. War driving d. Bluesnarfing PTS: 1 30. A programmer allocates 16 bytes for a string variableut does not adequately ensure that more than 16 bytes cannot be copied into the variable. This program may be vulnerable to which of the following attacks? a. Buffer overflow b. Cross-site scripting c. Session hijacking d. Directory traversal PTS: 1 31. Which of the following MUST a programmer implement to prevent cross-site scripting? a. Validate input to remove shell scripts b. Validate input to remove hypertext c. Validate input to remove batch files d. Validate input to remove Java bit code PTS: 1 32. Which of the following web application security weaknesses can be mitigated by preventing the use of HTML tags? a. LDAP injection b. SQL injection c. Error and exception handling d. Cross-site scripting PTS: 1 33. During the analysis of malicious code, a security analyst discovers JavaScript being used to send random data to another service on the same system. This is MOST likely an example of which of the following? a. Buffer overflow b. XML injection c. SQL injection d. Distributed denial of service PTS: 1 34. Which of the following attacks is manifested as an embedded HTML image object or JavaScript image tag in an email? a. Exception handling b. Adware c. Cross-site request forgery d. Cross-site scripting PTS: 1 35. A web application has been found to be vulnerable to a SQL injection attack. Which of the following BEST describes the required remediation action? a. Change the server's SSL key and add the previous key to the CRL. b. Install a host-based firewall. c. Install missing security updates for the operating system. d. Add input validation to forms. PTS: 1 36. An application log shows that the text "test; rm -rf /etc/passwd" was entered into an HTML form. Which of the following describes the type of attack that was attempted? a. Session hijacking b. Command injection c. Buffer overflow d. SQL injection PTS: 1 37. Which of the following is MOST relevant to a buffer overflow attack? a. Sequence numbers b. Set flags c. IV length d. NOOP instructions PTS: 1 38. The detection of a NOOP sled is an indication of which of the following attacks? a. SQL injection b. Buffer overflow c. Cross-site scripting d. Directory transversal PTS: 1 39. Which of the following devices BEST allows a security administrator to identify malicious activity after it has occurred? a. Spam filter b. IDS c. Firewall d. Malware inspection PTS: 1 40. Which of the following should be enabled to ensure only certain wireless clients can access the network? a. DHCP b. SSID broadcast c. MAC filtering d. AP isolation PTS: 1 41. Which of the following BEST describes an intrusion prevention system? a. A system that stops an attack in progress. b. A system that allows an attack to be identified. c. A system that logs the attack for later analysis. d. A system that serves as a honeypot. PTS: 1 42. Which of the following is a best practice when securing a switch from physical access? a. Disable unnecessary accounts b. Print baseline configuration c. Enable access lists d. Disable unused ports PTS: 1 43. Two systems are being designed. System A has a high availability requirement. System B has a high security requirement with less emphasis on system uptime. Which of the following configurations BEST fits the need for each system? a. System A fails open. System B fails closed. b. System A and System B both fail closed. c. System A and System B both fail open. d. System A fails closed. System B fails open. PTS: 1 44. Several staff members working in a datacenter have reported instances of tailgating. Which of the following could be implemented to prevent this security concern? a. Proximity readers b. Mantraps c. Video surveillance d. Biometric keypad PTS: 1 45. A visitor plugs their laptop into the network and receives a warning about their antivirus being out- of-date along with various patches that are missing. The visitor is unable to access the Internet or any network resources. Which of the following is the MOST likely cause? a. The IDS detected that the visitor's laptop did not have the right patches and updates so the IDS blocked access to the network. b. The security posture is disabled on the network but remediation must take place before access is given to the visitor on that laptop. c. The security posture is enabled on the network and remediation must take place before access is given to the visitor on that laptop. d. The IPS detected that the visitor's laptop did not have the right patches and updates so it prevented its access to the network. PTS: 1 46. Which of the following is a detective security control? a. CCTV b. Firewall c. Design reviews d. Bollards PTS: 1 47. A security administrator working for a health insurance company needs to protect customer data by installing an HVAC system and a mantrap in the datacenter. Which of the following are being addressed? (Select TWO). a. Integrity b. Recovery c. Clustering d. Confidentiality e. Availability PTS: 1 48. Which of the following malware types is an antivirus scanner MOST unlikely to discover? (Select TWO). a. Trojan b. Pharming c. Worms d. Virus e. Logic bomb PTS: 1 49. The security administrator implemented privacy screens, password protected screen savers, and hired a secure shredding and disposal service. Which of the following attacks is the security administrator trying to mitigate? (Select TWO). a. Whaling b. Dumpster diving c. Shoulder surfing d. Tailgating e. Impersonation PTS: 1 50. Which of the following can prevent an unauthorized employee from entering a datacenter? (Select TWO). a. Failsafe b. Video surveillance c. Bollards d. Security guard e. Proximity reader PTS: 1 Exam D 1. Which of the following identifies some of the running services on a system? a. Determine open ports b. Review baseline reporting c. Review honeypot logs d. Risk calculation PTS: 1 2. A security administrator is tasked with revoking the access of a terminated employee. Which of the following account policies MUST be enacted to ensure the employee no longer has access to the network? a. Account disablement b. Account lockout c. Password recovery d. Password expiration PTS: 1 3. A company needs to be able to prevent entry, at all times, to a highly sensitive area inside a public building. In order to ensure the BEST type of physical security, which of the following should be implemented? a. Intercom system b. Video surveillance c. Nightly guards d. Mantrap PTS: 1 4. Which of the following would provide the MOST reliable proof that a datacenter was accessed at a certain time of day? a. Video surveillance b. Security log c. Entry log d. Proximity readers PTS: 1 5. Users of specific systems are reporting that their data has been corrupted. After a recent patch update to those systems, the users are still reporting issues of data being corrupt. Which of the following assessment techniques need to be performed to identify the issue? a. Hardware baseline review b. Vulnerability scan c. Data integrity check d. Penetration testing PTS: 1 6. Which of the following would be the BEST action to perform when conducting a corporate vulnerability assessment? a. Document scan results for the change control board. b. Organize data based on severity and asset value. c. Examine the vulnerability data using a network analyzer. d. Update antivirus signatures and apply patches. PTS: 1 7. A new enterprise solution is currently being evaluated due to its potential to increase the company's profit margins. The security administrator has been asked to review its security implications. While evaluating the product, various vulnerability scans were performed. It was determined that the product is not a threat but has the potential to introduce additional vulnerabilities. Which of the following assessment types should the security administrator also take into consideration while evaluating this product? a. Threat assessment b. Vulnerability assessment c. Code assessment d. Risk assessment PTS: 1 8. Which of the following is used when performing a qualitative risk analysis? a. Exploit probability b. Judgment c. Threat frequency d. Asset value PTS: 1 9. An administrator identifies a security issue on the corporate web serverut does not attempt to exploit it. Which of the following describes what the administrator has done? a. Vulnerability scan b. Penetration test c. Social engineering d. Risk mitigation PTS: 1 10. Which of the following is used when performing a quantitative risk analysis? a. Focus groups b. Asset value c. Surveys d. Best practice PTS: 1 11. Which of the following describes a passive attempt to identify weaknesses? a. Vulnerability scanning b. Zero day attack c. Port scanning d. Penetration testing PTS: 1 12. An existing application has never been assessed from a security perspective. Which of the following is the BEST assessment technique in order to identify the application's security posture? a. Baseline reporting b. Protocol analysis c. Threat modeling d. Functional testing PTS: 1 13. The server log shows 25 SSH login sessions per hour. However, it is a large company and the administrator does not know if this is normal behavior or if the network is under attack. Where should the administrator look to determine if this is normal behavior? a. Change management b. Code review c. Baseline reporting d. Security policy PTS: 1 14. Upper management decides which risk to mitigate based on cost. This is an example of: a. qualitative risk assessment. b. business impact analysis. c. risk management framework. d. quantitative risk assessment. PTS: 1 15. A security administrator wants to know which systems are more susceptible to an attack compared to other systems on the network. Which of the following assessment tools would be MOST effective? a. Network design review b. Vulnerability scanner c. Baseline review d. Port scanner PTS: 1 16. Which of the following is a management control type? a. Vulnerability scanning b. Least privilege implementation c. Baseline configuration development d. Session locks PTS: 1 17. Which of the following devices would allow a technician to view IP headers on a data packet? a. NIDS b. Protocol analyzer c. VPN switch d. Firewall PTS: 1 18. Which of the following penetration testing types is performed by security professionals with limited inside knowledge of the network? a. Passive vulnerability scan b. Gray box c. White box d. Black box PTS: 1 19. Which of the following is a reason to perform a penetration test? a. To passively test security controls within the enterprise b. To provide training to white hat attackers c. To identify all vulnerabilities and weaknesses within the enterprise d. To determine the impact of a threat against the enterprise PTS: 1 20. Penetration testing should only be used during controlled conditions with express consent of the system owner because: a. white box penetration testing cannot identify zero day exploits. b. vulnerability scanners can cause massive network flooding during risk assessments. c. penetration testing passively tests policy controls and can identify vulnerabilities. d. penetration testing actively tests security controls and can cause system instability. PTS: 1 21. Which of the following security practices should occur initially in software development? a. Secure code review b. Patch management c. Fuzzing d. Penetration tests PTS: 1 22. A penetration test shows that almost all database servers were able to be compromised through a default database user account with the default password. Which of the following is MOST likely missing from the operational procedures? a. Application hardening b. OS hardening c. Application patch management d. SQL injection PTS: 1 23. Which of the following is an example of verifying new software changes on a test system? a. User access control b. Patch management c. Intrusion prevention d. Application hardening PTS: 1 24. Which of the following allows an attacker to identify vulnerabilities within a closed source software application? a. Fuzzing b. Compiling c. Code reviews d. Vulnerability scanning PTS: 1 25. Which of the following would an administrator do to ensure that an application is secure and all unnecessary services are disabled? a. Baselining b. Application hardening c. Secure application coding d. Patch management PTS: 1 26. A security administrator ensures that certain characters and commands entered on a web server are not interpreted as legitimate data and not passed on to backend servers. This is an example of which of the following? a. Error and exception handling b. Input validation c. Determining attack surface d. Data execution prevention PTS: 1 27. A business-critical application will be installed on an Internet facing server. Which of the following is the BEST security control that should be performed in conjunction with updating the application to the MOST current version? a. The firewall should be configured to allow the application to auto-update. b. The firewall should be configured to prevent the application from auto-updating. c. A port scan should be run against the application's server. d. Vendor-provided hardening documentation should be reviewed and applied. PTS: 1 28. Which of the following has a programmer MOST likely failed to consider if a user entering improper input is able to crash a program? a. SDLM b. CRC c. Data formatting d. Error handling PTS: 1 29. Which of the following is the MOST efficient way to combat operating system vulnerabilities? a. Anti-spam b. Locking cabinets c. Screen locks d. Patch management PTS: 1 30. Which of the following is a hardening step of an application during the SDLC? a. Disabling unnecessary accounts b. Application patch management schedule c. Secure coding concepts d. Disabling unnecessary services PTS: 1 31. Which of the following is the BEST way to mitigate data loss if a portable device is compromised? a. Full disk encryption b. Common access card c. Strong password complexity d. Biometric authentication PTS: 1 32. Which of the following should be performed if a smartphone is lost to ensure no data can be retrieved from it? a. Device encryption b. Remote wipe c. Screen lock d. GPS tracking PTS: 1 33. Several classified mobile devices have been stolen. Which of the following would BEST reduce the data leakage threat? a. Use GPS tracking to find the devices. b. Use stronger encryption algorithms. c. Immediately inform local law enforcement. d. Remotely sanitize the devices. PTS: 1 34. Which of the following should be used to help prevent device theft of unused assets? a. HSM device b. Locking cabinet c. Device encryption d. GPS tracking PTS: 1 35. Which of the following devices would be installed on a single computer to prevent intrusion? a. Host intrusion detection b. Network firewall c. Host-based firewall d. VPN concentrator PTS: 1 36. A security administrator has been receiving support tickets for unwanted windows appearing on user's workstations. Which of the following can the administrator implement to help prevent this from happening? a. Pop-up blockers b. Screen locks c. Host-based firewalls d. Antivirus PTS: 1 37. Which of the following would an administrator apply to mobile devices to BEST ensure the confidentiality of data? a. Screen locks b. Device encryption c. Remote sanitization d. Antivirus software PTS: 1 38. Which of the following is a security vulnerability that can be disabled for mobile device users? a. Group policy b. Remote wipe c. GPS tracking d. Pop-up blockers PTS: 1 39. Which of the following software should a security administrator implement if several users are stating that they are receiving unwanted email containing advertisements? a. Host-based firewalls b. Anti-spyware c. Anti-spam d. Anti-virus PTS: 1 40. An employee stores their list of passwords in a spreadsheet on their local desktop hard drive. Which of the following encryption types would protect this information from disclosure if lost or stolen? a. Database b. Removable media c. File and folder level d. Mobile device PTS: 1 41. A company has remote workers with laptops that house sensitive data. Which of the following can be implemented to recover the laptops if they are lost? a. GPS tracking b. Whole disk encryption c. Remote sanitation d. NIDS PTS: 1 42. When decommissioning old hard drives, which of the following is the FIRST thing a security engineer should do? a. Perform bit level erasure or overwrite b. Flash the hard drive firmware c. Format the drive with NTFS d. Use a waste disposal facility PTS: 1 43. Which of the following BEST describes the function of TPM? a. High speed secure removable storage device b. Third party certificate trust authority c. Hardware chip that stores encryption keys d. A trusted OS model PTS: 1 44. Which of the following is MOST likely to result in data loss? a. Accounting transferring confidential staff details via SFTP to the payroll department. b. Back office staff accessing and updating details on the mainframe via SSH. c. Encrypted backup tapes left unattended at reception for offsite storage. d. Developers copying data from production to the test environments via a USB stick. PTS: 1 45. A security administrator is implementing a solution that can integrate with an existing server and provide encryption capabilities. Which of the following would meet this requirement? a. Mobile device encryption b. Full disk encryption c. TPM d. HSM PTS: 1 46. A company needs to reduce the risk of employees emailing confidential data outside of the company. Which of the following describes an applicable security control to mitigate this threat? a. Install a network-based DLP device b. Prevent the use of USB drives c. Implement transport encryption d. Configure the firewall to block port 110 PTS: 1 47. Which of the following should be performed on a computer to protect the operating system from malicious software? (Select TWO). a. Disable unused services b. Update NIDS signatures c. Update HIPS signatures d. Disable DEP settings e. Install a perimeter firewall PTS: 1 48. Which of the following devices provides storage for RSA or asymmetric keys and may assist in user authentication? (Select TWO). a. Trusted platform module b. Hardware security module c. Facial recognition scanner d. Full disk encryption e. Encrypted USB PTS: 1 49. Which of the following is true about hardware encryption? (Select TWO). a. It must use elliptical curve encryption. b. It requires a HSM file system. c. It only works when data is not highly fragmented. d. It is faster than software encryption. e. It is available on computers using TPM. PTS: 1 50. Which of the following are the BEST reasons to use an HSM? (Select TWO). a. Encrypt the CPU L2 cache b. Recover keys c. Generate keys d. Transfer keys to the CPU e. Store keys PTS: 1 Exam E 1. Which of the following can cause hardware based drive encryption to see slower deployment? a. A lack of management software b. USB removable drive encryption c. Role/rule-based access control d. Multifactor authentication with smart cards PTS: 1 2. Which of the following is the MOST secure way of storing keys or digital certificates used for decryption/encryption of SSL sessions? a. Database b. HSM c. Key escrow d. Hard drive PTS: 1 3. Which of the following is a removable device that may be used to encrypt in a high availability clustered environment? a. Cloud computer b. HSM c. Biometrics d. TPM PTS: 1 4. A security administrator is implementing a solution that encrypts an employee's newly purchased laptop but does not require the company to purchase additional hardware or software. Which of the following could be used to meet this requirement? a. Mobile device encryption b. HSM c. TPM d. USB encryption PTS: 1 5. During incident response, which of the following procedures would identify evidence tampering by outside entities? a. Hard drive hashing b. Annualized loss expectancy c. Developing audit logs d. Tracking man hours and incident expenses PTS: 1 6. Which of the following protocols only encrypts password packets from client to server? a. XTACACS b. TACACS c. RADIUS d. TACACS+ PTS: 1 7. Which of the following methods of access, authentication, and authorization is the MOST secure by default? a. Kerberos b. TACACS c. RADIUS d. LDAP PTS: 1 8. Which of the following uses tickets to identify users to the network? a. RADIUS b. LDAP c. TACACS+ d. Kerberos PTS: 1 9. A purpose of LDAP authentication services is: a. to implement mandatory access controls. b. a single point of user management. c. to prevent multifactor authentication. d. to issue one-time hashed passwords. PTS: 1 10. When granting access, which of the following protocols uses multiple-challenge responses for authentication, authorization and audit? a. TACACS b. TACACS+ c. LDAP d. RADIUS PTS: 1 11. A security administrator is setting up a corporate wireless network using WPA2 with CCMP but does not want to use PSK for authentication. Which of the following could be used to support 802.1x authentication? a. LDAP b. RADIUS c. Kerberos d. Smart card PTS: 1 12. Which of the following authentication services would be used to authenticate users trying to access a network device? a. SSH b. SNMPv3 c. TACACS+ d. TELNET PTS: 1 13. Which of the following requires special handling and explicit policies for data retention and data distribution? a. Personally identifiable information b. Phishing attacks c. Zero day exploits d. Personal electronic devices PTS: 1 14. Centrally authenticating multiple systems and applications against a federated user database is an example of: a. smart card. b. common access card. c. single sign-on. d. access control list. PTS: 1 15. A Human Resource manager is assigning access to users in their specific department performing the same job function. This is an example of: a. role-based access control. b. rule-based access control. c. centralized access control. d. mandatory access control. PTS: 1 16. The security administrator often observes that an employee who entered the datacenter does not match the owner of the PIN that was entered into the keypad. Which of the following would BEST prevent this situation? a. Multifactor authentication b. Username and password c. Mandatory access control d. Biometrics PTS: 1 17. Which of the following allows a user to have a one-time password? a. Biometrics b. SSO c. PIV d. Tokens PTS: 1 18. Which of the following is a technical control? a. System security categorization requirement b. Baseline configuration development c. Contingency planning d. Least privilege implementation PTS: 1 19. A thumbprint scanner is used to test which of the following aspects of human authentication? a. Something a user did b. Something a user has c. Something a user is d. Something a user knows PTS: 1 20. A security administrator with full administrative rights on the network is forced to change roles on a quarterly basis with another security administrator. Which of the following describes this form of access control? a. Job rotation b. Separation of duties c. Mandatory vacation d. Least privilege PTS: 1 21. In order to access the network, an employee must swipe their finger on a device. Which of the following describes this form of authentication? a. Single sign-on b. Multifactor c. Biometrics d. Tokens PTS: 1 22. A proximity card reader is used to test which of the following aspects of human authentication? a. Something a user knows b. Something a user is c. Something a user did d. Something a user has PTS: 1 23. Which of the following would be considered multifactor authentication? a. Pin number and a smart card b. ACL entry and a pin number c. Username and password d. Common access card PTS: 1 24. Which of the following is a form of photo identification used to gain access into a secure location? a. Token b. CAC c. DAC d. Biometrics PTS: 1 25. Which of the following is a trusted OS implementation used to prevent malicious or suspicious code from executing on Linux and UNIX platforms? a. SELinux b. vmlinuz c. System File Checker (SFC) d. Tripwire PTS: 1 26. Which of the following is an example of allowing a user to perform a self-service password reset? a. Password length b. Password recovery c. Password complexity d. Password expiration PTS: 1 27. Which of the following is an example of requiring users to have a password of 16 characters or more? a. Password recovery requirements b. Password complexity requirements c. Password expiration requirements d. Password length requirements PTS: 1 28. A security administrator is asked to email an employee their password. Which of the following account policies MUST be set to ensure the employee changes their password promptly? a. Password expiration b. Account lockout c. Password recovery d. Account enablement PTS: 1 29. Employees are required to come up with a passphrase of at least 15 characters to access the corporate network. Which of the following account policies does this exemplify? a. Password expiration b. Password complexity c. Password lockout d. Password length PTS: 1 30. An administrator has implemented a policy that passwords expire after 60 days and cannot match their last six previously used passwords. Users are bypassing this policy by immediately changing their passwords six times and then back to the original password. Which of the following can the administrator MOST easily employ to prevent this unsecure practice, with the least administrative effort? a. Create a policy that passwords must be no less than ten characters. b. Monitor user accounts and change passwords of users found to be doing this. c. Create a policy that passwords cannot be changed more than once a day. d. Monitor user accounts and lock user accounts that are changing passwords excessively. PTS: 1 31. Which of the following MUST be implemented in conjunction with password history, to prevent a user from re-using the same password? a. Maximum age time b. Lockout time c. Minimum age time d. Expiration time PTS: 1 32. Which of the following represents the complexity of a password policy which enforces lower case password using letters from 'a' through 'z' where 'n' is the password length? a. n26 b. 2n * 26 c. 26n d. n2 * 26 PTS: 1 33. Which of the following BEST describes the process of key escrow? a. Maintains a copy of a user's public key for the sole purpose of recovering messages if it is lost b. Maintains a secured copy of a user's private key to recover the certificate revocation list c. Maintains a secured copy of a user's private key for the sole purpose of recovering the key if it is lost d. Maintains a secured copy of a user's public key in order to improve network performance PTS: 1 34. The fundamental difference between symmetric and asymmetric key cryptographic systems is that symmetric key cryptography uses: a. multiple keys for non-repudiation of bulk data. b. different keys on both ends of the transport medium. c. bulk encryption for data transmission over fiber. d. the same key on each end of the transmission medium. PTS: 1 35. Which of the following methods BEST describes the use of hiding data within other files? a. Digital signatures b. PKI c. Transport encryption d. Steganography PTS: 1 36. When a user first moves into their residence, the user receives a key that unlocks and locks their front door. This key is only given to them but may be shared with others they trust. Which of the following cryptography concepts is illustrated in the example above? a. Asymmetric key sharing b. Exchange of digital signatures c. Key escrow exchange d. Symmetric key sharing PTS: 1 37. Which of the following cryptography types provides the same level of security but uses smaller key sizes and less computational resources than logarithms which are calculated against a finite field? a. Elliptical curve b. Diffie-Hellman c. Quantum d. El Gamal PTS: 1 38. The BEST way to protect the confidentiality of sensitive data entered in a database table is to use: a. hashing. b. stored procedures. c. encryption. d. transaction logs. PTS: 1 39. WEP is seen as an unsecure protocol based on its improper use of which of the following? a. RC6 b. RC4 c. 3DES d. AES PTS: 1 40. Which of the following is used in conjunction with PEAP to provide mutual authentication between peers? a. LEAP b. MSCHAPv2 c. PPP d. MSCHAPv1 PTS: 1 41. Which of the following is seen as non-secure based on its ability to only store seven uppercase characters of data making it susceptible to brute force attacks? a. PAP b. NTLMv2 c. LANMAN d. CHAP PTS: 1 42. Which of the following access control technologies provides a rolling password for one-time use? a. RSA tokens b. ACL c. Multifactor authentication d. PIV card PTS: 1 43. A security administrator has discovered through a password auditing software that most passwords can be discovered by cracking the first seven characters and then cracking the second part of the password. Which of the following is in use by the company? a. LANMAN b. MD5 c. WEP d. 3DES PTS: 1 44. NTLM is an improved and substantially backwards compatible replacement for which of the following? a. 3DES b. LANMAN c. PGP d. passwd PTS: 1 45. Which of the following does a TPM allow for? a. Cloud computing b. Full disk encryption c. Application hardening d. Input validation PTS: 1 46. The company encryption policy requires all encryption algorithms used on the corporate network to have a key length of 128-bits. Which of the following algorithms would adhere to company policy? a. DES b. SHA c. 3DES d. AES PTS: 1 47. The security administrator wants to ensure messages traveling between point A and point B are encrypted and authenticated. Which of the following accomplishes this task? a. MD5 b. RSA c. Diffie-Hellman d. Whole disk encryption PTS: 1 48. Which of the following elements of PKI are found in a browser's trusted root CA? a. Private key b. Symmetric key c. Recovery key d. Public key PTS: 1 49. A security administrator wants to prevent users in sales from accessing their servers after 6:00 a. m., and prevent them from accessing accounting's network at all times. Which of the following should the administrator implement to accomplish these goals? (Select TWO). a. Separation of duties b. Time of day restrictions c. Access control lists d. Mandatory access control e. Single sign-on PTS: 1 50. Which of the following is the primary purpose of using a digital signature? (Select TWO). a. Encryption b. Integrity c. Confidentiality d. Non-repudiation e. Availability PTS: 1 Exam F 1. Where are revoked certificates stored? a. Recovery agent b. Registration c. Key escrow d. CRL PTS: 1 2. Which of the following asymmetric encryption keys is used to encrypt data to ensure only the intended recipient can decrypt the ciphertext? a. Private b. Escrow c. Public d. Preshared PTS: 1 3. Which of the following must a security administrator do when the private key of a web server has been compromised by an intruder? a. Submit the public key to the CRL. b. Use the recovery agent to revoke the key. c. Submit the private key to the CRL. d. Issue a new CA. PTS: 1 4. Which of the following PKI implementation element is responsible for verifying the authenticity of certificate contents? a. CRL b. Key escrow c. Recovery agent d. CA PTS: 1 5. If a user wishes to receive a file encrypted with PGP, the user must FIRST supply the: a. public key. b. recovery agent. c. key escrow account. d. private key. PTS: 1 6. A certificate that has been compromised should be published to which of the following? a. AES b. CA c. CRL d. PKI PTS: 1 7. The security administrator is tasked with authenticating users to access an encrypted database. Authentication takes place using PKI and the encryption of the database uses a separate cryptographic process to decrease latency. Which of the following would describe the use of encryption in this situation? a. Private key encryption to authenticate users and private keys to encrypt the database b. Private key encryption to authenticate users and public keys to encrypt the database c. Public key encryption to authenticate users and public keys to encrypt the database d. Public key encryption to authenticate users and private keys to encrypt the database PTS: 1 8. When a certificate issuer is not recognized by a web browser, which of the following is the MOST common reason? a. Lack of key escrow b. Self-signed certificate c. Weak certificate pass-phrase d. Weak certificate cipher PTS: 1 9. Public keys are used for which of the following? a. Decrypting wireless messages b. Decrypting the hash of an electronic signature c. Bulk encryption of IP based email traffic d. Encrypting web browser traffic PTS: 1 10. Which of the following is a requirement when implementing PKI if data loss is unacceptable? a. Web of trust b. Non-repudiation c. Key escrow d. Certificate revocation list PTS: 1 11. The recovery agent is used to recover the: a. root certificate. b. key in escrow. c. public key. d. private key. PTS: 1 12. Which of the following is true about the CRL? a. It should be kept public b. It signs other keys c. It must be kept secret d. It must be encrypted PTS: 1 13. Which of the following is the BEST filtering device capable of stateful packet inspection? a. Switch b. Protocol analyzer c. Firewall d. Router PTS: 1 14. An employee's workstation is connected to the corporate LAN. Due to content filtering restrictions, the employee attaches a 3G Internet dongle to get to websites that are blocked by the corporate gateway. Which of the following BEST describes a security implication of this practice? a. A corporate LAN connection and a 3G Internet connection are acceptable if a host firewall is installed. b. The security policy should be updated to state that corporate computer equipment should be dual-homed. c. Content filtering should be disabled because it may prevent access to legitimate sites. d. Network bridging must be avoided otherwise it may join two networks of different classifications. PTS: 1 15. Which of the following is the BEST approach to perform risk mitigation of user access control rights? a. Conduct surveys and rank the results. b. Perform routine user permission reviews. c. Implement periodic vulnerability scanning. d. Disable user accounts that have not been used within the last two weeks. PTS: 1 16. In a disaster recovery situation, operations are to be moved to an alternate site. Computers and network connectivity are already present; however, production backups are several days out-of- date. Which of the following site types is being described? a. Cold site b. High availability site c. Warm site d. Hot site PTS: 1 17. All of the following are valid cryptographic hash functions EXCEPT: a. RIPEMD. b. RC4. c. SHA-512. d. MD4. PTS: 1 18. Which of the following PKI components identifies certificates that can no longer be trusted? a. CRL b. CA public key c. Escrow d. Recovery agent PTS: 1 19. Which of the following can prevent an unauthorized person from accessing the network by plugging into an open network jack? a. 802.1x b. DHCP c. 802.1q d. NIPS PTS: 1 20. A digital signature provides which of the following security functions for an email message? a. Encryption b. Hashing c. Input validation d. Non-repudiation PTS: 1 21. By defaultCMP will use which of the following to encrypt wireless transmissions? a. RC4 b. Blowfish c. AES d. RSA PTS: 1 22. A programmer cannot change the production system directly and must have code changes reviewed and approved by the production system manager. Which of the following describes this control type? a. Discretionary access control b. Separation of duties c. Security policy d. Job rotation PTS: 1 23. ARP poison routing attacks are an example of which of the following? a. Distributed Denial of Service b. Smurf Attack c. Man-in-the-middle d. Vishing PTS: 1 24. A company hires a security firm to assess the security of the company's network. The company does not provide the firm with any internal knowledge or documentation of the network. Which of the following should the security firm perform? a. Black hat b. Black box c. Gray hat d. Gray box PTS: 1 25. Steganography is a form of which of the following? a. Block ciphering b. Quantum cryptography c. Security through obscurity d. Asymmetric encryption PTS: 1 26. In a public key infrastructure, a trusted third party is also known as which of the following? a. Public key b. Certificate signing request c. Common name d. Certificate authority PTS: 1 27. Which of the following threats are specifically targeted at high profile individuals? a. Whaling b. Malicious insider c. Privilege escalation d. Shoulder surfing PTS: 1 28. Which of the following devices is MOST commonly vulnerable to bluesnarfing? a. Mobile devices b. Desktops c. Digital signage d. Ethernet jacks PTS: 1 29. Which of the following application attacks typically involves entering a string of characters and bypassing input validation to display additional information? a. Session hijacking b. Zero day attack c. SQL injection d. Cross-site scripting PTS: 1 30. Which of the following features should be enabled on perimeter doors to ensure that unauthorized access cannot be gained in the event of a power outage? a. Manual override b. Fail closed c. Mantrap d. Fail open PTS: 1 31. Which of the following is the BEST tool to use when analyzing incoming network traffic? a. Sniffer b. Port scanner c. Firewall d. Syslog PTS: 1 32. Providing elastic computing resources that give a client access to more resources, allowing for distribution of large jobs across a flexible number of machines, or allowing for distributed storage of information are all hallmarks of which technology? a. Remote access b. Clustering c. Cloud computing d. IP networking PTS: 1 33. Which of the following network security techniques can be easily circumvented by using a network sniffer? a. Disabling the SSID broadcast b. Enabling strong wireless encryption c. Implementing MAC filtering on WAPs d. Reducing the wireless power level PTS: 1 34. Which of the following authentication services can be used to provide router commands to enforce policies? a. RADIUS b. Kerberos c. LDAP d. TACACS+ PTS: 1 35. Which of the following ports is used for telnet by default? a. 21 b. 23 c. 25 d. 33 PTS: 1 36. Which of the following BEST describes a malicious application that attaches itself to other files? a. Rootkits b. Adware c. Backdoors d. Virus PTS: 1 37. When an attack using a publicly unknown vulnerability compromises a system, it is considered to be which of the following? a. IV attack b. Zero day attack c. Buffer overflow d. Malicious insider threat PTS: 1 38. A professor at a university is given two keys. One key unlocks a classroom door and the other locks it. The key used to lock the door is available to all other faculty. The key used to unlock the door is only given to the professor. Which of the following cryptography concepts is illustrated in the example above? a. Key escrow exchange b. Asymmetric key sharing c. Exchange of digital signatures d. Symmetric key sharing PTS: 1 39. Which of the following attacks targets high profile individuals? a. Logic bomb b. Smurf attack c. Whaling d. Fraggle attack PTS: 1 40. A penetration tester is collecting a large amount of wireless traffic to perform an IV attack. Which of the following can be gained by doing this? a. WPA2 shared secret b. WPA key c. WEP key d. EAP-TLS private key PTS: 1 41. Which of the following allows users in offsite locations to connect securely to a corporate office? a. Telnet b. FTP c. VPN d. SNMP PTS: 1 42. On a website, which of the following protocols facilitates security for data in transit? a. HTTP b. SSL c. SSH d. DNS PTS: 1 43. Which of the following BEST describes the purpose of fuzzing? a. To decrypt network sessions b. To gain unauthorized access to a facility c. To hide system or session activity d. To discover buffer overflow vulnerabilities PTS: 1 44. There are several users for a particular Human Resources database that contains PII. Which of the following principles should be applied to the users in regards to privacy of information? a. Single sign-on b. Least privilege c. Time of day restrictions d. Multifactor authentication PTS: 1 45. Which of the following is true about PKI? (Select TWO). a. When encrypting a message with the public key, only the public key can decrypt it. b. When encrypting a message with the private key, only the private key can decrypt it. c. When encrypting a message with the public key, only the CA can decrypt it. d. When encrypting a message with the public key, only the private key can decrypt it. e. When encrypting a message with the private key, only the public key can decrypt it. PTS: 1 46. A file has been encrypted with an employee's private key. When the employee leaves the company, their account is deleted. Which of the following are the MOST likely outcomes? (Select TWO). a. Recreate the former employee's account to access the file. b. Use the recovery agent to decrypt the file. c. Use the root user account to access the file. d. The data is not recoverable. e. Decrypt the file with PKI. PTS: 1 47. Which of the following relies on creating additional traffic to congest networks? (Select TWO). a. Logic bomb b. Smurf attack c. Man-in-the-middle attack d. DDoS e. DNS poisoning PTS: 1 48. Which of the following MOST likely has its access controlled by TACACS+? (Select TWO). a. Mobile devices b. Active directory c. Router d. Switch e. Kerberos PTS: 1 49. Which of the following are often used to encrypt HTTP traffic? (Select TWO). a. PAP b. SCP c. SHA d. TLS e. SSL PTS: 1 50. Which of the following security controls is the BEST mitigation method to address mobile device data theft? (Select TWO). a. Inventory logs b. Remote wipe c. Device encryption d. Host-based firewall e. Check in and check out paperwork PTS: 1 Exam G 1. Which of the following would be a reason to implement DAC as an access control model? a. Management should have access to all resources b. An employee's security level should determine the access level c. The owner of the data should decide who has access d. Centrally administered roles determine who has access PTS: 1 2. A security administrator needs to install a new switch for a conference room where two different groups will be having separate meetings. Each of the groups uses different subnets and need to have their traffic separated. Which of the following would be the SIMPLEST solution? a. Create ACLs to deny traffic between the two networks on the switch. b. Install a network firewall. c. Create two VLANs on the switch. d. Add a router to separate the two networks. PTS: 1 3. Which of the following would need to be added to a network device's configuration in order to keep track of the device's various parameters and to monitor status? a. SNMP string b. ACLs c. Routing information d. VLAN information PTS: 1 4. Which of the following is a control that is gained by using cloud computing? a. Data encryption b. High availability of the data c. Administrative control of the data d. Physical control of the data PTS: 1 5. A security administrator ensures that rights on a web server are not sufficient to allow outside users to run JavaScript commands. This is an example of which of the following? a. Application patch management b. Data execution prevention c. Error and exception handling d. Cross-site scripting prevention PTS: 1 6. Which of the following creates a publicly accessible network and isolates the internal private network from the Internet? a. DMZ b. NAC c. NAT d. VPN PTS: 1 7. A security administrator is encrypting all smartphones connected to the corporate network. Which of the following could be used to meet this requirement? a. Mobile device encryption b. Database encryption c. Network encryption d. HSM PTS: 1 8. Using both a username and a password is an example of: a. biometric authentication. b. something a user knows and something a user has. c. single factor authentication. d. multifactor authentication. PTS: 1 9. GPU processing power is a mitigating factor for which of the following security concerns? a. Password complexity b. Cloud computing c. Biometrics d. Virtualization PTS: 1 10. Which of the following can the security administrator implement to BEST prevent laptop device theft? a. Device encryption b. Cable locks c. GPS tracking d. CCTV PTS: 1 11. The pharmacy has paper forms ready to use if the computer systems are unavailable. Which of the following has been addressed? a. Continuity of operations b. Single point of failure c. Disaster recovery d. Business process reengineering PTS: 1 12. Which of the following causes an issue when acquiring an image that occurs when a server hard drive is forensically examined? a. Servers often use RAID b. Servers contain sensitive information c. Servers cannot be powered down d. Servers often use file systems PTS: 1 13. Which of the following provides the BEST metric for determining the effectiveness of a Continuity of Operations Plan or Disaster Recovery Plan? a. Average downtime b. Mean time between failures c. Mean time to restore d. Average uptime PTS: 1 14. Which of the following is the correct formula for calculating mean time to restore (MTTR)? a. MTTR = (time of fail) / (time of restore) b. MTTR = (time of fail) # (time of restore) c. MTTR = (time of restore) # (time of fail) d. MTTR = (time of restore) x (time of fail) PTS: 1 15. The corporate NIDS keeps track of how each program acts and will alert the security administrator if it starts acting in a suspicious manner. Which of the following describes how the NIDS is functioning? a. Behavior based b. Signature based c. Host based d. Network Access Control (NAC) based PTS: 1 16. Pete, a security technician, has chosen IPSec for remote access VPN connections for company telecommuters. Which of the following combinations would be BEST for Pete to use to secure this connection? a. Transport modeSP b. Transport mode, AH c. Tunnel mode, AH d. Tunnel modeSP PTS: 1 17. Matt, a security administrator, is using AES. Which of the following cipher types is used by AES? a. Block b. Fourier c. Stream d. Turing PTS: 1 18. Which of the following forensic artifacts is MOST volatile? a. CD-ROM b. File system c. Random access memory d. Network topology PTS: 1 19. Which of the following protocols can Sara, a security administrator, use to implement security at the lowest OSI layer? a. IPSec b. SSL c. ICMP d. SSH PTS: 1 20. Which of the following protocols uses UDP port 69 by default? a. Kerberos b. TFTP c. SSH d. DNS PTS: 1 21. After completing a forensic image of a hard drive, which of the following can Jane, a security technician, use to confirm data integrity? a. Chain of custody b. Image compression c. AES256 encryption d. SHA512 hash PTS: 1 22. Which of the following can Matt, a security administrator, use to provide integrity verification when storing data? a. Encryption b. Hashing c. PKI d. ACL PTS: 1 23. Which of the following is an example of implementing security using the least privilege principle? a. Confidentiality b. Availability c. Integrity d. Non-repudiation PTS: 1 24. The decision to build a redundant datacenter MOST likely came from which of the following? a. Application performance monitoring b. Utilities cost analysis c. Business impact analysis d. Security procedures review PTS: 1 25. Sara and Pete are unauthorized system attackers that may be able to remotely destroy critical equipment in a datacenter if they gain control over which of the following systems? a. Physical access control b. Video surveillance c. HVAC d. Packet sniffer PTS: 1 26. In high traffic areas, Jane and Pete, security guards, need to be MOST concerned about which of the following attacks? a. War driving b. Blue jacking c. Shoulder surfing d. Tailgating PTS: 1 27. Which of the following BEST describes an attack whereby unsolicited messages are sent to nearby mobile devices? a. Smurf attack b. Bluejacking c. Bluesnarfing d. War driving PTS: 1 28. Which of the following network ACL entries BEST represents the concept of implicit deny? a. Deny UDP any b. Deny TCP any c. Deny ANY any d. Deny FTP any PTS: 1 29. Which of the following protocols assists in identifying Pete, a usery the generation of a key, to establish a secure session for command line administration of a computer? a. SFTP b. FTP c. SSH d. DNS PTS: 1 30. Which of the following is a major risk for Matt, a security administrator, to consider in regards to cloud computing? a. Loss of physical control over data b. Increased complexity of qualitative risk assessments c. Smaller attack surface d. Data labeling challenges PTS: 1 31. Matt, a security administrator, performs various audits of a specific system after an attack. Which of the following BEST describes this type of risk mitigation? a. Change management b. Incident management c. User training d. New policy implementation PTS: 1 32. Which of the following is the MOST appropriate risk mitigation strategy for Sara, a security administrator, to use in order to identify an unauthorized administrative account? a. Change management b. Incident management c. Routine audits of system logs d. User's rights and permissions review PTS: 1 33. Which of the following would Jane, a security administrator, MOST likely look for during a vulnerability assessment? a. Ability to gain administrative access to various systems b. Identify lack of security controls c. Exploit vulnerabilities d. Actively test security controls PTS: 1 34. Which of the following will contain a list of unassigned public IP addresses? a. TCP port b. 802.1x c. Loop protector d. Firewall rule PTS: 1 35. The MAIN difference between qualitative and quantitative risk assessment is: a. quantitative is based on the number of assets while qualitative is based on the type of asset. b. qualitative is used in small companies of 100 employees or less while quantitative is used in larger companies of 100 employees or more. c. quantitative must be approved by senior management while qualitative is used within departments without specific approval. d. quantitative is based on hard numbers while qualitative is based on subjective ranking. PTS: 1 36. Which of the following attacks involves sending unsolicited contact information to Bluetooth devices configured in discover mode? a. Impersonation b. Bluejacking c. War driving d. Bluesnarfing PTS: 1 37. Which of the following assessments is directed towards exploiting successive vulnerabilities to bypass security controls? a. Vulnerability scanning b. Penetration testing c. Port scanning d. Physical lock testing PTS: 1 38. Which of the following is the technical implementation of a security policy? a. VLAN b. Flood guards c. Cloud computing d. Firewall rules PTS: 1 39. Which of the following can Mike, a security technician, use to prevent numerous SYN packets from being accepted by a device? a. VLAN management b. Transport encryption c. Implicit deny d. Flood guards PTS: 1 40. Which of the following can Jane, a security technician, use to stop malicious traffic from affecting the company servers? a. NIDS b. Protocol analyzers c. Sniffers d. NIPS PTS: 1 41. Which of the following tools allows a security company to identify the latest unknown attacks utilized by attackers? a. IDS b. Honeypots c. Port scanners d. Code reviews PTS: 1 42. If continuity plans are not regularly exercised, which of the following aspects of business continuity planning are often overlooked until a disaster occurs? a. Zero day exploits b. Succession planning c. Tracking of man hours d. Single points of failure PTS: 1 43. Large, partially self-governingollection of hosts executing instructions for a specific purpose is an example of which type of malware? a. Virus b. Worm c. Trojan d. Botnet PTS: 1 44. Which of the following attacks is BEST described as an attempt to convince Matt, an authorized user, to provide information that can be used to defeat technical security controls? a. Shoulder surfing b. Tailgating c. Impersonation d. Packet sniffing PTS: 1 45. Randomly attempting to connect to wireless network access points and documenting the locations of accessible networks is known as which of the following? a. Packet sniffing b. War chalking c. Evil twin d. War driving PTS: 1 46. Which of the following should Sara, a security technicianheck regularly to avoid using compromised certificates? a. CRL b. PKI c. Key escrow d. CA PTS: 1 47. A user reports the ability to access the Internet but the inability to access a certain secure website. The web browser reports the site needs to be viewed under a secure connection. Which of the following is the MOST likely cause? (Select TWO). a. The site is using TLS instead of SSL. b. The user is not using HTTP. c. The site is not using URL redirection. d. ICMP needs to be enabled. e. The user is not using HTTPS. PTS: 1 48. Which of the following is the BEST way to implement data leakage prevention? (Select TWO). a. Installing DLP software on all computers along with the use of policy and procedures b. Installing DLP software on all perimeter appliances and incorporating new policies and procedures c. Securing all appliances and computers that control data going into the network along with the use of policy and procedures d. Ensuring the antivirus, NIDS, anti-malware software, and signatures are up-to-date e. Implementing firewall access control lists to block all incoming attachments PTS: 1 49. A tape library containing a database with sensitive information is lost in transit to the backup location. Which of the following will prevent this media from disclosing sensitive information? (Select TWO). a. Mobile device encryption b. Full disk encryption c. Database encryption d. Discretionary access control e. Trusted platform module PTS: 1 50. Which of the following password policies are designed to increase the offline password attack time? (Select TWO). a. Password expiration b. Password lockout time c. Password age time d. Password complexity e. Password length PTS: 1 Exam H 1. Matt, a user, was able to access a system when he arrived to work at 5:45 a.m. Just before Matt left at 6:30 p.m., he was unable to access the same systemven though he could ping the system. In a Kerberos realm, which of the following is the MOST likely reason for this? a. Matt's ticket has expired. b. The system has lost network connectivity. c. The CA issued a new CRL. d. The authentication server is down. PTS: 1 2. Pete, a security administrator, is considering using TACACS+. Which of the following is a reason to use TACACS+ over RADIUS? a. Combines authentication and authorization b. Encryption of all data between client and server c. TACACS+ uses the UDP protocol d. TACACS+ has less attribute-value pairs PTS: 1 3. A company is looking at various solutions to manage their large datacenter. The company has a lot of sensitive data on unreliable systems. Which of the following can Matt, a security technician, use to allow the company to minimize their footprint? a. Infrastructure as a Service b. Implement a NAC server c. Software as a Service d. Create a new DMZ PTS: 1 4. A hard drive of a terminated employee has been encrypted with full disk encryption, and Sara, a technician, is not able to decrypt the data. Which of the following ensures that, in the future, Sara will be able to decrypt this information? a. Certificate authority b. Key escrow c. Public key d. Passphrase PTS: 1 5. Which of the following is true about the private key in a PKI? a. It is used by the recovery agent to generate a lost public key b. It is used by the CA to validate a user's identity c. It is used to decrypt the email hash in signed emails d. It is used to encrypt the email hash in signed emails PTS: 1 6. Which of the following is an example of authentication using something Sara, a user, has and something she is? a. Username and PIN b. Token and PIN c. Password and retina scan d. Token and fingerprint scan PTS: 1 7. Which of the following attacks is MOST likely prevented when a website does not allow the '<' character as the input in a web form field? a. Integer overflow b. SQL injection c. Buffer overflow d. Cross-site scripting PTS: 1 8. Which of the following must Pete, a security administrator, install on a flash drive to allow for portable drive data confidentiality? a. USB encryptor b. Hardware write lock c. USB extension cable d. Ext2 file system PTS: 1 9. An online banking portal is not accessible by customers during a holiday season. Sara and Pete, network administrators, notice sustainedxtremely high network traffic being directed towards the web interface of the banking portal from various external networks. Which of the following BEST describes what is occurring? a. X-Mas attack b. DDoS attack c. DNS poisoning d. DOS attack PTS: 1 10. While chatting with friends over IM, Matt, a user, receives numerous instant messages from strangers advertising products or trying to send files. Which of the following BEST describes the threat? a. Spear phishing b. Spam c. Spim d. Spoofing PTS: 1 11. Which of the following is the MOST likely implication of a corporate firewall rule that allows TCP port 22 from any internal IP to any external site? a. Data loss can occur as an SSH tunnel may be established to home PCs. b. NAT of external websites to the internal network will be limited to TCP port 22 only. c. Host based firewalls may crash due to protocol compatibility issues. d. IPSec VPN access for home users will be limited to TCP port 22 only. PTS: 1 12. Jane, a network administratorhanges the default usernames and passwords on an 802.11n router. This is an example of which of the following network management controls? a. System hardening b. Rule-based management c. Network separation d. VLAN management PTS: 1 13. Jane, a security technician, needs to transfer files. Which of the following is the file transfer function that utilizes the MOST secure form of data transport? a. TFTP b. FTP active c. FTP passive d. SFTP PTS: 1 14. Which of the following, when used in conjunction with software-based encryptionnhances platform authentication by storing unique RSA keys and providing crypto processing? a. LDAP b. TPM c. Kerberos d. Biometrics PTS: 1 15. Which of the following exploitation types involves injection of pseudo-random data in order to crash or provide unexpected results from an application? a. Cross-site forgery b. Brute force attack c. Cross-site scripting d. Fuzzing PTS: 1 16. Which of the following ports would Sara, a security administrator, need to be open to allow TFTP by default? a. 69 b. 110 c. 137 d. 339 PTS: 1 17. Pete, a customer, has called a company to report that all of his computers are displaying a rival company's website when Pete types the correct URL into the browser. All of the other websites he visits work correctly and other customers are not having this issue. Which of the following has MOST likely occurred? a. The company's website has a misconfigured firewall. b. Pete has a virus outbreak. c. Pete's DNS has been poisoned. d. The company's website has been attacked by the rival company. PTS: 1 18. Jane, a system administrator, sees a firewall rule that applies to 10.4.4.58/27. Which of the following IP address ranges are encompassed by this rule? a. 10.4.4.27, 10.4.4.58 b. 10.4.4.32, 10.4.4.63 c. 10.4.4.58, 10.4.4.89 d. 10.4.4.58, 10.4.4.127 PTS: 1 19. Which of the following would be implemented if Jane, a security administrator, wants a door to electronically unlock when certain employees need access to a location? a. Device locks b. Video surveillance c. Mantraps d. Proximity readers PTS: 1 20. Which of the following is considered strong authentication? a. Trusted OS b. Smart card c. Biometrics d. Multifactor PTS: 1 21. Which of the following is an example of a smart card? a. PIV b. MAC c. One-time passwords d. Tokens PTS: 1 22. Which of the following is a security best practice that allows Pete, a user, to have one ID and password for all systems? a. SSO b. PIV c. Trusted OS d. Token PTS: 1 23. Which of the following is an example of the type of access control methodology provided on Windows systems by default? a. Single Sign-On b. Discretionary Access Control (DAC) c. Mandatory Access Control (MAC) d. Rule based Access Control (RBAC) PTS: 1 24. Which of the following is the MOST thorough way to discover software vulnerabilities after its release? a. Baseline reporting b. Design review c. Code review d. Fuzzing PTS: 1 25. Which of the following is the way Pete, a security administratoran actively test security controls on a system? a. White box testing b. Port scanning c. Penetration testing d. Vulnerability scanning PTS: 1 26. Which of the following is another name for fizzing third party proprietary software? a. Grey box testing b. Black box testing c. White box testing d. Blue jacking PTS: 1 27. Which of the following application attacks can be used against Active Directory based systems? a. XML injection b. SQL injection c. LDAP injection d. Malicious add-ons PTS: 1 28. Which of the following is a security best practice that Jane, a security technician, would implement before placing a new server online? a. On-demand computing b. Host software baselining c. Virtualization d. Code review PTS: 1 29. Which of the following software types can Sara, a security technician, use to protect against non- malicious but irritating malware? a. Pop-up blockers b. Antivirus c. Host-based firewalls d. Anti-spyware PTS: 1 30. Which of the following is the MOST common security issue on web-based applications? a. Hardware security b. Transport layer security c. Input validation d. Fizzing PTS: 1 31. Which of the following can cause data loss from web based applications? a. Device encryption b. Poor error handling c. Application hardening d. XML PTS: 1 32. Which of the following is a preventative physical security control? a. CCTV b. Armed guard c. Proper lighting d. Access list PTS: 1 33. Matt, a security administrator, is considering using cloud computing. Which of the following security concerns is MOST prominent when utilizing cloud computing service providers? a. Video surveillance b. Mobile device access c. Removable storage media d. Blended systems and data PTS: 1 34. Which of the following is a security control that can utilize a command such as 'deny ip any any'? a. ACL b. Content inspection c. Network bridge d. VPN PTS: 1 35. Which of the following is an account management principle for simplified user administration? a. Ensure password complexity requirements are met. b. Disable unused system accounts. c. Implement access based on groups. d. Ensure minimum password length is acquired. PTS: 1 36. In which of the following locations can password complexity be enforced via group policy? a. Domain controllers b. Local SAM databases c. ACLs d. NAC servers PTS: 1 37. A Black Box assessment of an application is one where Sara, the security assessor, has: a. access to the source code and the development documentation. b. no access to the application's source code and development documentation. c. access to the UAT documentation but not the source code. d. no access to the source code but access to the development documentation. PTS: 1 38. Which of the following security controls should Pete, the security administrator, implement to prevent server administrators from accessing information stored within an application on a server? a. File encryption b. Full disk encryption c. Change management d. Implicit deny PTS: 1 39. Which of the following can Pete, a security technicianeploy to provide secure tunneling services? a. IPv6 b. DNSSEC c. SNMPv2 d. SNMPv3 PTS: 1 40. Which of the following is a reason Pete, a security administrator, would implement Kerberos over local system authentication? a. Authentication to multiple devices b. Centralized file integrity protection c. Non-repudiation d. Greater password complexity PTS: 1 41. Which of the following is Pete, a security technician, MOST likely to use to secure the creation of cryptographic keys? a. Common access card b. Hashing algorithm c. Trusted platform module d. One-time pad PTS: 1 42. Which of the following is MOST likely to reduce the threat of a zero day vulnerability? a. Patch management b. Network-based intrusion detection system c. Disabling unnecessary services d. Host-based intrusion detection system PTS: 1 43. Which of the following has the capability to perform onboard cryptographic functions? a. Smartcard b. ACL c. RFID badge d. Proximity badge PTS: 1 44. Matt, a security administratoriscovers that Server1 and Server2 have been compromised, and then he observes unauthorized outgoing connections from Server1 to Server2. On Server1 there is an executable named tcpdump and several files that appear to be network dump files. Finally, there are unauthorized transactions in the database on Server2. Which of the following has MOST likely occurred? a. A logic bomb has been installed on Server1. b. A backdoor has been installed on Server2. c. A replay attack has been used against Server2. d. A botnet command and control has been installed on Server1. PTS: 1 45. Which of the following is MOST relevant for Jane, a security administrator, to use when investigating a SQL injection attack? a. Stored procedures b. Header manipulation c. Malformed frames d. Java byte code PTS: 1 46. Pete, a system administrator, was recently laid off for compromising various accounting systems within the company. A few months later, the finance department reported their applications were not working correctly. Upon further investigation, it was determined that unauthorized accounting software was installed onto a financial system and several application exploits existed within that system. This is an example of which of the following? a. Rootkit b. Logic bomb c. Worm d. Trojan horse PTS: 1 47. During a company's relocation, Sara, a security administrator, notices that several hard copies of company directories are being thrown away in public dumpsters. Which of the following attacks is the company vulnerable to without the proper user training and awareness? a. Hoaxes b. Pharming c. Social engineering d. Brute force PTS: 1 48. Matt, a security administrator, notices an unauthorized vehicle roaming the area on company grounds. Matt verifies that all network connectivity is up and running and that no unauthorized wireless devices are being used to authenticate other devices; however, he does notice an unusual spike in bandwidth usage. This is an example of which of the following attacks? a. Rogue access point b. Bluesnarfing c. Evil twin d. War driving PTS: 1 49. A new product is being evaluated by the security team. Which of the following would take financial and business impacts into consideration if this product was likely to be purchased for large scale use? a. Risk assessment b. Strength of security controls c. Application vulnerability d. Technical threat PTS: 1 50. Which of the following allows Jane, a security administrator, to divide a network into multiple zones? (Select TWO). a. PAT b. EIGRP c. VLAN d. NAT e. Subnetting PTS: 1 Exam I 1. Jane, a security administrator, needs to make a change in the network to accommodate a new remote location. The new location will be connected by a serial interface, off the main router, through a commercial circuit. This remote site will also have traffic completely separated from all other traffic. Which of the following design elements will Jane need to implement to accommodate the new location? a. VLANs need to be added on the switch but not the router. b. NAT needs to be re-configured to allow the remote location. c. The current IP scheme needs to be subnetted. d. The switch needs to be virtualized and a new DMZ needs to be created. PTS: 1 2. Matt, a security administrator, has recently performed a detailed datacenter inventory of all hardware and software. This analysis has resulted in identifying a lot of wasted resources. Which of the following design elements would eliminate the wasted resources and improve the datacenter's footprint? a. NAC b. Virtualization c. Remote access implementation d. Hosted IP Centrex PTS: 1 3. Pete, a user, reports that after a recent business trip, his laptop started having performance issues and unauthorized emails have been sent out from the laptop. Which of the following will resolve this issue? a. Updating Pete's laptop with current antivirus b. Updating the anti-spam application on the laptop c. Installing a new pop-up blocker d. Updating Pete's digital signature PTS: 1 4. When WPA is implemented using PSK by Pete, a security administrator, which of the following authentication types is he using? a. MD5 b. LEAP c. SHA d. TKIP PTS: 1 5. If Jane, a security administrator, is reviewing a verified JPEG's metadata and hash against an unverified copy of the graphic, which of the following is she looking for? a. Steganography b. Chain of custody c. Digital signatures d. Whole disk encryption PTS: 1 6. Which of the following technologies is often used by attackers to hide the origin of an attack? a. Open proxy b. Load balancer c. Flood guard d. URL filtering PTS: 1 7. Which of the following is susceptible to reverse lookup attacks if not configured properly? a. SSL b. IPSec c. ICMP d. DNS PTS: 1 8. Which of the following are the two basic components upon which cryptography relies? a. PKI and keys b. Algorithms and key escrow c. Key escrow and PKI d. Algorithms and keys PTS: 1 9. Jane, the company's Chief Information Officer (CIO)ontacts the security administrator about an email asking for money in order to receive the key that would decrypt the source code that the attacker encrypted. Which of the following malware types is this MOST likely to be in this situation? a. Worm b. Virus c. Spyware d. Ransomware PTS: 1 10. Matt, a security engineer, working at a public CA is implementing and installing a new CRL. Where should he logically place the server? a. On a wireless network b. Inside the DMZ c. On an non-routable network d. On a secure internal network PTS: 1 11. Jane, a security engineer, is deploying a new CA. Which of the following is the BEST strategy for the root CA after deploying an intermediate trusted CA? a. It should be placed outside of the firewall. b. It should be placed in the DMZ. c. It should be placed within an internal network. d. It should be shut down and kept in a secure location. PTS: 1 12. Matt, a security administrator, has installed a new server and has asked a network engineer to place the server within VLAN 100. This server can be reached from the Internetut Matt is unable to connect from the server to internal company resources. Which of the following is the MOST likely cause? a. The server is connected with a crossover cable. b. VLAN 100 does not have a default route. c. The server is in the DMZ. d. VLAN 100 is on the internal network. PTS: 1 13. Sara, a security administrator, is analyzing the packet capture from an IDS triggered filter. The packet capture shows the following string: 'or 1 ==1 - - Which of the following attacks is occurring? a. Cross-site scripting b. XML injection c. Buffer overflow d. SQL injection PTS: 1 14. Pete, a security administrator, is analyzing the packet capture from an IDS triggered filter. The packet capture shows the following string: <script>source=http://www.evilsite.co/evil.js</script> Which of the following attacks is occurring? a. SQL injection b. Redirection attack c. Cross-site scripting d. XML injection PTS: 1 15. Which of the following is true when Sara, a userrowsing to an HTTPS site receives the message: 'The site's certificate is not trusted'? a. The certificate has expired and was not renewed. b. The CA is not in the browser's root authority list. c. The intermediate CA was taken offline. d. The CA is not in the default CRL. PTS: 1 16. Which of the following is true when Sara, a userrowsing to an HTTPS site receives the message: 'Site name mismatch'? a. The certificate CN is different from the site DNS A record. b. The CA DNS name is different from the root certificate CN. c. The certificate was issued by the intermediate CA and not by the root CA. d. The certificate file name is different from the certificate CN. PTS: 1 17. Sara, a technician, must configure a network device to allow only certain protocols to the external servers and block requests to other internal sources. This is an example of a: a. demilitarized zone. b. load balancer. c. layer 2 switch. d. stateful firewall. PTS: 1 18. Pete, a user, wishes to encrypt only certain files and folders within a partition. Which of the following methods should Matt, a technician, recommend? a. EFS b. Partition encryption c. Full disk d. BitLocker PTS: 1 19. Which of the following can Jane, a security administrator, use to help prevent man-in-the-middle attacks? a. HTTP b. HTTPS c. SFTP d. Kerberos PTS: 1 20. Which of the following should Sara, a security administrator, implement on a mobile phone to help prevent a conversation from being captured? a. Device encryption b. Voice encryption c. GPS tracking d. Sniffer PTS: 1 21. Which of the following access control methods provides the BEST protection against attackers logging on as authorized users? a. Require a PIV card b. Utilize time of day restrictions c. Implement implicit deny d. Utilize separation of duties PTS: 1 22. Which of the following should Matt, a security technician, integrate into the fire alarm systems to help prevent a fire from spreading? a. HVAC b. Humidity controls c. Video monitoring d. Thermostats PTS: 1 23. An in-line network device examines traffic and determines that a parameter within a common protocol is well outside of expected boundaries. This is an example of which of the following? a. Anomaly based detection b. Behavior based detection c. IV attack detection d. Signature based detection PTS: 1 24. Jane, a malicious insider, obtains a copy of a virtual machine image for a server containing client financial records from the in-house virtualization cluster. Which of the following would BEST prevent Jane from accessing the client records? a. Cloud computing b. Separation of duties c. Portable media encryption d. File and folder encryption PTS: 1 25. Which of the following is the MOST effective method to provide security for an in-house created application during software development? a. Third-party white box testing of the completed application before it goes live. b. Third-party black box testing of the completed application before it goes live. c. Explicitly include security gates during the SDLC. d. Ensure an application firewall protects the application. PTS: 1 26. Matt, an attacker, incorrectly submits data on a website's form and is able to determine the type of database used by the application and the SQL statements used to query that database. Which of the following is responsible for this information disclosure? a. SQL injection b. Fuzzing c. XSS d. Error handling PTS: 1 27. Which of the following describes why Sara, the sender of an email, may encrypt the email with a private key? a. Confidentiality b. Non-repudiation c. Transmission speed d. Transport encryption PTS: 1 28. Matt, a security technician, needs to increase his password's key space. Which of the following increases the key space of a password the MOST? a. Letters, numbers, and special characters b. 25 or more alpha-numeric characters c. Two-factor authentication d. Sequential alpha-numeric patterns PTS: 1 29. Which of the following mitigation strategies is established to reduce risk when performing updates to business critical systems? a. Incident management b. Server clustering c. Change management d. Forensic analysis PTS: 1 30. Which of the following can Pete, a security administrator, use to distribute the processing effort when generating hashes for a password cracking program? a. RAID b. Clustering c. Redundancy d. Virtualization PTS: 1 31. An offsite location containing the necessary hardware without data redundancy would be an example of which of the following off-site contingency plans? a. Cluster b. Cold site c. Warm site d. Hot site PTS: 1 32. Which of the following should Jane, a security administrator, perform before a hard drive is analyzed with forensics tools? a. Identify user habits b. Disconnect system from network c. Capture system image d. Interview witnesses PTS: 1 33. Which of the following is BEST described as a scenario where organizational management decides not to provide a service offering because it presents an unacceptable risk to the organization? a. Mitigation b. Acceptance c. Deterrence d. Avoidance PTS: 1 34. Which of the following is the primary security reason why Pete, a security administrator, should block social networking sites in a large corporation? a. The proxy server needs to be specially configured for all social networking sites. b. The data traffic can cause system strain and can overwhelm the firewall rule sets. c. The users' work productivity decreases greatly. d. The users can unintentionally post sensitive company information. PTS: 1 35. Which of the following describes the importance of enacting and maintaining a clean desk policy? a. To ensure that data is kept on encrypted network shares b. To avoid passwords and sensitive data from being unsecured c. To verify that users are utilizing data storage resources d. To guarantee that users comply with local laws and regulations PTS: 1 36. Matt, a security technician, is using TFTP. Which of the following port numbers is used for TFTP? a. 22 b. 69 c. 80 d. 3389 PTS: 1 37. Which of the following systems implements a secure key distribution system that relies on hardcopy keys intended for individual sessions? a. Blowfish b. PGP/GPG c. One-time pads d. PKI PTS: 1 38. Which of the following devices would Jane, a security administrator, typically use at the enclave boundary to inspectlock, and re-route network traffic for security purposes? a. Load balancers b. Protocol analyzers c. Firewalls d. Spam filter PTS: 1 39. Which of the following devices is Pete, a security administrator, MOST likely to install to prevent malicious attacks? a. VPN concentrator b. Firewall c. NIDS d. Protocol analyzer PTS: 1 40. Which of the following devices should Jane, a security administrator, use to allow secure remote network access for mobile users? a. NIDS b. Protocol analyzer c. SFTP d. VPN concentrator PTS: 1 41. Which of the following is capable of providing the HIGHEST encryption bit strength? a. DES b. 3DES c. AES d. WPA PTS: 1 42. Which of the following technologies is used to verify that a file was not altered? a. RC5 b. AES c. DES d. MD5 PTS: 1 43. Which of the following, when used in conjunction with software-based encryptionnhances platform authentication by storing unique RSA keys and providing crypto processing? a. LDAP b. TPM c. Kerberos d. Biometrics PTS: 1 44. Which of the following should Jane, a security administratorheck for when conducting a wireless audit? (Select TWO). a. Open relays b. Antenna placement c. Encryption of wireless traffic d. URL filtering e. Open proxies PTS: 1 45. Which of the following passwords have the MOST similar key space? (Select TWO). a. AnDwWe9 b. check123 c. Mypassword!2~ d. C0mPTIA e. 5938472938193859392 PTS: 1 46. Pete, a security administrator, needs to implement a wireless system that will only be available within a building. Which of the following configurations can Pete modify to achieve this? (Select TWO). a. Proper AP placement b. Disable SSID broadcasting c. Use CCMP d. Enable MAC filtering e. Reduce the power levels PTS: 1 47. Which of the following protocols should Pete, a security administrator, use to ensure that the data remains encrypted during transport over the Internet? (Select THREE). a. TLS b. SSL c. FTP d. SSH e. HTTP f. TFTP PTS: 1 [Show More]
Last updated: 1 year ago
Preview 1 out of 139 pages
Buy this document to get the full access instantly
Instant Download Access after purchase
Add to cartInstant download
We Accept:
Reviews( 0 )
$18.00
Document information
Connected school, study & course
About the document
Uploaded On
Mar 07, 2020
Number of pages
139
Written in
Additional information
This document has been written for:
Uploaded
Mar 07, 2020
Downloads
0
Views
51

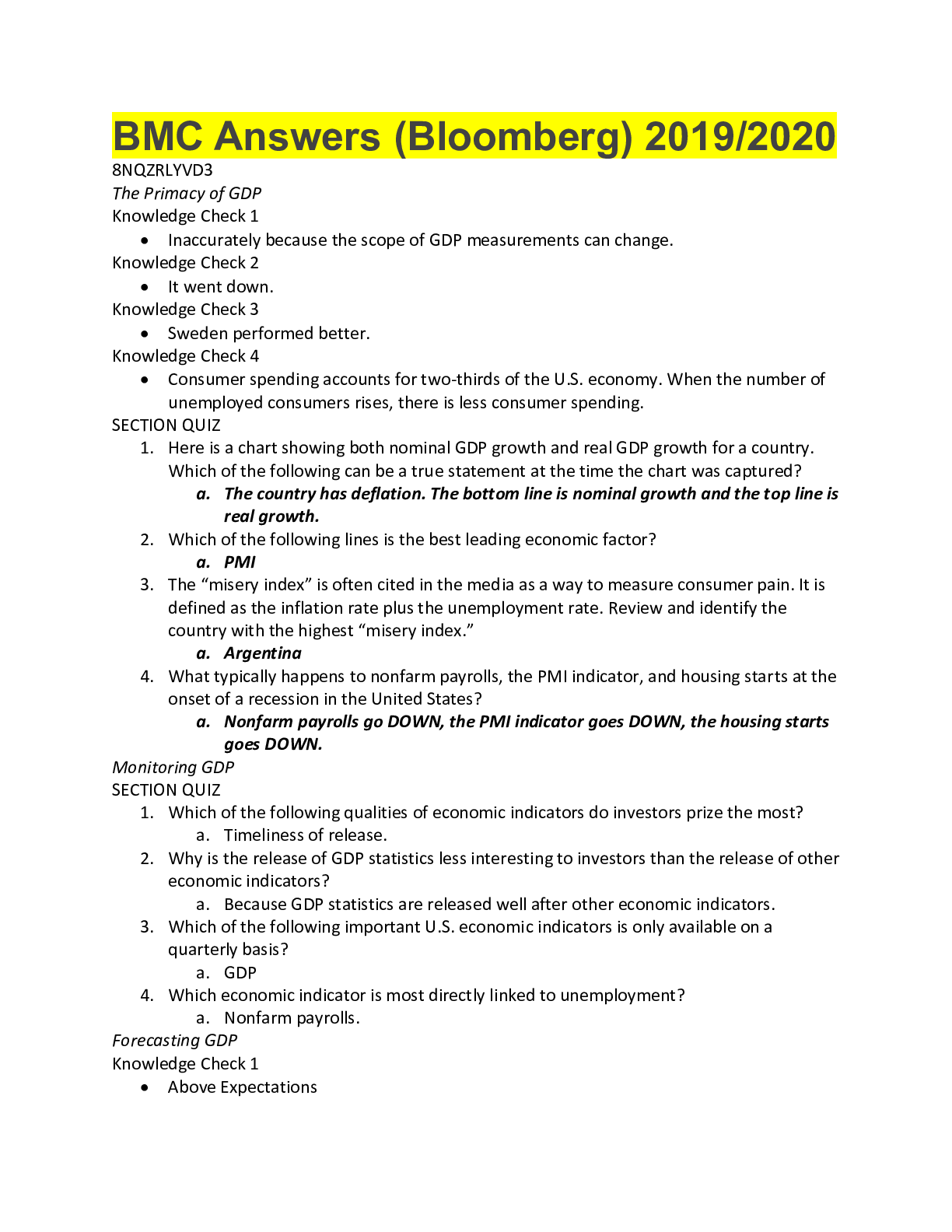
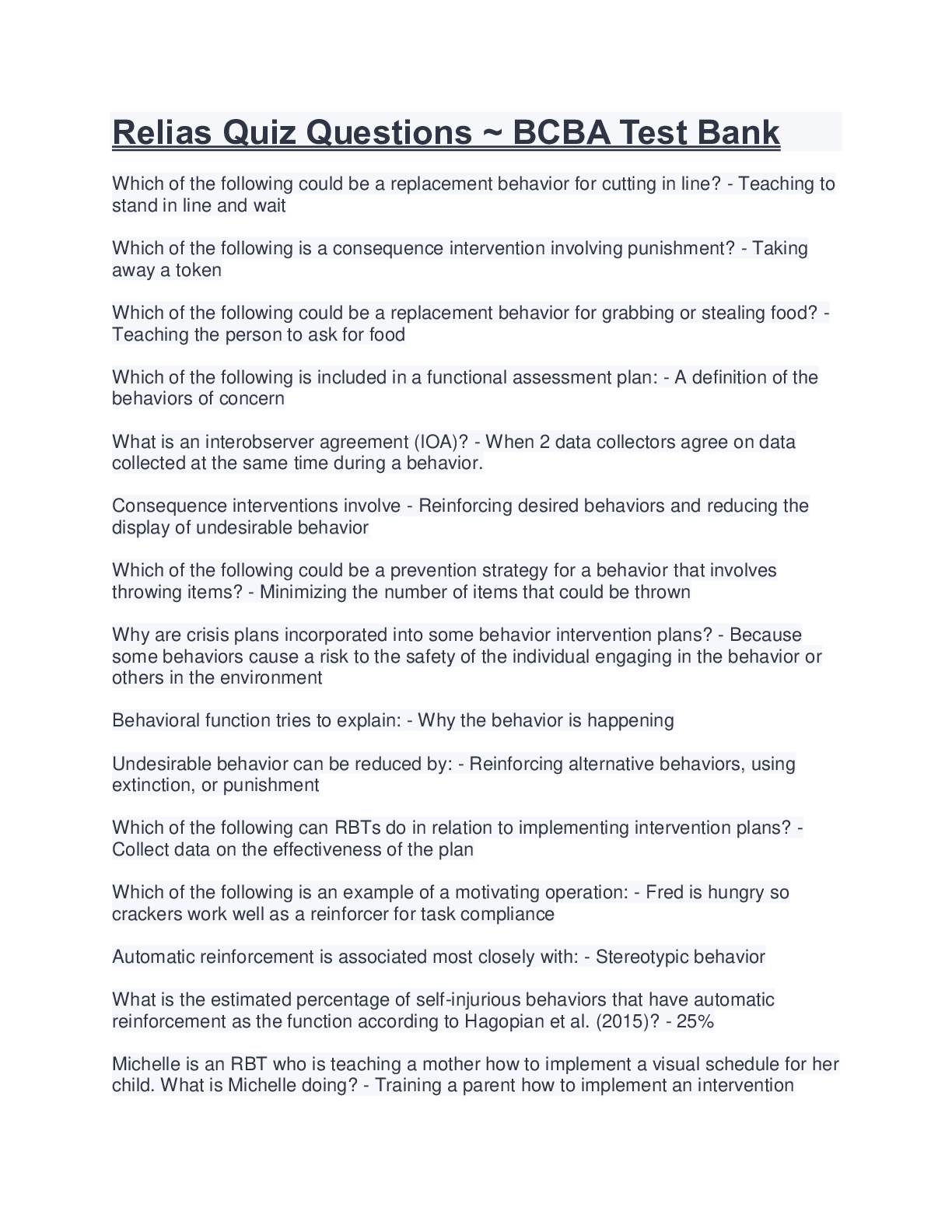
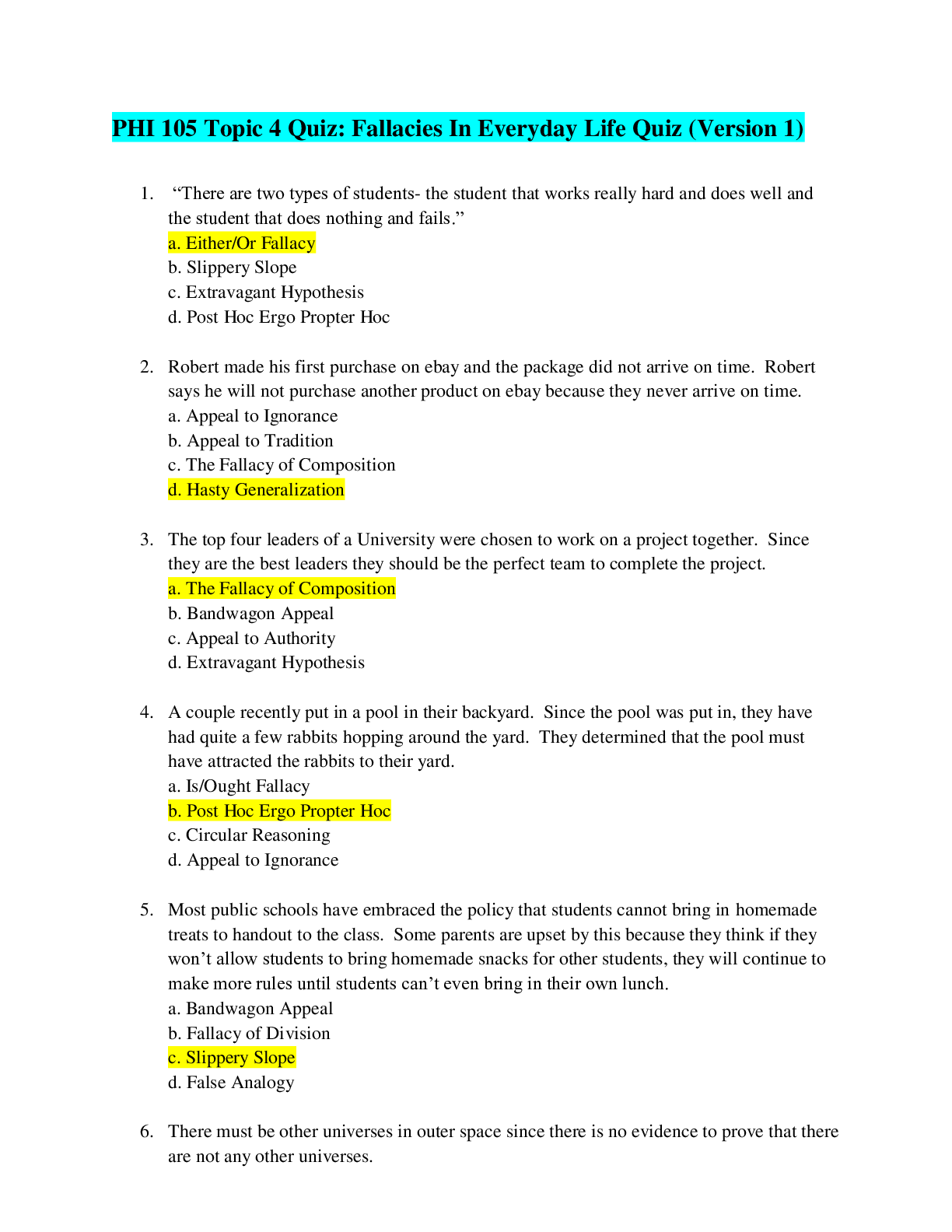

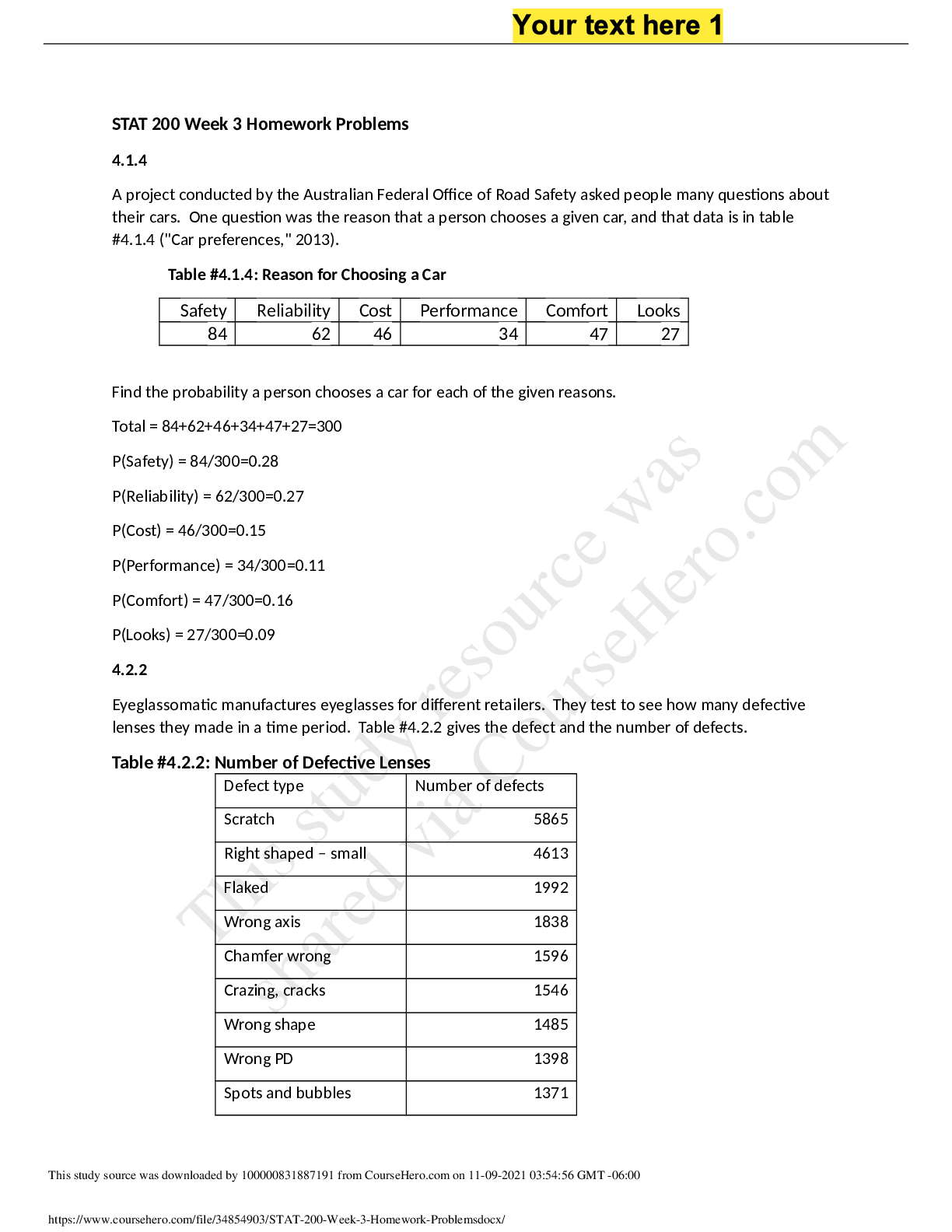
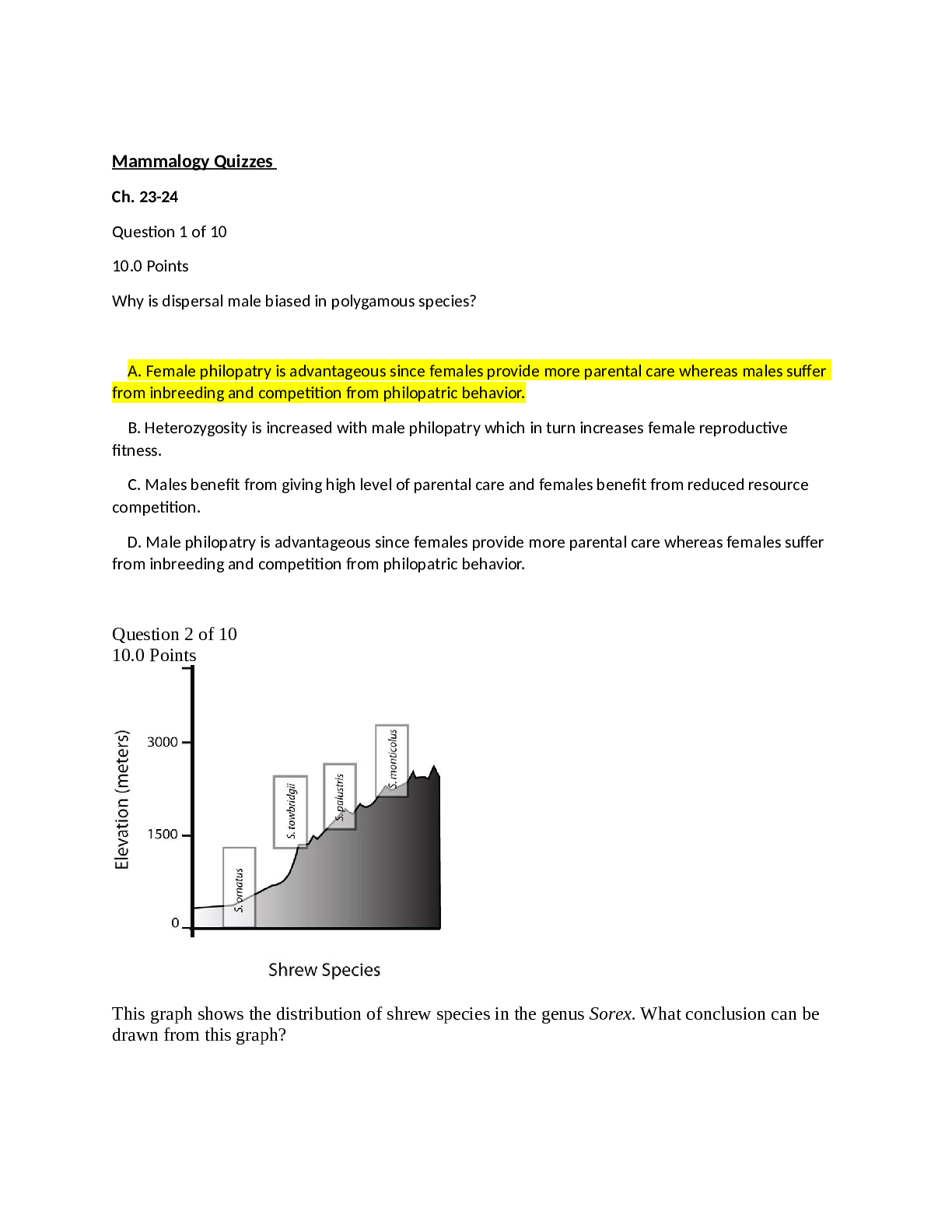
.png)