Information Technology > QUESTIONS & ANSWERS > WGU C795 NOC REPORTING TEMPLATE LATEST UPDATED 2022 ALREADY PASSED (All)
WGU C795 NOC REPORTING TEMPLATE LATEST UPDATED 2022 ALREADY PASSED
Document Content and Description Below
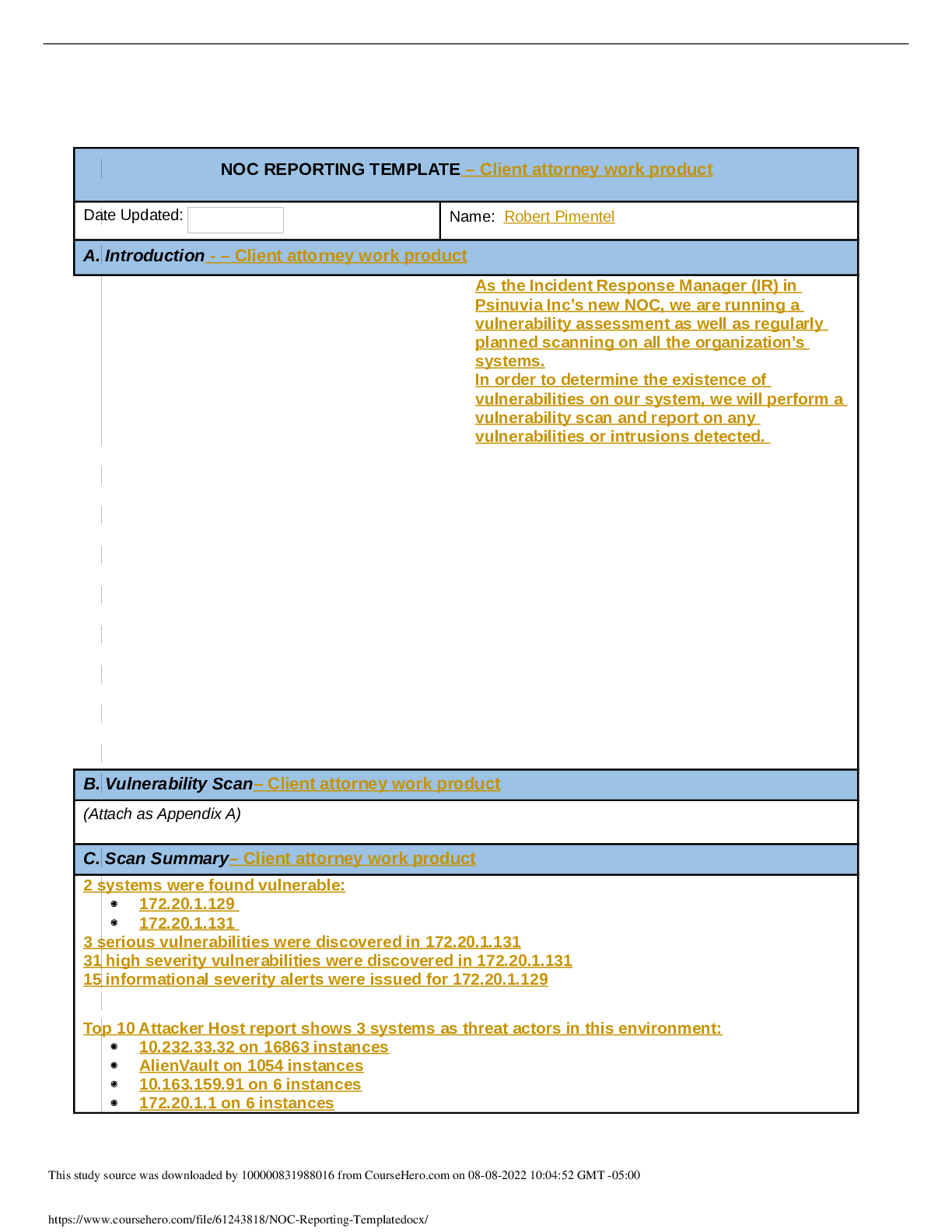
NOC REPORTING TEMPLATE Date Updated: Name: A. Introduction Summarize the events that lead to the discovery of the potential vulnerability. Record your summary in the attached “NOC Reporting Temp... late.” With a high number of web exploits being reported in the news, the Board of Directors requested a vulnerability scan along with standard scans for intrusions. It was deemed necessary as a means of preventative measures and hardening of current public facing systems. Summarize the events that lead to the discovery of the potential vulnerability. Record your summary in the attached “NOC Reporting Template.” B. Vulnerability Scan (Attach as Appendix A) C. Scan Summary Summarize the results of the vulnerability scans and intrusion alarms, including which systems and data were compromised. Be sure to address the basic assessment questions from the attached “Incident Response Plan” as part of your submission. Basic Assessment Questions: 1) Has the information been confirmed to be correct and accurate? Information has been confirmed to be correct and accurate by running vulnerability scans and intrusions alarms report via SIEM tool Alienvault. The vulnerability report was crossreferenced with the intrusion alarms and a zenmap scan which had a coorelation. 2) Who, what, when, where, why, and how? Host-172-20-1-129 was subjected to multiple SQL injection attempts by the same source ip, multiple failed login attempts and login attempts with non-existent user between 2019-12-26 to 2020-01-25. Host-172-20-1-131 was subjected to multiple SQL injections attempts and Web Server Attacks using Cross Site Scripting (XSS) method between 2019-12-26 to 2020-01-25 3) What information is available from the firewall, router, server, system, intrusion detection system (IDS), system logs, etc.? The Alienvault OSSIM has a list of reported alarms and Security Events listed in the time frame 2019-12-26 to 2020-01-25 that was collected and filed in a report for both Hosts in question. The vulnerability scan identified that Host-172-20-1-131 has 4x Serious, 31 High, 8x Medium, 1x Low and 60 Info vulnerabilities. The vulnerability scan identified that Host-172-20- 1-129 show there was no vulnerabilities but recommended 15 warnings. The report also showed that there was total of 2,335 SQL injection attempts, 325 SQL injection attempts form the same ip, 4 Web Server Attacks using Cross Site Scripting, 4 SQL Injection Pattern Attack and 4 Brute Force Authentication via SSH. 4) What type of data is involved, and what is its classification? From reviewing the type of alarms and the raw logs collected by the Alienvault HIDS sensor, the attacker was targeting the Apache Server to gain access to the database. According to the zenmap scan, Host-172-20-1-131 is running mysql on port 3306 that was open. Classification unknown. 5) Are there obscenities, child pornography, or confrontational data? The above could not be determined with the data provided or in this scope. 6) Is there criminal activity? The above could not be determined with the data provided or in this scope. 7) Is the data protected by an encryption solution? According to the zenmap scan Host-172-20-1-131 was running MariaDB. The zenmap probe shows “Maria DB (unauthorized)” meaning zenmap probe did not have the right credentials. The MariaDB is protected and only accepts remote connections from trusted sources. 8) What is the magnitude of the systems being impacted? It can be assumed that the database systems may contain user information stored in a database that may be subjected to PII and/or HIPAA. Not enough information was present to confirm. 9) Is the event still in progress? It is believed that the event has been terminated for both hosts in question as of the creation of this report. This was verified by looking at SIEM real time events filtered by the ip of the hosts in question. 10) Has preliminary containment been performed (i.e., disable account, reset password, remove remote access, isolate device in segregated segment)? Host-172-20-1-131 was shut down at the time of discovery. 11) What is the estimated value of the impacted data and systems? Both assets were given the Asset Value of 2 with 0 being the lowest and 5 being the highest. D. Detailed Analysis Explain the steps taken to identify any exploited systems and data that are included in the scope of the incident. Provide screenshots of specific examples within the logs, illustrating your findings as part of your documentation in the attached “NOC Reporting Template.” The screenshots should be taken within the lab environment and will include your name. Alienvault was used to conduct vulnerability scans. The Analysis feature was also used to identify Alarms and Security Events. Reports were also produced. Below are the steps followed to identify the exploited system: First, under the Analysis, Alarms tab, a query was ran for the dates 2019-07-01 to 2020-01-25 (reference Figure 1 on the left for scope of query). Figure 1 This query produced a report, which can be found under the Report, overview tab. This report presented us with the Top 10 Attacked Hosts which were Host-172-20-1-131 and Host-172-20-1-129 shown in Figure 2. The report narrowed down the list of devices to two hosts. We can now use this to drill down per host. In Figure 3 we can run a query on a specific host in question Host-172-20-1-129. In Figure 4 we can see the results of that query. Shows all the attacks that were launched at that host. We can also click on that particular alarm to get more info. Armed with the systems that are being attacked at a high rate we can use the Vulnerability scanner feature of Alienvault. In Figure 5, the vulnerability scan shows that Host-172-20-1-131 is the most at risk with 4 serious vulnerabilities and critically vulnerable.. Figure 5 Figure 2 Figure 3Figure 4 E. Scan Response Identify the event level of the incident, who needs to be contacted, and when should they be contacted based on the company's incident response plan Although the attempts to compromise Host-172-20-1-131 and Host-172-20-1-129 were unsuccessful, this incident would still be considered as Severity Type “High” according to Psinuvia’s Incident Response Plan. The data on the database hosted by the two Hosts in question could store non-sensitive and/or sensitive data. There were higher than normal level of intruder scanning and probing which was seen in the Alarms Report “Top 15 Alarms” with SQL injection attempts being 2,335 occurrences and 325 by the same source address. According to Psinuvia’s Incident Response Plan, an event with Severity Type is “High” and the CISO, CTO, Legal, Security and applicable management and executive teams should be contacted immediately. F. Remediation Justify the interventions you will use to quarantine and remediate the compromised machine using industry best practices. Host-172-20-1-131 This system was found to have Serious (4), High (31), Medium (8) vulnerabilities identified during vulnerability scan but there was no evidence of a breach or compromise according to the AlienVault OSSIM. Since there were no indicators of compromise (IOC), the system should be shut down for quarantine and containment. According to NIST800-61 (Cichonski et al., Computer Security Incident Handling Guide) “An essential part of containment is decision-making (e.g., shut down a system, disconnect it from a network, disable certain functions).” This will prevent the system from any possible future breaches while it is considered high risk by the vulnerability scan and according to Psinuvia’s Incident Response Plan. NIST800-61 (Cichonski et al., Computer Security Incident Handling Guide), suggests that “…restoring systems from clean backups, rebuilding systems from scratch, replacing compromised files with clean versions, installing patches, changing passwords, and tightening network perimeter security (e.g., firewall rulesets, boundary router access control lists)” are all in order to get the system to normal operation. After the system has been remedied and placed back into a production environment, according to NIST800-61 (Cichonski et al., Computer Security Incident Handling Guide), the system should be highly monitored as part of the recovery process [Show More]
Last updated: 1 year ago
Preview 1 out of 126 pages
Reviews( 0 )
Document information
Connected school, study & course
About the document
Uploaded On
Aug 08, 2022
Number of pages
126
Written in
Additional information
This document has been written for:
Uploaded
Aug 08, 2022
Downloads
1
Views
474

.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
 (1).png)
.png)
.png)