Computer Science > QUESTIONS & ANSWERS > EC Council - Certified Encryption Specialist Latest 2023 Graded A (All)
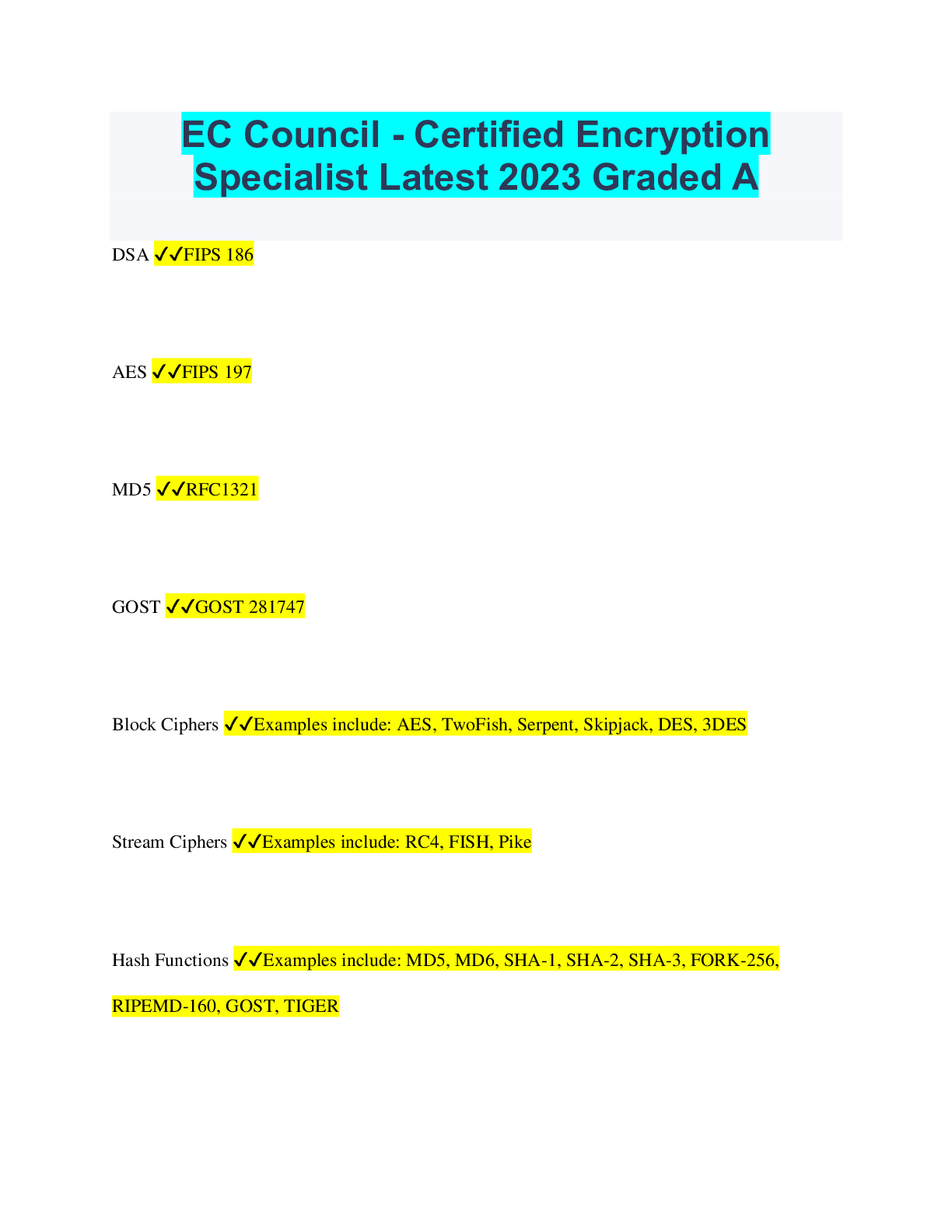
EC Council - Certified Encryption Specialist Latest 2023 Graded A
Document Content and Description Below
EC Council - Certified Encryption Specialist Latest 2023 Graded A DSA ✔✔FIPS 186 AES ✔✔FIPS 197 MD5 ✔✔RFC1321 GOST ✔✔GOST 281747 Block Ciphers ✔✔Examples include: AES, TwoFis... h, Serpent, Skipjack, DES, 3DES Stream Ciphers ✔✔Examples include: RC4, FISH, Pike Hash Functions ✔✔Examples include: MD5, MD6, SHA-1, SHA-2, SHA-3, FORK-256, RIPEMD-160, GOST, TIGER Asymmetric cryptography ✔✔Also called public key cryptography Symmetric Stream Cipher ✔✔Also called State Ciphers Symmetric cryptography ✔✔Single private key used to encrypt and decrypt Random Number Generators ✔✔Table look-up, Hardware, Algorithmic (software) K1 ✔✔Random numbers with low probability of identical consecutive elements K2 ✔✔Random numbers indistinguishable from "true random" numbers K3 ✔✔Impossible for attacker to calculate or guess previous/future number in sequence K4 ✔✔Impossible for attacker to calculate or guess from inner state of the generator any previous numbers or previous inner generator states Crypography ✔✔Study of message security Cryptography ✔✔In practice for over 3000 years, mostly by military or governments until the late 20th century Plain text ✔✔Unaltered text Cipher text ✔✔Encrypted text Mono-Alphabet Substitution ✔✔Examples include: Caesar, Atbash, ROT13 Caesar ✔✔Cipher used by Julius Caesar Caesar ✔✔Cipher where every letter in message is shifted a fixed x number to the right or left Mono-Alphabet Substitution ✔✔Type of Algorithm which substitutes 1 character of cipher text for 1 character of plain text Mono-Alphabet Substitution ✔✔Category of algorithms that are primitive, not secure and subject to frequency attacks Atbash ✔✔Cipher used by Hebrew scholars copying the book of Jeremiah from the Bible Atbash ✔✔Cipher where alphabet is reversed ROT13 ✔✔Cipher where letters are rotated 13 characters Scytale ✔✔Cipher used by the greeks and described in the 7th century by Archilochus Scytale ✔✔Cipher where parchment is wrapped around a rod; the recipient must have a matching rod of the same diameter and a leather "key" is wrapped around to decode the message Multi-Alphabet Subsitution ✔✔Examples include: CipherDisk, Vigenere, Playfair, ADFGVX, Enigma, TypeX, and SIGABA CipherDisk ✔✔Created by Leon Alberti in 1466 CipherDisk ✔✔Poly-alphabetic cipher where a disk is turned to encrypt plain text Vigenere ✔✔Invented in 1553 by Giovan Battista Bellaso Vigenere ✔✔Most widely known poly-alphabet cipher Vigenere ✔✔Uses series of different mono-alphabet ciphers based on the letters of the keyword Vigenere ✔✔Fredrich Kasiski published an attack on this cipher in 1863 Playfair ✔✔Created in 1854 by Charles Wheatstone Playfair ✔✔This cipher encrypts 2 letters at a time vs 1 and uses 5x5 table with a key word or phrase Playfair ✔✔This mono-alphabet cipher is more complex than other historical ciphers, but not more secure. ADFGVX ✔✔Created by Colonel Fritz Nebel in 1918 ADFGVX ✔✔Used by the German Army in WWI ADFGVX ✔✔Based on ADFGX Enigma Machine ✔✔Electromechanical rotor based cipher used by the Germans in WWII TypeX ✔✔Used by the British in WWII SIGABA ✔✔Used by the Americans in WWII Cryptography ✔✔Science of altering communication so it cannot be understood without a key Key ✔✔The random bits used in encrypting a message Algorithm ✔✔The mathematical process used to alter a message and read it unintelligible by any but the intended party Encryption ✔✔Converting plain text to ciphertext Decryption ✔✔Converting cipher text to plain text Symmetric ✔✔symmetric or asymmetric? Faster to encrypt/decrypt, issue of key exchange Asymmetric ✔✔symmetric or asymmetric? Slower to encrypt/decrypt, more secure key exchange Information Theory ✔✔Introduced by Claude Shannon in the publication "Communication Theory of Secrecy Systems" in the Bell System Technical Journal in 1949 Diffusion ✔✔Changes to 1 character in plain text affect multiple characters in cipher text Confusion ✔✔Statistical frequencies of the cipher text and key as complex as possible Avalanche ✔✔Small change yields large effects in output (Fiestal's variation on Diffusion) Kerckhoffs Principle ✔✔Modern cryptography is NOT based on keeping the algorithm secret; should be secure even if everything about the system is known but the key Transposition ✔✔Swapping blocks of cipher text Substitution ✔✔Changing some part of the plain text for some matching part of cipher text Binary XOR ✔✔1st Number: 1101 2nd Number: 0110 Result: 0100 Binary OR ✔✔1st Number: 1101 2nd Number: 0110 Result: 1111 Binary AND ✔✔1st Number: 1100 2nd Number: 0110 Result: 0101 Block Cipher ✔✔Encrypt data in blocks Stream Cipher ✔✔Encrypt the data as a stream 1 bit at a time Feistal Function ✔✔Larger block sizes more secure Larger key sizes more secure If the round function is secure, more rounds increase security Feistal Function ✔✔Forms the basis of most symmetric block ciphers Cipher ✔✔The algorithm(s) needed to encrypt/decrypt the message Round Function ✔✔A function performed with each iteration, or round, of the Feistel cipher Feistal Function ✔✔Block of plain text -- 1/2 of block L0 -- 1/2 of block R0 --> 1/2 of block L0 --> Round Function F --> Round Function F --> XOR <-- 1/2 of block R0 = Output of XOR of Output of F and R0 Unbalanced Feistal cipher ✔✔Uses a modified structure where L0 and R0 are not of equal lengths DES ✔✔Data Encryption Standard DES ✔✔Developed by IBM in the early 1970s Block cipher Feistal cipher DES ✔✔64 bit blocks 56 bit key 3DES ✔✔Uses a key bundle which is comprised of 3 DES keys K1, K2, K3 56 bit DES key DESx ✔✔Variation of DES that simply XORs another 64-bit key to the plaintext before applying the DES algorithm Key Whitening ✔✔XORing in an additional key AES ✔✔Advanced Encryption Standard AES ✔✔Also known as Rijndael block cipher AES ✔✔128 bit blocks 128, 192 or 256 bit key sizes AES ✔✔Uses substitution-permutation matrix The State ✔✔4x4 column-major order matrix of bytes Rijndael S-box ✔✔In the SubBytes step, each byte in the matrix is substituted for another byte using an 8-bit substitution box 256 bit ✔✔Key size of AES used for top secret data Blowfish ✔✔Created in 1993 by Bruce Schneier Blowfish ✔✔16 round Feistal cipher Blowfish ✔✔64 bit blocks 32-448 bit variable length key Blowfish ✔✔Block cipher in the public domain Serpent ✔✔Created by Ross Anderson, Eli Biham, Lars Knudsen Serpent ✔✔128 block size 128, 192, 256 bit key Serpent ✔✔AES Finalist Execute in parallel Sub permutation network Twofish ✔✔AES contest finalist Feistel cipher Twofish ✔✔128 bit block up to 256 bit key Twofish ✔✔Created by Bruce Schneier, John Kelsey, Doug Whiting, David Wagner, Chris Hall, and Niels Ferguson Skipjack ✔✔Developed by the NSA for the clipper chip Skipjack ✔✔Controversial as decryption key in escrow for law enforcement Skipjack ✔✔64 bit block 80 bit key Skipjack ✔✔Unbalanced Feistal network IDEA ✔✔Created by James Massey and Xuejia Lai in 1991 IDEA ✔✔64 bit blocks 128 bit keys ECB ✔✔Electronic Codebook ECB ✔✔Most basic encryption mode Message divided into blocks and each block is encrypted separately Weakness is same plain text always equals the same cipher text CBC ✔✔Cipher Block Chaining CBC ✔✔Each block of plain text is XORed with the and is the most common mode PCBC ✔✔Propagating Cipher-Block Chaining PCBC ✔✔Sometimes called plain text cipher-block chaining PCBC ✔✔Variation of CBC Not formally published as a federal standard PCBC ✔✔Designed to cause small changes in the cipher text to propagate indefinitely when decrypting, as well as when encrypting CFB ✔✔Cipher Feedback CFB ✔✔The previous ciphertext block is encrypted then the ciphertext produced is XORed back with the plaintext to produce the current ciphertext block OFB ✔✔Output feedback OFB ✔✔Turns a block cipher into a synchronous stream cipher It generates keystream blocks, which are then XORed with the plaintext blocks to get the ciphertext CTR ✔✔Counter CTR ✔✔used to turn a block cipher into a stream cipher. This is used to turn a block cipher into a stream cipher, much like much like OFB mode. CTR generates the next keystream block by encrypting successive values of a "counter." The counter can be any simple function that produces a sequence that is guaranteed not to repeat for a long time. IV ✔✔Initialization Vector IV ✔✔Fixed-size input to a cryptographic primitive that is random or pseudo-random Nonce ✔✔Number used once Self-synchronizing stream ciphers ✔✔sometimes also called asynchronous stream ciphers or ciphertext autokey (CTAK) RC4 ✔✔Ron Rivest created this algorithm in 1987 RC4 ✔✔The algorithm is used identically for encryption and decryption as the data stream is simply XORed with the key RC4 ✔✔variable length key from 1 to 256 bytes uses key scheduling algorithm KSA ✔✔Key scheduling algorithm PRGA ✔✔Pseudo-random generation algorithm FISH ✔✔Created by Siemans in 1993 FISH ✔✔Fibonacci shrinking FISH ✔✔SW based stream cipher Lagged Fibonacci generator Vulnerable to plain text attacks PIKE ✔✔Created by Ross Anderson PIKE ✔✔Faster and stronger than FISH Hash Function ✔✔Function takes a variable size input and returns a fixed size string Hash formula ✔✔h = H(m) Hash Function ✔✔One way Collision free Salt ✔✔Random bits intermixed with hash message MD5 ✔✔Created by Ron Rivist in 1991 MD5 ✔✔Replaced MD4 Flaw found in 1996 Not collision resistant MD6 ✔✔Merkle Tree like structure parallel computation submitted to NIST for SHA-3 Not ready because of speed issues SHA ✔✔Secure Hash Algorithm SHA ✔✔Most widely used Hash Function All versions secure and collision free SHA-1 ✔✔Developed by NSA for Digital Signature Algorithm 160 bits DSA ✔✔Digital Signature Algorithm SHA-2 ✔✔SHA 224, 256, 384, 512 SHA-3 ✔✔Still in development FORK-256 ✔✔512 b blocks 4 branches in parallel hard to analyze analysis phase, not widespread use RIPEMD-160 ✔✔Created by Hans Dobbertin, Antoon Bosselaers, Bart Praneal GOST ✔✔Russian National Standard TIGER ✔✔Created by Ross Anderson and Eli Biham in 1995 TIGER ✔✔Collision resistant Merkle-Dangard paradigm Entropy ✔✔Measure of uncertainty associated with random variable Co-prime ✔✔No factors in common (3, 7, etc) Eulers Totient ✔✔Part of RSA Number of positive integers less than or equal to n that are co-prime Modulus Operator ✔✔Expressed with % Division, return remainder Fibonacci Numbers ✔✔Leonardo of Pisa Last 2 numbers add together RSA ✔✔Created by Ron Rivest, Adi Shamir, Leonart Alleman RSA ✔✔Most widely used public key cryptography algorithm RSA ✔✔Based on relationships of prime numbers RSA ✔✔1024, 2048, 4096 b and larger keys MQV ✔✔Menezes, Qu, Vanstone MQV ✔✔1995 protocol for key agreement Based on DH MQV ✔✔IEEE P1363 DSA ✔✔Created by David Kravitz in 1991 True random number ✔✔Not possible to generate from computer algorithm DH ✔✔Diffie Hellman DH ✔✔2 parties to establish shared key over an insecure channel DH ✔✔Created by Witfiled Diffie and Martin Hellman in 1976 DH ✔✔Asymmetric key exchange of symmetric key Elliptic Curve ✔✔Created in 1985 by Victor Miller and Neil Koblitz Elliptic Curve ✔✔Endorsed by NSA Private key is random number Size of curve determines difficulty Difficult to find logarithm of random elliptic curve element Elgamal ✔✔Based on DH PGP and GNU Privacy guard Elgamal ✔✔Created in 1984 by Taher Elgamal Digital Signatures ✔✔Encryption of message or digest with senders private key, verify with senders public key Digital Signatures ✔✔Reverse of asymmetric encryption process Non-repudiation RSA DSA Class 1 ✔✔CA Verisign for individuals and email Class 2 ✔✔CA Verisign for organizations proof of identity Class 3 ✔✔CA Verisign Servers and Software Class 4 ✔✔CA Verisign online business transactions Class 5 ✔✔CA Verisign Private organizations and Government security OSCP ✔✔Online Certificate Status Protocol OSCP ✔✔Service that verifies certificates Server Based Certificate Validation ✔✔Delegated Path Discovery Delegated Path Validation [Show More]
Last updated: 11 months ago
Preview 1 out of 26 pages
Buy this document to get the full access instantly
Instant Download Access after purchase
Add to cartInstant download
We Accept:
Reviews( 0 )
$10.00
Document information
Connected school, study & course
About the document
Uploaded On
Jul 21, 2023
Number of pages
26
Written in
Additional information
This document has been written for:
Uploaded
Jul 21, 2023
Downloads
0
Views
51

.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)