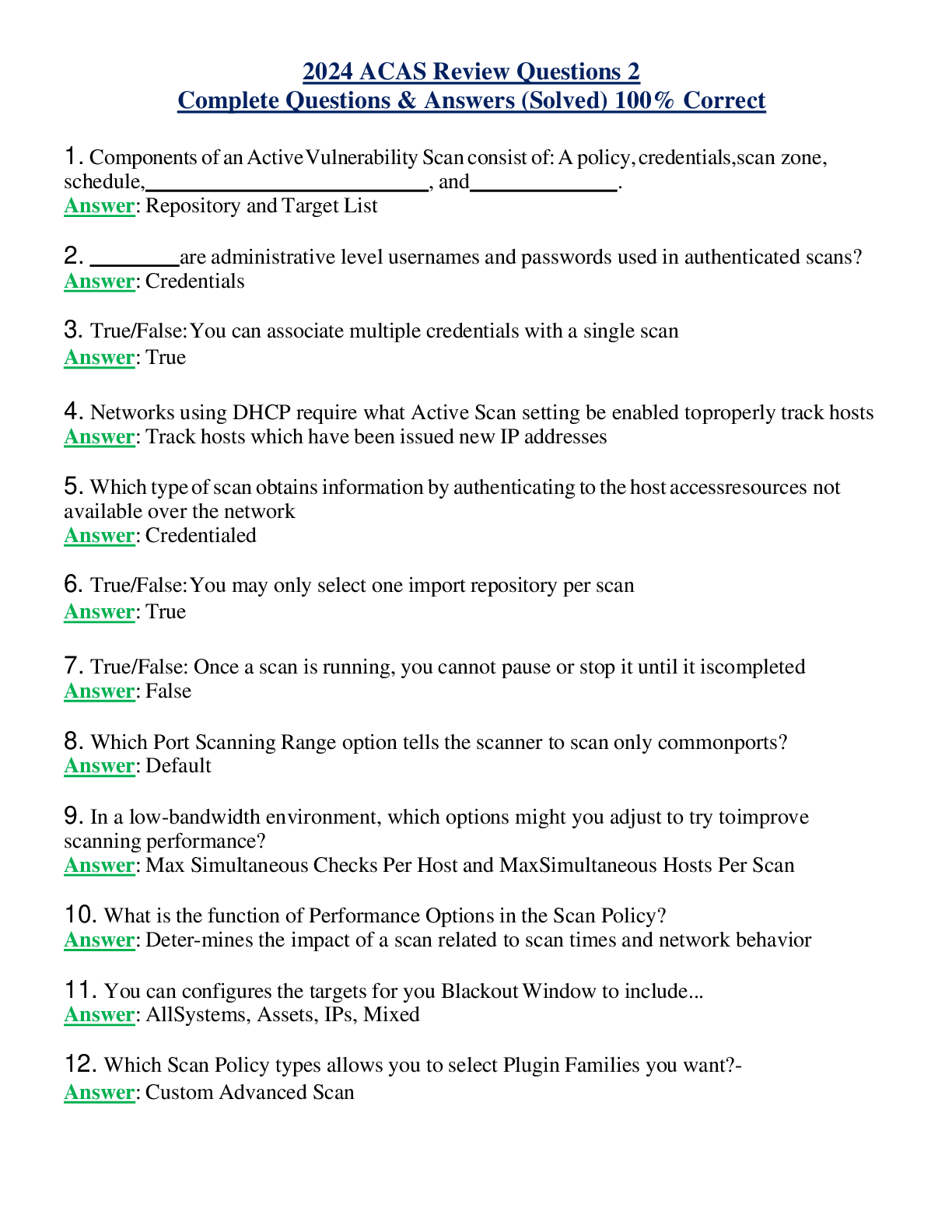
2024 ACAS Review Questions 2 Complete Questions & Answers (Solved) 100% Correct
Document Content and Description Below
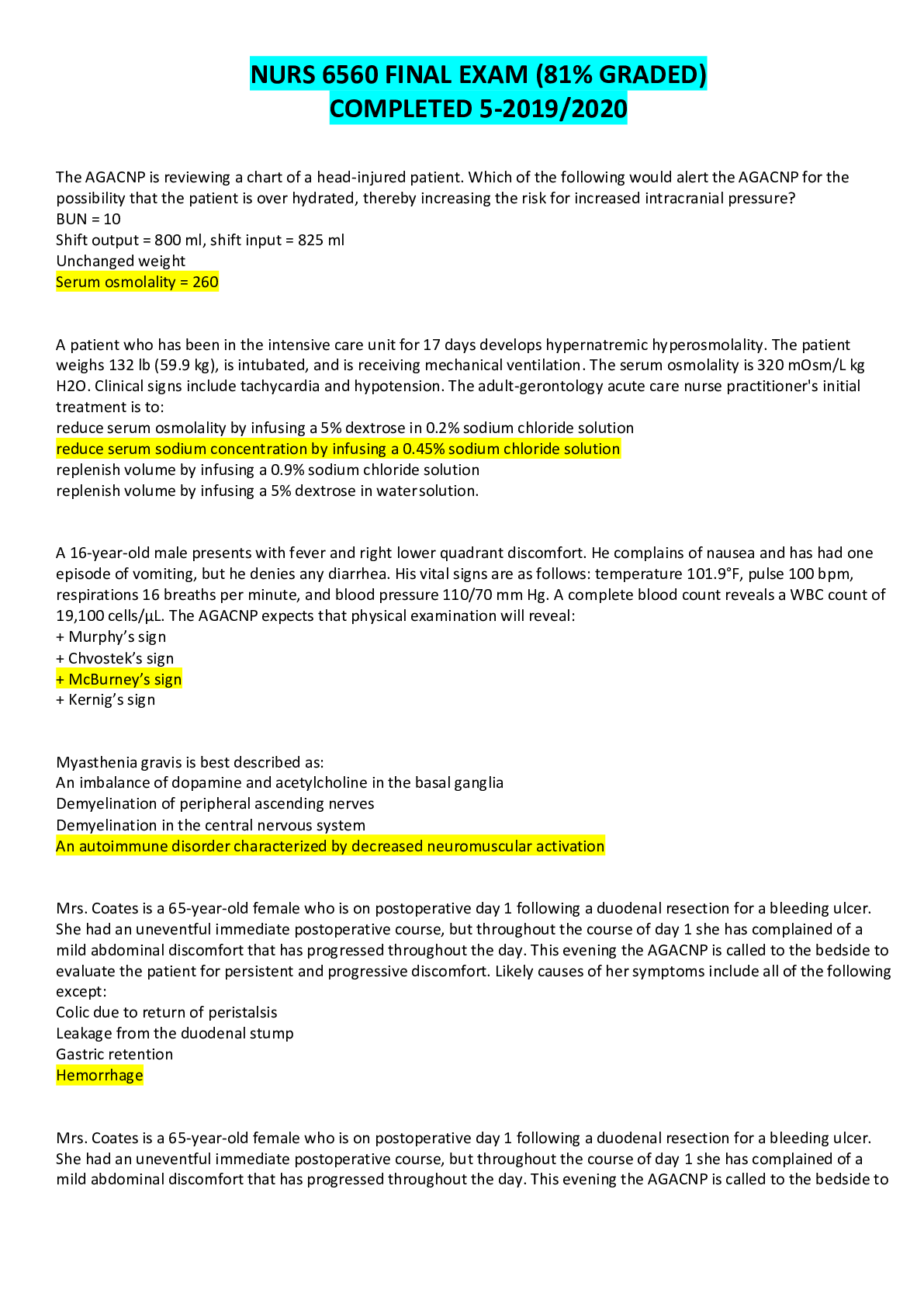
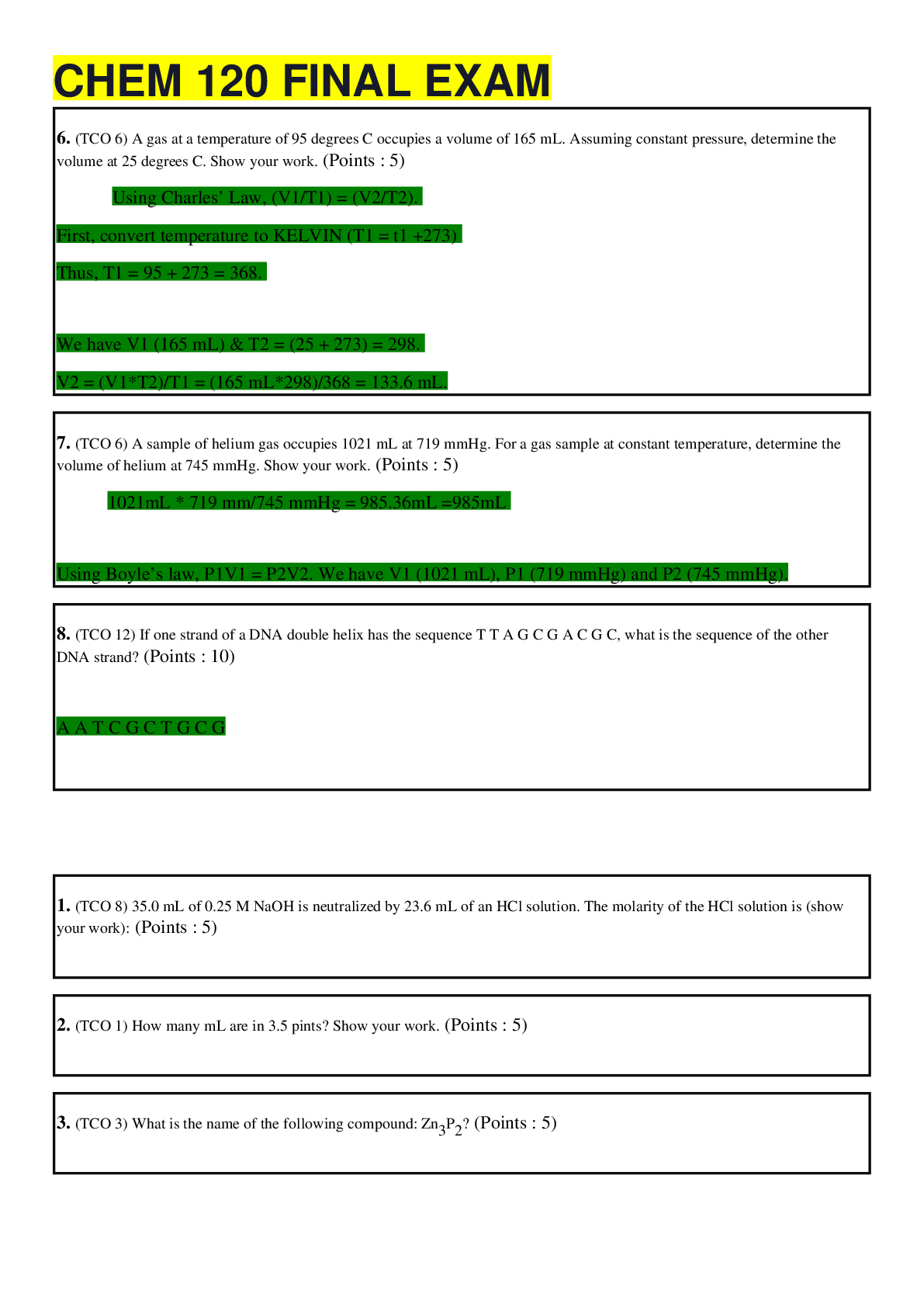
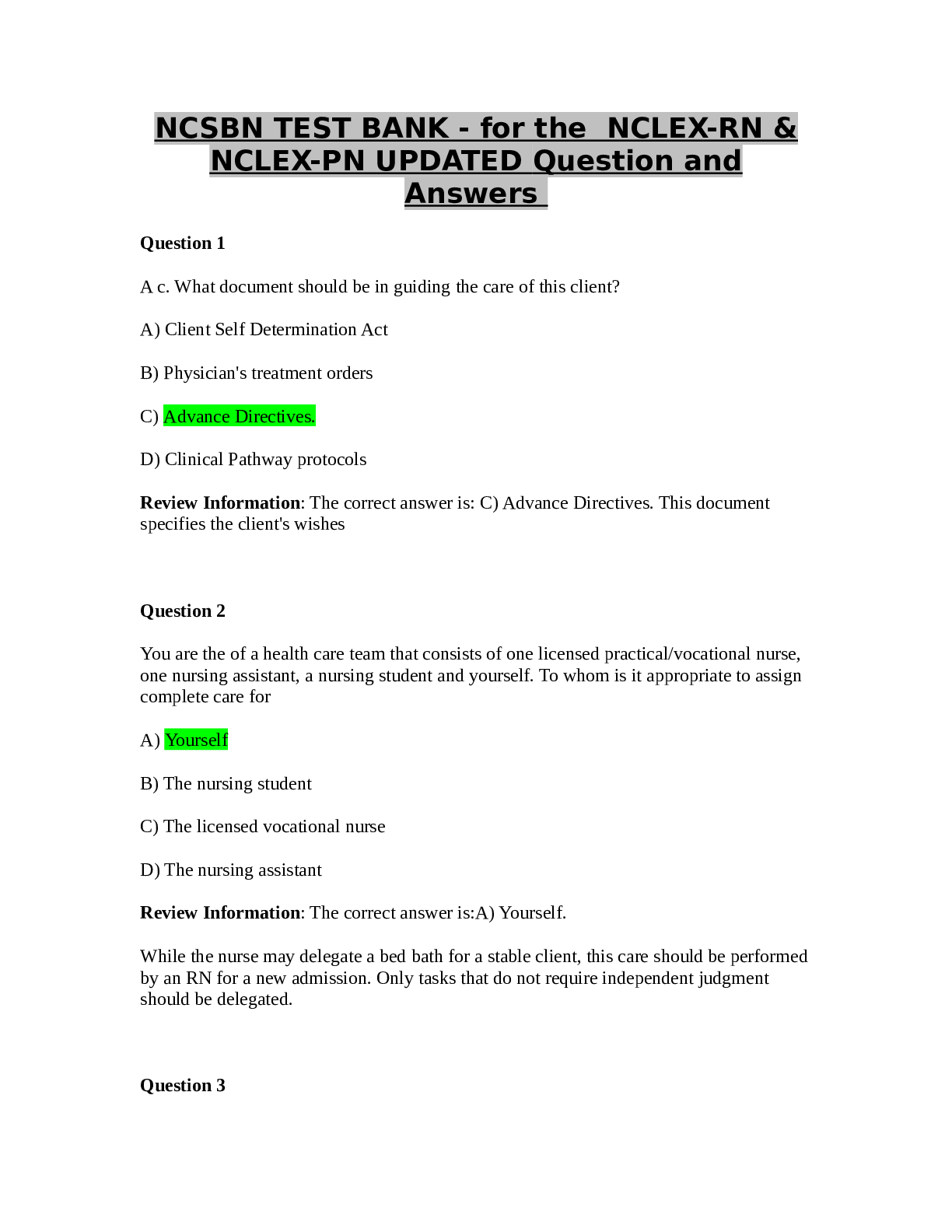
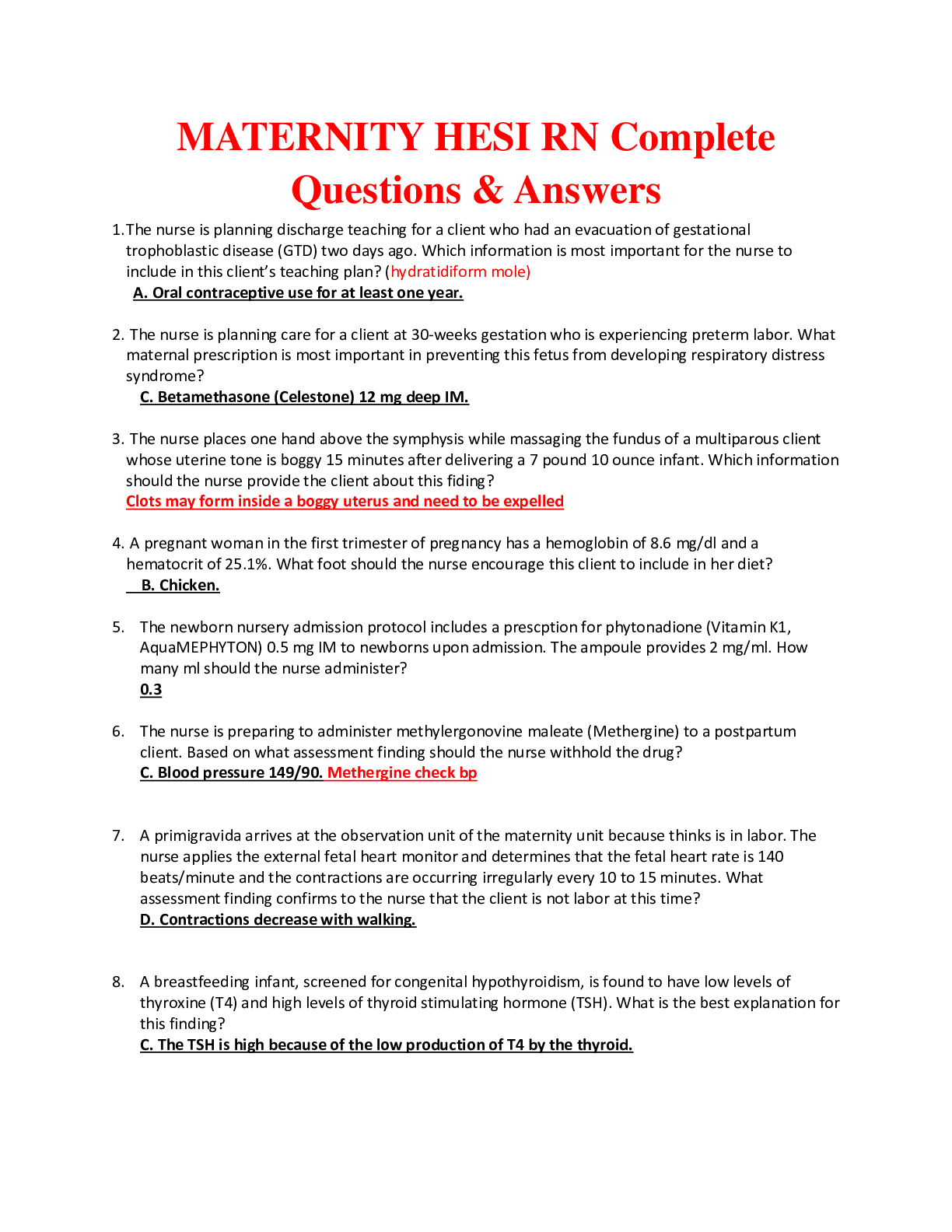
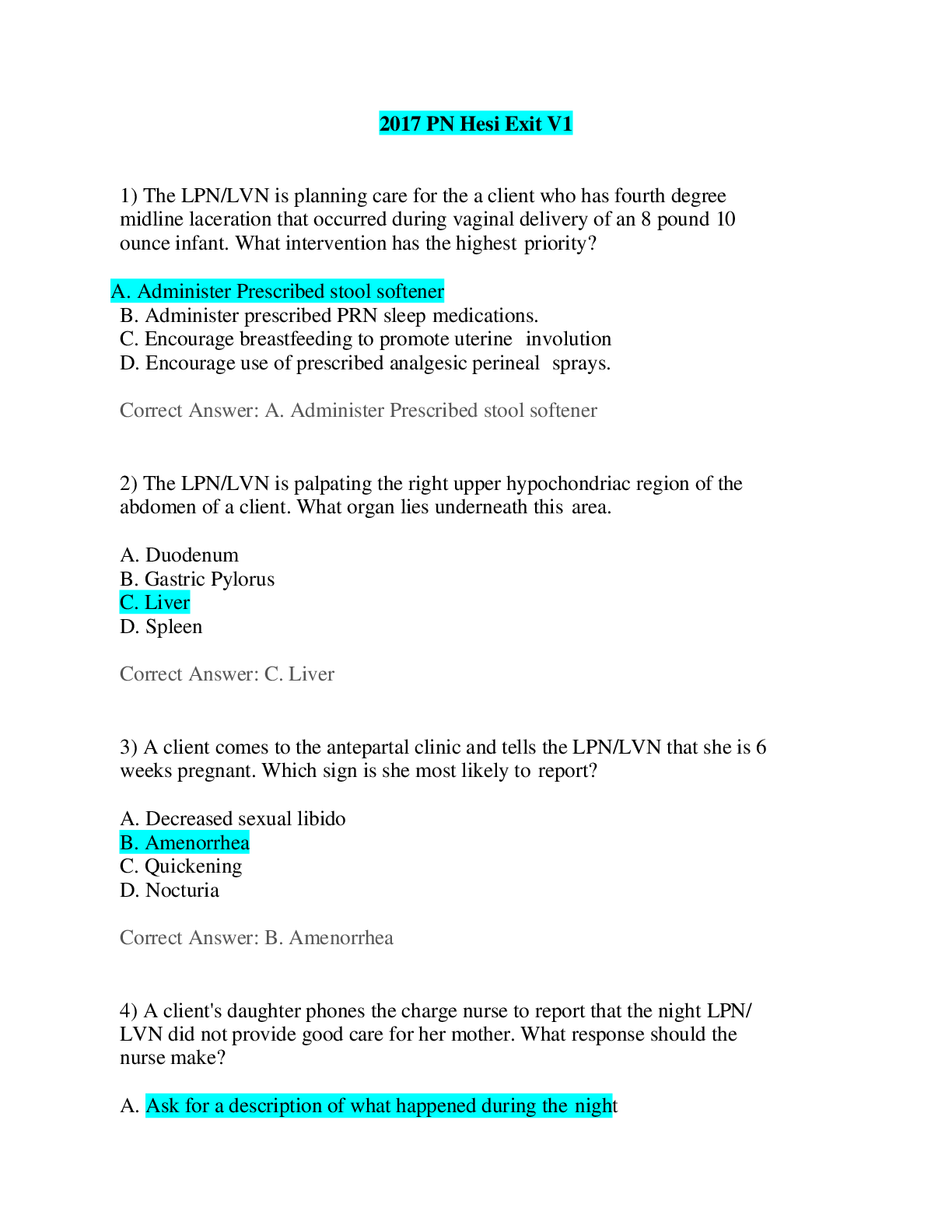
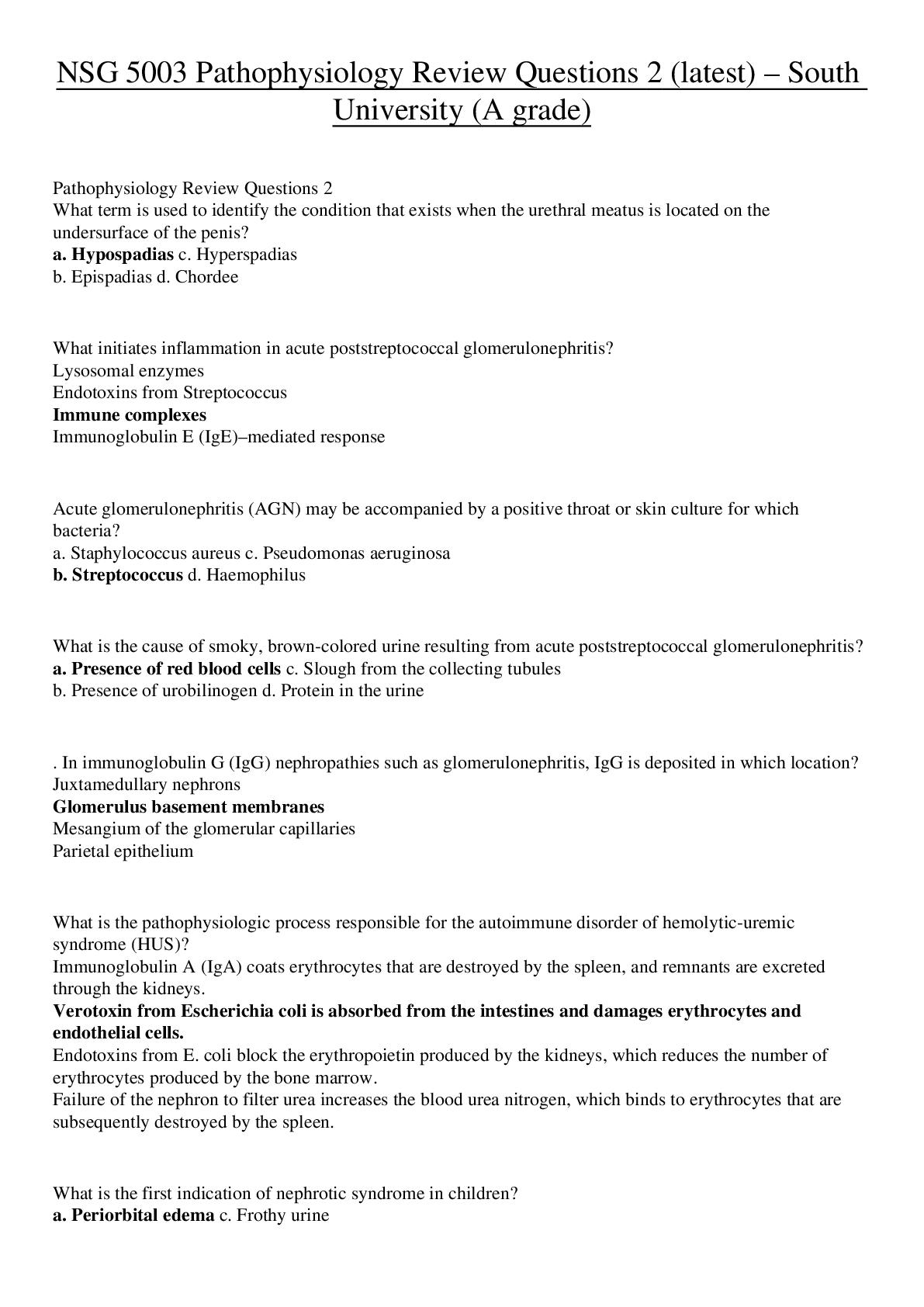
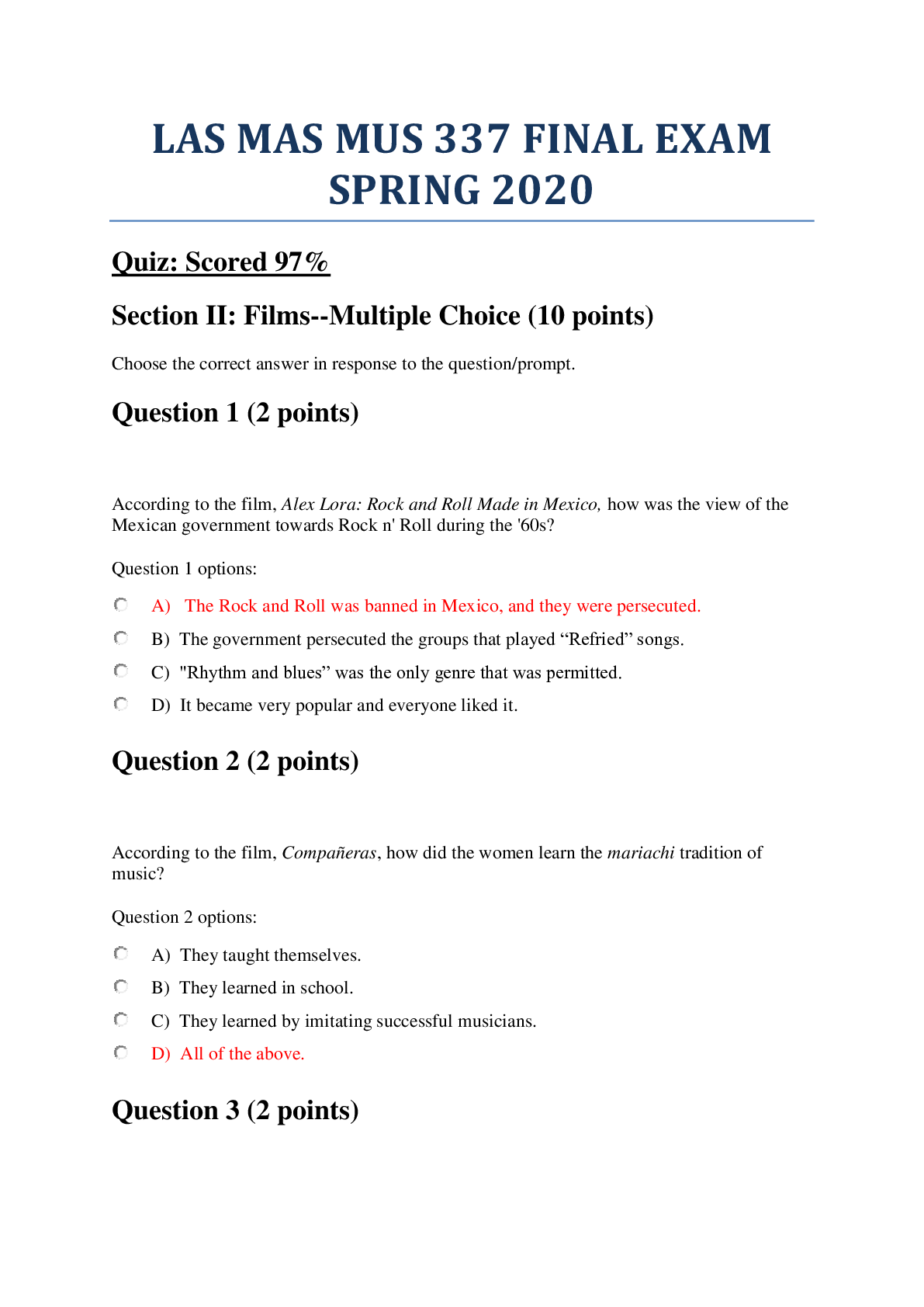
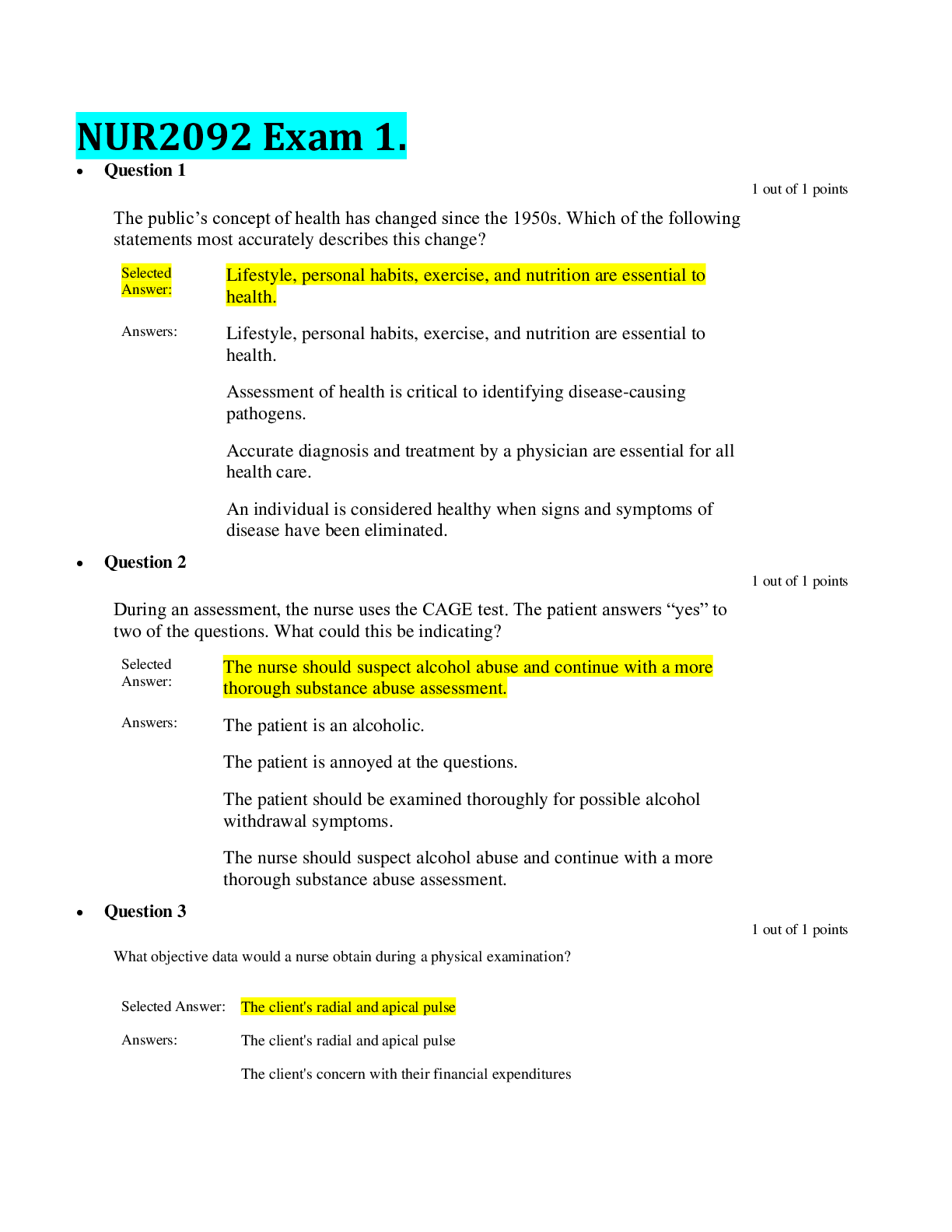
1. Components of an ActiveVulnerability Scan consist of:A policy, credentials,scan zone, schedule, , and . Answer: Repository and Target List 2. are administrative level usernames and passwords use... d in authenticated scans? Answer: Credentials 3. True/False:You can associate multiple credentials with a single scan Answer: True 4. Networks using DHCP require what Active Scan setting be enabled toproperly track hosts Answer: Track hosts which have been issued new IP addresses 5. Which type ofscan obtainsinformation by authenticating to the host accessresources not available over the network Answer: Credentialed 6. True/False:You may only select one import repository per scan Answer: True 7. True/False: Once a scan is running, you cannot pause or stop it until it iscompleted Answer: False 8. Which Port Scanning Range option tells the scanner to scan only commonports? Answer: Default 9. In a low-bandwidth environment, which options might you adjust to try toimprove scanning performance? Answer: Max Simultaneous Checks Per Host and MaxSimultaneous Hosts Per Scan 10. What is the function of Performance Options in the Scan Policy? Answer: Deter-mines the impact of a scan related to scan times and network behavior 11. You can configures the targets for you Blackout Window to include... Answer: AllSystems, Assets, IPs, Mixed 12. Which Scan Policy types allows you to select Plugin Families you want?- Answer: Custom Advanced Scan [Show More]
Last updated: 1 week ago
Preview 1 out of 11 pages
Instant download
Instant download
Reviews( 0 )
Document information
Connected school, study & course
About the document
Uploaded On
May 18, 2024
Number of pages
11
Written in
Additional information
This document has been written for:
Uploaded
May 18, 2024
Downloads
0
Views
4

.png)

.png)