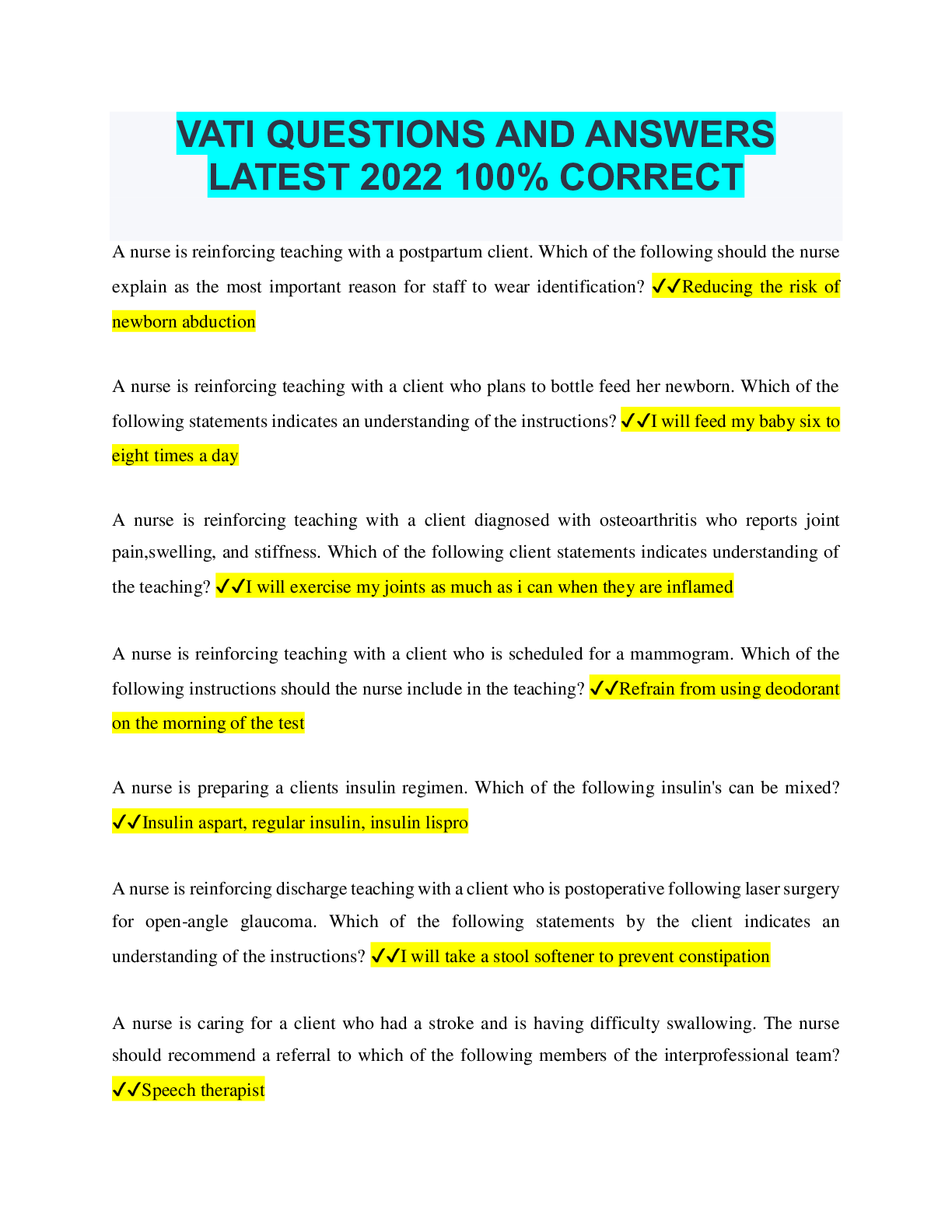
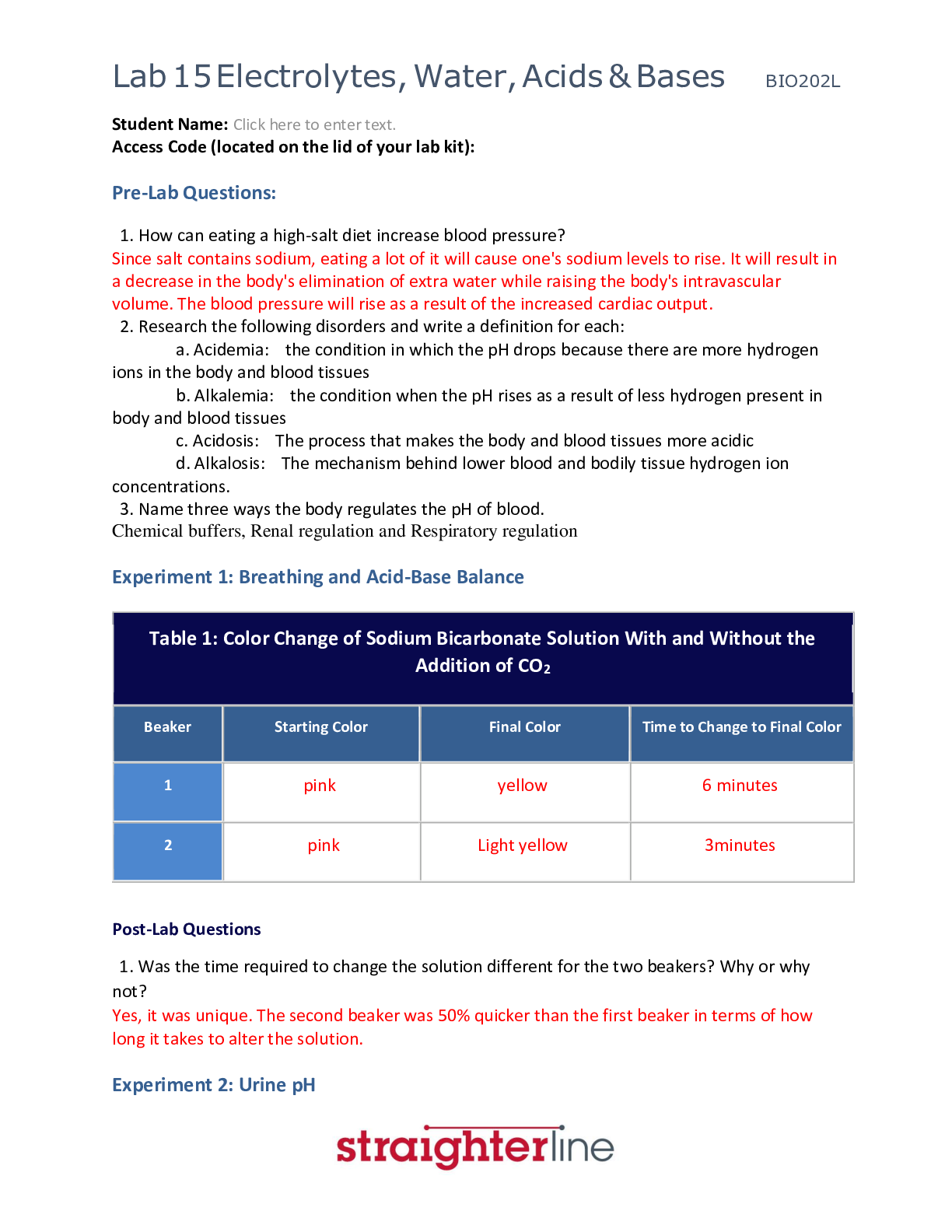
Information Technology > EXAM > ISACA Certified Information Security Manager (CISM) Prep | 40 Questions with 100% Correct Answers | (All)
ISACA Certified Information Security Manager (CISM) Prep | 40 Questions with 100% Correct Answers | Updated & Verified
Document Content and Description Below
Which of the following is the primary step in control implementation for a new business application? - ANS - D. Risk assessment When implementing an information security program, in which phase of t... he implementation should metrics be established to assess the effectiveness of the program over time?" - ANS - Either B. Initiation C. Design Data owners are concerned and responsible for who has access to their resources and therefore need to be concerned with the strategy of how to mitigate risk of data resource usage. Which of the following actions facilitates that responsibility? - ANS - B. Entitlement changes Which of the following is the best method to determine the effectiveness of the incident response process? - ANS - C. Post-incident review When properly implemented, a risk management program should be designed to reduce an organization's risk to: - ANS - C. A level at which the organization is willing to accept What controls the process of introducing changes to systems to ensure that unintended changes are not introduced? - ANS - C. Change management All actions dealing with incidents must be worked with cyclical consideration. What is the primary post-incident review takeaway? - ANS - Either A. Pursuit of legal action [Show More]
Last updated: 1 year ago
Preview 1 out of 6 pages

Reviews( 0 )
Document information
Connected school, study & course
About the document
Uploaded On
Oct 04, 2022
Number of pages
6
Written in
Additional information
This document has been written for:
Uploaded
Oct 04, 2022
Downloads
0
Views
37

.png)
.png)


.png)
.png)
.png)
.png)
.png)