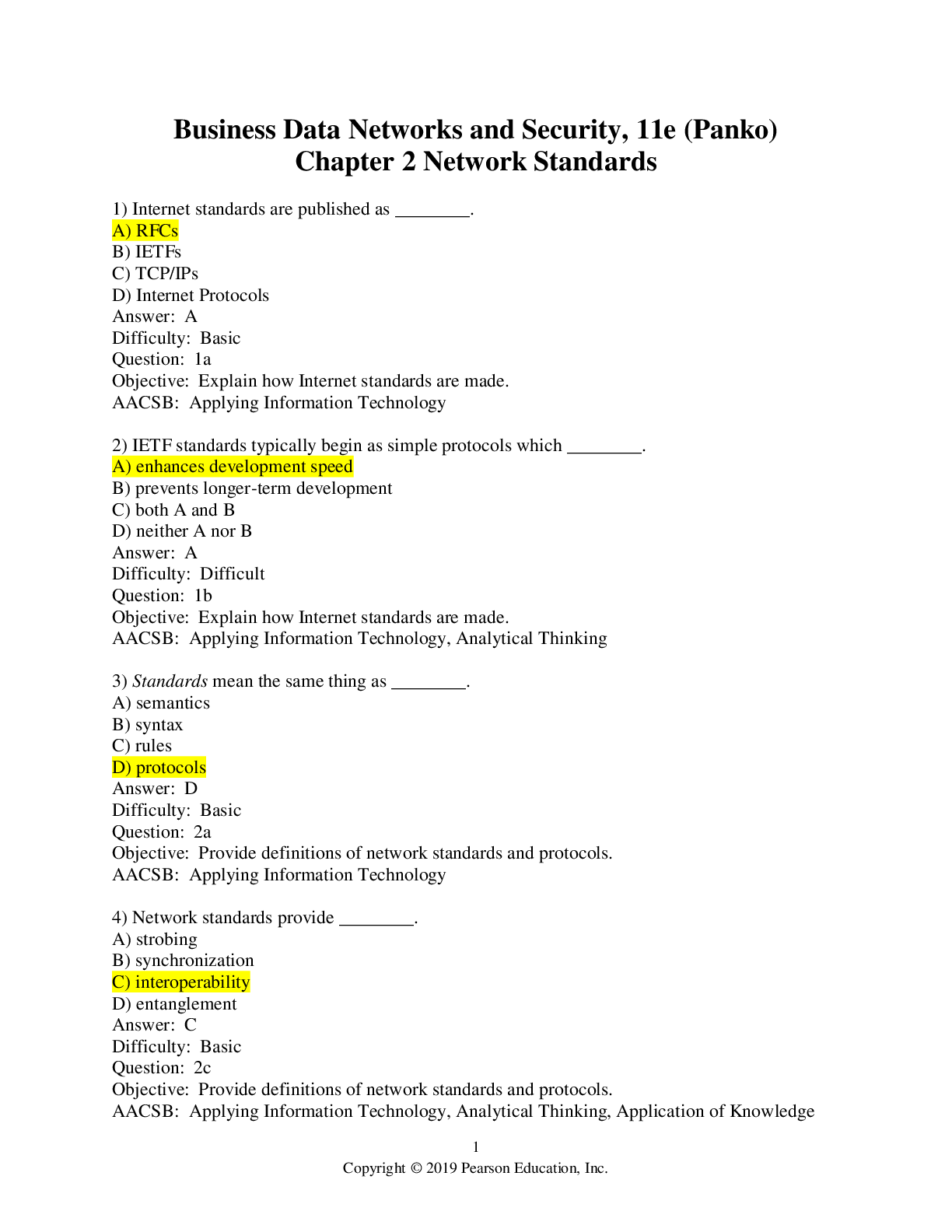
Computer Networking > EXAM > Business Data Networks and Security, 11e (Panko) Chapter 2 Network Standards>Attempt score-100% corr (All)
Business Data Networks and Security, 11e (Panko) Chapter 2 Network Standards>Attempt score-100% correct
Document Content and Description Below
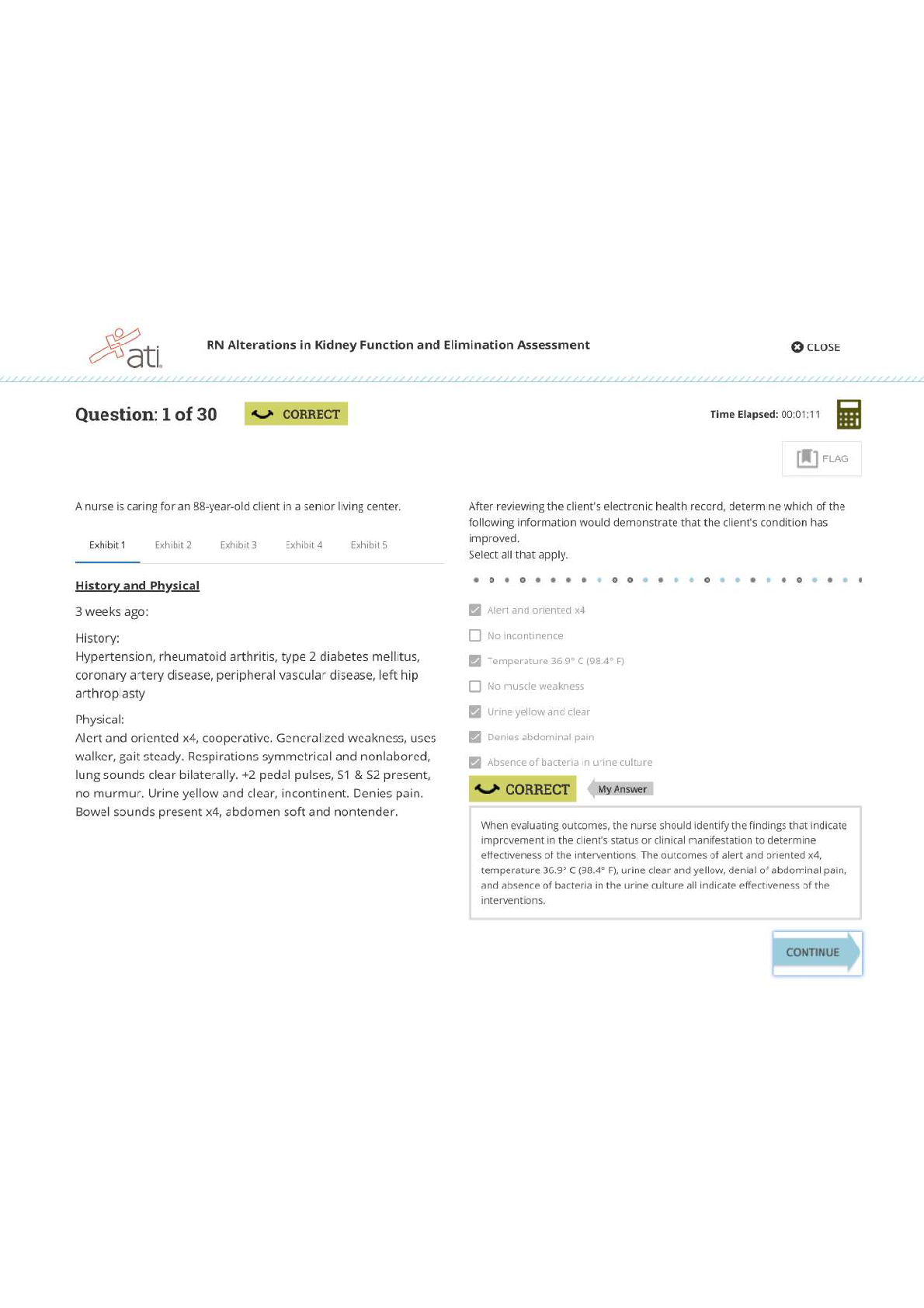
Business Data Networks and Security, 11e (Panko) Chapter 2 Network Standards 1) Internet standards are published as ________. A) RFCs B) IETFs C) TCP/IPs D) Internet Protocols Difficulty: Ba... sic Question: 1a Objective: Explain how Internet standards are made. AACSB: Applying Information Technology 2) IETF standards typically begin as simple protocols which ________. A) enhances development speed B) prevents longer-term development C) both A and B D) neither A nor B Difficulty: Difficult Question: 1b Objective: Explain how Internet standards are made. AACSB: Applying Information Technology, Analytical Thinking 3) Standards mean the same thing as ________. A) semantics B) syntax C) rules D) protocols Difficulty: Basic Question: 2a Objective: Provide definitions of network standards and protocols. AACSB: Applying Information Technology 4) Network standards provide ________. A) strobing B) synchronization C) interoperability D) entanglement Difficulty: Basic Question: 2c Objective: Provide definitions of network standards and protocols. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 5) Network standards ________. A) decrease equipment prices B) prevent the growth of new features C) both A and B D) neither A nor B Difficulty: Difficult Question: 2d Objective: Provide definitions of network standards and protocols. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 6) Which standards agency creates Internet standards? A) OSI B) TCP/IP C) ITU-T D) IETF Difficulty: Basic Question: 3a Objective: Explain standards agencies and architectures. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 7) Which of the following is a standards agency? A) OSI B) TCP/IP C) ITU-T D) all of the above Difficulty: Basic Question: 3b Objective: Explain standards agencies and architectures. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 8) Which standards agency is especially important for internet processes? A) ITU-T B) IETF C) Both A and B are about equally important. D) Neither A nor B are important. Difficulty: Basic Question: 3c Objective: Explain standards agencies and architectures. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 9) Which standards agency is especially important for physical transmission processes? A) ITU-T B) IETF C) Both A and B are about equally important. D) Neither A nor B are important. Difficulty: Basic Question: 3d Objective: Explain standards agencies and architectures. AACSB: Applying Information Technology, Application of Knowledge 10) Which standards agency is especially important for data link processes? A) ISO and ITU-T B) IETF C) Both A and B are about equally important. D) Neither A nor B are important. Difficulty: Basic Question: 3e Objective: Explain standards agencies and architectures. AACSB: Applying Information Technology, Application of Knowledge 11) Which standards agency is especially important for transport processes? A) ISO and ITU-T B) IETF C) Both A and B are about equally important. D) Neither A nor B are important. Difficulty: Basic Question: 3f Objective: Explain standards agencies and architectures. AACSB: Applying Information Technology, Application of Knowledge 12) Which standards agency is especially important for Internet supervisory processes? A) ISO and ITU-T B) IETF C) Both A and B are about equally important. D) Neither A nor B are important. Difficulty: Difficult Question: 3g Objective: Explain standards agencies and architectures. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 13) Standards layers provide services directly to ________. A) the next-higher layer B) the next-lower layer C) all layers D) only themselves Difficulty: Difficult Question: 4b Objective: Explain standards agencies and architectures. AACSB: Applying Information Technology 14) If you change a standard at one layer, you are not required to change standards at other layers. Answer: TRUE Difficulty: Basic Question: 4c Objective: Explain standards agencies and architectures. AACSB: Applying Information Technology 15) It is typically advantageous to change a standard if the layer ________ gets an upgraded standard. A) above it B) below it C) at least two layers away D) none of the above Difficulty: Difficult Question: 4d Objective: Explain standards agencies and architectures. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 16) A standards agency for OSI is ________. A) ITU-T B) IETF C) both A and B D) neither A nor B Difficulty: Basic Question: 5a Objective: Explain standards agencies and architectures. AACSB: Applying Information Technology 17) Which of the following is an architecture? A) ISO B) IETF C) both A and B D) neither A nor B Difficulty: Basic Question: 5b Objective: Explain standards agencies and architectures. AACSB: Applying Information Technology 18) Which of the following is a standards agency for the Internet? A) IETF B) ISO C) both A and B D) neither A nor B Difficulty: Basic Question: 5c Objective: Explain standards agencies and architectures. AACSB: Applying Information Technology 19) From which standards architectures do organizations typically take their standards? A) OSI B) TCP/IP C) both A and B D) neither A nor B Difficulty: Difficult Question: 5d Objective: Explain standards agencies and architectures. AACSB: Applying Information Technology, Application of Knowledge 20) IETF standards are dominant in the OSI-TCP/IP layered standards architecture at the ________ layer. A) data link B) transport C) both A and B D) neither A nor B Difficulty: Basic Question: 5e Objective: Explain standards agencies and architectures. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 21) ISO standards are dominant in the OSI-TCP/IP layered standards architecture at the ________ layer. A) transport B) Internet C) both A and B D) neither A nor B Difficulty: Basic Question: 5f Objective: Explain standards agencies and architectures. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 22) Only applications from the IETF are likely to be able to run over TCP. Answer: FALSE Difficulty: Difficult Question: 5g Objective: Explain standards agencies and architectures. AACSB: Applying Information Technology, Application of Knowledge 23) Which layer governs wires? A) transport B) physical C) Internet D) none of the above Difficulty: Basic Question: 6a Objective: Explain the purpose of each standards layer in the TCP/IP-OSI standards architecture. AACSB: Applying Information Technology, Application of Knowledge 24) Which standards layer governs e-mail? A) data link B) transport C) Internet D) none of the above Difficulty: Difficult Question: 6b Objective: Explain the purpose of each standards layer in the TCP/IP-OSI standards architecture. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 25) Which standards layer governs the World Wide Web? A) data link B) transport C) Internet D) none of the Above Difficulty: Difficult Question: 6b Objective: Explain the purpose of each standards layer in the TCP/IP-OSI standards architecture. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 26) Which standards layer governs peer-to-peer file sharing? A) data link B) transport C) Internet D) none of the Above Difficulty: Difficult Question: 6b Objective: Explain the purpose of each standards layer in the TCP/IP-OSI standards architecture. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 27) Which standards layer governs multiuser word processing programs? A) data link B) transport C) Internet D) none of the Above Difficulty: Difficult Question: 6b Objective: Explain the purpose of each standards layer in the TCP/IP-OSI standards architecture. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 28) Which layer(s) governs transmission through a single network? A) data link B) physical C) both A and B D) neither A nor B Difficulty: Basic Question: 6c Objective: Explain the purpose of each standards layer in the TCP/IP-OSI standards architecture. AACSB: Applying Information Technology 29) Which layer(s) governs transmission through the Internet? A) data link B) physical C) both A and B D) neither A nor B Difficulty: Basic Question: 6d Objective: Explain the purpose of each standards layer in the TCP/IP-OSI standards architecture. AACSB: Applying Information Technology 30) Which layer processes application message fragmentation? A) application B) transport C) Internet D) all of the above Difficulty: Difficult Question: 6e Objective: Explain the purpose of each standards layer in the TCP/IP-OSI standards architecture. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 31) The application layer processes application message fragmentation. Difficulty: Difficult Question: 6e Objective: Explain the purpose of each standards layer in the TCP/IP-OSI standards architecture. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 32) At what layer will you find standards for routers? A) transport B) Internet C) both A and B D) neither A nor B Difficulty: Difficult Question: 7a Objective: Explain the purpose of each standards layer in the TCP/IP-OSI standards architecture. AACSB: Applying Information Technology, Application of Knowledge 33) At what layer will you find standards for access points? A) physical B) data link C) both A and B D) neither A nor B Difficulty: Basic Question: 7b Objective: Explain the purpose of each standards layer in the TCP/IP-OSI standards architecture. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 34) At what layer will you find standards for packets? A) application B) data link C) transport D) Internet Difficulty: Basic Question: 7c Objective: Explain the purpose of each standards layer in the TCP/IP-OSI standards architecture. AACSB: Applying Information Technology, Application of Knowledge 35) At what layer will you find standards for switches? A) application B) data link C) transport D) Internet Difficulty: Basic Question: 7d Objective: Explain the purpose of each standards layer in the TCP/IP-OSI standards architecture. AACSB: Applying Information Technology, Application of Knowledge 36) At what layer will you find standards for frames? A) application B) data link C) transport D) Internet Difficulty: Basic Question: 7e Objective: Explain the purpose of each standards layer in the TCP/IP-OSI standards architecture. AACSB: Applying Information Technology, Application of Knowledge 37) At what layer will you find standards for IP addresses? A) application B) data link C) transport D) Internet Difficulty: Basic Question: 7f Objective: Explain the purpose of each standards layer in the TCP/IP-OSI standards architecture. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 38) At what layer will you find standards for routes? A) application B) data link C) transport D) Internet Difficulty: Basic Question: 7g Objective: Explain the purpose of each standards layer in the TCP/IP-OSI standards architecture. AACSB: Applying Information Technology, Application of Knowledge 39) At what layer will you find standards for EUI-48 addresses? A) application B) data link C) transport D) Internet Difficulty: Basic Question: 7h Objective: Explain the purpose of each standards layer in the TCP/IP-OSI standards architecture. AACSB: Applying Information Technology, Application of Knowledge 40) If two hosts are connected by five networks, how many packets will there be when one host sends a packet to the other host? A) 1 B) 2 C) 5 D) 7 Difficulty: Difficult Question: 8a Objective: Explain the purpose of each standards layer in the TCP/IP-OSI standards architecture. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 41) If two hosts are connected by five networks, how many frames will there be when one host sends a packet to the other host? A) 1 B) 2 C) 5 D) 6 Difficulty: Difficult Question: 8b Objective: Explain the purpose of each standards layer in the TCP/IP-OSI standards architecture. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 42) If two hosts are connected by five networks, how many routers will there be when one host sends a packet to the other host? A) 1 B) 2 C) 4 D) 5 Difficulty: Difficult Question: 8c Objective: Explain the purpose of each standards layer in the TCP/IP-OSI standards architecture. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 43) If two hosts are connected by five point-to-point networks, how physical links will there be when one host sends a packet to the other host? A) 1 B) 2 C) 5 D) 6 Difficulty: Difficult Question: 8d Objective: Explain the purpose of each standards layer in the TCP/IP-OSI standards architecture. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 44) In an HTTP, which one (browser or Webserver application program) transmits message first? A) browser B) Webserver application program C) They transmit simultaneously. D) It depends on the situation. Difficulty: Basic Question: 9a Objective: Explain message ordering in HTTP and TCP. AACSB: Applying Information Technology, Application of Knowledge 45) In HTTP, which program may initiate communication? A) browser B) Webserver program C) both A and B D) neither A nor B Difficulty: Difficult Question: 9a Objective: Explain message ordering in HTTP and TCP. AACSB: Applying Information Technology, Application of Knowledge 46) HTTP is a connectionless protocol. Difficulty: Basic Question: 9b Objective: Explain message ordering in HTTP and TCP. AACSB: Applying Information Technology 47) HTTP is a reliable protocol. Difficulty: Basic Question: 9c Objective: Explain message ordering in HTTP and TCP. AACSB: Applying Information Technology 48) HTTP is ________. A) connection-oriented. B) reliable C) both A and B D) neither A nor B Difficulty: Basic Question: 9c Objective: Explain message ordering in HTTP and TCP. AACSB: Applying Information Technology 49) TCP messages are called ________. A) frames B) packets C) segments D) fragments Difficulty: Basic Question: 10a Objective: Explain message ordering in HTTP and TCP. AACSB: Applying Information Technology 50) Host P transmits a SYN segment to Host Q. If host Q is willing to open the connection, it will transmit a(n) ________ segment. A) ACK B) SYN C) SYN/ACK D) none of the above Difficulty: Basic Question: 10b Objective: Explain message ordering in HTTP and TCP. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 51) If a destination host does not receive a segment, it will ________. A) transmit an ACK segment B) transmit a NAC segment C) transmit an RSND segment D) none of the above Difficulty: Basic Question: 10c Objective: Explain message ordering in HTTP and TCP. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 52) If a destination host receives a TCP segment with an error, it will transmit ________. A) an ACK segment B) an NAC segment C) an RSND segment D) nothing Difficulty: Basic Question: 10c Objective: Explain message ordering in HTTP and TCP. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 53) TCP control segments normally have ________. A) headers B) headers and data fields C) headers, data fields, and trailers D) none of the above Difficulty: Difficult Question: 10d Objective: Explain message ordering in HTTP and TCP. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 54) TCP is a connection-oriented protocol. Difficulty: Basic Question: 11a Objective: Explain message ordering in HTTP and TCP. AACSB: Applying Information Technology 55) During a connection opening, how many TCP segments will the side that initiates the connection send? A) 1 B) 2 C) 3 D) 4 Difficulty: Difficult Question: 11c Objective: Explain message ordering in HTTP and TCP. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 56) If a destination host receives a correct segment, it will transmit ________. A) an ACK segment B) an NAC segment C) an RSND segment D) nothing Difficulty: Basic Question: 12a Objective: Explain message ordering in HTTP and TCP. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 57) If a destination host does not receive a segment, it will ________. A) transmit an ACK segment B) transmit an NAC segment C) transmit an RSND segment D) none of the above Difficulty: Basic Question: 12b Objective: Explain message ordering in HTTP and TCP. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 58) If a destination host receives an incorrect segment, it will ________. A) transmit an ACK segment B) transmit an NAC segment C) transmit an RSND segment D) none of the above Difficulty: Basic Question: 12c Objective: Explain message ordering in HTTP and TCP. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 59) A sending host will retransmit a TCP segment if it ________. A) receives an ACK segment B) receives an NAC segment C) receives an RPT segment D) none of the above Difficulty: Basic Question: 12d Objective: Explain message ordering in HTTP and TCP. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 60) In a four-step close, which side transmits a FIN segment? A) the side that initiates the close B) the side that does not initiate the close C) both A and B D) neither A nor B Difficulty: Difficult Question: 13a Objective: Explain message ordering in HTTP and TCP. AACSB: Applying Information Technology, Application of Knowledge 61) After the side wishing to close a TCP connection sends a FIN segment, it will ________. A) not send any more segments B) only send ACK segments C) only send FIN segments D) none of the above Difficulty: Difficult Question: 13b Objective: Explain message ordering in HTTP and TCP. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 62) Which of the following is NOT one of the three general parts of messages? A) address field B) header C) data field D) trailer Difficulty: Difficult Question: 14a Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 63) The ________ contains the content being delivered by a message. A) address field B) header C) data field D) trailer Difficulty: Basic Question: 14b Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology 64) A header is defined as everything that comes before the data field. Difficulty: Basic Question: 14c Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology 65) A message always has a ________. A) header B) data field C) both A and B D) neither A nor B Difficulty: Difficult Question: 14c Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 66) There is always a data field in a message. Difficulty: Basic Question: 14d Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 67) A trailer is defined as everything that comes after the data field. Difficulty: Basic Question: 14e Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology 68) Which part of a message is included less frequently when compared to the other two parts? A) header B) data field C) trailer D) All of the above are equally included in messages. Difficulty: Basic Question: 14f Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology 69) "Header" means the same thing as "Header Field." Difficulty: Difficult Question: 14g Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 70) In IP, the first bit in the second row is ________. A) 0 B) 31 C) 32 D) none of the above. Difficulty: Basic Question: 15a Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology, Analytical Thinking 71) The internet process checks for errors. Difficulty: Difficult Question: 15c Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 72) If the destination internet process detects an error, it ________. A) discards the packet B) sends back a segment notifying the sender C) both A and B D) neither A nor B Difficulty: Difficult Question: 15d Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology, Application of Knowledge 73) IP is ________. A) reliable B) unreliable C) semi-reliable D) unreliable or reliable depending on the situation Difficulty: Basic Question: 15f Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 74) Which of the following is a connectionless protocol? A) IP B) TCP C) both A and B D) neither A nor B Difficulty: Difficult Question: 15g Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology, Application of Knowledge 75) TCP has single-bit fields in its headers; these single-bit fields are called ________ fields. A) port B) flag C) ACK D) binary Difficulty: Basic Question: 16a Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology 76) If someone says that a 1-bit flag is set, it is given the value ________. A) 0 B) 1 C) either 0 or 1 D) neither 0 or 1 Difficulty: Basic Question: 16b Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology 77) SYN segments have ________. A) headers B) headers and data fields C) headers, data fields, and trailers D) data fields only Difficulty: Difficult Question: 16f Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology, Analytical Thinking 78) A TCP segment can both send information and acknowledge an earlier message sent to its host. Difficulty: Basic Question: 16g Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology 79) The UDP header has ________ fields. A) 4 B) 8 C) 16 D) 32 Difficulty: Difficult Question: 17a Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology, Application of Knowledge 80) UDP ________. A) is unreliable B) has a checksum field C) both A and B D) neither A nor B Difficulty: Difficult Question: 17d Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 81) On a server, well-known port numbers indicate ________. A) applications B) connections with client computers C) both A and B D) neither A nor B Difficulty: Difficult Question: 18a Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology, Application of Knowledge 82) For every conversation, a client randomly generates an ephemeral port number for ________. A) applications B) conversations C) the server D) none of the above Difficulty: Difficult Question: 18b Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology, Application of Knowledge 83) The range of port 1024 to port 4999 is the usual range for ________ port numbers. A) well-known B) ephemeral C) both A and B D) neither A nor B Difficulty: Difficult Question: 18c Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology 84) 2500 is in the range for ________ port numbers. A) well-known B) ephemeral C) both A and B D) neither A nor B Difficulty: Difficult Question: 18d Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology 85) The source socket is 60.171.18.22:2707. The source is a(n) ________. A) client B) server C) well-known server D) ephemeral server Difficulty: Difficult Question: 19a Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 86) The destination socket is 60.171.18.22:161. The destination host is a(n) ________. A) client B) server C) well-known server D) ephemeral server Difficulty: Difficult Question: 19a Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 87) Which of the following is a socket? A) 80 B) 21 C) both A and B D) neither A nor B Difficulty: Difficult Question: 19a Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 88) "Octet" is the same as ________. A) "bit" B) "byte" C) either A or B, depending on the context D) neither A nor B Difficulty: Basic Question: 20a Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology 89) Ethernet syntax is displayed 32 bits on a line. Difficulty: Difficult Question: 20a Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology, Application of Knowledge 90) In the Ethernet II frame, the IP packet is carried in the ________ field. A) source address B) destination address C) data D) EtherType Difficulty: Basic Question: 20b Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology 91) The IP standard calls for IP packets to be carried in the Ethernet II version of the Ethernet frame. Difficulty: Basic Question: 20c Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology 92) To know what kind of message is in the Ethernet II data field, the receiver must look in the ________ field. A) source address B) destination address C) data D) EtherType Difficulty: Basic Question: 20d Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology 93) Ethernet has a Frame Check Sequence Field to check for errors. Ethernet is ________. A) reliable B) unreliable C) both A and B D) neither A nor B Difficulty: Difficult Question: 20e Objective: Explain message syntax in common network standards. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 94) Converting application messages into bits is called ________. A) encapsulation B) encryption C) encoding D) exchange Difficulty: Difficult Question: 21a Objective: Explain how application programs encode data into binary representation. AACSB: Applying Information Technology 95) At what layer is encoding done? A) application B) transport C) Internet D) none of the above Difficulty: Difficult Question: 21b Objective: Explain how application programs encode data into binary representation. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 96) How many bytes will it take to transmit "Brain Dead" without the quotation marks? A) 2 B) 3 C) 9 D) none of the above Difficulty: Difficult Question: 22b Objective: Explain how application programs encode data into binary representation. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 97) Transmitting "Oh, My!" without the quotes in ASCII requires ________ octets. A) 2 B) 4 C) 6 D) 7 Difficulty: Difficult Question: 22c Objective: Explain how application programs encode data into binary representation. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 98) Which of the following is an integer? A) 4,307 B) 45.7 C) both A and B D) neither A nor B Difficulty: Basic Question: 23a Objective: Explain how application programs encode data into binary representation. AACSB: Applying Information Technology, Application of Knowledge 99) Which of the following is an integer? A) 5,280 B) 98.6 C) both A and B D) neither A nor B Difficulty: Basic Question: 23b Objective: Explain how application programs encode data into binary representation. AACSB: Applying Information Technology, Application of Knowledge 100) Convert decimal 8 to binary. A) 100 B) 1000 C) 10000 D) 111 Difficulty: Difficult Question: 23e Objective: Explain how application programs encode data into binary representation. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 101) Convert a decimal number 15 to the binary number. A) It is a binary number. B) 1100 C) 1101 D) 1111 Difficulty: Difficult Question: 23g Objective: Explain how application programs encode data into binary representation. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 102) Convert the binary number 100 to decimal. A) It is in decimal. B) 2 C) 4 D) 8 Difficulty: Difficult Question: 23k Objective: Explain how application programs encode data into binary representation. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 103) In decimal, the binary number 110 is ________. A) 15 B) 16 C) 17 D) none of the above Difficulty: Difficult Question: 23k Objective: Explain how application programs encode data into binary representation. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 104) A 5-bit field can represent ________ alternatives or different combinations. A) 8 B) 16 C) 32 D) 64 Difficulty: Difficult Question: 24a Objective: Explain how application programs encode data into binary representation. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 105) If you add one bit to an alternatives field, you can have ________. A) one more alternative B) two more alternatives C) twice as many alternatives D) none of the above Difficulty: Basic Question: 24b Objective: Explain how application programs encode data into binary representation. AACSB: Applying Information Technology, Analytical Thinking 106) How many alternatives can you represent with a 10-bit field? A) 256 B) 512 C) 1,024 D) none of the above Difficulty: Difficult Question: 24c Objective: Explain how application programs encode data into binary representation. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 107) To represent 65 alternatives, your alternatives field would have to be at least ________ bits long. A) 5 B) 6 C) 7 D) 8 Answer: C Difficulty: Difficult Question: 24d Objective: Explain how application programs encode data into binary representation. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 108) The five senses can be represented with a ________-bit field. A) 2 B) 3 C) 4 D) 5 Difficulty: Difficult Question: 24e Objective: Explain how application programs encode data into binary representation. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 109) In TCP, port number fields are 16 bits long. How many possible port numbers are there? A) 16 B) 1,024 C) 16,384 D) 64,536 Answer: D Difficulty: Basic Question: 24a Objective: Explain how application programs encode data into binary representation. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 110) ASCII has a 7-bit code. How many keyboard characters can it represent? A) 128 B) 256 C) 512 D) 1,024 Answer: A Difficulty: Difficult Question: 24e Objective: Explain how application programs encode data into binary representation. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge 111) Which of the following protocols is reliable? A) IP B) TCP C) both A and B D) neither A nor B Answer: B Difficulty: Basic Question: 25a Objective: Explain how application programs encode data into binary representation. AACSB: Applying Information Technology, Application of Knowledge 112) Not making all protocols reliable ________. A) reduces cost B) is very dangerous C) is widely viewed as having been a mistake D) none of the above Answer: A Difficulty: Difficult Question: 25b Objective: Explain how application programs encode data into binary representation. AACSB: Applying Information Technology, Analytical Thinking, Application of Knowledge [Show More]
Last updated: 1 year ago
Preview 1 out of 28 pages
Reviews( 0 )
Document information
Connected school, study & course
About the document
Uploaded On
Sep 18, 2019
Number of pages
28
Written in
Additional information
This document has been written for:
Uploaded
Sep 18, 2019
Downloads
0
Views
65



 Chapter 5 Ethernet (802.png)