Information Technology > QUESTIONS & ANSWERS > WGU C961 Ethics in Technology Preassessment Questions and Answers with Complete Solutions (All)
WGU C961 Ethics in Technology Preassessment Questions and Answers with Complete Solutions
Document Content and Description Below
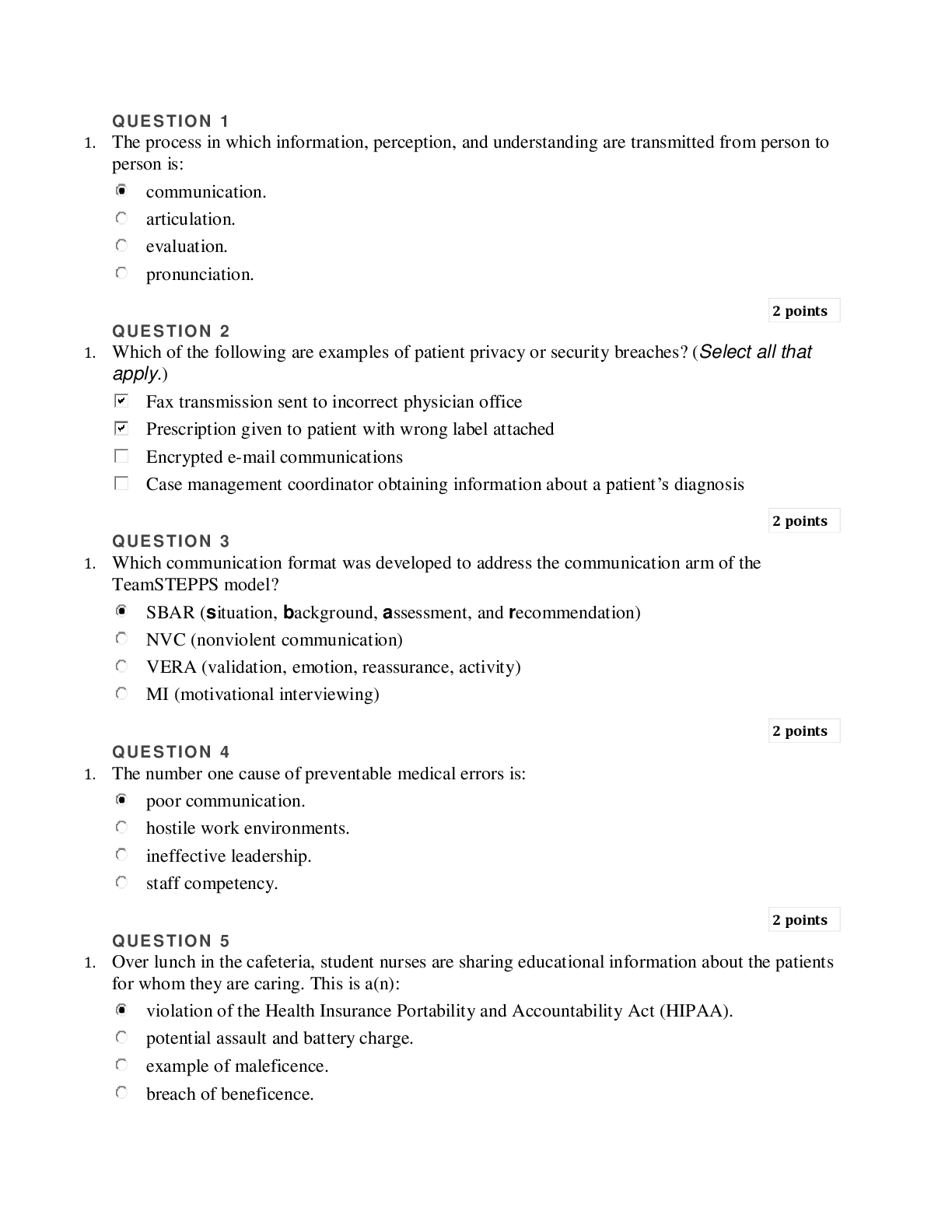
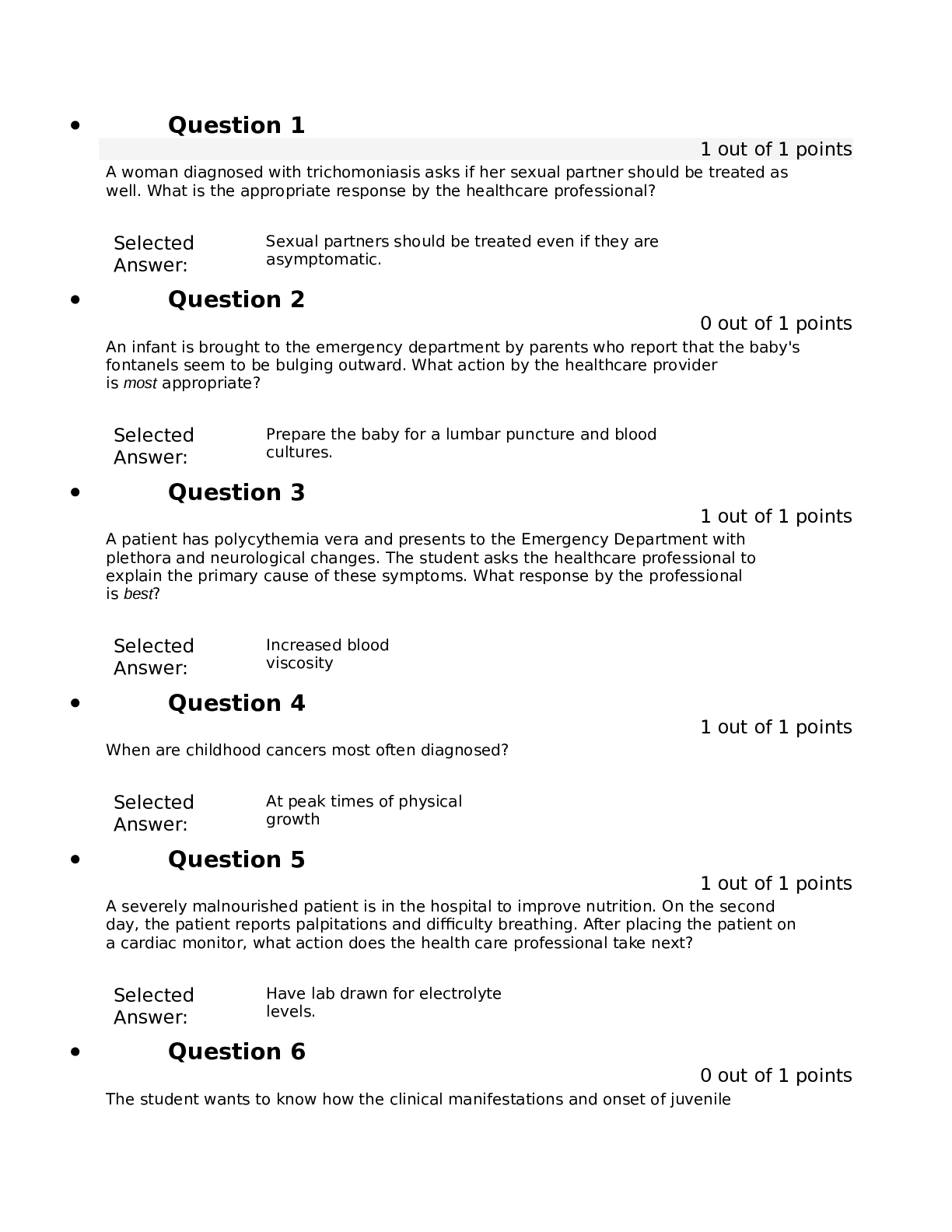
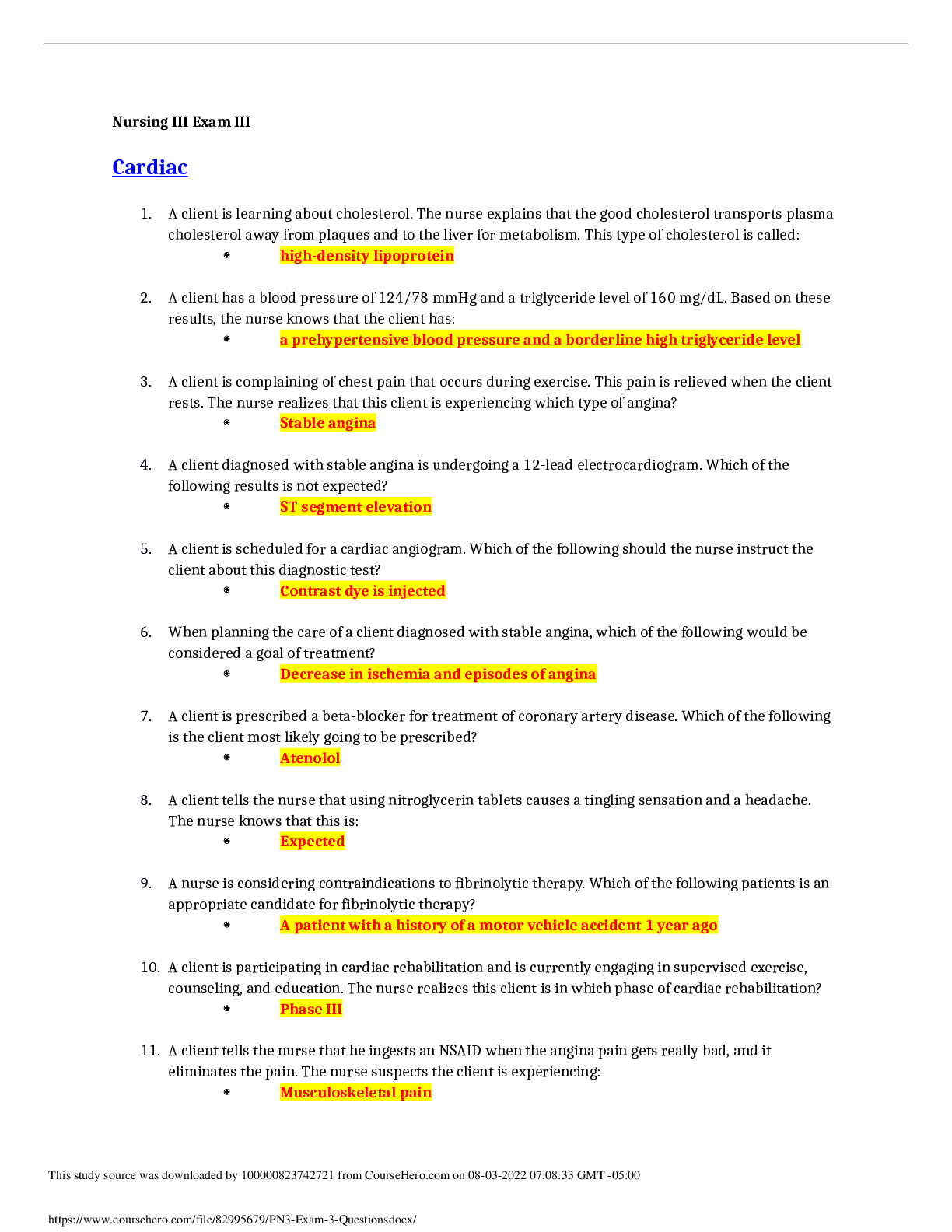
WGU C961 Ethics in Technology Preassessment Questions and Answers with Complete Solutions What does the Bathsheba syndrome refer to? ✔✔Ethical failure of people in power What is defined as a co... ncept by which organizations assimilate social and environmental concerns in their business operations and interactions with their stakeholders? ✔✔CSR (Corporate Social Responsibility) What is an example of corporate social responsibility (CSR)? ✔✔A local IT firm invests in green energy by partnering with a small business to install solar panels in the office. According to Aristotle's virtue ethics, what should be the nature of a person who wants to donate something to an orphanage? ✔✔Tolerant What is one outcome leaders should be aware of when making organizational decisions? ✔✔Increasing profits and revenues A person breaks a traffic law in order to get a critically injured man to a hospital. Which decision-making behavior describes this action? ✔✔Ethical and illegal Why is it important for IT professionals to incorporate good ethical practices? ✔✔So that employees are prepared to handle situations that could lead to misconduct. Why is it important for leaders to understand how technology affects their organization's daily practices? ✔✔To understand possible legal ramificationsWhat is an example of an IT professional demonstrating a commitment to ethics? ✔✔An IT professional wants to do a side project for a local business. He checks his employer's company policy handbook first to avoid a conflict of interest. What does PAPA stand for? ✔✔Privacy, accuracy, property, access Many computer-enabled equipment including tablets, smartphones, and vehicles is used to track the location of users. Corporations issue these devices to their employees to help them perform their jobs more efficiently. IT personnel can work remotely to assist customers and clients with various technology issues and projects. Some professionals are also provided a company-owned vehicle with GPS capabilities, which gives the employer 24/7 access to the employee's movements. What describes an employee's legal rights when an employer is using an auto-tracking device to monitor the employee's whereabouts? ✔✔The employer must obtain employee consent before installing an auto-tracking device. Many computer-enabled equipment including tablets, smartphones, and vehicles is used to track the location of users. Corporations issue these devices to their employees to help them perform their jobs more efficiently. IT personnel can work remotely to assist customers and clients with various technology issues and projects. Some professionals are also provided a company-owned vehicle with GPS capabilities, which gives the employer 24/7 access to the employee's movements. An IT worker uses a company-owned vehicle to transport illegal drugs. How does the use of autotracking devices explain the ethical issue in this scenario? ✔✔An employer can use GPS-tracking data as evidence for the investigation. Many computer-enabled equipment including tablets, smartphones, and vehicles is used to track the location of users. Corporations issue these devices to their employees to help them perform their jobs more efficiently. IT personnel can work remotely to assist customers and clients with various technology issues and projects. Some professionals are also provided a company-owned vehicle with GPS capabilities, which gives the employer 24/7 access to the employee's movements.An IT professional traveling for a work assignment decides to take a detour for personal business and due to excessive speed, causes an auto accident. Who is responsible for damages? ✔✔IT workers who breach the duty of care are accountable for injuries. Many computer-enabled equipment including tablets, smartphones, and vehicles is used to track the location of users. Corporations issue these devices to their employees to help them perform their jobs more efficiently. IT personnel can work remotely to assist customers and clients with various technology issues and projects. Some professionals are also provided a company-owned vehicle with GPS capabilities, which gives the employer 24/7 access to the employee's movements. Many IT professionals feel their privacy is violated when employers use GPS-tracking devices. What describes the employer's point of view? ✔✔Legal and ethical There is a news story about employees of a pharmacy at a local grocery store inadvertently releasing patient information. According to the story, the pharmacy employees printed patient records to review them and later threw them into the grocery store dumpster. Which privacy law was violated by these pharmacy employees? ✔✔HIPAA There is a news story about employees of a pharmacy at a local grocery store inadvertently releasing patient information. According to the story, the pharmacy employees printed patient records to review them and later threw them into the grocery store dumpster. How may the source of this IT issue be described? ✔✔Lack of internal controls There is a news story about employees of a pharmacy at a local grocery store inadvertently releasing patient information. According to the story, the pharmacy employees printed patient records to review them and later threw them into the grocery store dumpster.What explains this ethical issue? ✔✔Inappropriate sharing There is a news story about employees of a pharmacy at a local grocery store inadvertently releasing patient information. According to the story, the pharmacy employees printed patient records to review them and later threw them into the grocery store dumpster. How may the actions of these pharmacy employees be characterized? ✔✔Illegal and unethical The sandwich generation has increased. This generation compromises people who care for elderly parents and children simultaneously. In efforts to manage time effectively, this generation does the majority of work and communication electronically. What can organizations do to assist the sandwich generation in understanding the importance of protecting personal and financial information? ✔✔Have IT, financial, and medical professionals conduct information sessions for the community monthly A major online pet medical record supplier's information system is attacked, and data are stolen about recent pet deaths. The FBI determines that a mall pet store chain has taken the data and used it to send "buy a puppy" solicitations to the owners of the deceased pets. What is the source of the data threat in the scenario? ✔✔Industrial spy A major online pet medical record supplier's information system is attacked, and data are stolen about recent pet deaths. The FBI determines that a mall pet store chain has taken the data and used it to send "buy a puppy" solicitations to the owners of the deceased pets. What is a description of the threat to the data? ✔✔Unintended release of sensitive data or the access of sensitive data by unauthorized individualsJack works in the IT department of a major U.S. bank. The bank has created a mobile application for use by its customers. One of the permissions needed by the application is the location of the bank customer. Jack has decided to share the customer location information with his friend who works for a major hotel chain. The hotel chain will then reach out to the bank customers to offer them a discounted room in the customer's travel area. What is a description of the threat to the customer data? ✔✔Unintended release of sensitive data or the access of sensitive data by unauthorized individuals Jack works in the IT department of a major U.S. bank. The bank has created a mobile application for use by its customers. One of the permissions needed by the application is the location of the bank customer. Jack has decided to share the customer location information with his friend who works for a major hotel chain. The hotel chain will then reach out to the bank customers to offer them a discounted room in the customer's travel area. How should Jack's actions be characterized? ✔✔Illegal and unethical There are eight cities that impose a sugary drink tax. The purpose of this tax is to provide revenue for the city for additional educational support while reducing consumption of sugary drinks. An algorithmic decision-making process is used to collect data from different sources for a research project. The goal of the research project is to explore behaviors of the people in those cities before and after the tax. What can a novice researcher use to ensure data is accurate? ✔✔Sites that promote information accuracy and objectivity There are eight cities that impose a sugary drink tax. The purpose of this tax is to provide revenue for the city for additional educational support while reducing consumption of sugary drinks. An algorithmic decision-making process is used to collect data from different sources for a research project. The goal of the research project is to explore behaviors of the people in those cities before and after the tax.The agency the researcher works for has many resources to mine data. What concerns should this researcher have about these resources? ✔✔Rights and ownership of the data There are eight cities that impose a sugary drink tax. The purpose of this tax is to provide revenue for the city for additional educational support while reducing consumption of sugary drinks. An algorithmic decision-making process is used to collect data from different sources for a research project. The goal of the research project is to explore behaviors of the people in those cities before and after the tax. The researcher is not familiar with IT and visits a data site outside of the resources provided by the organization. Within an hour of access, employees are having difficulties performing job duties because their computer is frozen. The IT department identified the DDoS source and eradicated it. What should this IT department do to avoid this happening again? ✔✔Develop and maintain a risk management plan There are eight cities that impose a sugary drink tax. The purpose of this tax is to provide revenue for the city for additional educational support while reducing consumption of sugary drinks. An algorithmic decision-making process is used to collect data from different sources for a research project. The goal of the research project is to explore behaviors of the people in those cities before and after the tax. Which best practice standard should be enforced to ensure IT personnel are properly trained? ✔✔Reasonable professional standard As more aspects of communication and record keeping become digitized, the relationships between protecting consumer data and privacy grow increasingly complex. The interests of corporations and government agencies must be maintained as well. New questions emerge over how, when and to what extent consumer data are collected, retained, or shared. To mitigate theseconcerns, a variety of regulations have been passed in the United States to protect consumer privacy and ensure accuracy of the data which are harvested. What refers to a general set of guidelines to regulate the collection and use of personal data? ✔✔Fair information practices As more aspects of communication and record keeping become digitized, the relationships between protecting consumer data and privacy grow increasingly complex. The interests of corporations and government agencies must be maintained as well. New questions emerge over how, when and to what extent consumer data are collected, retained, or shared. To mitigate these concerns, a variety of regulations have been passed in the United States to protect consumer privacy and ensure accuracy of the data which are harvested. What is a risk of saving sensitive consumer data without using encryption and other safe archiving methods? ✔✔The data could be accessed by hackers. The leader of an IT department is approached by one of her managers to ask for a salary increase. The manager does a fantastic job of presenting a solid rationale for the increase. At the end his presentation, he says he knows the salaries of all his colleagues because he accessed the payroll file on the company network. Which part of the security triad was violated? ✔✔Confidentiality The leader of an IT department is approached by one of her managers to ask for a salary increase. The manager does a fantastic job of presenting a solid rationale for the increase. At the end his presentation, he says he knows the salaries of all his colleagues because he accessed the payroll file on the company network. [Show More]
Last updated: 1 year ago
Preview 1 out of 17 pages
Instant download
Buy this document to get the full access instantly
Instant Download Access after purchase
Add to cartInstant download
Also available in bundle (2)
WGU C720 Operations and Supply Chain Management BUNDLE – Questions and Answers, 100% ACCURATE. RATED A
COMPRISE OF EXAMINABLE QUESTIONS WITH ACCURATE ANSWERS, RATED A.
By bundleHub Solution guider 1 year ago
$20
21
WGU C961 Ethics in Technology Bundle, Shortcut to score A.
Comprises of study sets and exam questions with accurate answers, rated A, WGU C961 Ethics in Technology Bundle, Shortcut to score A.
By bundleHub Solution guider 1 year ago
$26
9
Reviews( 0 )
Document information
Connected school, study & course
About the document
Uploaded On
Sep 28, 2022
Number of pages
17
Written in
Additional information
This document has been written for:
Uploaded
Sep 28, 2022
Downloads
0
Views
90


 COMPREHENSIVE PREDICTOR ATI 1ST TAKE Questions and Answers with Complete Solutions.png)