Information Technology > QUESTIONS & ANSWERS > COMPTIA IT Fundamentals Certification Practice Questions (All)
COMPTIA IT Fundamentals Certification Practice Questions
Document Content and Description Below
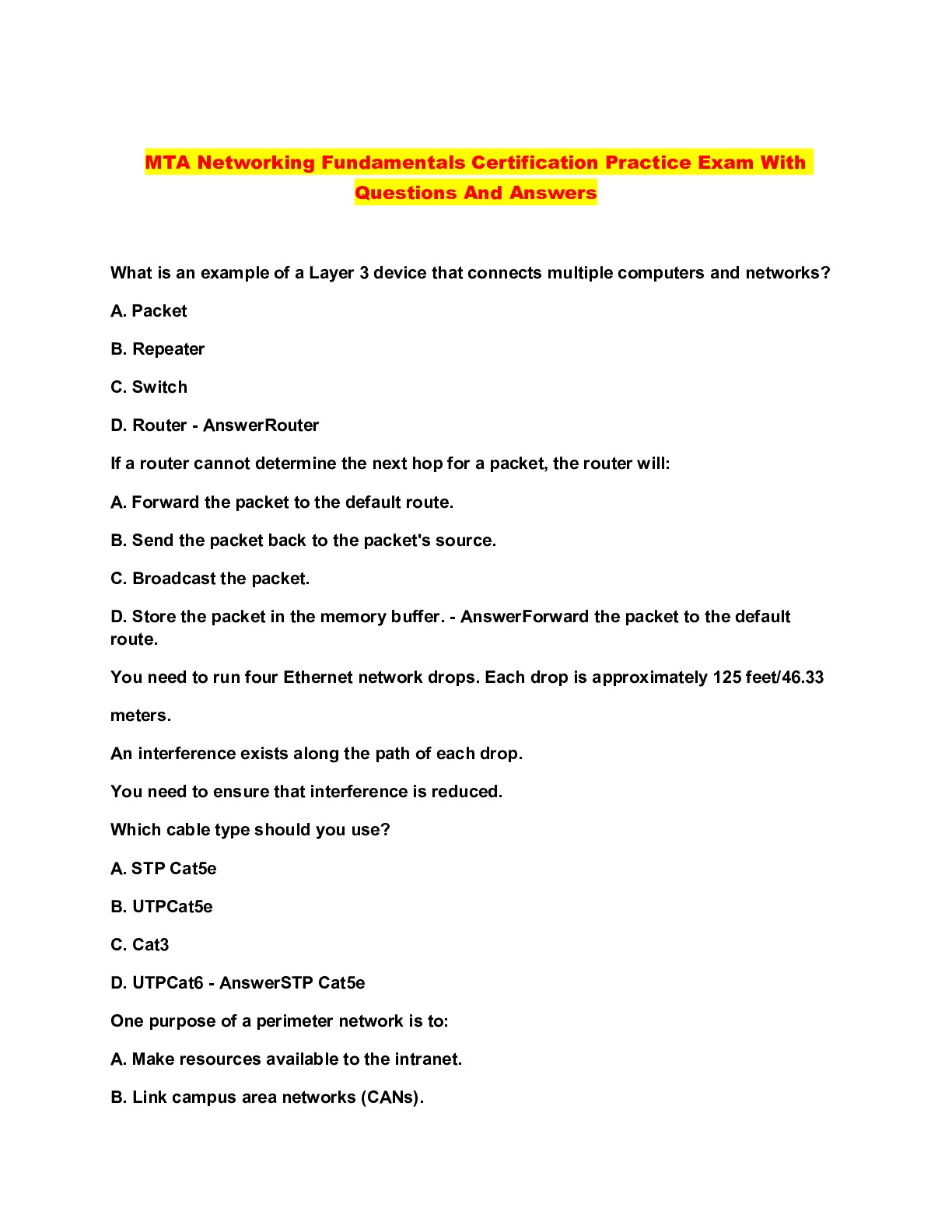
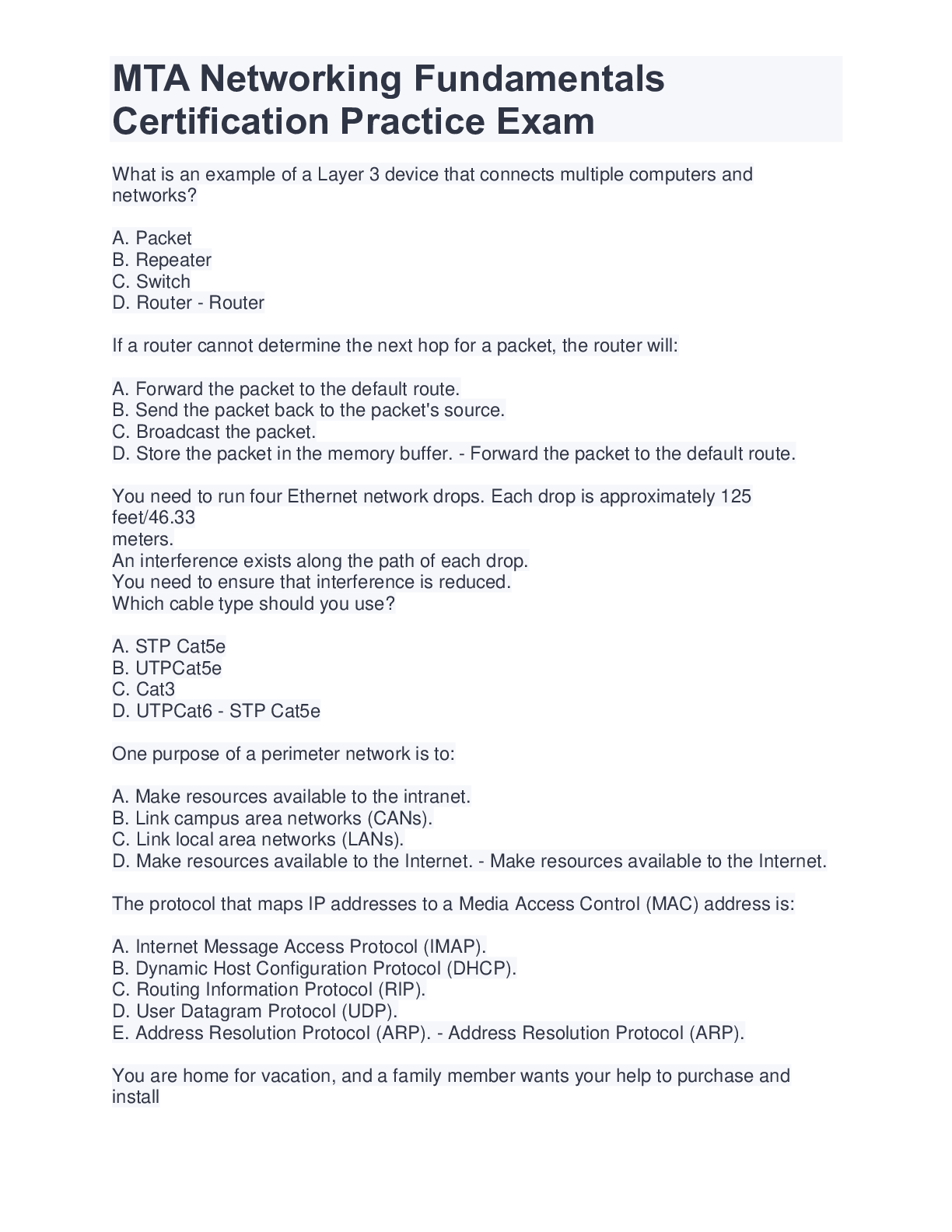
COMPTIA IT Fundamentals Certification Practice Questions After installing the OS on a workstation a technician notices everything is displayed in large windows and the viewing area is limited. What... will the technician need to adjust to resolve this issue? - ✔✔Resolution A User's OS is set to automatically update as updates are released. However, last week's updates failed to download. Which of the following should the user do FIRST to install the updates? - ✔✔Manually download the updates What component is used for temporary storage of program data that is cleared when the computer is turned off? - ✔✔System Memory Which method of patching allows for vendor controlled updates, reduced user interaction, and increased security of the OS or application? - ✔✔Automatic Updates What security threat would the use of cable locks reduce? - ✔✔Hardware Theft Name one reason why password complexity is a best practice. - ✔✔It makes passwords harder to crack. A user receives an email including a link, when they hover the mouse over the link, the actual URL does not match the text in the body of the email and appears to be a string of random characters. What would be the best course of action? - ✔✔Delete the email without clicking the link. What component serves as temporary storage for computer operations? - ✔✔RAM The extension .rtf is an example of what file type? - ✔✔Document What is a common method of preventing physical theft of a laptop or workstation? - ✔✔Cable and lock device securely attached to a secure object. After installing a new software application a user notices the application launches in demo mode. What needs to be done to fully activate the software package? - ✔✔Enter a product or licence key. A user's laptop contains sensitive information. The user often plugs the computer into the corporate network. A sensitive file from the laptop has been found on another user's laptop. How could the user have prevent this breach? - ✔✔Disable file and print sharing on the laptop. A user's government ID number, birth date, and current address are considered what? - ✔✔PII What is the function of a CPU? - ✔✔Performs data computation When trying to activate the OS, a user receives a notice that the software is not genuine. What security threat has occurred? - ✔✔License theft A user is configuring a SOHO wireless router. The user should change the router's default administrator password for what reason? - ✔✔To prevent unauthorized configuration changes A user wants to purchase a CAD application that requires 8GB of RAM to operate. What OS type is required? - ✔✔64-bit Several users want to share a common folder with high availability. What device is best to use for this requirement? - ✔✔Network attached storage appliance (NAS) Which component is responsible for the interconnectivitiy of internal system devices? - ✔✔Motherboard What software type protects a desktop from malicious attacks? - ✔✔Antivirus software What internal computer component is used to connect video, audio, and network cards? - ✔✔Motherboard What method is most important to make sure computer temperature is maintained within normal limits? - ✔✔Ensuring of efficient airflow An employee is using a desk phone that is connected by only a network cable. What technology is the phone using? - ✔✔VoIP What is an example of a file type that can be used to consolidate a group of files? - ✔✔.rar What permission is required to run a .bat file? - ✔✔Execute What connector types can be used by both mice and keyboards? - ✔✔USB/PS2 What will allow the easiest and fastest way to share a file between 2 modern smart phones without joining the same WIFI network? - ✔✔Bluetooth An end user has 16 GB of ram installed on a computer system. Why does the OS only use a maximum of 4 GB of ram? - ✔✔The OS is 32 bit A technician just installed a new computer. What is the best way to manage the cables? - ✔✔Line the cables up neatly and wrap them together with cable ties. A user wants to run a major update on a laptop. What should be considered before running any major updates? - ✔✔Backup important files What allows for the fastest printer connections? - ✔✔USB A user needs to establish a password for an email account. What is a good example of a complex password? - ✔✔01#iWant!2686612338 What is an advantage of using a 64-bit OS? - ✔✔Ability to use a larger amount of RAM A user has finished browsing the internet at a public workstation. What steps should be taken to best secure PII? - ✔✔Clear the browser cache, cookies, and history. [Show More]
Last updated: 10 months ago
Preview 1 out of 5 pages
Instant download
Buy this document to get the full access instantly
Instant Download Access after purchase
Add to cartInstant download
Reviews( 0 )
Document information
Connected school, study & course
About the document
Uploaded On
Aug 21, 2023
Number of pages
5
Written in
Additional information
This document has been written for:
Uploaded
Aug 21, 2023
Downloads
0
Views
81

.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)

.png)